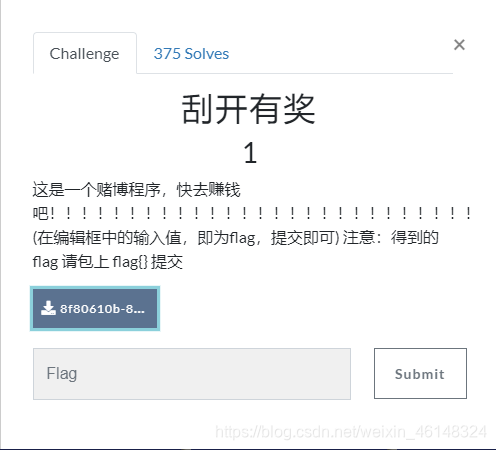
附件是一个exe程序,运行如图:
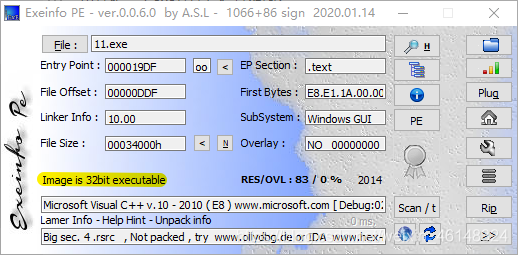
放入PE里查看,是一个32位的程序:
放入32位ida分析伪代码:
BOOL __stdcall DialogFunc(HWND hDlg, UINT a2, WPARAM a3, LPARAM a4)
{
const char *v4; // esi
const char *v5; // edi
int v7; // [esp+8h] [ebp-20030h]
int v8; // [esp+Ch] [ebp-2002Ch]
int v9; // [esp+10h] [ebp-20028h]
int v10; // [esp+14h] [ebp-20024h]
int v11; // [esp+18h] [ebp-20020h]
int v12; // [esp+1Ch] [ebp-2001Ch]
int v13; // [esp+20h] [ebp-20018h]
int v14; // [esp+24h] [ebp-20014h]
int v15; // [esp+28h] [ebp-20010h]
int v16; // [esp+2Ch] [ebp-2000Ch]
int v17; // [esp+30h] [ebp-20008h]
CHAR String; // [esp+34h] [ebp-20004h]
char v19; // [esp+35h] [ebp-20003h]
char v20; // [esp+36h] [ebp-20002h]
char v21; // [esp+37h] [ebp-20001h]
char v22; // [esp+38h] [ebp-20000h]
char v23; // [esp+39h] [ebp-1FFFFh]
char v24; // [esp+3Ah] [ebp-1FFFEh]
char v25; // [esp+3Bh] [ebp-1FFFDh]
char v26; // [esp+10034h] [ebp-10004h]
char v27; // [esp+10035h] [ebp-10003h]
char v28; // [esp+10036h] [ebp-10002h]
if ( a2 == 272 )
return 1;
if ( a2 != 273 )
return 0;
if ( (_WORD)a3 == 1001 )
{
memset(&String, 0, 0xFFFFu);
GetDlgItemTextA(hDlg, 1000, &String, 0xFFFF);
if ( strlen(&String) == 8 )
{
v7 = 90;
v8 = 74;
v9 = 83;
v10 = 69;
v11 = 67;
v12 = 97;
v13 = 78;
v14 = 72;
v15 = 51;
v16 = 110;
v17 = 103;
sub_4010F0(&v7, 0, 10);
memset(&v26, 0, 0xFFFFu);
v26 = v23;
v28 = v25;
v27 = v24;
v4 = (const char *)sub_401000(&v26, strlen(&v26));
memset(&v26, 0, 0xFFFFu);
v27 = v21;
v26 = v20;
v28 = v22;
v5 = (const char *)sub_401000(&v26, strlen(&v26));
if ( String == v7 + 34
&& v19 == v11
&& 4 * v20 - 141 == 3 * v9
&& v21 / 4 == 2 * (v14 / 9)
&& !strcmp(v4, "ak1w")
&& !strcmp(v5, "V1Ax") )
{
MessageBoxA(hDlg, "U g3t 1T!", "@_@", 0);
}
}
return 0;
}
if ( (_WORD)a3 != 1 && (_WORD)a3 != 2 )
return 0;
EndDialog(hDlg, (unsigned __int16)a3);
return 1;
}
ida分析出的伪代码有点问题,下面是我从网上找到的伪代码,
来源链接1
BOOL __stdcall DialogFunc(HWND hDlg, UINT a2, WPARAM a3, LPARAM a4)
{
const char *v4; // esi
const char *v5; // edi
int v7[11]; // [esp+8h] [ebp-20030h]
CHAR String[9]; // [esp+34h] [ebp-20004h]
CHAR v9[3]; // [esp+10034h] [ebp-10004h]
if ( a2 == 272 )
return 1;
if ( a2 != 273 )
return 0; //
// a2 = 273
if ( a3 == 1001 ) // a3 = 1001
{
memset(String, 0, 0xFFFFu); // 给string清零
GetDlgItemTextA(hDlg, 1000, String, 0xFFFF);// 获取对话框文本,然后赋值给string
if ( strlen(String) == 8 ) // string的长度要为8
{
v7[0] = 90;
v7[1] = 74;
v7[2] = 83;
v7[3] = 69;
v7[4] = 67;
v7[5] = 97;
v7[6] = 78;
v7[7] = 72;
v7[8] = 51;
v7[9] = 110;
v7[10] = 103;
sub_4010F0(v7, 0, 10); // 对v7进行处理,处理后的数据
// 51 67 69 72 74 78 83 90 97 103 110
memset(v9, 0, 0xFFFFu); // 给v16清零
v9[0] = String[5];
v9[2] = String[7];
v9[1] = String[6];
v4 = sub_401000(v9, strlen(v9)); // 对v9进行base64加密然后传递给v4
memset(v9, 0, 0xFFFFu); // 给v9清零
v9[1] = String[3];
v9[0] = String[2];
v9[2] = String[4];
v5 = sub_401000(v9, strlen(v9)); // 对v9进行base64加密然后传递给v4
if ( String[0] == v7[0] + 34 // string[0] = 'U'
&& String[1] == v7[4] // string[1] = 'J'
&& 4 * String[2] - 141 == 3 * v7[2] // string[2] = 'W'
&& String[3] / 4 == 2 * (v7[7] / 9) // string[3] = 'P'
&& !strcmp(v4, "ak1w") // v4 = "ak1w"
&& !strcmp(
v5, // v5 = "V1Ax"
"V1Ax") )
{
MessageBoxA(hDlg, "U g3t 1T!", "@_@", 0);
}
}
return 0;
}
if ( a3 != 1 && a3 != 2 )
return 0;
EndDialog(hDlg, a3);
return 1;
}
经过查阅多篇博客,终于弄明白这道题的各个原理和误解
博客链接2
经过分析sub——4010F0函数可以得出算法改变后v7的值

C代码如下
#include <stdio.h>
using namespace std;
int sub(char a1[],int a2,int a3)
{
int i;
int v5;
int v6;
int result;
result=a3;
for (i=a2;i<=a3;a2=i)
{
v5=i;
v6=a1[i];
if (a2<result && i<result)
{
do
{
if (v6>a1[result])
{
if (i>=result)
break;
++i;
a1[v5]=a1[result];
if (i>=result)
break;
while (a1[i]<=v6)
{
if (++i>=result)
goto LABEL_13;
}
if (i>=result)
break;
v5=i;
a1[result]=a1[i];
}
--result;
}
while (i<result);
}
LABEL_13:
a1[result]=v6;
sub(a1,a2,i-1);
result=a3;
++i;
}
return result;
}
int main(int argc, const char *argv[])
{
char v7[11];
v7[0]=90;
v7[1]=74;
v7[2]=83;
v7[3]=69;
v7[4]=67;
v7[5]=97;
v7[6]=78;
v7[7]=72;
v7[8]=51;
v7[9]=110;
v7[10]=103;
sub(v7,0,10);
printf(v7);
return 0;
}
最后结果为

双击v23可以知道是string【5】的值


修改后如图

分析sub_401000函数,通过里面的byte_407830知道是base64加密


分析最后的if语句连续判定知道string的部分值

已知剩下的为base64加密的,通过解密后再给string排序就得出
flag{UJWP1jMp}