下载到的是一个.vmem文件.
https://pan.baidu.com/s/1x8YDL6IJkB7wEFJAtcHOBw
使用volatility获取信息进行取证.
volatility -f '/root/DATABASE/191009/mem.vmem' imageinfo
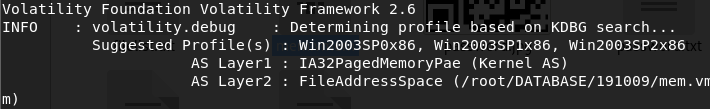
之后通过尝试确定profiles=Win2003SP1x86
volatility notepad -f '/root/DATABASE/191009/mem.vmem'读取记事本信息,提示
hello hust
flag is not here
I can only tell you that I downloaded a file and the password of the compressed package is in it
volatility -f '/root/文档/mem.vmem' --profile=Win2003SP1x86 hivelist扫注册表
volatility -f '/root/文档/mem.vmem' --profile=Win2003SP1x86 pslist扫进程
volatility -f '/root/文档/mem.vmem' --profile=Win2003SP1x86 filesscan扫文件,有
0x00000000032b2a30 1 0 R--rw- \Device\HarddiskVolume1\MyDownloads\Download\password.txt
dump出来之后是个RGB文档,辨识出是二维码.
使用如下脚本进行转换:
from PIL import Image
x = 256 #x坐标 通过对txt里的行数进行整数分解
y = 256 #y坐标 x * y = 行数
im = Image.new("RGB", (x, y)) #创建图片
file = open('password_with_rgb.txt') #打开rbg值的文件
#通过每个rgb点生成图片
for i in range(0, x):
for j in range(0, y):
line = file.readline() #获取一行的rgb值
rgb = line.split(",") #分离rgb,文本中逗号后面有空格
im.putpixel((i, j), (int(rgb[0]), int(rgb[1]), int(rgb[2]))) #将rgb转化为像素
im.show()
im.save('password.jpg')
#也可用im.save('flag.jpg')保存下来
来源:https://blog.csdn.net/ssjjtt1997/article/details/78450816
扫码得到密码
p@@@ssw02d2333
注意到
0x00000000014fcad8 1 0 R--rw- \Device\HarddiskVolume1\Documents and Settings\Administrator\桌面\welcome.zip
dump下来
解压得到flag.txt
ZmxhZ3tkZDVhNGUxcjNfOGQ0cWU1ZjJfYTVkYWZ3cjVnfQ==
b64之后得到flag.
flag{dd5a4e1r3_8d4qe5f2_a5dafwr5g}
技术参考
https://www.4hou.com/technology/5860.html
https://www.restran.net/2017/08/10/memory-forensics-tool-volatility/
https://mengsec.com/2018/10/20/CTF-Volatility/
https://www.jianshu.com/p/6438bc3302c8
