在博客 Pointproofs: Aggregating Proofs for Multiple Vector Commitments 学习笔记1 中,主要对 Algorand团队Gorbunov等人2020年论文《Pointproofs: Aggregating Proofs for Multiple Vector Commitments 》做了一个总体的梳理。该论文在 Libert和Yung 2010年论文《Concise mercurial vector commitments and independent zero-knowledge sets with short proofs 》的基础上,做了以下改进:
采用了非对称bilinear pairing group,并针对
G
1
\mathbb{G}_1
G 1
G
2
\mathbb{G}_2
G 2
G
T
\mathbb{G}_T
G T
r
=
(
∑
i
∈
S
m
i
t
i
)
−
1
m
o
d
p
r=(\sum_{i\in S}m_it_i)^{-1}\ mod\ p
r = ( ∑ i ∈ S m i t i ) − 1 m o d p
G
T
\mathbb{G}_T
G T
G
1
\mathbb{G}_1
G 1
采用Random Oracle Model,基于hash函数
H
H
H
t
i
=
H
(
i
,
C
,
S
,
m
⃗
[
S
]
)
t_i=H(i,C,S,\vec{m}[S])
t i = H ( i , C , S , m
[ S ] )
H
H
H
H
′
H'
H ′
t
j
,
i
=
H
(
i
,
C
j
,
S
j
,
m
⃗
j
[
S
j
]
)
t_{j,i}=H(i,C_j,S_j,\vec{m}_j[S_j])
t j , i = H ( i , C j , S j , m
j [ S j ] )
t
j
′
=
H
′
(
j
,
{
C
j
,
S
j
,
m
⃗
j
[
S
j
]
}
j
∈
[
l
]
)
t_j'=H'(j,\{C_j,S_j,\vec{m}_j[S_j]\}_{j\in[l]})
t j ′ = H ′ ( j , { C j , S j , m
j [ S j ] } j ∈ [ l ] )
本博客将重点关注:
proof of correctness/binding for same-commitment aggregation
proof of correctness/binding for cross-commitment aggregation
same-commitment aggregation from CDH-like assumption
weak binding and realization
cross-commitment aggregation from polynomial commitments
https://github.com/algorand/pointproofs 代码解析
该论文实现的binding属性是基于AGW+ROM model under the
l
l
l Pointproofs: Aggregating Proofs for Multiple Vector Commitments 学习笔记1 1.1节内容)
具体的实现为:
Setup(
1
λ
,
1
N
1^{\lambda},1^N
1 λ , 1 N
α
←
Z
p
\alpha\leftarrow \mathbb{Z}_p
α ← Z p
a
⃗
=
(
α
,
α
2
,
⋯
,
α
N
)
\vec{a}=(\alpha,\alpha^2,\cdots,\alpha^N)
a
= ( α , α 2 , ⋯ , α N )
g
1
a
⃗
=
(
g
1
α
,
⋯
,
g
1
α
N
)
g_1^{\vec{a}}=(g_1^\alpha,\cdots,g_1^{\alpha^N})
g 1 a
= ( g 1 α , ⋯ , g 1 α N )
g
1
α
N
a
⃗
[
−
1
]
=
(
g
1
α
N
+
2
,
⋯
,
g
1
α
2
N
)
g_1^{\alpha^N\vec{a}[-1]}=(g_1^{\alpha^{N+2}},\cdots,g_1^{\alpha^{2N}})
g 1 α N a
[ − 1 ] = ( g 1 α N + 2 , ⋯ , g 1 α 2 N )
g
2
a
⃗
=
(
g
2
α
,
⋯
,
g
2
α
N
)
g_2^{\vec{a}}=(g_2^\alpha,\cdots,g_2^{\alpha^N})
g 2 a
= ( g 2 α , ⋯ , g 2 α N )
g
T
α
N
+
1
=
e
(
g
1
α
,
g
2
α
N
)
g_T^{\alpha^{N+1}}=e(g_1^{\alpha},g_2^{\alpha^N})
g T α N + 1 = e ( g 1 α , g 2 α N )
g
1
a
⃗
,
g
1
α
N
a
⃗
[
−
1
]
g_1^{\vec{a}},g_1^{\alpha^N\vec{a}[-1]}
g 1 a
, g 1 α N a
[ − 1 ]
g
2
a
⃗
,
g
T
α
N
+
1
g_2^{\vec{a}},g_T^{\alpha^{N+1}}
g 2 a
, g T α N + 1
α
\alpha
α
Commit(
m
⃗
\vec{m}
m
m
⃗
∈
Z
p
N
\vec{m}\in \mathbb{Z}_p^N
m
∈ Z p N
C
=
g
1
m
⃗
T
a
⃗
=
g
1
∑
i
∈
N
m
i
α
i
C=g_1^{\vec{m}^T\vec{a}}=g_1^{\sum_{i\in N}m_i\alpha^i}
C = g 1 m
T a
= g 1 ∑ i ∈ N m i α i
UpdateCommit(
C
,
S
,
m
⃗
[
S
]
,
m
⃗
′
[
S
]
C,S,\vec{m}[S],\vec{m}'[S]
C , S , m
[ S ] , m
′ [ S ]
C
′
=
C
⋅
g
1
(
m
⃗
′
[
S
]
−
m
⃗
[
S
]
)
T
a
⃗
[
S
]
=
C
⋅
g
1
∑
i
∈
S
(
m
i
′
−
m
i
)
α
i
C'=C\cdot g_1^{(\vec{m}'[S]-\vec{m}[S])^T\vec{a}[S]}=C\cdot g_1^{\sum_{i\in S}(m_i'-m_i)\alpha^i}
C ′ = C ⋅ g 1 ( m
′ [ S ] − m
[ S ] ) T a
[ S ] = C ⋅ g 1 ∑ i ∈ S ( m i ′ − m i ) α i
Prove(
i
,
m
⃗
i,\vec{m}
i , m
i
i
i
π
i
=
g
1
α
N
+
1
−
i
m
⃗
[
−
i
]
T
a
⃗
[
−
i
]
=
g
1
∑
j
∈
[
N
]
−
{
i
}
m
j
α
N
+
1
−
i
+
j
\pi_i=g_1^{\alpha^{N+1-i}\vec{m}[-i]^T\vec{a}[-i]}=g_1^{\sum_{j\in [N]-\{i\}}m_j\alpha^{N+1-i+j}}
π i = g 1 α N + 1 − i m
[ − i ] T a
[ − i ] = g 1 ∑ j ∈ [ N ] − { i } m j α N + 1 − i + j
g
1
α
N
+
1
−
i
a
⃗
[
−
i
]
g_1^{\alpha^{N+1-i}\vec{a}[-i]}
g 1 α N + 1 − i a
[ − i ]
m
j
m_j
m j
j
≠
i
j\neq i
j = i
m
j
′
m_j'
m j ′
π
i
′
=
π
⋅
g
1
(
m
j
′
−
m
j
)
α
N
+
1
−
i
+
j
\pi_i'=\pi\cdot g_1^{(m_j'-m_j)\alpha^{N+1-i+j}}
π i ′ = π ⋅ g 1 ( m j ′ − m j ) α N + 1 − i + j
m
i
m_i
m i
m
i
′
m_i'
m i ′
π
i
′
=
π
i
\pi_i'=\pi_i
π i ′ = π i
C
C
C
C
′
C'
C ′
Aggregate(
C
,
S
,
m
⃗
[
S
]
,
{
π
i
:
i
∈
S
}
C,S,\vec{m}[S],\{\pi_i:i\in S\}
C , S , m
[ S ] , { π i : i ∈ S }
π
^
=
∏
i
∈
S
π
i
t
i
\hat{\pi}=\prod_{i\in S}\pi_i^{t_i}
π ^ = ∏ i ∈ S π i t i
t
i
=
H
(
i
,
C
,
S
,
m
⃗
[
S
]
)
t_i=H(i,C,S,\vec{m}[S])
t i = H ( i , C , S , m
[ S ] )
Verify(
C
,
S
,
m
⃗
[
S
]
,
π
^
C,S,\vec{m}[S],\hat{\pi}
C , S , m
[ S ] , π ^
e
(
C
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
=
e
(
π
^
,
g
2
)
⋅
g
T
α
N
+
1
∑
i
∈
S
m
i
t
i
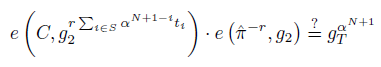
e(C,g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})=e(\hat{\pi},g_2)\cdot g_T^{\alpha^{N+1}\sum_{i\in S}m_it_i}
e ( C , g 2 ∑ i ∈ S α N + 1 − i t i ) = e ( π ^ , g 2 ) ⋅ g T α N + 1 ∑ i ∈ S m i t i
t
i
=
H
(
i
,
C
,
S
,
m
⃗
[
S
]
)
t_i=H(i,C,S,\vec{m}[S])
t i = H ( i , C , S , m
[ S ] )
对于任意的
i
∈
[
N
]
,
π
i
=
P
r
o
v
e
(
i
,
m
⃗
)
=
g
1
α
N
+
1
−
i
m
⃗
[
−
i
]
T
a
⃗
[
−
i
]
i\in [N],\pi_i=Prove(i,\vec{m})=g_1^{\alpha^{N+1-i}\vec{m}[-i]^T\vec{a}[-i]}
i ∈ [ N ] , π i = P r o v e ( i , m
) = g 1 α N + 1 − i m
[ − i ] T a
[ − i ] Commit/Prove/Aggregate/Verify整个流程,可分两步证明:
1)证明
e
(
C
,
g
2
α
N
+
1
−
i
)
=
e
(
π
i
,
g
2
)
⋅
g
T
α
N
+
1
m
i
e(C,g_2^{\alpha^{N+1-i}})=e(\pi_i,g_2)\cdot g_T^{\alpha^{N+1}m_i}
e ( C , g 2 α N + 1 − i ) = e ( π i , g 2 ) ⋅ g T α N + 1 m i
2)证明
e
(
C
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
=
e
(
π
^
,
g
2
)
⋅
g
T
α
N
+
1
∑
i
∈
S
m
i
t
i
e(C,g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})=e(\hat{\pi},g_2)\cdot g_T^{\alpha^{N+1}\sum_{i\in S}m_it_i}
e ( C , g 2 ∑ i ∈ S α N + 1 − i t i ) = e ( π ^ , g 2 ) ⋅ g T α N + 1 ∑ i ∈ S m i t i
具体为:
m
⃗
T
a
⃗
=
m
⃗
[
−
i
]
T
a
⃗
[
−
i
]
+
α
i
m
i
\vec{m}^T\vec{a}=\vec{m}[-i]^T\vec{a}[-i]+\alpha^im_i
m
T a
= m
[ − i ] T a
[ − i ] + α i m i
α
N
+
1
−
i
\alpha^{N+1-i}
α N + 1 − i
(
m
⃗
T
a
⃗
)
α
N
+
1
−
i
=
α
N
+
1
−
i
m
⃗
[
−
i
]
T
a
⃗
[
−
i
]
+
α
N
+
1
m
i
(\vec{m}^T\vec{a})\alpha^{N+1-i}=\alpha^{N+1-i}\vec{m}[-i]^T\vec{a}[-i]+\alpha^{N+1}m_i
( m
T a
) α N + 1 − i = α N + 1 − i m
[ − i ] T a
[ − i ] + α N + 1 m i
e
(
g
1
m
⃗
T
a
⃗
,
g
2
α
N
+
1
−
i
)
=
e
(
g
1
α
N
+
1
−
i
m
⃗
[
−
i
]
T
a
⃗
[
−
i
]
,
g
2
)
⋅
g
T
α
N
+
1
m
i
e(g_1^{\vec{m}^T\vec{a}},g_2^{\alpha^{N+1-i}})=e(g_1^{\alpha^{N+1-i}\vec{m}[-i]^T\vec{a}[-i]},g_2)\cdot g_T^{\alpha^{N+1}m_i}
e ( g 1 m
T a
, g 2 α N + 1 − i ) = e ( g 1 α N + 1 − i m
[ − i ] T a
[ − i ] , g 2 ) ⋅ g T α N + 1 m i
e
(
C
,
g
2
α
N
+
1
−
i
)
=
e
(
π
i
,
g
2
)
⋅
g
T
α
N
+
1
m
i
e(C,g_2^{\alpha^{N+1-i}})=e(\pi_i,g_2)\cdot g_T^{\alpha^{N+1}m_i}
e ( C , g 2 α N + 1 − i ) = e ( π i , g 2 ) ⋅ g T α N + 1 m i
2)在
e
(
C
,
g
2
α
N
+
1
−
i
)
=
e
(
π
i
,
g
2
)
⋅
g
T
α
N
+
1
m
i
e(C,g_2^{\alpha^{N+1-i}})=e(\pi_i,g_2)\cdot g_T^{\alpha^{N+1}m_i}
e ( C , g 2 α N + 1 − i ) = e ( π i , g 2 ) ⋅ g T α N + 1 m i
t
i
t_i
t i
e
(
C
,
g
2
α
N
+
1
−
i
t
i
)
=
e
(
π
i
t
i
,
g
2
)
⋅
g
T
α
N
+
1
m
i
t
i
e(C,g_2^{\alpha^{N+1-i}t_i})=e(\pi_i^{t_i},g_2)\cdot g_T^{\alpha^{N+1}m_it_i}
e ( C , g 2 α N + 1 − i t i ) = e ( π i t i , g 2 ) ⋅ g T α N + 1 m i t i
S
S
S
i
∈
S
i\in S
i ∈ S
e
(
C
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
=
e
(
∏
i
∈
S
π
i
t
i
,
g
2
)
⋅
g
T
α
N
+
1
∑
i
∈
S
m
i
t
i
=
e
(
π
^
,
g
2
)
⋅
g
T
α
N
+
1
∑
i
∈
S
m
i
t
i
e(C,g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})=e(\prod_{i\in S}\pi_i^{t_i},g_2)\cdot g_T^{\alpha^{N+1}\sum_{i\in S}m_it_i}=e(\hat{\pi},g_2)\cdot g_T^{\alpha^{N+1}\sum_{i\in S}m_it_i}
e ( C , g 2 ∑ i ∈ S α N + 1 − i t i ) = e ( ∏ i ∈ S π i t i , g 2 ) ⋅ g T α N + 1 ∑ i ∈ S m i t i = e ( π ^ , g 2 ) ⋅ g T α N + 1 ∑ i ∈ S m i t i
证明UpdateCommit算法正确性的思路为:
m
⃗
′
T
a
⃗
=
(
m
⃗
′
[
S
]
−
m
⃗
[
S
]
)
T
a
⃗
[
S
]
+
m
⃗
T
a
⃗
\vec{m}'^T\vec{a}=(\vec{m}'[S]-\vec{m}[S])^T\vec{a}[S]+\vec{m}^T\vec{a}
m
′ T a
= ( m
′ [ S ] − m
[ S ] ) T a
[ S ] + m
T a
采用归谬法来证明,假设adversary 可计算
C
=
g
1
z
⃗
T
a
⃗
C=g_1^{\vec{z}^T\vec{a}}
C = g 1 z
T a
(
S
,
m
⃗
[
S
]
)
(S,\vec{m}[S])
( S , m
[ S ] )
π
^
\hat{\pi}
π ^
m
⃗
[
S
]
≠
z
⃗
[
S
]
\vec{m}[S]\neq \vec{z}[S]
m
[ S ] = z
[ S ]
π
^
\hat{\pi}
π ^
e
(
g
1
z
⃗
T
a
⃗
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
=
e
(
π
^
,
g
2
)
⋅
g
T
α
N
+
1
∑
i
∈
S
z
i
t
i
=
e
(
π
^
,
g
2
)
⋅
g
T
α
N
+
1
∑
i
∈
S
m
i
t
i
e(g_1^{\vec{z}^T\vec{a}},g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})=e(\hat{\pi},g_2)\cdot g_T^{\alpha^{N+1}\sum_{i\in S}z_it_i}=e(\hat{\pi},g_2)\cdot g_T^{\alpha^{N+1}\sum_{i\in S}m_it_i}
e ( g 1 z
T a
, g 2 ∑ i ∈ S α N + 1 − i t i ) = e ( π ^ , g 2 ) ⋅ g T α N + 1 ∑ i ∈ S z i t i = e ( π ^ , g 2 ) ⋅ g T α N + 1 ∑ i ∈ S m i t i
注意adversary也不知道
g
1
α
N
+
1
g_1^{\alpha^{N+1}}
g 1 α N + 1
log
g
1
π
^
\log_{g_1}\hat{\pi}
log g 1 π ^
α
N
+
1
\alpha^{N+1}
α N + 1
0
0
0
g
T
α
N
+
1
g_T^{\alpha^{N+1}}
g T α N + 1
∑
i
∈
S
m
i
t
i
≡
p
∑
i
∈
S
z
i
t
i
\sum_{i\in S}m_it_i\equiv_p \sum_{i \in S}z_it_i
∑ i ∈ S m i t i ≡ p ∑ i ∈ S z i t i
z
⃗
[
S
]
T
t
⃗
≡
p
m
⃗
[
S
]
T
t
⃗
\vec{z}[S]^T\vec{t}\equiv_p \vec{m}[S]^T\vec{t}
z
[ S ] T t
≡ p m
[ S ] T t
t
⃗
=
(
H
(
i
,
C
,
S
,
m
⃗
[
S
]
)
,
i
∈
S
)
\vec{t}=(H(i,C,S,\vec{m}[S]),i\in S)
t
= ( H ( i , C , S , m
[ S ] ) , i ∈ S )
假设当
(
S
,
z
⃗
[
S
]
,
m
⃗
[
S
]
)
(S,\vec{z}[S],\vec{m}[S])
( S , z
[ S ] , m
[ S ] )
t
⃗
←
Z
p
∣
S
∣
\vec{t}\leftarrow \mathbb{Z}_p^{|S|}
t
← Z p ∣ S ∣
Pr
t
⃗
[
z
⃗
[
S
]
̸
≡
p
m
⃗
[
S
]
a
n
d
z
⃗
[
S
]
T
t
⃗
≡
p
m
⃗
[
S
]
T
t
⃗
]
=
1
/
p
\Pr_{\vec{t}}[\vec{z}[S]\not\equiv_p \vec{m}[S]\ and\ \vec{z}[S]^T\vec{t}\equiv_p \vec{m}[S]^T\vec{t}]=1/p
Pr t
[ z
[ S ] ≡ p m
[ S ] a n d z
[ S ] T t
≡ p m
[ S ] T t
] = 1 / p
因此问题的关键在于:ensure the uniform choice of
t
⃗
\vec{t}
t
(
S
,
z
⃗
[
S
]
,
m
⃗
[
S
]
)
(S,\vec{z}[S],\vec{m}[S])
( S , z
[ S ] , m
[ S ] )
C
C
C
z
⃗
\vec{z}
z
C
,
S
,
m
⃗
[
S
]
C,S,\vec{m}[S]
C , S , m
[ S ]
H
(
i
,
⋅
,
⋅
,
⋅
)
H(i,\cdot,\cdot,\cdot)
H ( i , ⋅ , ⋅ , ⋅ )
t
i
t_i
t i
若adversary可以找到相应的
m
i
≠
z
i
m_i\neq z_i
m i = z i
∑
i
∈
S
z
i
t
i
≡
p
∑
i
∈
S
m
i
t
i
\sum_{i\in S}z_it_i\equiv_p \sum_{i \in S}m_it_i
∑ i ∈ S z i t i ≡ p ∑ i ∈ S m i t i
C
,
S
,
m
⃗
[
S
]
C,S,\vec{m}[S]
C , S , m
[ S ]
H
H
H
t
i
=
H
(
i
,
⋅
,
⋅
,
⋅
)
t_i=H(i,\cdot,\cdot,\cdot)
t i = H ( i , ⋅ , ⋅ , ⋅ )
C
,
S
,
m
⃗
[
S
]
C,S,\vec{m}[S]
C , S , m
[ S ]
H
H
H
若
t
i
t_i
t i
m
i
m_i
m i
∣
S
∣
−
1
|S|-1
∣ S ∣ − 1
m
i
m_i
m i
∑
i
∈
S
z
i
t
i
≡
p
∑
i
∈
S
m
i
t
i
\sum_{i\in S}z_it_i\equiv_p \sum_{i \in S}m_it_i
∑ i ∈ S z i t i ≡ p ∑ i ∈ S m i t i
m
i
m_i
m i
若
t
i
=
H
(
i
,
C
)
t_i=H(i,C)
t i = H ( i , C )
2
log
p
2^{\sqrt{\log p}}
2 log p
{
z
i
t
i
,
m
i
t
i
}
i
∈
[
N
]
\{z_it_i,m_it_i\}_{i \in [N]}
{ z i t i , m i t i } i ∈ [ N ]
S
S
S
2
log
p
2^{\sqrt{\log p}}
2 log p
∑
i
∈
S
z
i
t
i
≡
p
∑
i
∈
S
m
i
t
i
\sum_{i\in S}z_it_i\equiv_p \sum_{i \in S}m_it_i
∑ i ∈ S z i t i ≡ p ∑ i ∈ S m i t i
log
p
≈
256
\log p\approx 256
log p ≈ 2 5 6
2
log
p
≈
2
16
2^{\sqrt{\log p}}\approx 2^{16}
2 log p
≈ 2 1 6
若
t
i
=
H
(
i
,
C
,
S
)
t_i=H(i,C,S)
t i = H ( i , C , S )
t
i
=
H
(
i
,
C
)
t_i=H(i,C)
t i = H ( i , C )
t
i
=
H
(
i
,
C
,
S
)
t_i = H(i, C, S)
t i = H ( i , C , S )
∑
i
∈
S
z
i
t
i
\sum_{i\in S} z_it_i
∑ i ∈ S z i t i
m
i
m_i
m i
i
∈
S
i \in S
i ∈ S
分为两步来分析:相当于对于固定
C
,
S
,
m
⃗
[
S
]
C,S,\vec{m}[S]
C , S , m
[ S ]
z
⃗
和
y
⃗
\vec{z}和\vec{y}
z
和 y
C
=
g
1
z
⃗
T
a
⃗
+
α
N
y
⃗
T
a
⃗
[
−
1
]
C=g_1^{\vec{z}^T\vec{a}+\alpha^N\vec{y}^T\vec{a}[-1]}
C = g 1 z
T a
+ α N y
T a
[ − 1 ]
m
⃗
[
S
]
̸
≡
p
z
⃗
[
S
]
且
(
m
⃗
[
S
]
−
z
⃗
[
S
]
)
T
t
⃗
≡
p
0
\vec{m}[S]\not\equiv_p\vec{z}[S]且(\vec{m}[S]-\vec{z}[S])^T\vec{t}\equiv_p 0
m
[ S ] ≡ p z
[ S ] 且 ( m
[ S ] − z
[ S ] ) T t
≡ p 0
z
⃗
和
y
⃗
\vec{z}和\vec{y}
z
和 y
正常open为
{
z
i
}
i
∈
[
S
]
\{z_i\}_{i\in [S]}
{ z i } i ∈ [ S ]
e
(
C
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
=
e
(
g
1
z
⃗
T
a
⃗
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
=
e
(
π
^
,
g
2
)
⋅
g
T
α
N
+
1
∑
i
∈
S
z
i
t
i
e(C,g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})=e(g_1^{\vec{z}^T\vec{a}},g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})=e(\hat{\pi},g_2)\cdot g_T^{\alpha^{N+1}\sum_{i\in S}z_it_i}
e ( C , g 2 ∑ i ∈ S α N + 1 − i t i ) = e ( g 1 z
T a
, g 2 ∑ i ∈ S α N + 1 − i t i ) = e ( π ^ , g 2 ) ⋅ g T α N + 1 ∑ i ∈ S z i t i
{
m
i
}
i
∈
[
S
]
,
其
中
m
⃗
[
S
]
≠
z
⃗
[
S
]
\{m_i\}_{i\in [S]},其中\vec{m}[S]\neq \vec{z}[S]
{ m i } i ∈ [ S ] , 其 中 m
[ S ] = z
[ S ]
e
(
g
1
∑
j
∈
[
N
−
1
]
y
j
α
N
+
1
+
j
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
e(g_1^{\sum_{j\in[N-1]}y_j\alpha^{N+1+j}},g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})
e ( g 1 ∑ j ∈ [ N − 1 ] y j α N + 1 + j , g 2 ∑ i ∈ S α N + 1 − i t i )
等式左边为:
e
(
g
1
z
⃗
T
a
⃗
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
⋅
e
(
g
1
∑
j
∈
[
N
−
1
]
y
j
α
N
+
1
+
j
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
=
e
(
g
1
∑
i
∈
[
N
]
z
i
α
i
+
∑
j
∈
[
N
−
1
]
y
j
α
N
+
1
+
j
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
=
e
(
C
′
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
e(g_1^{\vec{z}^T\vec{a}},g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})\cdot e(g_1^{\sum_{j\in[N-1]}y_j\alpha^{N+1+j}},g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})=e(g_1^{\sum_{i\in[N]}z_i\alpha^i+\sum_{j\in[N-1]}y_j\alpha^{N+1+j}},g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})=e(C',g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})
e ( g 1 z
T a
, g 2 ∑ i ∈ S α N + 1 − i t i ) ⋅ e ( g 1 ∑ j ∈ [ N − 1 ] y j α N + 1 + j , g 2 ∑ i ∈ S α N + 1 − i t i ) = e ( g 1 ∑ i ∈ [ N ] z i α i + ∑ j ∈ [ N − 1 ] y j α N + 1 + j , g 2 ∑ i ∈ S α N + 1 − i t i ) = e ( C ′ , g 2 ∑ i ∈ S α N + 1 − i t i )
等式右边为:
e
(
π
^
,
g
2
)
⋅
g
T
α
N
+
1
∑
i
∈
S
z
i
t
i
⋅
e
(
g
1
∑
j
∈
[
N
−
1
]
y
j
α
N
+
1
+
j
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
=
e
(
π
^
,
g
2
)
⋅
g
T
α
N
+
1
∑
i
∈
S
z
i
t
i
⋅
e
(
g
1
,
g
2
)
α
N
+
1
∑
j
∈
[
N
−
1
]
y
j
α
j
⋅
∑
i
∈
[
S
]
α
N
+
1
−
i
t
i
e(\hat{\pi},g_2)\cdot g_T^{\alpha^{N+1}\sum_{i\in S}z_it_i}\cdot e(g_1^{\sum_{j\in[N-1]}y_j\alpha^{N+1+j}},g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})=e(\hat{\pi},g_2)\cdot g_T^{\alpha^{N+1}\sum_{i\in S}z_it_i}\cdot e(g_1,g_2)^{\alpha^{N+1}\sum_{j\in[N-1]}y_j\alpha^j\cdot\sum_{i\in[S]}\alpha^{N+1-i}t_i}
e ( π ^ , g 2 ) ⋅ g T α N + 1 ∑ i ∈ S z i t i ⋅ e ( g 1 ∑ j ∈ [ N − 1 ] y j α N + 1 + j , g 2 ∑ i ∈ S α N + 1 − i t i ) = e ( π ^ , g 2 ) ⋅ g T α N + 1 ∑ i ∈ S z i t i ⋅ e ( g 1 , g 2 ) α N + 1 ∑ j ∈ [ N − 1 ] y j α j ⋅ ∑ i ∈ [ S ] α N + 1 − i t i
∑
j
∈
[
N
−
1
]
y
j
α
j
⋅
∑
i
∈
[
S
]
α
N
+
1
−
i
t
i
=
∑
i
∈
[
S
]
(
t
i
⋅
∑
j
∈
[
N
−
1
]
y
j
α
N
+
1
−
i
+
j
)
=
∑
i
∈
[
S
]
t
i
x
i
\sum_{j\in[N-1]}y_j\alpha^j\cdot\sum_{i\in[S]}\alpha^{N+1-i}t_i=\sum_{i\in [S]}(t_i\cdot \sum_{j\in[N-1]}y_j\alpha^{N+1-i+j})=\sum_{i\in[S]}t_ix_i
∑ j ∈ [ N − 1 ] y j α j ⋅ ∑ i ∈ [ S ] α N + 1 − i t i = ∑ i ∈ [ S ] ( t i ⋅ ∑ j ∈ [ N − 1 ] y j α N + 1 − i + j ) = ∑ i ∈ [ S ] t i x i
x
i
=
∑
j
∈
[
N
−
1
]
y
j
α
N
+
1
−
i
+
j
x_i=\sum_{j\in[N-1]}y_j\alpha^{N+1-i+j}
x i = ∑ j ∈ [ N − 1 ] y j α N + 1 − i + j
这样就有
e
(
C
′
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
=
e
(
π
^
,
g
2
)
⋅
g
T
α
N
+
1
∑
i
∈
S
z
i
t
i
⋅
g
T
α
N
+
1
∑
i
∈
[
S
]
t
i
x
i
=
e
(
π
^
,
g
2
)
⋅
g
T
α
N
+
1
∑
i
∈
S
(
z
i
+
x
i
)
t
i
=
e
(
π
^
,
g
2
)
⋅
g
T
α
N
+
1
∑
i
∈
S
m
i
t
i
e(C',g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})=e(\hat{\pi},g_2)\cdot g_T^{\alpha^{N+1}\sum_{i\in S}z_it_i}\cdot g_T^{\alpha^{N+1}\sum_{i\in[S]}t_ix_i}=e(\hat{\pi},g_2)\cdot g_T^{\alpha^{N+1}\sum_{i\in S}(z_i+x_i)t_i}=e(\hat{\pi},g_2)\cdot g_T^{\alpha^{N+1}\sum_{i\in S}m_it_i}
e ( C ′ , g 2 ∑ i ∈ S α N + 1 − i t i ) = e ( π ^ , g 2 ) ⋅ g T α N + 1 ∑ i ∈ S z i t i ⋅ g T α N + 1 ∑ i ∈ [ S ] t i x i = e ( π ^ , g 2 ) ⋅ g T α N + 1 ∑ i ∈ S ( z i + x i ) t i = e ( π ^ , g 2 ) ⋅ g T α N + 1 ∑ i ∈ S m i t i
m
i
=
z
i
+
x
i
=
z
i
+
∑
j
∈
[
N
−
1
]
y
j
α
N
+
1
−
i
+
j
m_i=z_i+x_i=z_i+\sum_{j\in[N-1]}y_j\alpha^{N+1-i+j}
m i = z i + x i = z i + ∑ j ∈ [ N − 1 ] y j α N + 1 − i + j
C
′
=
g
1
∑
i
∈
[
N
]
z
i
α
i
+
∑
j
∈
[
N
−
1
]
y
j
α
N
+
1
+
j
C'=g_1^{\sum_{i\in[N]}z_i\alpha^i+\sum_{j\in[N-1]}y_j\alpha^{N+1+j}}
C ′ = g 1 ∑ i ∈ [ N ] z i α i + ∑ j ∈ [ N − 1 ] y j α N + 1 + j
C
=
g
1
∑
i
∈
[
N
]
z
i
α
i
C=g_1^{\sum_{i\in[N]}z_i\alpha^i}
C = g 1 ∑ i ∈ [ N ] z i α i
也就是说,若adversary可找到相应的
C
′
C'
C ′
H
(
i
,
C
,
S
,
m
⃗
[
S
]
)
=
H
(
i
,
C
′
,
S
,
m
⃗
[
S
]
)
H(i,C,S,\vec{m}[S])=H(i,C',S,\vec{m}[S])
H ( i , C , S , m
[ S ] ) = H ( i , C ′ , S , m
[ S ] )
C
′
=
g
1
∑
i
∈
[
N
]
z
i
α
i
+
∑
j
∈
[
N
−
1
]
y
j
α
N
+
1
+
j
且
C
=
g
1
∑
i
∈
[
N
]
z
i
α
i
C'=g_1^{\sum_{i\in[N]}z_i\alpha^i+\sum_{j\in[N-1]}y_j\alpha^{N+1+j}}且C=g_1^{\sum_{i\in[N]}z_i\alpha^i}
C ′ = g 1 ∑ i ∈ [ N ] z i α i + ∑ j ∈ [ N − 1 ] y j α N + 1 + j 且 C = g 1 ∑ i ∈ [ N ] z i α i
e
(
C
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
=
(
e
(
π
^
,
g
2
)
/
e
(
g
1
∑
j
∈
[
N
−
1
]
y
j
α
N
+
1
+
j
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
)
⋅
g
T
α
N
+
1
∑
i
∈
S
m
i
t
i
=
e
(
g
1
,
π
^
∗
)
⋅
g
T
α
N
+
1
∑
i
∈
S
m
i
t
i
e(C,g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})=(e(\hat{\pi},g_2)/e(g_1^{\sum_{j\in[N-1]}y_j\alpha^{N+1+j}},g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i}))\cdot g_T^{\alpha^{N+1}\sum_{i\in S}m_it_i}=e(g_1,\hat{\pi}^*)\cdot g_T^{\alpha^{N+1}\sum_{i\in S}m_it_i}
e ( C , g 2 ∑ i ∈ S α N + 1 − i t i ) = ( e ( π ^ , g 2 ) / e ( g 1 ∑ j ∈ [ N − 1 ] y j α N + 1 + j , g 2 ∑ i ∈ S α N + 1 − i t i ) ) ⋅ g T α N + 1 ∑ i ∈ S m i t i = e ( g 1 , π ^ ∗ ) ⋅ g T α N + 1 ∑ i ∈ S m i t i
e
(
g
1
∑
j
∈
[
N
−
1
]
y
j
α
N
+
1
+
j
,
g
2
∑
i
∈
S
α
N
+
1
−
i
t
i
)
e(g_1^{\sum_{j\in[N-1]}y_j\alpha^{N+1+j}},g_2^{\sum_{i\in S}\alpha^{N+1-i}t_i})
e ( g 1 ∑ j ∈ [ N − 1 ] y j α N + 1 + j , g 2 ∑ i ∈ S α N + 1 − i t i ) 【这段话理解有问题,不应在于Hash碰撞,而在于,应该是对于固定
C
,
S
,
m
⃗
[
S
]
C,S,\vec{m}[S]
C , S , m
[ S ]
z
⃗
和
y
⃗
\vec{z}和\vec{y}
z
和 y
C
=
g
1
z
⃗
T
a
⃗
+
α
N
y
⃗
T
a
⃗
[
−
1
]
C=g_1^{\vec{z}^T\vec{a}+\alpha^N\vec{y}^T\vec{a}[-1]}
C = g 1 z
T a
+ α N y
T a
[ − 1 ]
m
⃗
[
S
]
̸
≡
p
z
⃗
[
S
]
且
(
m
⃗
[
S
]
−
z
⃗
[
S
]
)
T
t
⃗
≡
p
0
\vec{m}[S]\not\equiv_p\vec{z}[S]且(\vec{m}[S]-\vec{z}[S])^T\vec{t}\equiv_p 0
m
[ S ] ≡ p z
[ S ] 且 ( m
[ S ] − z
[ S ] ) T t
≡ p 0
z
⃗
和
y
⃗
\vec{z}和\vec{y}
z
和 y
C
C
C
π
^
∗
\hat{\pi}^*
π ^ ∗
z
⃗
[
S
]
\vec{z}[S]
z
[ S ]
m
⃗
[
S
]
\vec{m}[S]
m
[ S ]
由于
Pr
t
⃗
[
z
⃗
[
S
]
̸
≡
p
m
⃗
[
S
]
a
n
d
z
⃗
[
S
]
T
t
⃗
≡
p
m
⃗
[
S
]
T
t
⃗
]
=
1
/
p
,
其
中
t
⃗
=
(
H
(
i
,
C
,
S
,
m
⃗
[
S
]
)
:
i
∈
S
)
\Pr_{\vec{t}}[\vec{z}[S]\not\equiv_p \vec{m}[S]\ and\ \vec{z}[S]^T\vec{t}\equiv_p \vec{m}[S]^T\vec{t}]=1/p,其中\vec{t}=(H(i,C,S,\vec{m}[S]):i\in S)
Pr t
[ z
[ S ] ≡ p m
[ S ] a n d z
[ S ] T t
≡ p m
[ S ] T t
] = 1 / p , 其 中 t
= ( H ( i , C , S , m
[ S ] ) : i ∈ S )
(
S
,
m
⃗
[
S
]
,
z
⃗
[
S
]
)
(S,\vec{m}[S],\vec{z}[S])
( S , m
[ S ] , z
[ S ] )
C
′
C'
C ′
H
(
i
,
C
,
S
,
m
⃗
[
S
]
)
=
H
(
i
,
C
′
,
S
,
m
⃗
[
S
]
)
H(i,C,S,\vec{m}[S])=H(i,C',S,\vec{m}[S])
H ( i , C , S , m
[ S ] ) = H ( i , C ′ , S , m
[ S ] )
z
⃗
∈
Z
p
N
,
y
⃗
∈
Z
p
N
−
1
\vec{z}\in \mathbb{Z}_p^N,\vec{y}\in\mathbb{Z}_p^{N-1}
z
∈ Z p N , y
∈ Z p N − 1
C
′
=
g
1
∑
i
∈
[
N
]
z
i
α
i
+
∑
j
∈
[
N
−
1
]
y
j
α
N
+
1
+
j
,
C
=
g
1
∑
i
∈
[
N
]
z
i
α
i
C'=g_1^{\sum_{i\in[N]}z_i\alpha^i+\sum_{j\in[N-1]}y_j\alpha^{N+1+j}},C=g_1^{\sum_{i\in[N]}z_i\alpha^i}
C ′ = g 1 ∑ i ∈ [ N ] z i α i + ∑ j ∈ [ N − 1 ] y j α N + 1 + j , C = g 1 ∑ i ∈ [ N ] z i α i
1
/
p
1/p
1 / p
By the union bound, the probability that an adversary makes an H-lucky query is at most
q
H
/
p
q_H/p
q H / p
q
H
q_H
q H
H
H
H
2)若可extracting
g
1
α
N
+
1
g_1^{\alpha^{N+1}}
g 1 α N + 1
l
l
l
若对于
C
=
g
1
z
⃗
T
a
⃗
+
α
N
y
⃗
T
a
⃗
[
−
1
]
=
g
1
∑
i
∈
[
N
]
z
i
α
i
+
∑
j
∈
[
N
−
1
]
y
j
α
N
+
1
+
j
C=g_1^{\vec{z}^T\vec{a}+\alpha^N\vec{y}^T\vec{a}[-1]}=g_1^{\sum_{i\in[N]}z_i\alpha^i+\sum_{j\in[N-1]}y_j\alpha^{N+1+j}}
C = g 1 z
T a
+ α N y
T a
[ − 1 ] = g 1 ∑ i ∈ [ N ] z i α i + ∑ j ∈ [ N − 1 ] y j α N + 1 + j
(
S
∗
,
m
⃗
∗
,
π
^
∗
)
(S^*,\vec{m}^*,\hat{\pi}^*)
( S ∗ , m
∗ , π ^ ∗ )
m
⃗
∗
[
S
∗
]
≠
z
⃗
[
S
∗
]
且
V
e
r
i
f
y
(
C
,
S
∗
,
m
⃗
∗
[
S
∗
]
,
π
^
∗
)
\vec{m}^*[S^*]\neq \vec{z}[S^*] 且 Verify(C,S^*,\vec{m}^*[S^*],\hat{\pi}^*)
m
∗ [ S ∗ ] = z
[ S ∗ ] 且 V e r i f y ( C , S ∗ , m
∗ [ S ∗ ] , π ^ ∗ )
即有
e
(
C
,
g
2
∑
i
∈
S
∗
α
N
+
1
−
i
t
i
)
=
e
(
π
^
∗
,
g
2
)
⋅
g
T
α
N
+
1
m
⃗
∗
[
S
∗
]
T
t
⃗
e(C,g_2^{\sum_{i\in S^*}\alpha^{N+1-i}t_i})=e(\hat{\pi}^*,g_2)\cdot g_T^{\alpha^{N+1}\vec{m}^*[S^*]^T\vec{t}}
e ( C , g 2 ∑ i ∈ S ∗ α N + 1 − i t i ) = e ( π ^ ∗ , g 2 ) ⋅ g T α N + 1 m
∗ [ S ∗ ] T t
t
i
=
H
(
i
,
C
,
S
∗
,
m
⃗
∗
[
S
∗
]
)
t_i=H(i,C,S^*,\vec{m}^*[S^*])
t i = H ( i , C , S ∗ , m
∗ [ S ∗ ] )
于是有:
C
∑
i
∈
S
∗
α
N
+
1
−
i
t
i
=
π
^
∗
⋅
g
1
α
N
+
1
m
⃗
∗
[
S
∗
]
T
t
⃗
C^{\sum_{i\in S^*}\alpha^{N+1-i}t_i}=\hat{\pi}^*\cdot g_1^{\alpha^{N+1}\vec{m}^*[S^*]^T\vec{t}}
C ∑ i ∈ S ∗ α N + 1 − i t i = π ^ ∗ ⋅ g 1 α N + 1 m
∗ [ S ∗ ] T t
上述等式左侧展开为含
g
1
α
N
+
1
g_1^{\alpha^{N+1}}
g 1 α N + 1
g
1
α
N
+
1
g_1^{\alpha^{N+1}}
g 1 α N + 1
C
∑
i
∈
S
∗
α
N
+
1
−
i
t
i
=
g
1
(
z
⃗
T
a
⃗
+
α
N
y
⃗
T
a
⃗
[
−
1
]
)
⋅
∑
i
∈
S
∗
α
N
+
1
−
i
t
i
C^{\sum_{i\in S^*}\alpha^{N+1-i}t_i}=g_1^{(\vec{z}^T\vec{a}+\alpha^N\vec{y}^T\vec{a}[-1])\cdot \sum_{i\in S^*}\alpha^{N+1-i}t_i}
C ∑ i ∈ S ∗ α N + 1 − i t i = g 1 ( z
T a
+ α N y
T a
[ − 1 ] ) ⋅ ∑ i ∈ S ∗ α N + 1 − i t i
The smallest
i
i
i
1
1
1
(1)
z
⃗
T
a
⃗
∑
i
∈
S
∗
α
N
+
1
−
i
t
i
=
∑
i
∈
S
∗
z
⃗
T
a
⃗
α
N
+
1
−
i
t
i
=
∑
i
∈
S
∗
(
z
i
α
i
+
z
⃗
[
−
i
]
a
⃗
[
−
i
]
)
α
N
+
1
−
i
t
i
=
α
N
+
1
∑
i
∈
S
∗
z
i
t
i
+
∑
i
∈
S
∗
α
N
+
1
−
i
z
⃗
[
−
i
]
a
⃗
[
−
i
]
t
i
\vec{z}^T\vec{a}\sum_{i\in S^*}\alpha^{N+1-i}t_i=\sum_{i\in S^*}\vec{z}^T\vec{a}\alpha^{N+1-i}t_i =\sum_{i\in S^*}(z_i\alpha^i+\vec{z}[-i]\vec{a}[-i])\alpha^{N+1-i}t_i=\alpha^{N+1}\sum_{i\in S^*}z_it_i+\sum_{i\in S^*}\alpha^{N+1-i}\vec{z}[-i]\vec{a}[-i]t_i
z
T a
∑ i ∈ S ∗ α N + 1 − i t i = ∑ i ∈ S ∗ z
T a
α N + 1 − i t i = ∑ i ∈ S ∗ ( z i α i + z
[ − i ] a
[ − i ] ) α N + 1 − i t i = α N + 1 ∑ i ∈ S ∗ z i t i + ∑ i ∈ S ∗ α N + 1 − i z
[ − i ] a
[ − i ] t i
其中
∑
i
∈
S
∗
α
N
+
1
−
i
z
⃗
[
−
i
]
a
⃗
[
−
i
]
t
i
\sum_{i\in S^*}\alpha^{N+1-i}\vec{z}[-i]\vec{a}[-i]t_i
∑ i ∈ S ∗ α N + 1 − i z
[ − i ] a
[ − i ] t i
g
1
α
,
g
1
α
2
,
⋯
,
g
1
α
N
,
g
1
α
N
+
2
,
⋯
,
g
1
α
2
N
g_1^{\alpha},g_1^{\alpha^2},\cdots,g_1^{\alpha^N},g_1^{\alpha^{N+2}},\cdots,g_1^{\alpha^{2N}}
g 1 α , g 1 α 2 , ⋯ , g 1 α N , g 1 α N + 2 , ⋯ , g 1 α 2 N
(2)
α
N
y
⃗
T
a
⃗
[
−
1
]
)
⋅
∑
i
∈
S
∗
α
N
+
1
−
i
t
i
\alpha^N\vec{y}^T\vec{a}[-1])\cdot \sum_{i\in S^*}\alpha^{N+1-i}t_i
α N y
T a
[ − 1 ] ) ⋅ ∑ i ∈ S ∗ α N + 1 − i t i
g
1
α
N
+
3
,
⋯
,
g
1
α
3
N
g_1^{\alpha^{N+3}},\cdots,g_1^{\alpha^{3N}}
g 1 α N + 3 , ⋯ , g 1 α 3 N
For :
C
∑
i
∈
S
∗
α
N
+
1
−
i
t
i
=
π
^
∗
⋅
g
1
α
N
+
1
m
⃗
∗
[
S
∗
]
T
t
⃗
C^{\sum_{i\in S^*}\alpha^{N+1-i}t_i}=\hat{\pi}^*\cdot g_1^{\alpha^{N+1}\vec{m}^*[S^*]^T\vec{t}}
C ∑ i ∈ S ∗ α N + 1 − i t i = π ^ ∗ ⋅ g 1 α N + 1 m
∗ [ S ∗ ] T t
Then:
(
g
1
∑
i
∈
S
∗
,
j
∈
S
∗
,
i
≠
j
z
j
t
i
α
N
+
1
−
i
+
j
)
⋅
(
g
1
z
⃗
[
−
S
∗
]
T
a
⃗
[
−
S
∗
]
⋅
∑
i
∈
S
∗
α
N
+
1
−
i
t
i
)
⋅
(
g
1
α
N
y
⃗
T
a
⃗
[
−
1
]
)
⋅
∑
i
∈
S
∗
α
N
+
1
−
i
t
i
)
⋅
(
π
^
∗
)
−
1
=
g
1
α
N
+
1
∑
i
∈
S
∗
(
m
i
−
z
i
)
t
i
(g_1^{\sum_{i\in S^*,j\in S^*,i\neq j}z_jt_i\alpha^{N+1-i+j}})\cdot(g_1^{\vec{z}[-S^*]^T\vec{a}[-S^*]\cdot{\sum_{i\in S^*}\alpha^{N+1-i}t_i}})\cdot(g_1^{\alpha^N\vec{y}^T\vec{a}[-1])\cdot \sum_{i\in S^*}\alpha^{N+1-i}t_i})\cdot (\hat{\pi}^*)^{-1}=g_1^{\alpha^{N+1}\sum_{i \in S^*}(m_i-z_i)t_i}
( g 1 ∑ i ∈ S ∗ , j ∈ S ∗ , i = j z j t i α N + 1 − i + j ) ⋅ ( g 1 z
[ − S ∗ ] T a
[ − S ∗ ] ⋅ ∑ i ∈ S ∗ α N + 1 − i t i ) ⋅ ( g 1 α N y
T a
[ − 1 ] ) ⋅ ∑ i ∈ S ∗ α N + 1 − i t i ) ⋅ ( π ^ ∗ ) − 1 = g 1 α N + 1 ∑ i ∈ S ∗ ( m i − z i ) t i
当不存在H-lucky queries,且adversary可成功将
z
⃗
[
S
∗
]
\vec{z}[S^*]
z
[ S ∗ ]
m
⃗
[
S
∗
]
\vec{m}[S^*]
m
[ S ∗ ]
g
1
α
N
+
1
g_1^{\alpha^{N+1}}
g 1 α N + 1
z
⃗
[
S
∗
]
≠
m
⃗
[
S
∗
]
\vec{z}[S^*]\neq \vec{m}[S^*]
z
[ S ∗ ] = m
[ S ∗ ]
∑
i
∈
S
∗
(
m
i
−
z
i
)
t
i
̸
≡
p
0
\sum_{i \in S^*}(m_i-z_i)t_i\not\equiv_p 0
∑ i ∈ S ∗ ( m i − z i ) t i ≡ p 0
r
=
1
/
(
∑
i
∈
S
∗
(
m
i
−
z
i
)
t
i
)
m
o
d
p
r=1/(\sum_{i \in S^*}(m_i-z_i)t_i)\mod p
r = 1 / ( ∑ i ∈ S ∗ ( m i − z i ) t i ) m o d p
r
r
r
g
1
α
N
+
1
g_1^{\alpha^{N+1}}
g 1 α N + 1
⇒
\Rightarrow
⇒
g
1
α
N
+
1
g_1^{\alpha^{N+1}}
g 1 α N + 1
l
l
l
Aggregation of proofs across
l
l
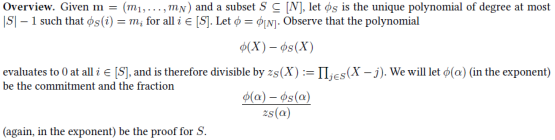
l AggregateAcross和VerifyAcross算法,具体的实现为:
AggregateAcross(
{
C
j
,
S
j
,
m
⃗
j
[
S
j
]
,
π
^
j
}
j
∈
[
l
]
\{C_j,S_j,\vec{m}_j[S_j],\hat{\pi}_j\}_{j\in [l]}
{ C j , S j , m
j [ S j ] , π ^ j } j ∈ [ l ]
π
=
∏
j
=
1
l
π
^
j
t
j
′
\pi=\prod_{j=1}^{l}\hat{\pi}_j^{t_j'}
π = ∏ j = 1 l π ^ j t j ′
t
j
’
=
H
’
(
j
,
{
C
j
,
S
j
,
m
⃗
j
[
S
j
]
}
j
∈
[
l
]
)
t_j’=H’(j,\{C_j,S_j,\vec{m}_j[S_j]\}_{j\in[l]})
t j ’ = H ’ ( j , { C j , S j , m
j [ S j ] } j ∈ [ l ] )
VerifyAcross(
{
C
j
,
S
j
,
m
⃗
j
}
j
∈
[
l
]
,
π
\{C_j,S_j,\vec{m}_j\}_{j\in[l]},\pi
{ C j , S j , m
j } j ∈ [ l ] , π
∏
j
=
1
l
e
(
C
j
,
g
2
∑
i
∈
S
j
α
N
+
1
−
i
t
j
,
i
)
t
j
′
=
e
(
π
,
g
2
)
⋅
g
T
α
N
+
1
∑
j
∈
[
l
]
,
i
∈
S
j
m
j
,
i
t
j
,
i
t
j
′
\prod_{j=1}^{l}e(C_j,g_2^{\sum_{i\in S_j}\alpha^{N+1-i}t_{j,i}})^{t_j'}=e(\pi,g_2)\cdot g_T^{\alpha^{N+1}\sum_{j\in[l],i\in S_j}m_{j,i}t_{j,i}t_j'}
∏ j = 1 l e ( C j , g 2 ∑ i ∈ S j α N + 1 − i t j , i ) t j ′ = e ( π , g 2 ) ⋅ g T α N + 1 ∑ j ∈ [ l ] , i ∈ S j m j , i t j , i t j ′
t
j
,
i
=
H
(
i
,
C
j
,
S
j
,
m
⃗
j
[
S
j
]
)
t_{j,i}=H(i,C_j,S_j,\vec{m}_j[S_j])
t j , i = H ( i , C j , S j , m
j [ S j ] )
t
j
′
=
H
′
(
j
,
{
C
j
,
S
j
,
m
⃗
j
[
S
j
]
}
j
∈
[
l
]
)
t_j'=H'(j,\{C_j,S_j,\vec{m}_j[S_j]\}_{j\in[l]})
t j ′ = H ′ ( j , { C j , S j , m
j [ S j ] } j ∈ [ l ] )
m
⃗
j
=
(
m
j
,
1
,
⋯
,
m
j
,
N
)
\vec{m}_j=(m_{j,1},\cdots,m_{j,N})
m
j = ( m j , 1 , ⋯ , m j , N )
采用2.2类似的方式,证明
π
^
j
\hat{\pi}_j
π ^ j
π
^
j
\hat{\pi}_j
π ^ j
j
j
j
t
j
′
t_j'
t j ′
j
∈
[
l
]
j\in[l]
j ∈ [ l ]
分三步实现:
C
,
S
,
m
⃗
[
S
]
C,S,\vec{m}[S]
C , S , m
[ S ]
z
⃗
和
y
⃗
\vec{z}和\vec{y}
z
和 y
C
=
g
1
z
⃗
T
a
⃗
+
α
N
y
⃗
T
a
⃗
[
−
1
]
C=g_1^{\vec{z}^T\vec{a}+\alpha^N\vec{y}^T\vec{a}[-1]}
C = g 1 z
T a
+ α N y
T a
[ − 1 ]
m
⃗
[
S
]
̸
≡
p
z
⃗
[
S
]
且
(
m
⃗
[
S
]
−
z
⃗
[
S
]
)
T
t
⃗
≡
p
0
\vec{m}[S]\not\equiv_p\vec{z}[S]且(\vec{m}[S]-\vec{z}[S])^T\vec{t}\equiv_p 0
m
[ S ] ≡ p z
[ S ] 且 ( m
[ S ] − z
[ S ] ) T t
≡ p 0
z
⃗
和
y
⃗
\vec{z}和\vec{y}
z
和 y
(
S
,
m
⃗
[
S
]
,
z
⃗
[
S
]
)
(S,\vec{m}[S],\vec{z}[S])
( S , m
[ S ] , z
[ S ] )
m
⃗
[
S
]
≡
p
z
⃗
[
S
]
\vec{m}[S]\equiv_p \vec{z}[S]
m
[ S ] ≡ p z
[ S ]
(
m
⃗
[
S
]
−
z
⃗
[
S
]
)
T
t
⃗
≡
p
0
(\vec{m}[S]-\vec{z}[S])^T\vec{t}\equiv_p 0
( m
[ S ] − z
[ S ] ) T t
≡ p 0
1
/
p
1/p
1 / p
2)bounding “H’-lucky” queries:
l
l
l
{
(
S
j
,
m
⃗
j
[
S
j
]
,
z
⃗
j
[
S
j
]
)
j
∈
[
l
]
}
\{(S_j,\vec{m}_j[S_j],\vec{z}_j[S_j])_{j\in[l]}\}
{ ( S j , m
j [ S j ] , z
j [ S j ] ) j ∈ [ l ] }
∃
j
:
(
m
⃗
j
[
S
j
]
−
z
⃗
j
[
S
j
]
)
T
t
⃗
j
̸
≡
p
0
\exists j: (\vec{m}_j[S_j]-\vec{z}_j[S_j])^T\vec{t}_j\not\equiv_p 0
∃ j : ( m
j [ S j ] − z
j [ S j ] ) T t
j ≡ p 0
∑
j
=
1
l
(
m
⃗
j
[
S
j
]
−
z
⃗
j
[
S
j
]
)
T
t
⃗
j
t
j
’
≡
p
0
\sum_{j=1}^{l}(\vec{m}_j[S_j]-\vec{z}_j[S_j])^T\vec{t}_jt_j’\equiv_p 0
∑ j = 1 l ( m
j [ S j ] − z
j [ S j ] ) T t
j t j ’ ≡ p 0
1
/
p
1/p
1 / p
3)extracting
g
1
α
N
+
1
g_1^{\alpha^{N+1}}
g 1 α N + 1
l
=
1
l=1
l = 1
t
1
’
=
1
t_1’=1
t 1 ’ = 1 Verify算法即可,extracting
g
1
α
N
+
1
g_1^{\alpha^{N+1}}
g 1 α N + 1
l
l
l
m
⃗
j
∗
∗
[
S
j
∗
∗
]
\vec{m}_{j^*}^*[S_{j^*}^*]
m
j ∗ ∗ [ S j ∗ ∗ ]
z
⃗
j
∗
∗
[
S
j
∗
∗
]
\vec{z}_{j^*}^*[S_{j^*}^*]
z
j ∗ ∗ [ S j ∗ ∗ ] VerifyAcross算法验证通过,基本思路与2.3.2节第二步类似。
(
m
⃗
j
∗
∗
[
S
j
∗
∗
]
−
z
⃗
j
∗
∗
[
S
j
∗
∗
]
)
T
t
⃗
j
∗
̸
≡
p
0
(\vec{m}_{j^*}^*[S_{j^*}^*]-\vec{z}_{j^*}^*[S_{j^*}^*])^T\vec{t}_{j*}\not\equiv_p 0
( m
j ∗ ∗ [ S j ∗ ∗ ] − z
j ∗ ∗ [ S j ∗ ∗ ] ) T t
j ∗ ≡ p 0
∑
h
=
1
l
∗
(
m
⃗
j
∗
[
S
j
∗
]
−
z
⃗
j
∗
[
S
j
∗
]
)
T
t
⃗
j
t
j
’
̸
≡
p
0
\sum_{h=1}^{l^*}(\vec{m}_j^*[S_j^*]-\vec{z}_j^*[S_j^*])^T\vec{t}_jt_j’\not\equiv_p 0
∑ h = 1 l ∗ ( m
j ∗ [ S j ∗ ] − z
j ∗ [ S j ∗ ] ) T t
j t j ’ ≡ p 0
则该adversary可采用2.3.2节第二步类似的方式计算出相应的
g
1
α
N
+
1
g_1^{\alpha^{N+1}}
g 1 α N + 1
l
l
l
采用Dario Catalano 和 Dario Fiore 2013年论文《Vector Commitments and their Applications 》类似思路(可参见博客Vector Commitments and their Applications学习笔记 第2.1节“基于CDH的Vector Commitment实现”内容)以及 Russell W. F. Lai 和 Giulio Malavolta 在Crypto 2019上发表的论文《Subvector Commitments with Application to Succinct Arguments 》(参见博客 subvector commitment based on CubeDH assumption over pairing group 第4节“”内容),本文使用的是非对称pairing bilinear group。
采用CDH assumption,所需要的public parameter size为
O
(
N
2
)
O(N^2)
O ( N 2 )
在非对称pairing bilinear group中,本文用到的CDH-like static assumption为:
{
g
1
u
i
,
g
2
v
i
}
i
∈
[
N
]
,
{
g
1
u
j
v
i
}
i
≠
j
\{g_1^{u_i},g_2^{v_i}\}_{i\in [N]},\{g_1^{u_jv_i}\}_{i\neq j}
{ g 1 u i , g 2 v i } i ∈ [ N ] , { g 1 u j v i } i = j
g
T
u
i
v
i
2
g_T^{u_iv_i^2}
g T u i v i 2
具体的实现为:
Setup(
1
λ
,
1
N
1^{\lambda},1^N
1 λ , 1 N
N
N
N
u
i
,
v
i
←
Z
p
u_i,v_i\leftarrow \mathbb{Z}_p
u i , v i ← Z p
{
g
1
u
i
,
g
2
v
i
}
i
∈
[
N
]
,
{
g
1
u
j
v
i
}
i
≠
j
\{g_1^{u_i},g_2^{v_i}\}_{i\in [N]},\{g_1^{u_jv_i}\}_{i\neq j}
{ g 1 u i , g 2 v i } i ∈ [ N ] , { g 1 u j v i } i = j
Commit(
m
⃗
\vec{m}
m
C
=
g
1
∑
i
∈
[
N
]
m
i
u
i
C=g_1^{\sum_{i\in[N]}m_iu_i}
C = g 1 ∑ i ∈ [ N ] m i u i
UpdateCommit(
C
,
S
,
m
⃗
[
S
]
,
m
⃗
’
[
S
]
C,S,\vec{m}[S],\vec{m}’[S]
C , S , m
[ S ] , m
’ [ S ]
C
’
=
C
⋅
g
1
∑
i
∈
S
(
m
i
’
−
m
i
)
u
i
C’=C\cdot g_1^{\sum_{i\in S}(m_i’-m_i)u_i}
C ’ = C ⋅ g 1 ∑ i ∈ S ( m i ’ − m i ) u i
Prove(
i
,
m
⃗
i,\vec{m}
i , m
π
i
=
g
1
∑
j
≠
i
m
j
u
j
v
i
\pi_i=g_1^{\sum_{j\neq i}m_ju_jv_i}
π i = g 1 ∑ j = i m j u j v i
Aggregate(
C
,
S
,
m
⃗
[
S
]
,
{
π
i
:
i
∈
S
}
C,S,\vec{m}[S],\{\pi_i:i\in S\}
C , S , m
[ S ] , { π i : i ∈ S }
π
^
=
∏
i
∈
S
π
i
\hat{\pi}=\prod_{i\in S}\pi_i
π ^ = ∏ i ∈ S π i
Verify(
C
,
S
,
m
⃗
[
S
]
,
π
^
C,S,\vec{m}[S],\hat{\pi}
C , S , m
[ S ] , π ^
e
(
C
,
g
2
∑
i
∈
S
v
i
)
=
e
(
π
^
,
g
2
)
⋅
g
T
∑
i
∈
S
m
i
u
i
v
i
e(C,g_2^{\sum_{i\in S}v_i})=e(\hat{\pi},g_2)\cdot g_T^{\sum_{i\in S}m_iu_iv_i}
e ( C , g 2 ∑ i ∈ S v i ) = e ( π ^ , g 2 ) ⋅ g T ∑ i ∈ S m i u i v i
注意:Subvector Commitments with Application to Succinct Arguments 》(参见博客 subvector commitment based on CubeDH assumption over pairing group 第4节“”内容)中,所采用的是
u
i
=
v
i
u_i=v_i
u i = v i
u
i
=
v
i
u_i=v_i
u i = v i
verify公式为:
e
(
C
,
g
2
∑
i
∈
S
v
i
)
=
e
(
π
^
,
g
2
)
⋅
g
T
∑
i
∈
S
m
i
u
i
v
i
e(C,g_2^{\sum_{i\in S}v_i})=e(\hat{\pi},g_2)\cdot g_T^{\sum_{i\in S}m_iu_iv_i}
e ( C , g 2 ∑ i ∈ S v i ) = e ( π ^ , g 2 ) ⋅ g T ∑ i ∈ S m i u i v i
(
∑
j
∈
[
N
]
m
j
u
j
)
⋅
v
i
=
m
i
u
i
v
i
+
∑
j
≠
i
m
j
u
j
v
i
(\sum_{j\in[N]}m_ju_j)\cdot v_i=m_iu_iv_i+\sum_{j\neq i}m_ju_jv_i
( ∑ j ∈ [ N ] m j u j ) ⋅ v i = m i u i v i + ∑ j = i m j u j v i
i
∈
S
i\in S
i ∈ S
若对于
C
,
{
S
b
,
m
⃗
b
[
S
b
]
,
π
^
b
}
b
=
0
,
1
C,\{S^b,\vec{m}^b[S^b],\hat{\pi}^b\}_{b=0,1}
C , { S b , m
b [ S b ] , π ^ b } b = 0 , 1
i
∗
i^*
i ∗
m
i
∗
0
≠
m
i
∗
1
m_{i^*}^0\neq m_{i^*}^1
m i ∗ 0 = m i ∗ 1
verify公式为:
e
(
C
,
g
2
∑
i
∈
S
v
i
)
=
e
(
π
^
,
g
2
)
⋅
g
T
∑
i
∈
S
m
i
u
i
v
i
e(C,g_2^{\sum_{i\in S}v_i})=e(\hat{\pi},g_2)\cdot g_T^{\sum_{i\in S}m_iu_iv_i}
e ( C , g 2 ∑ i ∈ S v i ) = e ( π ^ , g 2 ) ⋅ g T ∑ i ∈ S m i u i v i
∑
i
∈
S
v
i
\sum_{i\in S}v_i
∑ i ∈ S v i
v
S
v_S
v S
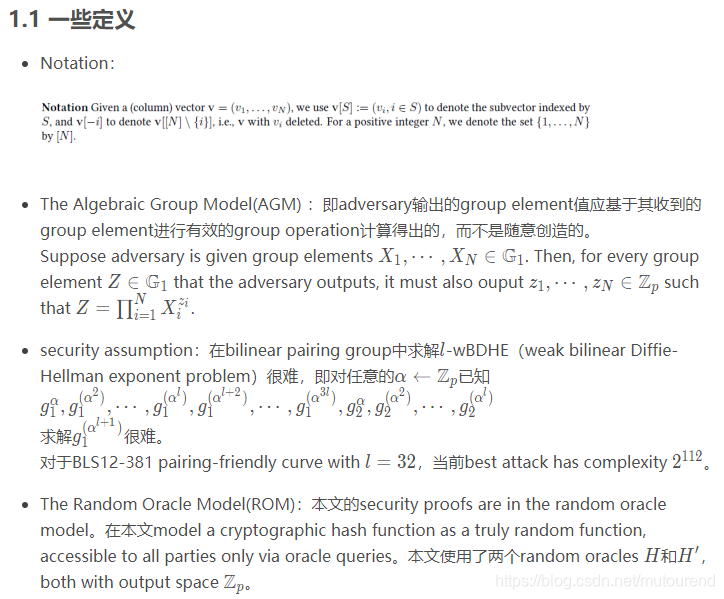
e
(
C
,
g
2
v
S
0
)
=
e
(
π
^
0
,
g
2
)
⋅
g
T
∑
i
∈
S
0
m
i
0
u
i
v
i
e(C,g_2^{v_{S^0}})=e(\hat{\pi}^0,g_2)\cdot g_T^{\sum_{i\in S^0}m_i^0u_iv_i}
e ( C , g 2 v S 0 ) = e ( π ^ 0 , g 2 ) ⋅ g T ∑ i ∈ S 0 m i 0 u i v i
e
(
C
,
g
2
v
S
1
)
=
e
(
π
^
1
,
g
2
)
⋅
g
T
∑
i
∈
S
1
m
i
1
u
i
v
i
e(C,g_2^{v_{S^1}})=e(\hat{\pi}^1,g_2)\cdot g_T^{\sum_{i\in S^1}m_i^1u_iv_i}
e ( C , g 2 v S 1 ) = e ( π ^ 1 , g 2 ) ⋅ g T ∑ i ∈ S 1 m i 1 u i v i
v
S
1
v_{S^1}
v S 1
v
S
0
v_{S^0}
v S 0
e
(
π
^
0
,
g
2
v
S
1
)
⋅
g
T
v
S
1
∑
i
∈
S
0
m
i
0
u
i
v
i
=
e
(
π
^
1
,
g
2
v
S
0
)
⋅
g
T
v
S
0
∑
i
∈
S
1
m
i
1
u
i
v
i
e(\hat{\pi}^0,g_2^{v_{S^1}})\cdot g_T^{v_{S^1}\sum_{i\in S^0}m_i^0u_iv_i}= e(\hat{\pi}^1,g_2^{v_{S^0}})\cdot g_T^{v_{S^0}\sum_{i\in S^1}m_i^1u_iv_i}
e ( π ^ 0 , g 2 v S 1 ) ⋅ g T v S 1 ∑ i ∈ S 0 m i 0 u i v i = e ( π ^ 1 , g 2 v S 0 ) ⋅ g T v S 0 ∑ i ∈ S 1 m i 1 u i v i
i
∗
i^*
i ∗
m
i
∗
1
−
m
i
∗
0
≠
0
m_{i^*}^1 - m_{i^*}^0\neq 0
m i ∗ 1 − m i ∗ 0 = 0
g
t
u
i
∗
v
i
∗
2
g_t^{u_{i^*}v_{i^*}^2}
g t u i ∗ v i ∗ 2
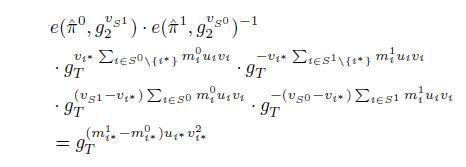
weak binding是指adversary (输入任意消息)honestly执行了Commit运算来生成commitment
C
C
C
C
C
C
对于
C
,
m
⃗
,
r
,
(
π
^
,
S
,
m
⃗
∗
[
S
]
)
C,\vec{m},r,(\hat{\pi},S,\vec{m}^*[S])
C , m
, r , ( π ^ , S , m
∗ [ S ] )
C
=
C
o
m
m
i
t
(
m
⃗
;
r
)
C=Commit(\vec{m};r)
C = C o m m i t ( m
; r )
V
e
r
i
f
y
(
C
,
S
,
m
⃗
∗
[
S
]
,
π
^
)
=
1
Verify(C,S,\vec{m}^*[S],\hat{\pi})=1
V e r i f y ( C , S , m
∗ [ S ] , π ^ ) = 1
m
⃗
[
S
]
≠
m
⃗
∗
[
S
]
\vec{m}[S]\neq\vec{m}^*[S]
m
[ S ] = m
∗ [ S ]
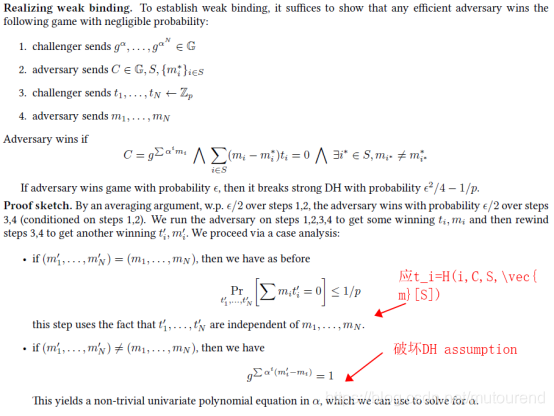
Challenger与Adversary之间相互交互:【借助same-commitment aggregation中proof of binding思路】
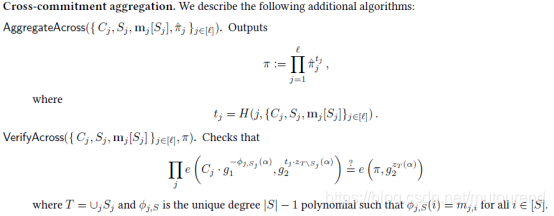
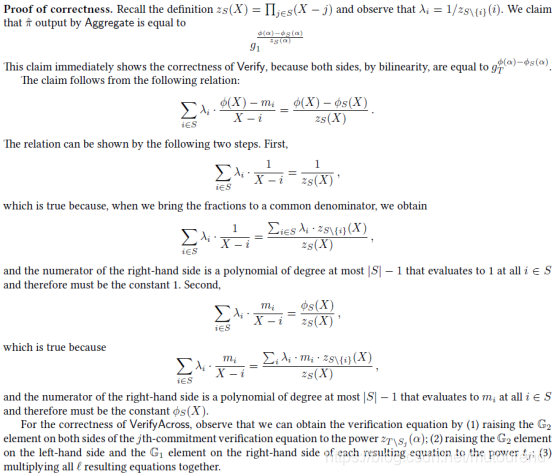
在Boneh, Drake, Fisch, and Gabizon 2020年论文《Efficient polynomial commitment schemes for multiple points and polynomials 》 (基于Kate等人2010年论文《Constant-size commitments to polynomials and their applications 》和Maller等人2019年论文《Sonic: Zero-knowledge SNARKs from linear-size universal and updatable structured reference strings 》)的第3节算法的基础上,本文利用polynomial commitment 实现了支持cross-commitment aggregation 的vector commitment。
[Gab20] 中指出,polynomial commitment初始设计时并不支持efficient updates,在本文中,可通过a bit of precomputation 来支持efficient update。其它算法的执行效率基本相当(up to constant factors),除了VerifyAcross算法,需要额外增加
Θ
(
l
N
)
\Theta(lN)
Θ ( l N )
Boneh, Drake, Fisch, and Gabizon [BDFG20] 2020年论文《Efficient polynomial commitment schemes for multiple points and polynomials 》第4节的算法执行效率更高,但是该算法似乎无法支持cross-commitment aggregation。【because the second element of the proof (denoted
W
’
W’
W ’
π
\pi
π AggregateAcross below and
W
W
W
Binding holds under a
q
q
q Efficient polynomial commitment schemes for multiple points and polynomials 》第3节内容。