一个网络安全学习爱好者在学习过程中记录下的笔记,希望在CSDN能和大家一起成长,学习,分享,进步,下面分享的是代码审计中SQL注入的案例,希望对入门网安的朋友们有所帮助,大神有兴趣看看即可,勿喷感谢,同时也欢迎各位师傅私聊交流学习。文章有所参考,也感谢教授我网安知识的师父们,感谢出生在这个互联网时代,知识触手可及。
SQL注入
原理:用户输入的数据被当做SQL语句执行
案例:
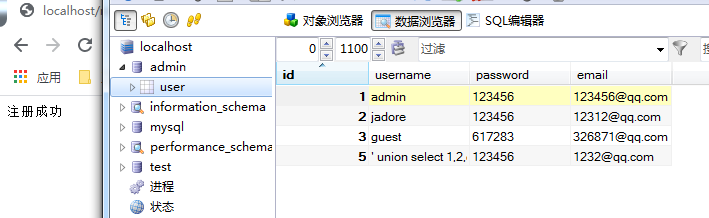
MySQL建立数据库admin,库中有表user,四个字段,分别是id,username,password,email
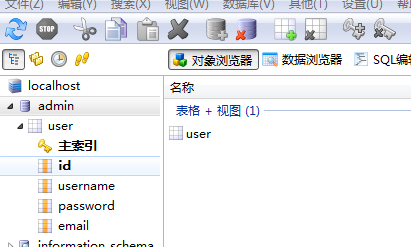
插入三条记录
构造登录界面
login.html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
<form action="login.php" method="post">
账号:<input type="text" name="username"></br>
密码:<input type="password" name="password"></br>
<input type="submit" value="点击登录" name="login">
</form>
</body>
</html>
MySQL处理流程
login.php
<?php
if(!isset($_POST['login'])) {
echo "login fail!";
}else{
$username = $_POST['username'];
$password = $_POST['password'];
$conn = mysql_connect("localhost","root","root");
mysql_select_db("admin",$conn);
$sql = "SELECT * FROM user WHERE username='".$username."'";
$result = mysql_query($sql) or die('执行SQL语句失败'.mysql_error());
while($row = mysql_fetch_array($result)) {
$get_username = $row['username'];
$get_password = $row['password'];
}
if($get_password == $password && $get_username == $username) {
echo "login success!";
}else{
echo "please login!";
}
}
读者可自行尝试验证SQL注入漏洞,后面记录下二次注入
一阶注入(案例在上面):
一阶SQL注入发生在一次HTTP请求和响应中,即攻击者发送恶意请求后服务器立即接收该请求并作出响应,例如在参数?id=1后面添加单引号可能有报错提示。
二阶注入(二次注入):
二阶注入会发生在两次HTTP请求和响应中,攻击者提交恶意数据并使其存储在数据库中,攻击者利用web应用检索存储在数据库中的恶意数据,造成二次注入。
构造注册页面
reg.html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
<form action="reg.php" method="post">
id:<input type="text" name="id"><br >
username:<input type="text" name="username"><br >
password:<input type="password" name="password"><br >
email:<input type="text" name="email"><br >
<input type="submit" name="submit" value="点击提交">
</form>
</body>
</html>
MySQL处理流程
reg.php
<?php
header("content-type:text/jtml;charset=utf-8");
if(!empty($_POST['submit'])) {
$id = addslashes($_POST['id']);
$username = addslashes($_POST['username']);
$password = addslashes($_POST['password']);
$email = addslashes($_POST['email']);
$conn = mysql_connect("localhost","root","root");
mysql_select_db("admin",$conn);
$sql = "INSERT INTO USER (id,username,password,email) VALUES ('$id','$username','$password','$email');";
$result = mysql_query($sql) or die('执行SQL语句失败!'.mysql_error());
if($result) {
echo "注册成功";
}else{
echo "注册失败";
}
}else {
echo "Please submit data!";
}
构造检索界面
search.html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
<form action="search.php" method="post">
search id:<input type="text" name="id"><br>
<input type="submit" name="submit" value="点击查询">
</form>
</body>
</html>
MySQL处理流程
<?php
header("content-type:text/jtml;charset=utf-8");
if(!empty($_POST['submit'])){
$id = $_POST['id'];
$conn = mysql_connect("localhost","root","root");
mysql_select_db("admin",$conn);
$sql = "SELECT * FROM user WHERE id='$id'";
$result = mysql_query($sql);
while($row = mysql_fetch_array($result)) {
$username = $row['username'];
$sql = "SELECT * FROM user WHERE username='$username'";
$result = mysql_query($sql);
while($row = mysql_fetch_array($result)) {
echo "ID:".$row['id']."\n";
echo "USERNAME:".$row['username']."\n";
echo "PASSWORD:".$row['password']."\n";
echo "EMAIL:".$row['email']."\n";
}
}
}
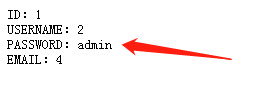
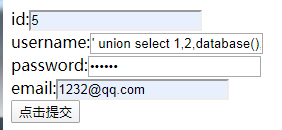
二次注入验证:
注册一个账号,使其用户名为’ union select * from 1,2,database(),4#
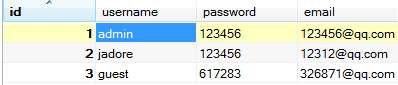
数据库中存储的恶意数据
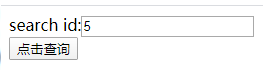
 检索
检索
拼接成SQL语句为
select * from user where username='' union select 1,2,database(),4#'