1. 简介
OpenSSH 是 SSH (Secure SHell) 协议的免费开源实现。SSH协议族可以用来进行远程控制, 或在计算机之间传送文件。而实现此功能的传统方式,如telnet(终端仿真协议)、 rcp ftp、 rlogin、rsh都是极为不安全的,并且会使用明文传送密码。OpenSSH提供了服务端后台程序和客户端工具,用来加密远程控制和文件传输过程中的数据,并由此来代替原来的类似服务。
2. 下载
移植的的时候需要用到openssh、openssl、zlib这三个库(openssh依赖于openssl和zlib这两个库),下载链接如下:
- zlib官方下载:http://www.zlib.net/
- openssl官方下载:http://www.openssl.org/source
- openssh下载地址: http://www.openssh.com/portable.html
大家 不想自己下载的也可以从我提供的百度云连接下载,我已经把三个需要用到的库打包好了
链接:https://pan.baidu.com/s/1X4kcLE4ABGlEyOvkErJ7IQ
提取码:rf1g
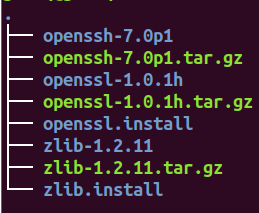
我用到的版本如下:

3. 编译
编译之前需要配置好目标板所需的交叉编译器,这里我已经配置好了,就不再赘述了
3.1. 部署
mkdir ssh # 创建ssh目录用来存放我们的库
cd ssh # 进入ssh目录
mkdir zlib.install # zlib 编译完后的安装目录
mkdir openssl.install # openssl 编译完后的安装目录
# 分别解压3个库
tar zxvf openssl-1.0.1h
tar zxvf openssh-7.0p1
tar zxvf zlib-1.2.11
3.2. 编译zlib
cd zlib-1.2.11
prefix=~/work/plc_gateway/nuc970_lib/ssh/zlib.install CC=arm-linux-gcc ./configure
make
make install
3.3. 编译openssl
cd openssl-1.0.1h
./Configure --prefix=~/work/plc_gateway/nuc970_lib/ssh/openssl.install os/compiler:arm-linux-gcc
make
make install
3.4 编译openssh
cd openssh-7.0p1
./configure --host=arm-linux --with-libs --with-zlib=../zlib.install --with-ssl-dir=../openssl.install --disable-etc-default-login CC=arm-linux-gcc AR=arm-linux-ar
make # 配置编译器和zlib、openssl库的目录
openssh我们只make就可以了不需要make install ,编译完的文件我们一会打包到目标板上即可
4. 安装
4.1 配置
目标板上如果没有以下目录的话我们需要先创建以下目录:
/usr/local/bin
/usr/local/etc
/usr/libexec
/var/run
/var/empty
将openssh-7.0p1目录下编译完的文件复制到板子上:
-
scp、sftp、ssh 、sshd、ssh-add、ssh-agent、ssh-keygen、ssh-keyscan共8个文件拷贝到目标板/usr/local/bin
扫描二维码关注公众号,回复: 13593157 查看本文章
-
moduli、ssh_config、sshd_config共3个文件拷贝到目标板 /usr/local/etc
-
sftp-server、ssh-keysign 共2个文件拷贝到目标板 /usr/libexec
4.2 修改sshd_config
我们需要简单修改 /usr/local/etc/sshd_config 配置文件才能使用
添加或者打开PermitRootLogin yes 我们才能用root账户ssh登录上去
配置sftp:这个目录要填写正确要不然没法使用sftp
4.3 生成Key文件
在目标版 /usr/local/etc/ 目录下生成key文件:
$ cd /usr/local/etc/
$ ssh-keygen -t rsa -f ssh_host_rsa_key -N ""
$ ssh-keygen -t dsa -f ssh_host_dsa_key -N ""
$ ssh-keygen -t ecdsa -f ssh_host_ecdsa_key -N ""
$ ssh-keygen -t dsa -f ssh_host_ed25519_key -N ""
修改 ssh_host_ed25519_key 权限为 600:
$ chmod 600 ssh_host_ed25519_key
4.4 修改目标板配置
打开 /etc/passwd 文件,在最后添加下面这一行:
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
如果开发板的 root 用户还没有密码,键入以下命令然输入两次密码来修改,否其他设备无法连:
$ passwd root
5. 测试
在目标板上运行sshd(sshd要用绝对路径运行)
/usr/local/bin/sshd
ssh连接:
ssh [email protected](板子ip)

sftp测试:

6. 修改后的sshd_config
# This is the sshd server system-wide configuration file. See
# sshd_config(5) for more information.
# This sshd was compiled with PATH=/usr/bin:/bin:/usr/sbin:/sbin
# The strategy used for options in the default sshd_config shipped with
# OpenSSH is to specify options with their default value where
# possible, but leave them commented. Uncommented options override the
# default value.
#Port 22
#AddressFamily any
#ListenAddress 0.0.0.0
#ListenAddress ::
# The default requires explicit activation of protocol 1
#Protocol 2
# HostKey for protocol version 1
#HostKey /etc/ssh/ssh_host_key
#HostKeys for protocol version 2
#HostKey /etc/ssh/ssh_host_rsa_key
#HostKey /etc/ssh/ssh_host_dsa_key
#HostKey /etc/ssh/ssh_host_ecdsa_key
#HostKey /etc/ssh/ssh_host_ed25519_key
# Lifetime and size of ephemeral version 1 server key
#KeyRegenerationInterval 1h
#ServerKeyBits 1024
# Ciphers and keying
#RekeyLimit default none
# Logging
# obsoletes QuietMode and FascistLogging
#SyslogFacility AUTH
#LogLevel INFO
# Authentication:
#LoginGraceTime 2m
#PermitRootLogin prohibit-password
#StrictModes yes
#MaxAuthTries 6
#MaxSessions 10
#RSAAuthentication yes
PubkeyAuthentication yes
# The default is to check both .ssh/authorized_keys and .ssh/authorized_keys2
# but this is overridden so installations will only check .ssh/authorized_keys
AuthorizedKeysFile .ssh/authorized_keys
#AuthorizedPrincipalsFile none
#AuthorizedKeysCommand none
#AuthorizedKeysCommandUser nobody
# For this to work you will also need host keys in /etc/ssh/ssh_known_hosts
#RhostsRSAAuthentication no
# similar for protocol version 2
#HostbasedAuthentication no
# Change to yes if you don't trust ~/.ssh/known_hosts for
# RhostsRSAAuthentication and HostbasedAuthentication
#IgnoreUserKnownHosts no
# Don't read the user's ~/.rhosts and ~/.shosts files
#IgnoreRhosts yes
# To disable tunneled clear text passwords, change to no here!
PasswordAuthentication yes
PermitEmptyPasswords no
PermitRootLogin yes
# Change to no to disable s/key passwords
#ChallengeResponseAuthentication yes
# Kerberos options
#KerberosAuthentication no
#KerberosOrLocalPasswd yes
#KerberosTicketCleanup yes
#KerberosGetAFSToken no
# GSSAPI options
#GSSAPIAuthentication no
#GSSAPICleanupCredentials yes
# Set this to 'yes' to enable PAM authentication, account processing,
# and session processing. If this is enabled, PAM authentication will
# be allowed through the ChallengeResponseAuthentication and
# PasswordAuthentication. Depending on your PAM configuration,
# PAM authentication via ChallengeResponseAuthentication may bypass
# the setting of "PermitRootLogin without-password".
# If you just want the PAM account and session checks to run without
# PAM authentication, then enable this but set PasswordAuthentication
# and ChallengeResponseAuthentication to 'no'.
#UsePAM no
#AllowAgentForwarding yes
#AllowTcpForwarding yes
#GatewayPorts no
#X11Forwarding no
#X11DisplayOffset 10
#X11UseLocalhost yes
#PermitTTY yes
#PrintMotd yes
#PrintLastLog yes
#TCPKeepAlive yes
#UseLogin no
UsePrivilegeSeparation sandbox # Default for new installations.
#PermitUserEnvironment no
#Compression delayed
#ClientAliveInterval 0
#ClientAliveCountMax 3
#UseDNS no
#PidFile /var/run/sshd.pid
#MaxStartups 10:30:100
#PermitTunnel no
#ChrootDirectory none
#VersionAddendum none
# no default banner path
#Banner none
# override default of no subsystems
Subsystem sftp /usr/local/libexec/sftp-server
# Example of overriding settings on a per-user basis
#Match User anoncvs
# X11Forwarding no
# AllowTcpForwarding no
# PermitTTY no
# ForceCommand cvs server