文章目录
一、配置防盗链
1、防盗链概述
防盗链就是防止别人的网站代码里面盗用服务器的图片,文件,视频等相关资源
如果别人盗用网站的这些静态资源,明显的是会增大服务器的带宽压力
作为网站的维护人员,要杜绝我们服务器的静态资源被其他网站盗用
2、盗链模拟步骤
两台主机配置测试页面
盗链网站的测试网页page盗用源主机目录page/image的一个logo.jpg文件
在Windows中访问测试网页,并使用Fiddler抓包工具的查看效果图
3、检查Apache是否安装了mod_rewrite模块
/usr/local/apache/bin/apachectl -t -D DUMP_MODULES
如果输出中没有rewrite_module(static),则说明编译时没有安装mod_resrite模块
若没有安装则需要重新编译安装
./configure --enable-rewrite…
make && make install
4、配置规则变量说明
%{HTTP_REFERER}:浏览header中的链接字段,存放一个链接的URL,代表是从哪个链接访问所需的网页
!^:不以后面的字符串开头
.*$:以任意字符结尾
NC:不区分大写
R:强制跳转
5、规则匹配说明
规则匹配
如果相应变量的值匹配所设置的规则,则逐条往下处理;如果不匹配,则往后的规则不再匹配
规则匹配说明
RewriteEngine On:打开网页重写功能
RewriteCond:设置匹配规则
RewriteRule:设置跳转动作
6、配置操作演示
修改配置文件,启用防盗链功能并设置规则
RewriteEngine On
RewriteCond %{HTTP_REFERER}!^http://test.com/.*$ [NC]
RewriteCond %{HTTP_REFERER}!^http://test.com$ [NC]
RewriteCond %{HTTP_REFERER}!^http://www.test.com/.*$ [NC]
RewriteCond %{HTTP_REFERER}!^http://www.test.com$ [NC]
RewriteRule .*\.(gif|jpg|swf)$ http://www.test.com/error.html [R,NC]
二、防盗链实操
1、环境配置
环境配置同之前的网页缓存
之前的win10作为盗链客户端
添加一台centos7虚拟机作为测试机
2、源码编译下载apache
#!/bin/bash
ip=www.baidu.com
ping -c 2 -w 3 -i 0.3 $ip &>/dev/null
if [ $? -eq 0 ]
then
echo " 可以ping的通百度"
else
echo "正在更改你的网卡"
sed -i '/^IPADDR=/cIPADDR=192.168.110.132' /etc/sysconfig/network-scripts/ifcfg-ens33
sed -i '/^GATEWAY=/cGATEWAY=192.168.110.2' /etc/sysconfig/network-scripts/ifcfg-ens33
sed -i '/^DNS1=/cDNS1=8.8.8.8' /etc/sysconfig/network-scripts/ifcfg-ens33
echo "网卡配置文件已改完 正在重启网络服务"
systemctl restart network
fi
ping -c 2 $ip &>/dev/null
if [ $? -eq 0 ] ;then
echo "一切准备就绪"
else
echo "请检查你绑定的网卡是不是vm8"
fi
cd ~
cd apache
tar zxvf apr-1.6.2.tar.gz
tar zxvf apr-util-1.6.0.tar.gz
tar jxvf httpd-2.4.29.tar.bz2
mv apr-1.6.2 httpd-2.4.29/srclib/apr
mv apr-util-1.6.0 httpd-2.4.29/srclib/apr-util
yum -y install gcc gCc-C++ make pcre-devel expat-devel perl zlib-devel
if [ $? -eq 0 ];then
echo "正在下载软件包环境"
fi
cd httpd-2.4.29
./configure \
--prefix=/usr/local/httpd \
--enable-so \
--enable-rewrite \
--enable-charset-lite \
--enable-cgi \
--enable-deflate
if [ $? -eq 0 ];then
echo "./configure 执行成功"
else
echo "凉了"
fi
make
make install
cp /usr/local/httpd/bin/apachectl /etc/init.d/httpd
sed -i '2a#chkconfig: 35 85 21' /etc/init.d/httpd
chkconfig --add httpd
sed -i '/#ServerName www.example.com:80/cServerName www.shang.com:80' /usr/local/httpd/conf/httpd.conf
sed -i '52s/^/#/' /usr/local/httpd/conf/httpd.conf
sed -i '/#Listen 12.34.56.78:80/cListen 192.168.110.132:80' /usr/local/httpd/conf/httpd.conf
ln -s /usr/local/httpd/conf/httpd.conf /etc/httpd.conf
ln -S /usr/local/httpd/bin/* /usr/local/bin/
systemctl stop firewalld.service
setenforce 0
service httpd start
if [ $? -eq 0 ] ;then
echo "成功启动apache"
else
echo "完犊子了"
fi
3、设置dns
[root@localhost bin]# yum install bind -y
[root@localhost bin]# vim /etc/named.conf
options {
listen-on port 53 { any;}; '//修改为any'
...省略内容
allow-query { any; }; '//修改为any'
[root@localhost bin]# vim /etc/named.rfc1912.zones
'//添加以下内容到正向解析中'
zone "shang.com" IN {
type master;
file "shang.com.zone";
allow-update { none; };
};
[root@localhost etc]# cp -p /var/named/named.localhost /var/named/shang.com.zone
[root@localhost etc]# vim /var/named/shang.com.zone
'//尾行修改为下面内容'
www IN A 192.168.110.132
[root@localhost etc]# systemctl start named
4、在网页中添加一张图片
[root@promote htdocs]# vim /usr/local/httpd/htdocs/index.html
<html><body><h1>It works!</h1>
<img src="av.jpg"/>
</body></html>
[root@promote htdocs]# service httpd restart
[root@localhost bin]# netstat -ntap |grep 80
tcp 0 0 192.168.197.143:80 0
5、验证
在win10上进行验证

6、盗链主机设置(另起一台centos)
[root@localhost ~]# yum install httpd -y
[root@localhost ~]# echo "nameserver 192.168.110.132" > /etc/resolv.conf
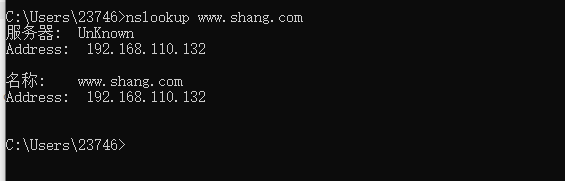
[root@localhost ~]# nslookup www.shang.com
Server: 192.168.110.133
Address: 192.168.110.133#53
Name: www.shang.com
Address: 192.168.110.133
[root@localhost ~]# ifconfig
ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.110.133
[root@localhost ~]# vim /var/www/html/index.html
<html><body><h1>this is daolian web!</h1>
<img src="http://www.shang.com/av.jpg"/>
</body></html>
[root@localhost ~]# systemctl start httpd
[root@localhost ~]# systemctl stop firewalld.service
[root@localhost ~]# setenforce 0
7、测试是否成功盗链

8、正常主机开启防盗链功能
[root@promote htdocs]# vim /usr/local/httpd/conf/httpd.conf
LoadModule rewrite_module modules/mod_rewrite.so
'//将以下文字添加到<Directory "/usr/local/httpd/htdocs"> </Directory>中'
<Directory "/usr/local/httpd/htdocs">
以下是要添加的内容
RewriteEngine On
RewriteCond %{HTTP_REFERER} !^http://shang.com/.*$ [NC]
RewriteCond %{HTTP_REFERER} !^http://shang.com$ [NC]
RewriteCond %{HTTP_REFERER} !^http://www.shang.com/.*$ [NC]
RewriteCond %{HTTP_REFERER} !^http://www.shang.com$ [NC]
RewriteRule .*\.(gif|jpg|swf)$ http://www.shang.com/error.png
</Directory>
[root@localhost htdocs]# ls
aaa.jpg error.png index.html
[root@localhost htdocs]# service httpd restart
win10 验证

二、隐藏版本信息
1、配置Apache隐藏版本信息的必要性
Apache的版本信息,透露了一定的漏洞信息,从而给网站带来安全隐患
生产环境中要配置Apache隐藏版本信息
可使用Fiddler抓包工具分析
2、配置Apache隐藏版本信息详解
将主配置文件httpd.conf以下行注释去掉
#Include conf/extra/httpd-default.conf
修改httpd-default.conf文件两个地方
ServerTokens Full修改为ServerTokens Prod
将ServersSignature On 修改为ServersSignature Off
重启httpd服务,访问网站,抓包测试
3、隐藏版本信息实操
没隐藏之前

(1)Apache主机设置
[root@promote htdocs]# vim /usr/local/httpd/conf/httpd.conf
Include conf/extra/httpd-default.conf '将此开启'
[root@localhost extra]# vim httpd-default.conf
'//将以下内容修改'
Include conf/extra/httpd-default.conf '//开启,取消注释'
ServerTokens Prod '//将原本的Full修改为Prod
ServerSignature Off '//保持是Off'
[root@promote htdocs]# service httpd restart
(3)验证隐藏
