目标app-引力波

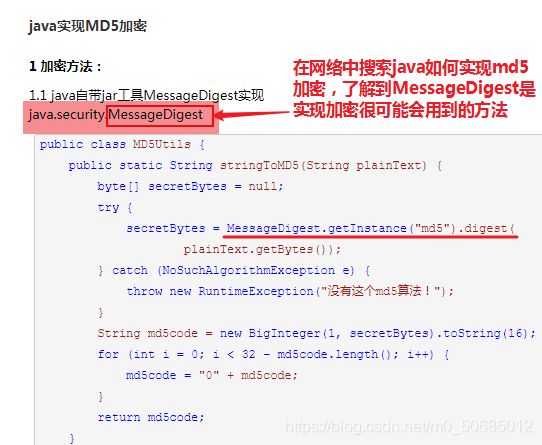
首先了解在java中进行md5加密会用到的方法,然后对方法进行hook盲狙
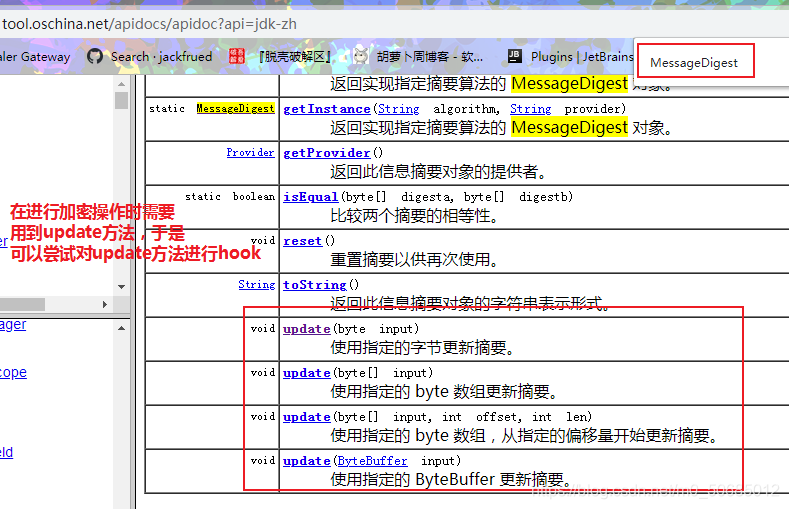
在https://tool.oschina.net/apidocs/apidoc?api=jdk-zh进一步了解MessageDigest
import frida, sys
def on_message(message, data):
if message['type'] == 'send':
print("[*] {0}".format(message['payload']))
else:
print(message)
jscode = """
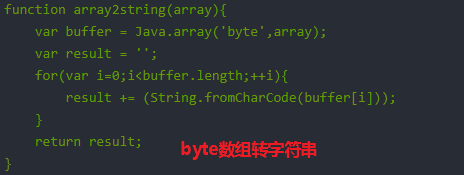
function array2string(array){
var buffer = Java.array('byte',array);
var result = '';
for(var i=0;i<buffer.length;++i){
result += (String.fromCharCode(buffer[i]));
}
return result;
}
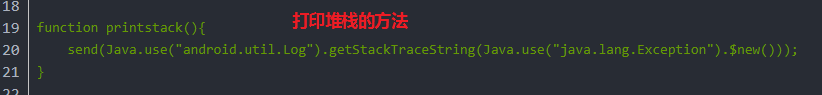
function printstack(){
send(Java.use("android.util.Log").getStackTraceString(Java.use("java.lang.Exception").$new()));
}
Java.perform(
function(){
var MessageDigest = Java.use('java.security.MessageDigest');
MessageDigest.update.overload('[B').implementation = function (bytesarray) {
send('I am here 0');
send("ori:"+array2string(bytesarray));
printstack();
this.update(bytesarray);
},
MessageDigest.update.overload('byte').implementation = function (bytesarray) {
send('I am here 1');
send("ori:"+array2string(bytesarray));
printstack();
this.update(bytesarray);
},
MessageDigest.update.overload('java.nio.ByteBuffer').implementation = function (bytesarray) {
send('I am here 2');
send("ori:"+array2string(bytesarray));
printstack();
this.update(bytesarray);
},
MessageDigest.update.overload('[B','int','int').implementation = function (bytesarray) {
send('I am here 3');
send("ori:"+array2string(bytesarray));
printstack();
this.update(bytesarray);
}
})
"""
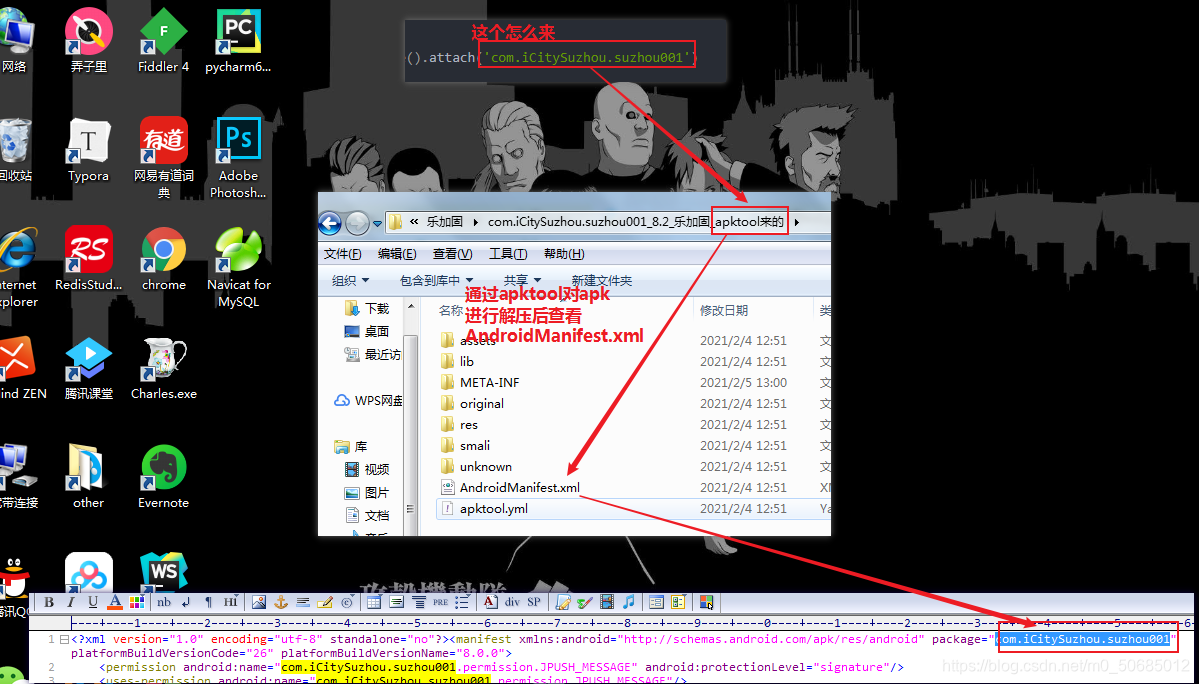
# 定位包
process = frida.get_usb_device().attach('com.iCitySuzhou.suzhou001')
# 传入上面的js代码创造脚本
script = process.create_script(jscode)
# 接受信息打印信息模块
script.on('message', on_message)
print('[*] Running')
script.load()
sys.stdin.read()
代码中的注意点
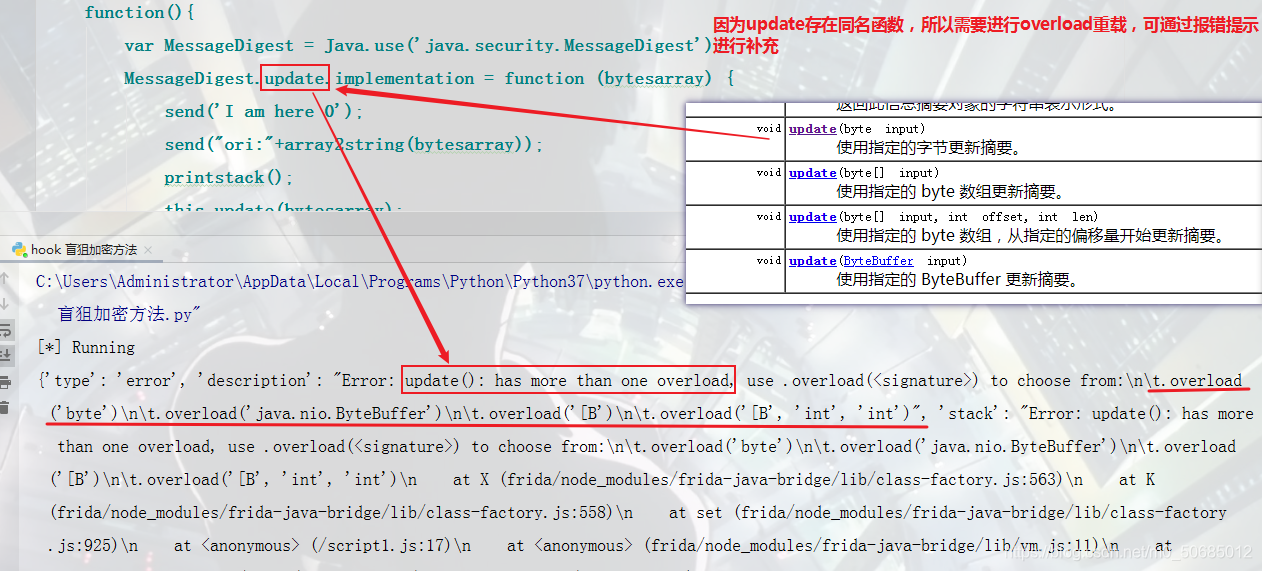
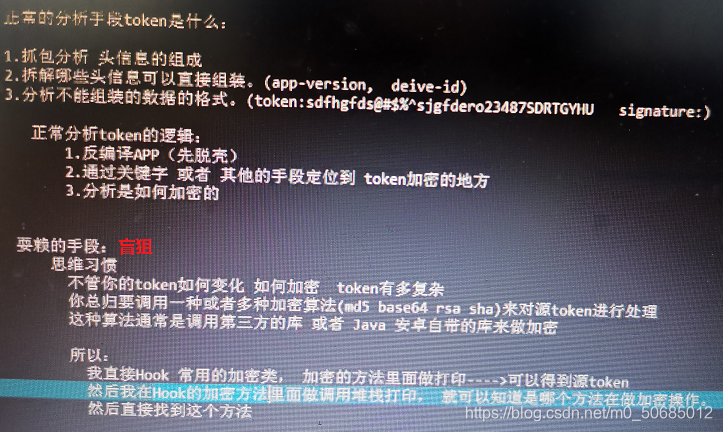
分析思路