在Apache上配置防盗链功能
安装DNS服务
[root@localhost opt]# yum -y install bind
[root@localhost opt]# vi /etc/named.conf
options {
listen-on port 53 { any; };
listen-on-v6 port 53 { ::1; };
directory "/var/named";
dump-file "/var/named/data/cache_dump.db";
statistics-file "/var/named/data/named_stats.txt";
memstatistics-file "/var/named/data/named_mem_stats.txt";
recursing-file "/var/named/data/named.recursing";
secroots-file "/var/named/data/named.secroots";
allow-query { any; }
root@localhost named]# vim /etc/named.rfc1912.zones
};
zone "kgc.com" IN {
type master;
file "kgc.com.zone";
allow-update { none; };
};
[root@localhost opt]# cd /var/named/
[root@localhost named]# cp -p named.localhost kgc.com.zone
www IN A 192.168.136.10
[root@localhost named]# systemctl start named
查看DNS解析是否生效
配置http服务软件目录
实验所需要的三个软件包的下载地址:
httpd-2.4.25:https://wwa.lanzous.com/i0VcXebkl6h
apr-util-1.4.1:https://wwa.lanzous.com/i8Cbjebkl3e
apr-1.4.6:https://wwa.lanzous.com/iR5Orebkl0b
[root@localhost opt]# tar jxvf httpd-2.4.29.tar.bz2
[root@localhost opt]# tar zxvf apr-1.6.2.tar.gz
[root@localhost opt]# tar zxvf apr-util-1.6.0.tar.gz
[root@localhost opt]# mv apr-1.6.2 httpd-2.4.29/srclib/apr
[root@localhost opt]# mv apr-util-1.6.0 httpd-2.4.29/srclib/apr-util
安装必须的依赖及编译环境
yum -y install gcc gcc-c++ pcre pcre-devel perl expat-devel zlib-devel
[root@localhost named]# cd /opt/httpd-2.4.29/
配置http服务安装脚本:
./configure \
--prefix=/usr/local/httpd \
--enable-deflate \
--enable-so \
--enable-rewrite \
--enable-charset-lite \
--enable-cgi
[root@localhost httpd-2.4.29]# ln -s /usr/local/httpd/conf/httpd.conf /etc
建立软连接
[root@localhost httpd-2.4.29]# ln -s /usr/local/httpd/conf/httpd.conf /etc/httpd.conf
http配置文件中修改
[root@localhost httpd-2.4.29]# vim /etc/httpd.conf
ServerName www.kgc.com:80
Listen 192.168.136.10:80
#Listen 80
进入站点目录,修改站点页面文件
[root@localhost httpd-2.4.29]# cd /usr/local/httpd/htdocs/
[root@localhost htdocs]# ll
-rw-r--r--. 1 root root 88108 8月 6 10:23 kgc.jpg
[root@localhost htdocs]# vim index.html
<h1>this is web</h1>
<img src="kgc.jpg"/>
开启服务
cd /usr/local/httpd/bin ## 进入http命令存放目录
停止服务:
[root@localhost bin]# ./apachectl stop
启动服务:
[root@localhost bin]# ./apachectl start
部署盗链服务器
[root@localhost ~]# yum -y install httpd
[root@localhost ~]#vim /etc/http/conf/httpd.conf
Listen 192.168.136.20:80
#Listen 80
ServerName www.kgc.com:80
创建盗链站点主页
[root@localhost ~]# vim /var/www/html/index.html
<h1>dao tu web</h1>
<img src="http://www.kgc.com/kgc.jpg"/>
[root@daolian ~]# echo "nameserver 192.168.50.134" > /etc/resolv.conf 将DNS服务器地址添加到盗链服务器上的resolv.conf中
开启服务
[root@localhost ~]# systemctl start httpd
[root@localhost ~]# systemctl stop firewalld
源站进行防盗链操作
配置规则变量说明
●%{HTTP_ REFERER}:浏览header中的链接字段,代表是从哪个链接访问所需的网址
●!^:不以后面的字符串开头
.*$: 以任意字符结尾
●NC:不区分大写
●R:强制跳转
规则匹配说明
●RewriteEngine On:打开网页重写功能
●RewriteCond:设置匹配规则
●RewriteRule:设置跳转动作
[root@localhost ~]# vim /etc/httpd.conf
将156行的rewrite模块功能开启(前面的#去掉)
156 LoadModule rewrite_module modules/mod_rewrite.so
在<Directory "/usr/local/httpd/htdocs">标签内添加如下防盗链的规则:
在249行下添加或Require all granted下面添加
RewriteEngine On
RewriteCond %{HTTP_REFERER} !^http://kgc.com/.*$ [NC]
RewriteCond %{HTTP_REFERER} !^http://kgc.com$ [NC]
RewriteCond %{HTTP_REFERER} !^http://www.kgc.com/.*$ [NC]
RewriteCond %{HTTP_REFERER} !^http://www.kgc.com/$ [NC]
RewriteRule .*\.(gif|jpg|swf)$ http://www.kgc.com/error.png 盗链图片名称(error.peng)
在网上找一张图片做出盗链图片将一张error.jpg图片上传到该目录下,如果发生盗链情况则自动显示该图片
[root@localhost bin]# cd /usr/local/httpd/htdocs/
[root@localhost htdocs]# ls
error.png index.html kgc.jpg
重启一下http服务
[[root@server local]# cd /usr/local/httpd/bin/ ## 进入http命令存放目录
[root@server bin]# ./apachectl stop ## 停止服务
[root@server bin]# ./apachectl start ## 启动服务
回到客户机上,首先清除浏览器缓存,再重启浏览器,访问盗链网站192.168.50.136
显示如下页面,说明防盗链配置已经生效了
我么在访问一下源站服务器可以访问
隐藏版本信息步骤
使用抓包工具查看版本信息
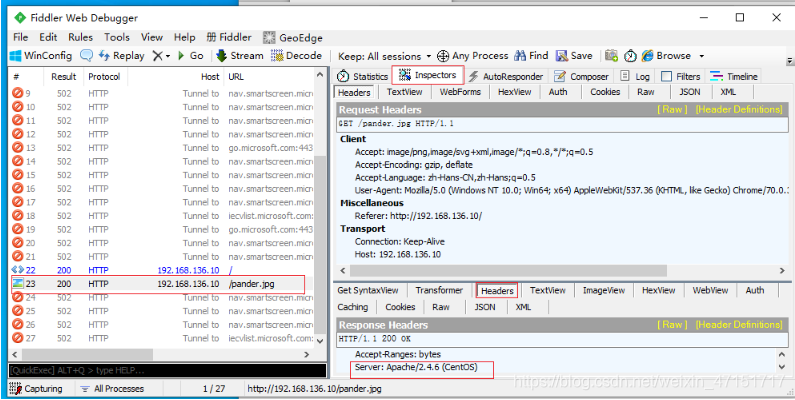
Server:Apache2.4.29(Linux)
隐藏设置
vim /etc/httpd.conf
Include conf/extra/httpd-default.conf (前面的#去掉)
vim /usr/local/httpd/conf/extra/httpd-default.conf
ServerTokens Prod 修改一下添加pord
重启再次查看
Server:Apache2.4.29(Linux)