一.openssh
1.openssh:当主机中开启openssh服务,那么就对外开放了远程连接的接口
openssh服务的服务端:sshd
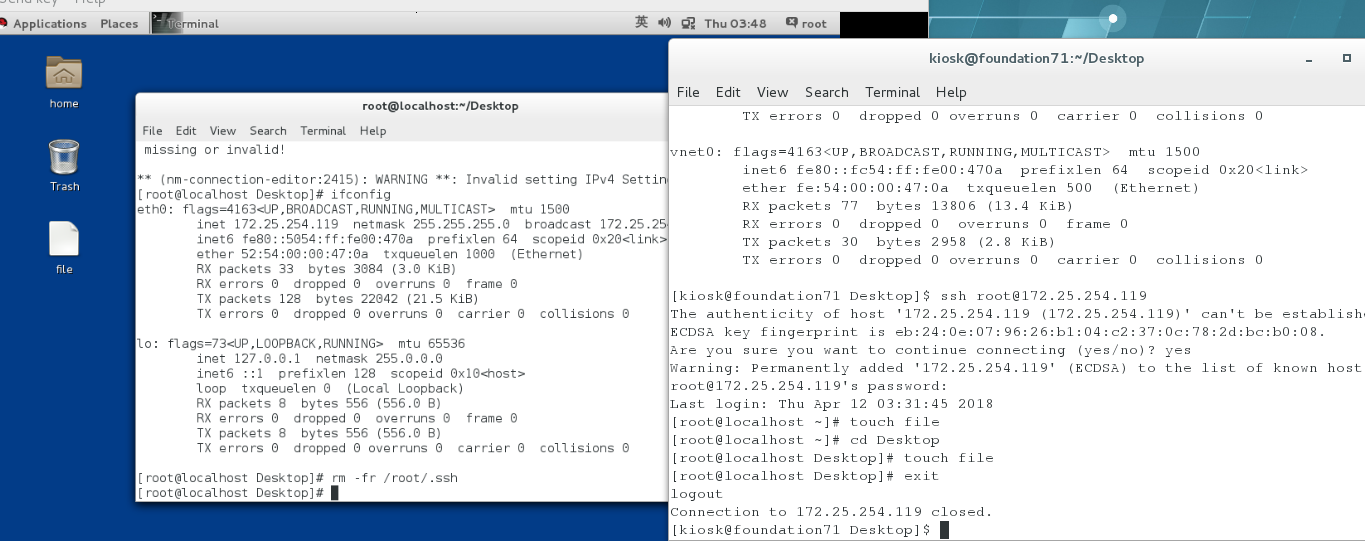
2.在客户端连接sshd的方式:ssh 服务端用户@服务端ip地址
例如
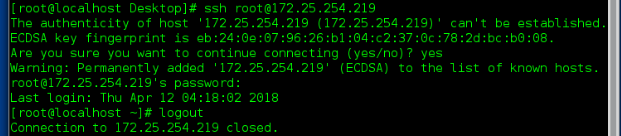
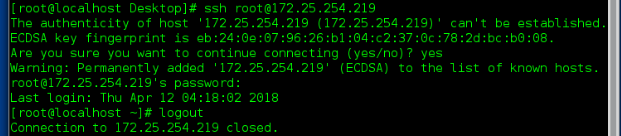
ECDSA key fingerprint is eb:24:0e:07:96:26:b1:04:c2:37:0c:78:2d:bc:b0:08.
Are you sure you want to continue connecting (yes/no)? 当当前主机第一次连接陌生主机时
会自动建立.ssh/know_hosts
这个文中记录的是连接过的主机信息
[email protected]'s password: 输入密码连接成功
Last login: Fri Mar 30 02:05:52 2018 from 172.25.254.119
[root@localhost ~]# exit 表示退出当前连接
logout
Connection to 172.25.254.219 closed.
"注意:以上连接方式是不能打开远程主机的图形功能的如果需要打开远程主机图形功能需要输入 -X"
ssh -X [email protected]
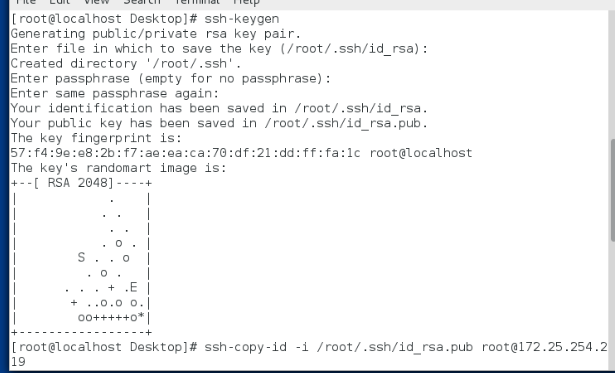
1.生成锁和钥匙
[root@localhost ~]# ssh-keygen 生成密钥的命令
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa): 保存加密字符的文件用默认
Created directory '/root/.ssh'.
Enter passphrase (empty for no passphrase): 可以为空,如果想为空必须大于4位
Enter same passphrase again:
Your identification has been saved in /root/.ssh/id_rsa. 私钥
Your public key has been saved in /root/.ssh/id_rsa.pub. 公钥
The key fingerprint is:
00:4f:b0:72:40:9f:a6:fb:91:86:d2:69:bc:7c:75:5f root@localhost
The key's randomart image is:
+--[ RSA 2048]----+
| .o o.. |
| o * |
| . * o |
| = . |
| . S |
| o + .. . E |
|. B +. . . . |
| + +.. . |
| o.. |
+-----------------+
2.加密ssh用户的认证
在服务端
例子:ssh-copy-id -i /root/.ssh/id_rsa.pub [email protected]
ssh-copy-id 加密命令
-i 指定密钥
/root/.ssh/id_rsa.pub 密钥
root 加密用户
172.25.254.219 主机ip
3.验证
4.sshd的安全配置
80 DenyUsers linux 用户黑名单,当前设定是只不允许linux登陆
systemctl start sshd 开启服务
systemctl stop sshd 停止服务
systemctl status sshd 查看服务状态
systemctl restart sshd 重启服务
systemctl reload sshd 让服务从新加载配置
systemctl enable sshd 设定服务开启启动
systemctl disable sshd 设定服务开机不启动
systemctl list-unit-files 查看系统中所有服务的开机启动状态
systemctl list-units 查看系统中所有开启的服务
systemctl set-default graphical.target 开机时开启图形
systemctl set-default multi-user.targe 开机时不开图形
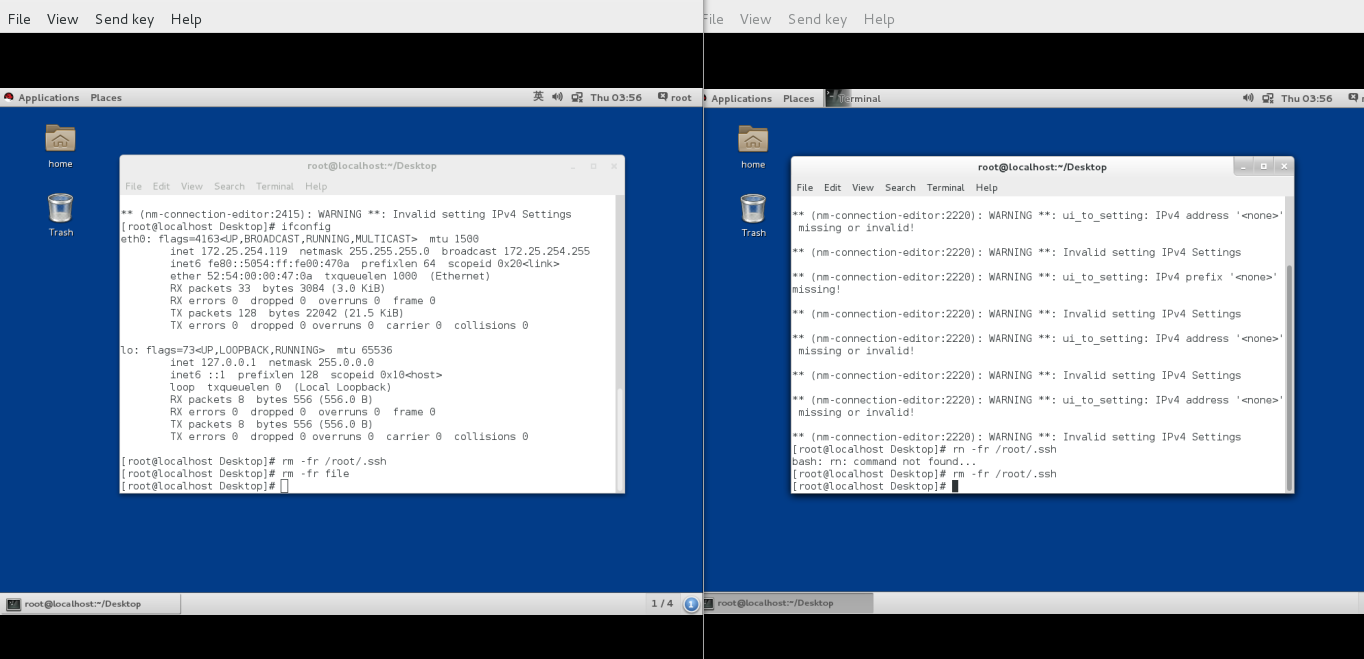
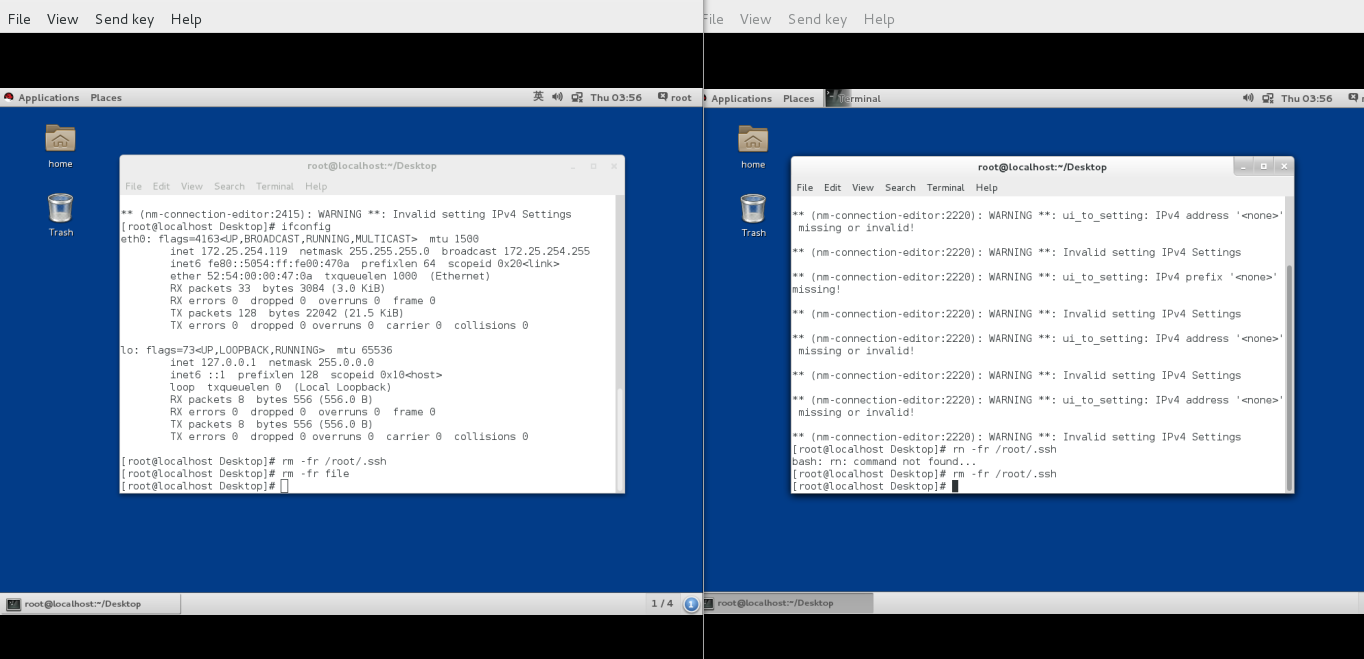
1.openssh:当主机中开启openssh服务,那么就对外开放了远程连接的接口
openssh服务的服务端:sshd
openssh服务的客户端:ssh
例如
ssh [email protected] 在客户端用ssh命令连接172.25.254.119主机的root用户
[root@localhost ~]# ssh [email protected]
The authenticity of host '172.25.254.200 (172.25.254.200)' can't be established.ECDSA key fingerprint is eb:24:0e:07:96:26:b1:04:c2:37:0c:78:2d:bc:b0:08.
Are you sure you want to continue connecting (yes/no)? 当当前主机第一次连接陌生主机时
会自动建立.ssh/know_hosts
这个文中记录的是连接过的主机信息
[email protected]'s password: 输入密码连接成功
Last login: Fri Mar 30 02:05:52 2018 from 172.25.254.119
[root@localhost ~]# exit 表示退出当前连接
logout
Connection to 172.25.254.219 closed.
"注意:以上连接方式是不能打开远程主机的图形功能的如果需要打开远程主机图形功能需要输入 -X"
ssh -X [email protected]
cheese
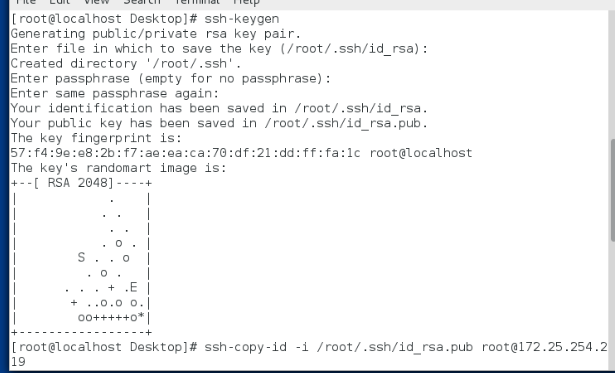
1.生成锁和钥匙
[root@localhost ~]# ssh-keygen 生成密钥的命令
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa): 保存加密字符的文件用默认
Created directory '/root/.ssh'.
Enter passphrase (empty for no passphrase): 可以为空,如果想为空必须大于4位
Enter same passphrase again:
Your identification has been saved in /root/.ssh/id_rsa. 私钥
Your public key has been saved in /root/.ssh/id_rsa.pub. 公钥
The key fingerprint is:
00:4f:b0:72:40:9f:a6:fb:91:86:d2:69:bc:7c:75:5f root@localhost
The key's randomart image is:
+--[ RSA 2048]----+
| .o o.. |
| o * |
| . * o |
| = . |
| . S |
| o + .. . E |
|. B +. . . . |
| + +.. . |
| o.. |
+-----------------+
2.加密ssh用户的认证
在服务端
例子:ssh-copy-id -i /root/.ssh/id_rsa.pub [email protected]
ssh-copy-id 加密命令
-i 指定密钥
/root/.ssh/id_rsa.pub 密钥
root 加密用户
172.25.254.219 主机ip
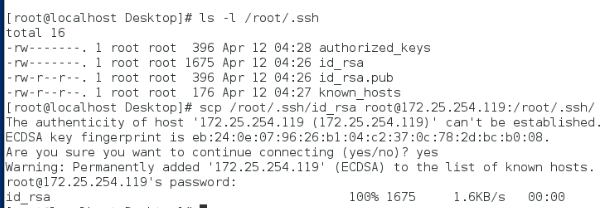
3.验证
解密文件传输到客户端:scp /root/.ssh/id_rsa [email protected]:/root/.ssh/
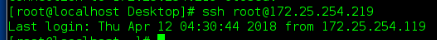
在客户端:ssh [email protected] 连接不需要密码
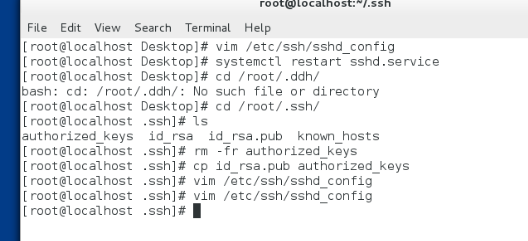
在服务端:cp /root/.ssh/id_rsa.pub /root/.ssh/authorized_keys 从新生成锁文件,解密文件功能恢复
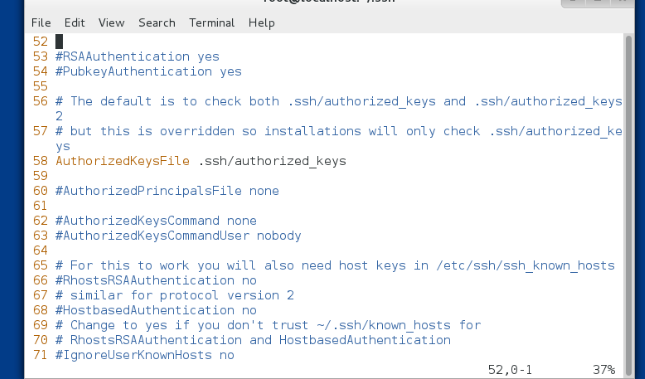
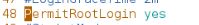
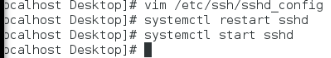
4.sshd的安全配置
1.禁止原始认证方式
78 PasswordAuthentication no|yes 开启或关闭ssh的默认认证方式
48 PermitRootLogin no|yes 开启或关闭root用户的登陆权限
80 DenyUsers linux 用户黑名单,当前设定是只不允许linux登陆
6.linux中服务的管理
systemctl 动作 服务systemctl start sshd 开启服务
systemctl stop sshd 停止服务
systemctl status sshd 查看服务状态
systemctl restart sshd 重启服务
systemctl reload sshd 让服务从新加载配置
systemctl enable sshd 设定服务开启启动
systemctl disable sshd 设定服务开机不启动
systemctl list-unit-files 查看系统中所有服务的开机启动状态
systemctl list-units 查看系统中所有开启的服务
systemctl set-default graphical.target 开机时开启图形
systemctl set-default multi-user.targe 开机时不开图形