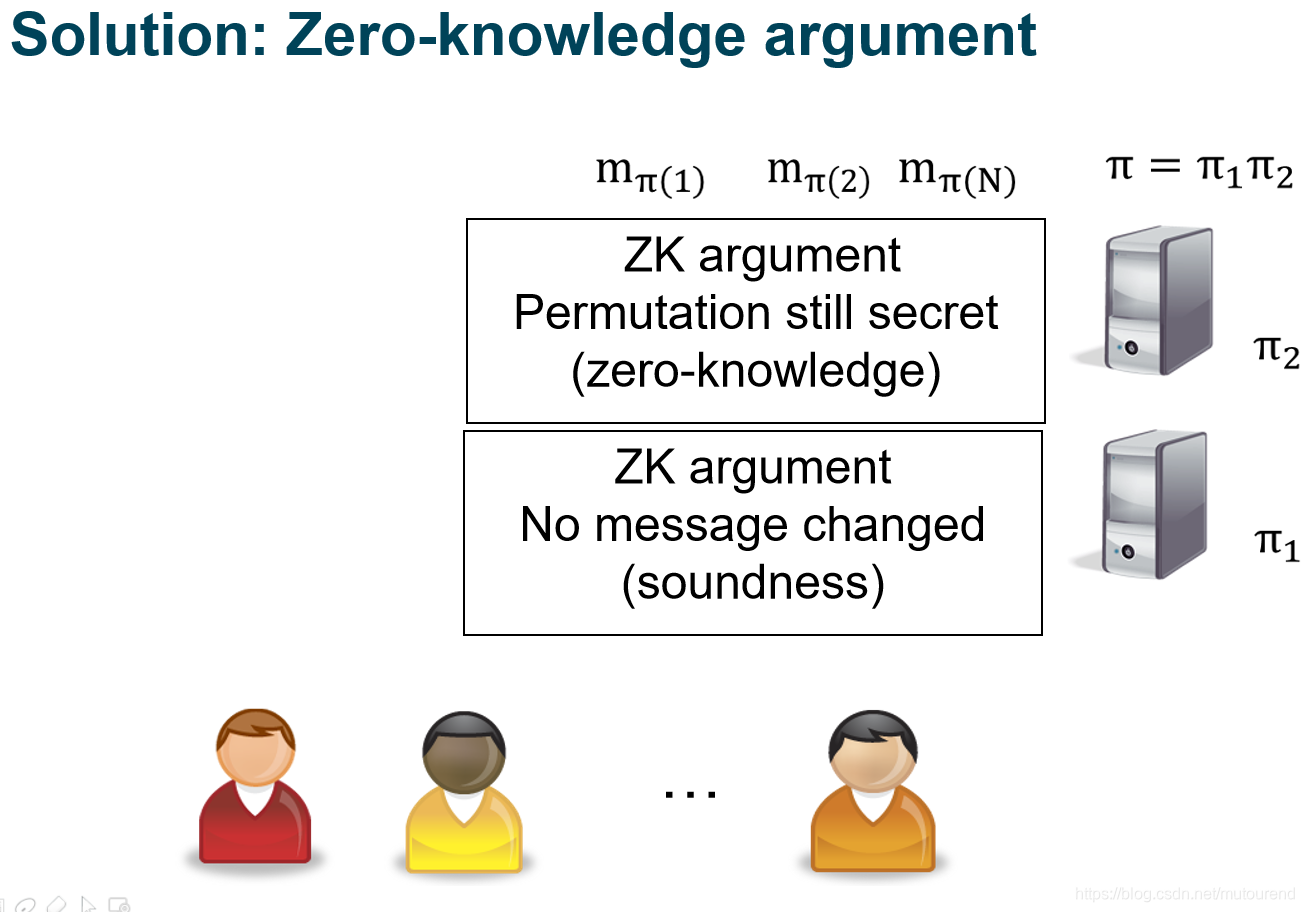
Stephanie Bayer和Jens Groth 2012年论文《Efficient Zero-Knowledge Argument for Correctness of a Shuffle 》。
本论文的argument具有sublinear communication complexity,当shuffle
N
(
=
m
×
n
)
N(=m\times n)
N ( = m × n )
O
(
m
+
n
)
O(m+n)
O ( m + n )
m
=
n
m=n
m = n
O
(
N
)
O(\sqrt{N})
O ( N
)
prover的computational complexity为
O
(
N
log
m
)
O(N\log{m})
O ( N log m )
O
(
N
)
O(N)
O ( N )
verifier的计算比较轻量。
构建full shuffle argument的基础为:Neff’s approach [Nef01] is based on the invariance of polynomials under permutation of the roots,即Nef01的shuffle算法基于的是:多项式的根permutation的话,其最终形成的多项式是不变的——
f
(
x
)
=
(
x
−
r
1
)
(
x
−
r
2
)
.
.
.
(
x
−
r
n
)
f(x)=(x-r_1)(x-r_2)...(x-r_n)
f ( x ) = ( x − r 1 ) ( x − r 2 ) . . . ( x − r n )
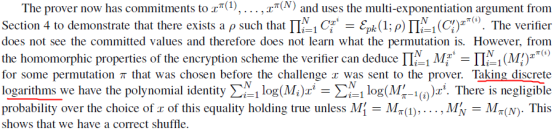
引入了multi-exponentiation argument,用于hide committed values。
基于hidden committed values的shuffle argument。与[Gro09]类似,做了些微改进。
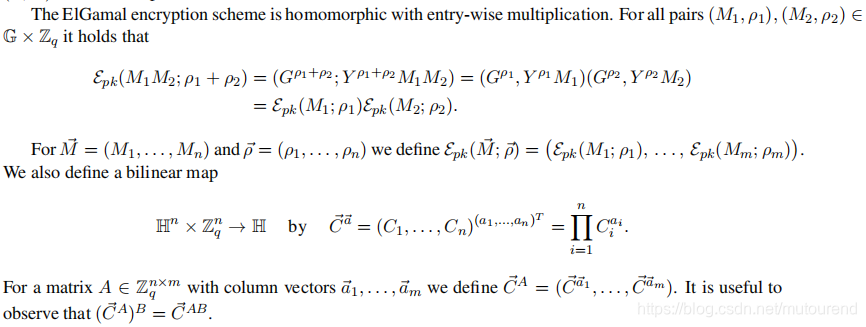
主要是利用了EIGamal encryption的乘法同态性和Pedersen commitment的加法同态性。所以需要构建相应的common reference string
σ
=
(
p
k
,
c
k
)
\sigma =(pk,ck)
σ = ( p k , c k )
p
k
pk
p k
c
k
ck
c k
q
q
q
其中EIGamal的知识详见:博客 EIGamal encryption VS Pairing encryption 。
EIGamal具有乘法同态性:
Pedersen commitment具有加法同态性:
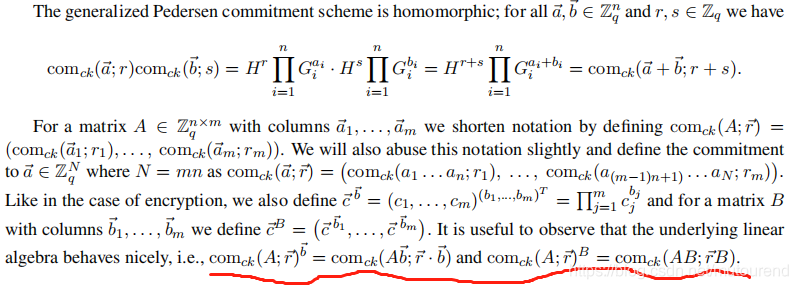
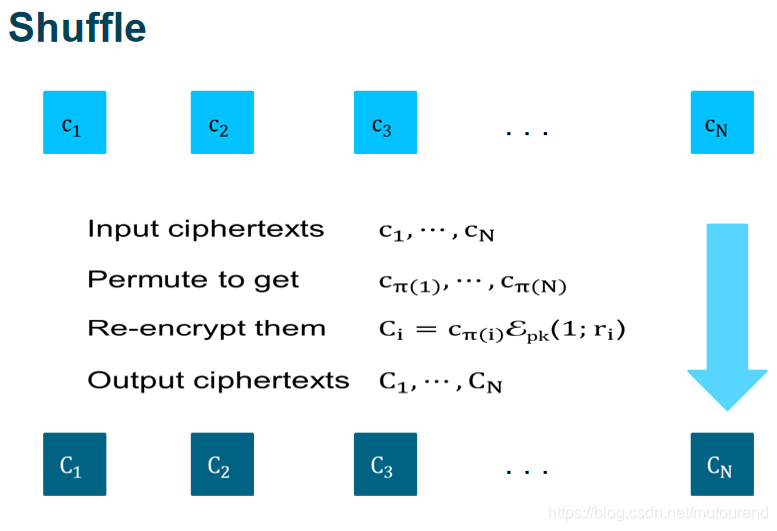
需要an argument of knowledge of permutation
π
∈
∑
N
\pi\in \sum_{N}
π ∈ ∑ N
{
ρ
i
}
i
=
1
N
\{\rho_i\}_{i=1}^N
{ ρ i } i = 1 N
{
C
i
}
i
=
1
N
\{C_i\}_{i=1}^N
{ C i } i = 1 N
{
C
i
′
}
i
=
1
N
\{C_i^{'}\}_{i=1}^N
{ C i ′ } i = 1 N
C
i
′
=
C
π
(
i
)
ε
p
k
(
1
;
ρ
i
)
C_i^{'}=C_{\pi(i)} \varepsilon_{pk}(1;\rho_i)
C i ′ = C π ( i ) ε p k ( 1 ; ρ i )
multi-exponentiation argument:用于证明the product of a set of ciphertexts raised to a set of committed exponents yields a particular ciphertext。
product argument:用于证明a set of committed values has a particular product。
主要的实现步骤为:
Prover对permutation进行commit,即commit to
π
(
1
)
,
…
,
π
(
N
)
\pi(1),…,\pi(N)
π ( 1 ) , … , π ( N )
Verifier给Prover challenge
x
x
x
Prover commit to
x
π
(
1
)
,
…
,
x
π
(
N
)
x^{\pi(1)},…,x^{\pi(N)}
x π ( 1 ) , … , x π ( N )
Prover提供argument,证明其知道相应的openings of the commitments to permutations of respectively
1
,
…
,
N
1,…,N
1 , … , N
x
1
,
…
,
x
N
x^1,…,x^N
x 1 , … , x N
x
1
,
…
,
x
N
x^1,…,x^N
x 1 , … , x N
x
x
x
4.1 为了证明两组commitment采用的是相同的permutation,Verifier给Prover random challenges
y
y
y
z
z
z
4.2 Prover commit to 一系列
d
1
−
z
=
y
π
(
1
)
+
x
π
(
1
)
−
z
,
…
,
d
N
−
z
=
y
π
(
N
)
+
x
π
(
N
)
−
z
d_1-z=y\pi(1)+x^{\pi(1)}-z,…,d_N-z=y\pi(N)+x^{\pi(N)}-z
d 1 − z = y π ( 1 ) + x π ( 1 ) − z , … , d N − z = y π ( N ) + x π ( N ) − z
∏
i
=
1
N
(
d
i
−
z
)
=
∏
i
=
1
N
(
y
i
+
x
i
−
z
)
\prod_{i=1}^{N}(d_i-z)= \prod_{i=1}^{N}(yi+x^i-z)
∏ i = 1 N ( d i − z ) = ∏ i = 1 N ( y i + x i − z )
z
z
z
d
i
d_i
d i
y
i
+
x
i
yi+x^i
y i + x i
z
z
z
d
i
d_i
d i
N
q
−
1
\frac{N}{q-1}
q − 1 N
y
y
y
Prover使用multi-exponentiation argument来证明存在
ρ
\rho
ρ
∏
i
=
1
N
C
i
x
i
=
ε
p
k
(
1
;
ρ
)
∏
i
=
1
N
(
C
i
’
)
x
π
(
i
)
\prod_{i=1}^{N}C_i^{x^i}=\varepsilon_{pk}(1;\rho)\prod_{i=1}^{N}(C_i^’)^{x^{\pi(i)}}
∏ i = 1 N C i x i = ε p k ( 1 ; ρ ) ∏ i = 1 N ( C i ’ ) x π ( i )
C
i
,
C
i
’
C_i,C_i^’
C i , C i ’
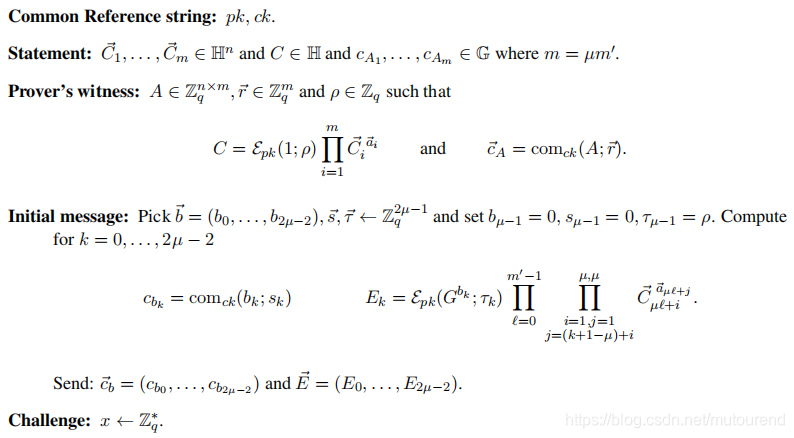
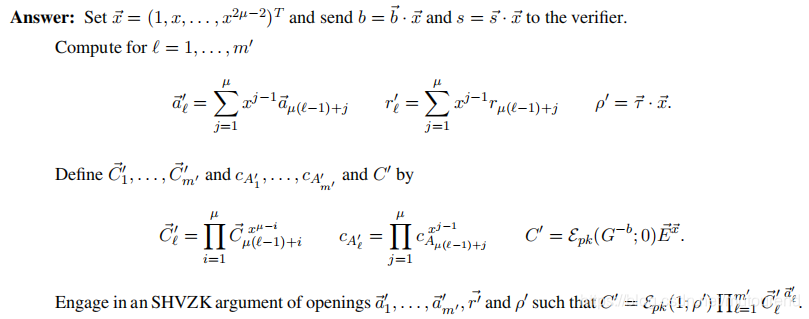
详细的shuffle argument算法流程为:
将第二节shuffle argument算法流程中的
a
⃗
,
b
⃗
\vec{a},\vec{b}
a
, b
ρ
=
0
\rho=0
ρ = 0
C
1
⃗
,
.
.
.
,
C
m
⃗
,
C
\vec{C_1},...,\vec{C_m},C
C 1
, . . . , C m
, C
a
1
⃗
,
.
.
.
,
a
m
⃗
\vec{a_1},...,\vec{a_m}
a 1
, . . . , a m
C
=
∏
i
=
1
m
C
i
⃗
a
i
⃗
C=\prod_{i=1}^{m}\vec{C_i}^{\vec{a_i}}
C = ∏ i = 1 m C i
a i
Prover依次对
a
1
⃗
,
.
.
.
,
a
m
⃗
\vec{a_1},...,\vec{a_m}
a 1
, . . . , a m
c
A
⃗
=
(
c
o
m
c
k
(
a
1
⃗
;
r
1
)
,
.
.
.
,
c
o
m
c
k
(
a
m
⃗
;
r
m
)
)
\vec{c_A}=(com_{ck}(\vec{a_1};r_1),...,com_{ck}(\vec{a_m};r_m))
c A
= ( c o m c k ( a 1
; r 1 ) , . . . , c o m c k ( a m
; r m ) )
Prover计算
E
k
=
∏
1
≤
i
,
j
≤
m
;
j
=
(
k
−
m
)
+
i
C
i
⃗
a
j
⃗
E_k=\prod_{1\leq i,j\leq m;j=(k-m)+i}\vec{C_i}^{\vec{a_j}}
E k = ∏ 1 ≤ i , j ≤ m ; j = ( k − m ) + i C i
a j
E
1
,
E
2
,
.
.
.
,
E
2
m
−
1
E_1,E_2,...,E_{2m-1}
E 1 , E 2 , . . . , E 2 m − 1
E
m
=
C
E_m=C
E m = C
Verifier给Prover challenge
x
x
x
Prover计算
a
⃗
=
∑
j
=
1
m
x
j
a
j
⃗
\vec{a}=\sum_{j=1}^{m}x^j\vec{a_j}
a
= ∑ j = 1 m x j a j
a
⃗
\vec{a}
a
Verifier验证
C
x
m
∏
k
=
1
;
k
≠
m
2
m
−
1
E
k
x
k
=
∏
i
=
1
m
C
i
⃗
(
x
m
−
i
a
⃗
)
C^{x^m}\prod_{k=1;k\neq m}^{2m-1}E_k^{x^k}=\prod_{i=1}^{m}\vec{C_i}^{(x^{m-i}\vec{a})}
C x m ∏ k = 1 ; k = m 2 m − 1 E k x k = ∏ i = 1 m C i
( x m − i a
)
C
=
∏
i
=
1
m
C
i
⃗
a
i
⃗
C=\prod_{i=1}^{m}\vec{C_i}^{\vec{a_i}}
C = ∏ i = 1 m C i
a i
∏
i
=
1
2
m
−
1
E
k
x
k
=
∏
i
=
1
m
C
i
⃗
(
x
m
−
i
∑
j
=
1
m
x
j
a
j
⃗
)
=
∏
i
=
1
m
C
i
⃗
(
x
m
−
i
a
⃗
)
=
C
x
m
∏
k
=
1
;
k
≠
m
2
m
−
1
E
k
x
k
=
C
x
m
∏
k
=
1
;
k
≠
m
2
m
−
1
∏
1
≤
i
,
j
≤
m
;
j
=
(
k
−
m
)
+
i
C
i
⃗
a
j
⃗
x
k
=
C
x
m
∏
i
=
1
m
C
i
⃗
∑
1
≤
j
≤
m
;
k
=
m
−
i
+
j
;
k
≠
m
a
j
⃗
x
k
\prod_{i=1}^{2m-1}E_k^{x^k}=\prod_{i=1}^{m}\vec{C_i}^{(x^{m-i}\sum_{j=1}^{m}x^j\vec{a_j})}=\prod_{i=1}^{m}\vec{C_i}^{(x^{m-i}\vec{a})}=C^{x^m}\prod_{k=1;k\neq m}^{2m-1}E_k^{x^k}=C^{x^m}\prod_{k=1;k\neq m}^{2m-1}{\prod_{1\leq i,j\leq m;j=(k-m)+i}\vec{C_i}^{\vec{a_j}x^k}}=C^{x^m}\prod_{i=1}^{m}{\vec{C_i}}^{\sum_{1\leq j\leq m;k=m-i+j;k\neq m}\vec{a_j}x^k}
∏ i = 1 2 m − 1 E k x k = ∏ i = 1 m C i
( x m − i ∑ j = 1 m x j a j
) = ∏ i = 1 m C i
( x m − i a
) = C x m ∏ k = 1 ; k = m 2 m − 1 E k x k = C x m ∏ k = 1 ; k = m 2 m − 1 ∏ 1 ≤ i , j ≤ m ; j = ( k − m ) + i C i
a j
x k = C x m ∏ i = 1 m C i
∑ 1 ≤ j ≤ m ; k = m − i + j ; k = m a j
x k
C
x
m
=
∏
i
=
1
m
C
i
⃗
(
x
m
−
i
∑
j
=
1
m
x
j
a
j
⃗
−
∑
1
≤
j
≤
m
;
k
=
m
−
i
+
j
;
k
≠
m
a
j
⃗
x
k
)
=
∏
i
=
1
m
C
i
⃗
a
i
⃗
x
m
=
(
∏
i
=
1
m
C
i
⃗
a
i
⃗
)
x
m
C^{x^m}=\prod_{i=1}^{m}{\vec{C_i}}^{(x^{m-i}\sum_{j=1}^{m}x^j\vec{a_j}-\sum_{1\leq j\leq m;k=m-i+j;k\neq m}\vec{a_j}x^k)}=\prod_{i=1}^{m}{\vec{C_i}}^{\vec{a_i}x^m}=(\prod_{i=1}^{m}{\vec{C_i}}^{\vec{a_i}})^{x^m}
C x m = ∏ i = 1 m C i
( x m − i ∑ j = 1 m x j a j
− ∑ 1 ≤ j ≤ m ; k = m − i + j ; k = m a j
x k ) = ∏ i = 1 m C i
a i
x m = ( ∏ i = 1 m C i
a i
) x m
C
=
∏
i
=
1
m
C
i
⃗
a
i
⃗
C=\prod_{i=1}^{m}\vec{C_i}^{\vec{a_i}}
C = ∏ i = 1 m C i
a i
以上流程,可能存在witness泄露的来源点有:
x
x
x
a
⃗
=
∑
j
=
1
m
x
j
a
j
⃗
\vec{a}=\sum_{j=1}^{m}x^j\vec{a_j}
a
= ∑ j = 1 m x j a j
a
1
⃗
,
.
.
.
,
a
m
⃗
\vec{a_1},...,\vec{a_m}
a 1
, . . . , a m
a
0
⃗
←
Z
q
n
\vec{a_0}\leftarrow \mathbb{Z}_q^n
a 0
← Z q n
a
0
⃗
\vec{a_0}
a 0
x
x
x
a
⃗
=
a
0
⃗
+
∑
j
=
1
m
x
j
a
j
⃗
\vec{a}=\vec{a_0}+\sum_{j=1}^{m}x^j\vec{a_j}
a
= a 0
+ ∑ j = 1 m x j a j
E
k
=
∏
1
≤
i
,
j
≤
m
;
j
=
(
k
−
m
)
+
i
C
i
⃗
a
j
⃗
E_k=\prod_{1\leq i,j\leq m;j=(k-m)+i}\vec{C_i}^{\vec{a_j}}
E k = ∏ 1 ≤ i , j ≤ m ; j = ( k − m ) + i C i
a j
a
1
⃗
,
.
.
.
,
a
m
⃗
\vec{a_1},...,\vec{a_m}
a 1
, . . . , a m
ε
p
k
(
G
b
k
;
τ
k
)
\varepsilon_{pk}(G^{b_k};\tau_k)
ε p k ( G b k ; τ k )
x
x
x
b
k
b_k
b k
c
B
k
=
c
o
m
c
k
(
b
k
;
s
k
)
c_{B_k}=com_{ck}(b_k;s_k)
c B k = c o m c k ( b k ; s k )
E
m
=
C
E_m=C
E m = C
b
m
=
0
,
s
m
=
0
b_m=0,s_m=0
b m = 0 , s m = 0
ρ
≠
0
\rho\neq0
ρ = 0
E
m
=
C
E_m=C
E m = C
τ
m
=
ρ
\tau_m=\rho
τ m = ρ
(
a
0
⃗
a
1
⃗
⋯
a
m
−
1
⃗
a
m
⃗
)
(
C
1
⃗
C
2
⃗
⋮
C
m
⃗
)
(
C
1
⃗
a
0
⃗
C
1
⃗
a
1
⃗
⋱
C
1
⃗
a
m
−
1
⃗
C
1
⃗
a
m
⃗
C
2
⃗
a
0
⃗
C
2
⃗
a
1
⃗
⋱
C
2
⃗
a
m
−
1
⃗
C
2
⃗
a
m
⃗
⋱
⋱
⋱
⋱
⋱
C
m
⃗
a
0
⃗
C
m
⃗
a
1
⃗
⋱
C
m
⃗
a
m
−
1
⃗
C
m
⃗
a
m
⃗
)
ε
p
k
(
G
b
2
m
−
1
;
τ
2
m
−
1
)
E
2
m
−
1
⋮
ε
p
k
(
G
b
m
+
1
;
τ
m
+
1
)
E
m
+
1
ε
p
k
(
1
;
ρ
)
E
m
ε
p
k
(
G
b
0
;
τ
0
)
E
0
ε
p
k
(
G
b
1
;
τ
1
)
E
1
⋯
ε
p
k
(
G
b
m
−
1
;
τ
m
−
1
)
E
m
−
1
\begin{matrix} & \begin{pmatrix} \ \ \ \ \vec{a_0}&\ \ \ \ \vec{a_1} & \cdots &\ \ \ \vec{a_{m-1}} &\ \ \ \ \vec{a_m} \end{pmatrix} & \\ \begin{pmatrix} \vec{C_1}\\ \vec{C_2}\\ \vdots\\ \vec{C_m} \end{pmatrix} & \begin{pmatrix} \vec{C_1}^{\vec{a_0}}& \vec{C_1}^{\vec{a_1}} & \ddots & \vec{C_1}^{\vec{a_{m-1}}} & \vec{C_1}^{\vec{a_m}}\\ \vec{C_2}^{\vec{a_0}} & \vec{C_2}^{\vec{a_1}} & \ddots & \vec{C_2}^{\vec{a_{m-1}}} & \vec{C_2}^{\vec{a_m}}\\ \ddots & \ddots & \ddots & \ddots & \ddots\\ \vec{C_m}^{\vec{a_0}} & \vec{C_m}^{\vec{a_1}} & \ddots & \vec{C_m}^{\vec{a_{m-1}}} & \vec{C_m}^{\vec{a_m}} \end{pmatrix} & \begin{matrix} \\ \varepsilon_{pk}(G^{b_{2m-1}};\tau_{2m-1})E_{2m-1}\\ \vdots\\ \varepsilon_{pk}(G^{b_{m+1}};\tau_{m+1})E_{m+1}\\ \varepsilon_{pk}(1;\rho)E_m \end{matrix} \\ & \begin{matrix} \varepsilon_{pk}(G^{b_0};\tau_0)E_0& \varepsilon_{pk}(G^{b_1};\tau_1)E_1 & \cdots & \varepsilon_{pk}(G^{b_{m-1}};\tau_{m-1})E_{m-1} \end{matrix}& \end{matrix}
⎝ ⎜ ⎜ ⎜ ⎛ C 1
C 2
⋮ C m
⎠ ⎟ ⎟ ⎟ ⎞ ( a 0
a 1
⋯ a m − 1
a m
) ⎝ ⎜ ⎜ ⎜ ⎜ ⎛ C 1
a 0
C 2
a 0
⋱ C m
a 0
C 1
a 1
C 2
a 1
⋱ C m
a 1
⋱ ⋱ ⋱ ⋱ C 1
a m − 1
C 2
a m − 1
⋱ C m
a m − 1
C 1
a m
C 2
a m
⋱ C m
a m
⎠ ⎟ ⎟ ⎟ ⎟ ⎞ ε p k ( G b 0 ; τ 0 ) E 0 ε p k ( G b 1 ; τ 1 ) E 1 ⋯ ε p k ( G b m − 1 ; τ m − 1 ) E m − 1 ε p k ( G b 2 m − 1 ; τ 2 m − 1 ) E 2 m − 1 ⋮ ε p k ( G b m + 1 ; τ m + 1 ) E m + 1 ε p k ( 1 ; ρ ) E m
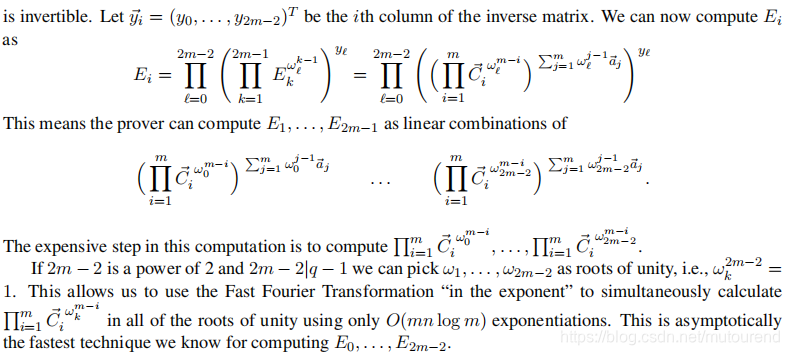
在上述Multi-exponentiation Argument中,Prover需要计算
E
0
,
⋯
,
E
2
m
−
1
E_0,\cdots,E_{2m-1}
E 0 , ⋯ , E 2 m − 1
k
=
1
,
⋯
,
2
m
−
1
k=1,\cdots,2m-1
k = 1 , ⋯ , 2 m − 1
E
k
=
∏
1
≤
i
,
j
≤
m
;
j
=
(
k
−
m
)
+
i
C
i
⃗
a
j
⃗
=
∏
i
=
1
,
j
=
1
;
j
=
(
k
−
m
)
+
i
m
,
m
C
i
⃗
a
j
⃗
E_k=\prod_{1\leq i,j\leq m;j=(k-m)+i}\vec{C_i}^{\vec{a_j}}=\prod_{i=1,j=1;j=(k-m)+i}^{m,m}\vec{C_i}^{\vec{a_j}}
E k = ∏ 1 ≤ i , j ≤ m ; j = ( k − m ) + i C i
a j
= ∏ i = 1 , j = 1 ; j = ( k − m ) + i m , m C i
a j
m
2
m^2
m 2
C
i
⃗
a
j
⃗
\vec{C_i}^{\vec{a_j}}
C i
a j
C
i
⃗
a
j
⃗
=
∏
l
=
1
n
C
i
l
a
i
l
\vec{C_i}^{\vec{a_j}}=\prod_{l=1}^{n}C_{il}^{a_{il}}
C i
a j
= ∏ l = 1 n C i l a i l
n
n
n
H
\mathbb{H}
H
E
k
E_k
E k
m
n
2
mn^2
m n 2
H
\mathbb{H}
H
当
m
m
m
FFT:
Toom-Cook:
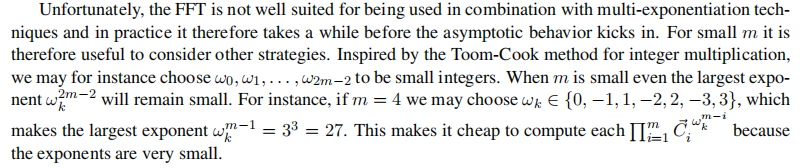
增加Verifier与Prover交互次数:基本思路为:
m
×
m
m\times m
m × m
m
2
m^2
m 2
m
×
m
m\times m
m × m
μ
×
μ
\mu \times \mu
μ × μ
m
=
μ
m
′
m=\mu m'
m = μ m ′
(
C
1
⃗
a
1
⃗
⋱
C
1
⃗
a
m
−
1
⃗
C
1
⃗
a
m
⃗
C
2
⃗
a
1
⃗
⋱
C
2
⃗
a
m
−
1
⃗
C
2
⃗
a
m
⃗
⋱
⋱
⋱
⋱
C
m
⃗
a
1
⃗
⋱
C
m
⃗
a
m
−
1
⃗
C
m
⃗
a
m
⃗
)
\begin{pmatrix} \vec{C_1}^{\vec{a_1}} & \ddots & \vec{C_1}^{\vec{a_{m-1}}} & \vec{C_1}^{\vec{a_m}}\\ \vec{C_2}^{\vec{a_1}} & \ddots & \vec{C_2}^{\vec{a_{m-1}}} & \vec{C_2}^{\vec{a_m}}\\ \ddots & \ddots & \ddots & \ddots\\ \vec{C_m}^{\vec{a_1}} & \ddots & \vec{C_m}^{\vec{a_{m-1}}} & \vec{C_m}^{\vec{a_m}} \end{pmatrix}
⎝ ⎜ ⎜ ⎜ ⎜ ⎛ C 1
a 1
C 2
a 1
⋱ C m
a 1
⋱ ⋱ ⋱ ⋱ C 1
a m − 1
C 2
a m − 1
⋱ C m
a m − 1
C 1
a m
C 2
a m
⋱ C m
a m
⎠ ⎟ ⎟ ⎟ ⎟ ⎞
针对3.1中的计算压力,在https://github.com/3for/verifiable-shuffle中分别做了相应的优化实现:
# This parameter determine which version of the program is executed.
# 0 stands for no optimization inside of the code
# 1 uses multi-exponentiation techniques
# 2 uses multi-exponentiation techniques and FFT to find values E_i
# 3 uses multi-exponentiation techniques, extra interaction and Toom-Cook 4 to find values E_i, in this case m =16 or 64\n
3
参考资料:Efficient Zero-Knowledge Argument for Correctness of a Shuffle 》Efficient Zero-Knowledge Argument for Correctness of a Shuffle 》向量的Hadamard product VS Inner product EIGamal encryption VS Pairing encryption