前言
项目用的ruoyi的扩展版本(ts版本),如果有缺失类,可以自行下载或补充------》个人理解
实现多端token,多端httpSecurity,并且相互隔离(局部AuthenticationManager管理认证及授权)
在最近的项目中遇到一个特别的需求:
- 想用一个后端实现两套认证(微信、pc),并且两套认证的token不能共用(相互隔离),
意思就是:如果微信端认证了获取了token,如果拿着这个token访问pc端是访问不通的,因为token不共用(隔离了)- 微信和pc配置的httpSecurity匹配各自的url请求路径
意思就是:第一个我配置成微信的url前缀(/mobile/),第二个配置成pc的url前缀(/manage/),那么token拦截器及认证都按照各自配置的路径走,言外之意就是两个htttpSecurity各管个的
代码实操
security 版本
SecurityBeanConfig 配置多端局部AuthenticationManager
此处是核心配置
- @Order 配置级别
- httpSecurity.requestMatchers((request) -> { request.antMatchers(“/mobile/**”); }) 配置各自的匹配路径
- @Bean(“mobileAuthenticationManager”):因为要注入多个authenticationMannger所以需要起别名
package com.hos.framework.config;
import com.hos.framework.config.properties.PermitAllUrlProperties;
import com.hos.framework.security.CustomAuthenticationProvider;
import com.hos.framework.security.filter.JwtMobileAuthenticationTokenFilter;
import com.hos.framework.security.handler.MobileLogoutSuccessHandlerImpl;
import com.hos.framework.web.service.TokenService;
import lombok.extern.slf4j.Slf4j;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.beans.factory.annotation.Qualifier;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
import org.springframework.core.annotation.Order;
import org.springframework.http.HttpMethod;
import org.springframework.security.authentication.AuthenticationManager;
import org.springframework.security.config.annotation.authentication.builders.AuthenticationManagerBuilder;
import org.springframework.security.config.annotation.method.configuration.EnableGlobalMethodSecurity;
import org.springframework.security.config.annotation.web.builders.HttpSecurity;
import org.springframework.security.config.annotation.web.configuration.WebSecurityConfigurerAdapter;
import org.springframework.security.config.annotation.web.configurers.ExpressionUrlAuthorizationConfigurer;
import org.springframework.security.config.http.SessionCreationPolicy;
import org.springframework.security.core.userdetails.UserDetailsService;
import org.springframework.security.crypto.bcrypt.BCryptPasswordEncoder;
import org.springframework.security.web.authentication.UsernamePasswordAuthenticationFilter;
import org.springframework.security.web.authentication.logout.LogoutFilter;
import org.springframework.web.filter.CorsFilter;
import com.hos.framework.security.filter.JwtAuthenticationTokenFilter;
import com.hos.framework.security.handler.AuthenticationEntryPointImpl;
import com.hos.framework.security.handler.LogoutSuccessHandlerImpl;
import javax.annotation.Resource;
/**
* spring security配置
*
* @author ruoyi
*/
@Slf4j
@EnableGlobalMethodSecurity(prePostEnabled = true, securedEnabled = true)
public class SecurityBeanConfig
{
/**
* 强散列哈希加密实现
*/
@Bean
public BCryptPasswordEncoder bCryptPasswordEncoder()
{
return new BCryptPasswordEncoder();
}
@Configuration
@Order(1)
public static class MobileSecurityConfig extends WebSecurityConfigurerAdapter {
/**
* 认证失败处理类
*/
@Autowired
private AuthenticationEntryPointImpl unauthorizedHandler;
@Autowired
private TokenService tokenService;
/**
* 退出处理类
*/
@Autowired
private MobileLogoutSuccessHandlerImpl logoutSuccessHandler;
/**
* 跨域过滤器
*/
@Autowired
private CorsFilter corsFilter;
/**
* 允许匿名访问的地址
*/
@Autowired
private PermitAllUrlProperties permitAllUrl;
@Autowired
private CustomAuthenticationProvider customAuthenticationProvider;
/**
* anyRequest | 匹配所有请求路径
* access | SpringEl表达式结果为true时可以访问
* anonymous | 匿名可以访问
* denyAll | 用户不能访问
* fullyAuthenticated | 用户完全认证可以访问(非remember-me下自动登录)
* hasAnyAuthority | 如果有参数,参数表示权限,则其中任何一个权限可以访问
* hasAnyRole | 如果有参数,参数表示角色,则其中任何一个角色可以访问
* hasAuthority | 如果有参数,参数表示权限,则其权限可以访问
* hasIpAddress | 如果有参数,参数表示IP地址,如果用户IP和参数匹配,则可以访问
* hasRole | 如果有参数,参数表示角色,则其角色可以访问
* permitAll | 用户可以任意访问
* rememberMe | 允许通过remember-me登录的用户访问
* authenticated | 用户登录后可访问
*/
@Override
protected void configure(HttpSecurity httpSecurity) throws Exception
{
// 注解标记允许匿名访问的url
ExpressionUrlAuthorizationConfigurer<HttpSecurity>.ExpressionInterceptUrlRegistry registry = httpSecurity.authorizeRequests();
permitAllUrl.getUrls().forEach(url -> registry.antMatchers(url).permitAll());
httpSecurity.requestMatchers((request) -> {
request.antMatchers("/mobile/**");
}).authorizeRequests((request) ->{
// 对于登录login 注册register 验证码captchaImage 允许匿名访问
request.antMatchers("/mobile/wx/**").permitAll()
// 静态资源,可匿名访问
.antMatchers(HttpMethod.GET, "/", "/*.html", "/**/*.html", "/**/*.css", "/**/*.js", "/profile/**").permitAll()
// 除上面外的所有请求全部需要鉴权认证
.anyRequest().authenticated();
})
// 除上面外的所有请求全部需要鉴权认证
// .anyRequest().authenticated()
// CSRF禁用,因为不使用session
.csrf().disable()
// 禁用HTTP响应标头
.headers().cacheControl().disable().and()
// 认证失败处理类
.exceptionHandling().authenticationEntryPoint(unauthorizedHandler).and()
// 基于token,所以不需要session
.sessionManagement().sessionCreationPolicy(SessionCreationPolicy.STATELESS)
.and()
.headers().frameOptions().disable();
// 添加Logout filter
httpSecurity.logout().logoutUrl("/mobile/logout").logoutSuccessHandler(logoutSuccessHandler);
// httpSecurity.addFilterAt(new MobileLoginAuthenticationFilter(authenticationManagerBean()),UsernamePasswordAuthenticationFilter.class);
// 添加JWT 替换 filter
httpSecurity.addFilterBefore(new JwtMobileAuthenticationTokenFilter(tokenService), UsernamePasswordAuthenticationFilter.class);
// 添加CORS filter
httpSecurity.addFilterBefore(corsFilter, UsernamePasswordAuthenticationFilter.class);
httpSecurity.addFilterBefore(corsFilter, LogoutFilter.class);
}
/**
* 解决 无法直接注入 AuthenticationManager
*
* @return
* @throws Exception
*/
@Bean("mobileAuthenticationManager")
@Qualifier("mobileAuthenticationManager")
@Override
public AuthenticationManager authenticationManagerBean() throws Exception
{
log.info("mobileAuthenticationManager");
return super.authenticationManagerBean();
}
/**
* 身份认证接口
*/
@Override
protected void configure(AuthenticationManagerBuilder auth) throws Exception
{
log.info("AuthenticationManagerBuilder:{}",auth.getClass());
// customAuthenticationProvider.setUserDetailsService(userDetailsService);
auth.authenticationProvider(customAuthenticationProvider);
// auth.userDetailsService(userDetailsService);//.passwordEncoder(bCryptPasswordEncoder);
}
}
@Configuration
@Order(2)
public static class ManageSecurityConfig extends WebSecurityConfigurerAdapter {
/**
* 自定义用户认证逻辑
*/
@Resource(name = "manageUserDetailsService")
private UserDetailsService userDetailsService;
/**
* 认证失败处理类
*/
@Autowired
private AuthenticationEntryPointImpl unauthorizedHandler;
@Autowired
private TokenService tokenService;
/**
* 退出处理类
*/
@Autowired
private LogoutSuccessHandlerImpl logoutSuccessHandler;
@Autowired
private BCryptPasswordEncoder bCryptPasswordEncoder;
/**
* 跨域过滤器
*/
@Autowired
private CorsFilter corsFilter;
/**
* 允许匿名访问的地址
*/
@Autowired
private PermitAllUrlProperties permitAllUrl;
/**
* anyRequest | 匹配所有请求路径
* access | SpringEl表达式结果为true时可以访问
* anonymous | 匿名可以访问
* denyAll | 用户不能访问
* fullyAuthenticated | 用户完全认证可以访问(非remember-me下自动登录)
* hasAnyAuthority | 如果有参数,参数表示权限,则其中任何一个权限可以访问
* hasAnyRole | 如果有参数,参数表示角色,则其中任何一个角色可以访问
* hasAuthority | 如果有参数,参数表示权限,则其权限可以访问
* hasIpAddress | 如果有参数,参数表示IP地址,如果用户IP和参数匹配,则可以访问
* hasRole | 如果有参数,参数表示角色,则其角色可以访问
* permitAll | 用户可以任意访问
* rememberMe | 允许通过remember-me登录的用户访问
* authenticated | 用户登录后可访问
*/
@Override
protected void configure(HttpSecurity httpSecurity) throws Exception
{
// 注解标记允许匿名访问的url
ExpressionUrlAuthorizationConfigurer<HttpSecurity>.ExpressionInterceptUrlRegistry registry = httpSecurity.authorizeRequests();
permitAllUrl.getUrls().forEach(url -> registry.antMatchers(url).permitAll());
httpSecurity
.requestMatchers((request) -> request.antMatchers("/manage/**"))
.authorizeRequests((request) -> {
request // 对于登录login 注册register 验证码captchaImage 允许匿名访问
.antMatchers("/manage/login", "/manage/register", "/manage/captchaImage"
// todo: 删除
,"/manage/wxTemplate/**"
).permitAll()
// 静态资源,可匿名访问
.antMatchers(HttpMethod.GET, "/", "/*.html", "/**/*.html", "/**/*.css", "/**/*.js", "/profile/**").permitAll()
.antMatchers("/swagger-ui.html", "/swagger-resources/**", "/webjars/**", "/*/api-docs", "/druid/**").permitAll()
.anyRequest().authenticated();
})
// CSRF禁用,因为不使用session
.csrf().disable()
// 禁用HTTP响应标头
.headers().cacheControl().disable().and()
// 认证失败处理类
.exceptionHandling().authenticationEntryPoint(unauthorizedHandler).and()
// 基于token,所以不需要session
.sessionManagement().sessionCreationPolicy(SessionCreationPolicy.STATELESS).and()
// // 过滤请求
// .authorizeRequests()
// // 对于登录login 注册register 验证码captchaImage 允许匿名访问
// .antMatchers("/login", "/register", "/captchaImage").permitAll()
// // 静态资源,可匿名访问
// .antMatchers(HttpMethod.GET, "/", "/*.html", "/**/*.html", "/**/*.css", "/**/*.js", "/profile/**").permitAll()
// .antMatchers("/swagger-ui.html", "/swagger-resources/**", "/webjars/**", "/*/api-docs", "/druid/**").permitAll()
// // 除上面外的所有请求全部需要鉴权认证
// .anyRequest().authenticated()
// .and()
.headers().frameOptions().disable();
// 添加Logout filter
httpSecurity.logout().logoutUrl("/manage/logout").logoutSuccessHandler(logoutSuccessHandler);
// 添加JWT filter
httpSecurity.addFilterBefore(new JwtAuthenticationTokenFilter(tokenService), UsernamePasswordAuthenticationFilter.class);
// 添加CORS filter
httpSecurity.addFilterBefore(corsFilter, UsernamePasswordAuthenticationFilter.class);
httpSecurity.addFilterBefore(corsFilter, LogoutFilter.class);
}
/**
* 解决 无法直接注入 AuthenticationManager
*
* @return
* @throws Exception
*/
@Bean("manageAuthenticationManager")
@Qualifier("manageAuthenticationManager")
@Override
public AuthenticationManager authenticationManagerBean() throws Exception
{
log.info("manageAuthenticationManager");
return super.authenticationManagerBean();
}
/**
* 身份认证接口
*/
@Override
protected void configure(AuthenticationManagerBuilder auth) throws Exception
{
log.info("AuthenticationManagerBuilder:{}",auth.getClass());
auth.userDetailsService(userDetailsService).passwordEncoder(bCryptPasswordEncoder);
}
}
}
公用认证配置实现
TokenService 认证service
- 里面提供了两个token获取及校验,分别对应手机端和pc端
- 根据redis key区分pc及手机端的token
package com.hos.framework.web.service;
import java.util.HashMap;
import java.util.Map;
import java.util.concurrent.TimeUnit;
import javax.servlet.http.HttpServletRequest;
import com.hos.common.config.properties.TokenProperties;
import lombok.extern.slf4j.Slf4j;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.stereotype.Component;
import com.hos.common.constant.CacheConstants;
import com.hos.common.constant.Constants;
import com.hos.common.core.domain.model.LoginUser;
import com.hos.common.core.redis.RedisCache;
import com.hos.common.utils.ServletUtils;
import com.hos.common.utils.StringUtils;
import com.hos.common.utils.ip.AddressUtils;
import com.hos.common.utils.ip.IpUtils;
import com.hos.common.utils.uuid.IdUtils;
import eu.bitwalker.useragentutils.UserAgent;
import io.jsonwebtoken.Claims;
import io.jsonwebtoken.Jwts;
import io.jsonwebtoken.SignatureAlgorithm;
/**
* token验证处理
*
* @author ruoyi
*/
@Slf4j
@Component
public class TokenService
{
protected static final long MILLIS_SECOND = 1000;
protected static final long MILLIS_MINUTE = 60 * MILLIS_SECOND;
private static final Long MILLIS_MINUTE_TEN = 20 * 60 * 1000L;
@Autowired
private RedisCache redisCache;
/**
* 获取用户身份信息
*
* @return 用户信息
*/
public LoginUser getLoginUser(HttpServletRequest request)
{
// 获取请求携带的令牌
String token = getToken(request);
log.info("manage token:{}",token);
if (StringUtils.isNotEmpty(token))
{
try
{
Claims claims = parseToken(token);
// 解析对应的权限以及用户信息
String uuid = (String) claims.get(Constants.LOGIN_USER_KEY);
String userKey = getTokenKey(uuid);
LoginUser user = redisCache.getCacheObject(userKey);
return user;
}
catch (Exception e)
{
e.printStackTrace();
}
}
return null;
}
public LoginUser getMobileLoginUser(HttpServletRequest request)
{
// 获取请求携带的令牌
String token = getToken(request);
log.info("mobile Token: {}",token);
if (StringUtils.isNotEmpty(token))
{
try
{
String userKey = getMobileTokenKey(token);
return redisCache.getCacheObject(userKey);
}
catch (Exception e)
{
}
}
return null;
}
/**
* 获取用户信息
* @param token token
* @return LoginUser
*/
public LoginUser getLoginUser(String token)
{
// 获取请求携带的令牌
if (StringUtils.isNotEmpty(token))
{
try
{
Claims claims = parseToken(token);
// 解析对应的权限以及用户信息
String uuid = (String) claims.get(Constants.LOGIN_USER_KEY);
String userKey = getTokenKey(uuid);
LoginUser user = redisCache.getCacheObject(userKey);
return user;
}
catch (Exception e)
{
}
}
return null;
}
public LoginUser getMobileLoginUser(String token)
{
// 获取请求携带的令牌
if (StringUtils.isNotEmpty(token))
{
try
{
Claims claims = parseToken(token);
// 解析对应的权限以及用户信息
String uuid = (String) claims.get(Constants.LOGIN_USER_KEY);
String userKey = getMobileTokenKey(uuid);
LoginUser user = redisCache.getCacheObject(userKey);
return user;
}
catch (Exception e)
{
}
}
return null;
}
/**
* 设置用户身份信息
*/
public void setLoginUser(LoginUser loginUser)
{
if (StringUtils.isNotNull(loginUser) && StringUtils.isNotEmpty(loginUser.getToken()))
{
refreshToken(loginUser);
}
}
/**
* 删除用户身份信息
*/
public void delLoginUser(LoginUser loginUser)
{
if (StringUtils.isNotEmpty(loginUser.getToken()))
{
String userKey;
if("mobile".equals(loginUser.getType())){
userKey = getMobileTokenKey(loginUser.getToken());
}else {
userKey = getTokenKey(loginUser.getToken());
}
redisCache.deleteObject(userKey);
}
}
/**
* 创建令牌
*
* @param loginUser 用户信息
* @return 令牌
*/
public String createToken(LoginUser loginUser)
{
String token = IdUtils.fastUUID();
loginUser.setToken(token);
setUserAgent(loginUser);
refreshToken(loginUser);
Map<String, Object> claims = new HashMap<>();
claims.put(Constants.LOGIN_USER_KEY, token);
return createToken(claims);
}
public String createMobileToken(LoginUser loginUser,String cookie)
{
loginUser.setToken(cookie);
setUserAgent(loginUser);
refreshToken(loginUser);
Map<String, Object> claims = new HashMap<>();
claims.put(Constants.LOGIN_USER_KEY, cookie);
return createToken(claims);
}
/**
* 验证令牌有效期,相差不足20分钟,自动刷新缓存
*
* @param loginUser
* @return 令牌
*/
public void verifyToken(LoginUser loginUser)
{
long expireTime = loginUser.getExpireTime();
long currentTime = System.currentTimeMillis();
if (expireTime - currentTime <= MILLIS_MINUTE_TEN)
{
refreshToken(loginUser);
}
}
/**
* 刷新令牌有效期
*
* @param loginUser 登录信息
*/
public void refreshToken(LoginUser loginUser)
{
loginUser.setLoginTime(System.currentTimeMillis());
loginUser.setExpireTime(loginUser.getLoginTime() + TokenProperties.EXPIRE_TIME * MILLIS_MINUTE);
// 根据uuid将loginUser缓存
String userKey;
if("mobile".equals(loginUser.getType())){
// c端用户
userKey = getMobileTokenKey(loginUser.getToken());
}else {
userKey = getTokenKey(loginUser.getToken());
}
redisCache.setCacheObject(userKey, loginUser, TokenProperties.EXPIRE_TIME, TimeUnit.MINUTES);
}
/**
* 设置用户代理信息
*
* @param loginUser 登录信息
*/
public void setUserAgent(LoginUser loginUser)
{
UserAgent userAgent = UserAgent.parseUserAgentString(ServletUtils.getRequest().getHeader("User-Agent"));
String ip = IpUtils.getIpAddr(ServletUtils.getRequest());
loginUser.setIpaddr(ip);
loginUser.setLoginLocation(AddressUtils.getRealAddressByIP(ip));
loginUser.setBrowser(userAgent.getBrowser().getName());
loginUser.setOs(userAgent.getOperatingSystem().getName());
}
/**
* 从数据声明生成令牌
*
* @param claims 数据声明
* @return 令牌
*/
private String createToken(Map<String, Object> claims)
{
String token = Jwts.builder()
.setClaims(claims)
.signWith(SignatureAlgorithm.HS512, TokenProperties.SECRET).compact();
return token;
}
/**
* 从令牌中获取数据声明
*
* @param token 令牌
* @return 数据声明
*/
private Claims parseToken(String token)
{
return Jwts.parser()
.setSigningKey(TokenProperties.SECRET)
.parseClaimsJws(token)
.getBody();
}
/**
* 从令牌中获取用户名
*
* @param token 令牌
* @return 用户名
*/
public String getUsernameFromToken(String token)
{
Claims claims = parseToken(token);
return claims.getSubject();
}
/**
* 获取请求token
*
* @param request
* @return token
*/
private String getToken(HttpServletRequest request)
{
String token = request.getHeader(TokenProperties.HEADER);
if (StringUtils.isNotEmpty(token) && token.startsWith(Constants.TOKEN_PREFIX))
{
token = token.replace(Constants.TOKEN_PREFIX, "");
}
return token;
}
private String getTokenKey(String uuid)
{
return CacheConstants.LOGIN_TOKEN_KEY + uuid;
}
private String getMobileTokenKey(String uuid)
{
return CacheConstants.LOGIN_MOBILE_TOKEN_KEY + uuid;
}
}
AuthenticationEntryPointImpl 认证失败处理器
/**
* 认证失败处理类 返回未授权
*
* @author ruoyi
*/
@Component
public class AuthenticationEntryPointImpl implements AuthenticationEntryPoint, Serializable
{
private static final long serialVersionUID = -8970718410437077606L;
@Override
public void commence(HttpServletRequest request, HttpServletResponse response, AuthenticationException e)
throws IOException
{
int code = HttpStatus.UNAUTHORIZED;
String msg = StringUtils.format("请求访问:{},认证失败,无法访问系统资源", request.getRequestURI());
ServletUtils.renderString(response, JSON.toJSONString(AjaxResult.error(code, msg)));
}
}
手机端认证配置实现
CustomAuthenticationProvider 自定义认证provider
@Component
@Slf4j
public class CustomAuthenticationProvider implements AuthenticationProvider {
@Autowired
@Qualifier(value = "mobileUserDetailsService")
private UserDetailsService userDetailsService;
private GrantedAuthoritiesMapper authoritiesMapper = new NullAuthoritiesMapper();
private boolean forcePrincipalAsString = false;
@Override
public Authentication authenticate(Authentication auth)
throws AuthenticationException {
//
log.info("自定义 mp 认证:{}",auth);
UserDetails user = userDetailsService.loadUserByUsername(auth.getName());
Object principalToReturn = user;
if (this.forcePrincipalAsString) {
principalToReturn = user.getUsername();
}
return createSuccessAuthentication(principalToReturn,auth,user);
// throw new
// BadCredentialsException("External system authentication failed");
//
}
@Override
public boolean supports(Class<?> auth) {
return auth.equals(MobileAuthenticationToken.class);
}
protected Authentication createSuccessAuthentication(Object principal, Authentication authentication,
UserDetails user) {
// Ensure we return the original credentials the user supplied,
// so subsequent attempts are successful even with encoded passwords.
// Also ensure we return the original getDetails(), so that future
// authentication events after cache expiry contain the details
UsernamePasswordAuthenticationToken result = new UsernamePasswordAuthenticationToken(principal,
authentication.getCredentials(), this.authoritiesMapper.mapAuthorities(user.getAuthorities()));
result.setDetails(authentication.getDetails());
log.info("Authenticated user");
return result;
}
}
MobileLogoutSuccessHandlerImpl 退出处理器
@Configuration
public class MobileLogoutSuccessHandlerImpl implements LogoutSuccessHandler
{
@Autowired
private TokenService tokenService;
/**
* 退出处理
*
* @return
*/
@Override
public void onLogoutSuccess(HttpServletRequest request, HttpServletResponse response, Authentication authentication)
throws IOException, ServletException
{
LoginUser loginUser = tokenService.getMobileLoginUser(request);
if (StringUtils.isNotNull(loginUser))
{
String userName = loginUser.getUser().getNickName();
// 删除用户缓存记录
tokenService.delLoginUser(loginUser);
// 记录用户退出日志
AsyncManager.me().execute(AsyncFactory.recordLogininfor(userName, Constants.LOGOUT, "退出成功"));
}
ServletUtils.renderString(response, JSON.toJSONString(AjaxResult.success("退出成功")));
}
}
JwtMobileAuthenticationTokenFilter 手机token过滤器
/**
* token过滤器 验证token有效性
*
* @author ruoyi
*/
@Slf4j
public class JwtMobileAuthenticationTokenFilter extends OncePerRequestFilter
{
private final TokenService tokenService;
public JwtMobileAuthenticationTokenFilter(TokenService tokenService){
this.tokenService = tokenService;
}
@Override
protected void doFilterInternal(HttpServletRequest request, HttpServletResponse response, FilterChain chain)
throws ServletException, IOException
{
log.info("mobile jwt 拦截器:{}",request.getRequestURL());
LoginUser loginUser = tokenService.getMobileLoginUser(request);
if (StringUtils.isNotNull(loginUser) && StringUtils.isNull(SecurityUtils.getAuthentication()))
{
tokenService.verifyToken(loginUser);
UsernamePasswordAuthenticationToken authenticationToken = new UsernamePasswordAuthenticationToken(loginUser, null, loginUser.getAuthorities());
authenticationToken.setDetails(new WebAuthenticationDetailsSource().buildDetails(request));
SecurityContextHolder.getContext().setAuthentication(authenticationToken);
}
log.info("mobile jwt 拦截器 结束");
chain.doFilter(request, response);
}
}
pc端认证配置实现
manageUserDetailsService pc端认证UserDetailsService实现
/**
* 用户验证处理
*
* @author ruoyi
*/
@Service(value = "manageUserDetailsService")
public class UserDetailsServiceImpl implements UserDetailsService
{
private static final Logger log = LoggerFactory.getLogger(UserDetailsServiceImpl.class);
@Autowired
private ISysUserService userService;
@Autowired
private SysPasswordService passwordService;
@Autowired
private SysPermissionService permissionService;
@Override
public UserDetails loadUserByUsername(String username) throws UsernameNotFoundException
{
SysUser user = userService.selectUserByUserName(username);
if (StringUtils.isNull(user))
{
log.info("登录用户:{} 不存在.", username);
throw new ServiceException("登录用户:" + username + " 不存在");
}
else if (UserStatus.DELETED.getCode().equals(user.getDelFlag()))
{
log.info("登录用户:{} 已被删除.", username);
throw new ServiceException("对不起,您的账号:" + username + " 已被删除");
}
else if (UserStatus.DISABLE.getCode().equals(user.getStatus()))
{
log.info("登录用户:{} 已被停用.", username);
throw new ServiceException("对不起,您的账号:" + username + " 已停用");
}
passwordService.validate(user);
return createLoginUser(user);
}
public UserDetails createLoginUser(SysUser user)
{
return new LoginUser(user.getUserId(), user.getDeptId(), user, permissionService.getMenuPermission(user));
}
}
LogoutSuccessHandler pc端退出处理类
/**
* 自定义退出处理类 返回成功
*
* @author ruoyi
*/
@Configuration
public class LogoutSuccessHandlerImpl implements LogoutSuccessHandler
{
@Autowired
private TokenService tokenService;
/**
* 退出处理
*
* @return
*/
@Override
public void onLogoutSuccess(HttpServletRequest request, HttpServletResponse response, Authentication authentication)
throws IOException, ServletException
{
LoginUser loginUser = tokenService.getLoginUser(request);
if (StringUtils.isNotNull(loginUser))
{
String userName = loginUser.getUsername();
// 删除用户缓存记录
tokenService.delLoginUser(loginUser);
// 记录用户退出日志
AsyncManager.me().execute(AsyncFactory.recordLogininfor(userName, Constants.LOGOUT, "退出成功"));
}
ServletUtils.renderString(response, JSON.toJSONString(AjaxResult.success("退出成功")));
}
}
JwtAuthenticationTokenFilter pc端token过滤器
/**
* token过滤器 验证token有效性
*
* @author ruoyi
*/
@Slf4j
public class JwtAuthenticationTokenFilter extends OncePerRequestFilter
{
private final TokenService tokenService;
public JwtAuthenticationTokenFilter(TokenService tokenService){
this.tokenService = tokenService;
}
@Override
protected void doFilterInternal(HttpServletRequest request, HttpServletResponse response, FilterChain chain)
throws ServletException, IOException
{
log.info("manage jwt 拦截器:{}",request.getRequestURI());
LoginUser loginUser = tokenService.getLoginUser(request);
if (StringUtils.isNotNull(loginUser) && StringUtils.isNull(SecurityUtils.getAuthentication()))
{
// 兜底验证
if("mobile".equals(loginUser.getType())){
throw new ServiceException("无权限访问",401);
}
tokenService.verifyToken(loginUser);
UsernamePasswordAuthenticationToken authenticationToken = new UsernamePasswordAuthenticationToken(loginUser, null, loginUser.getAuthorities());
authenticationToken.setDetails(new WebAuthenticationDetailsSource().buildDetails(request));
SecurityContextHolder.getContext().setAuthentication(authenticationToken);
}
log.info("manage jwt 拦截器 结束");
chain.doFilter(request, response);
}
}
效果截图
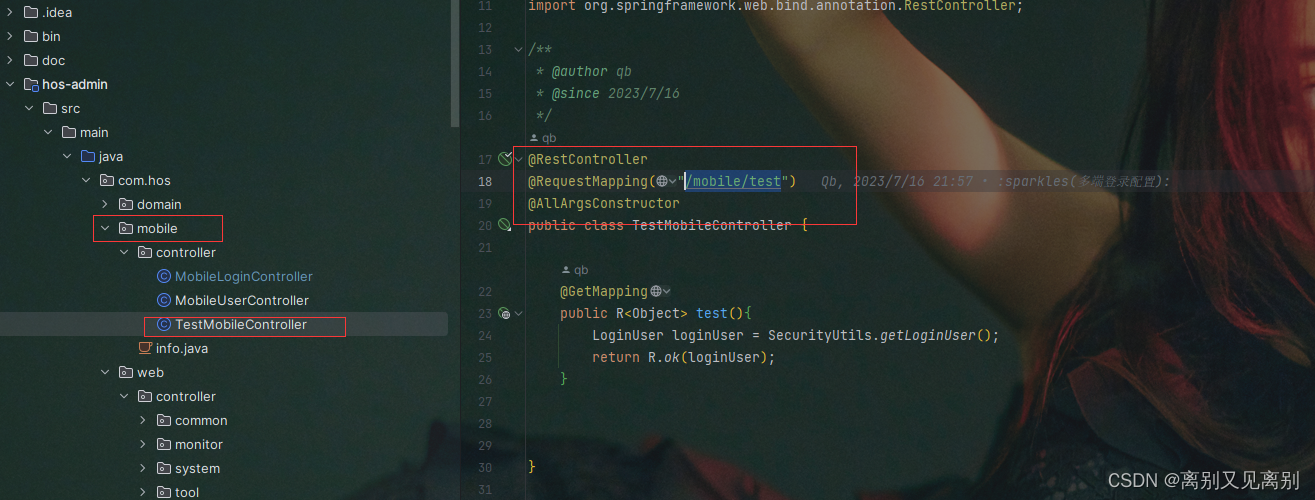
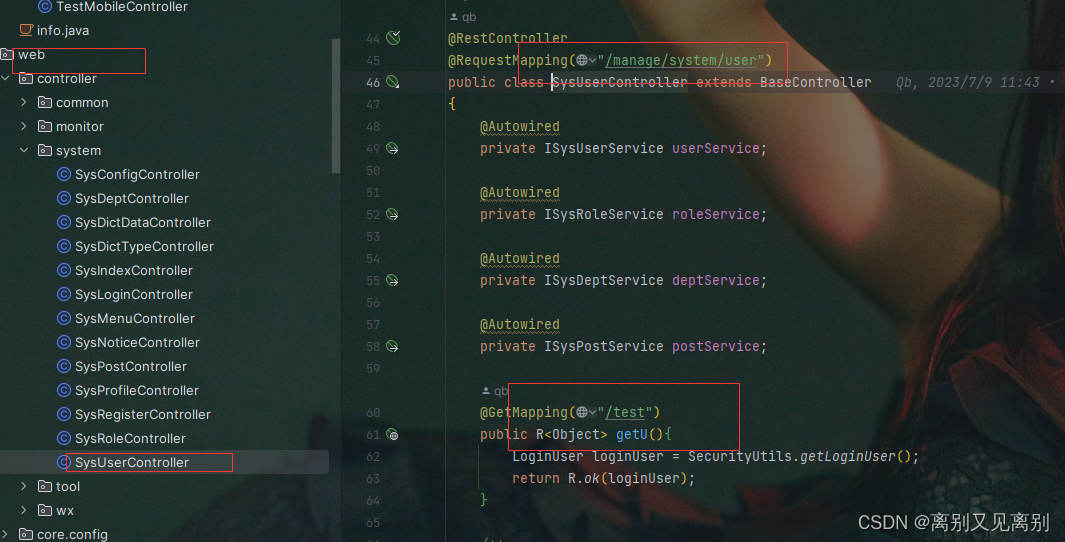
测试接口截图
手机端测试接口(mobile/test)
pc端测试接口(/manage/system/user)
手机端认证
不登录测试
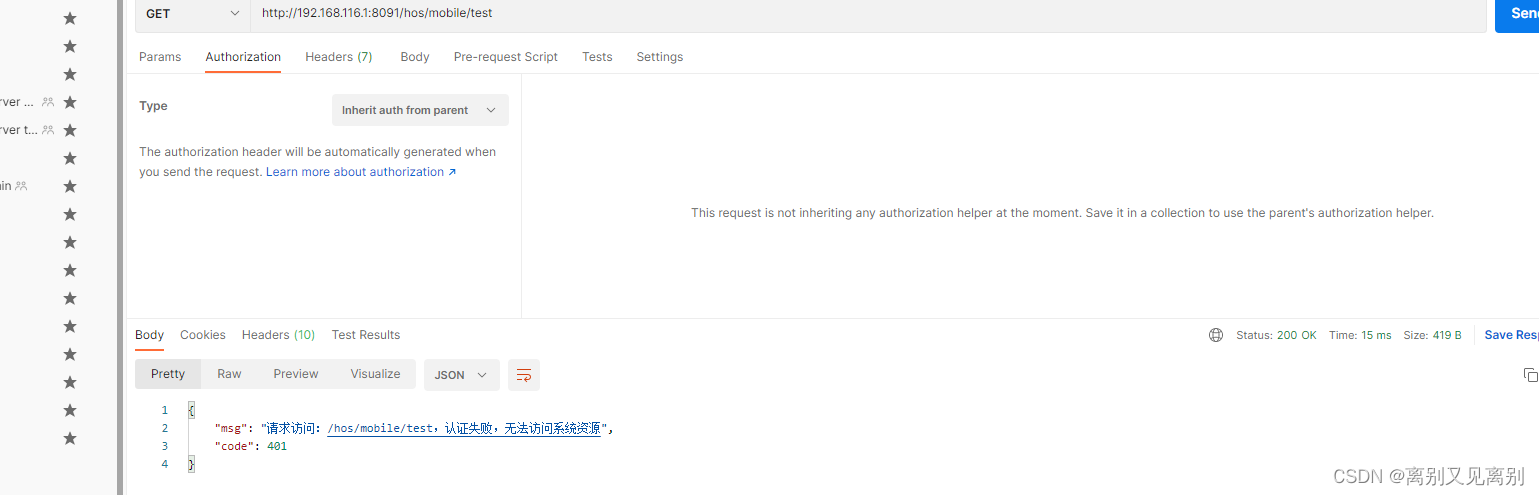
可以看到是请求不通的,因为没有token
登录获取token
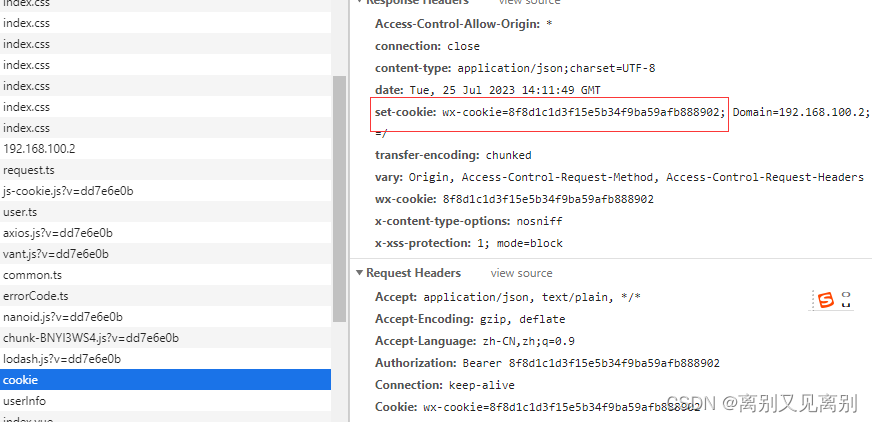
再次请求mobile/test
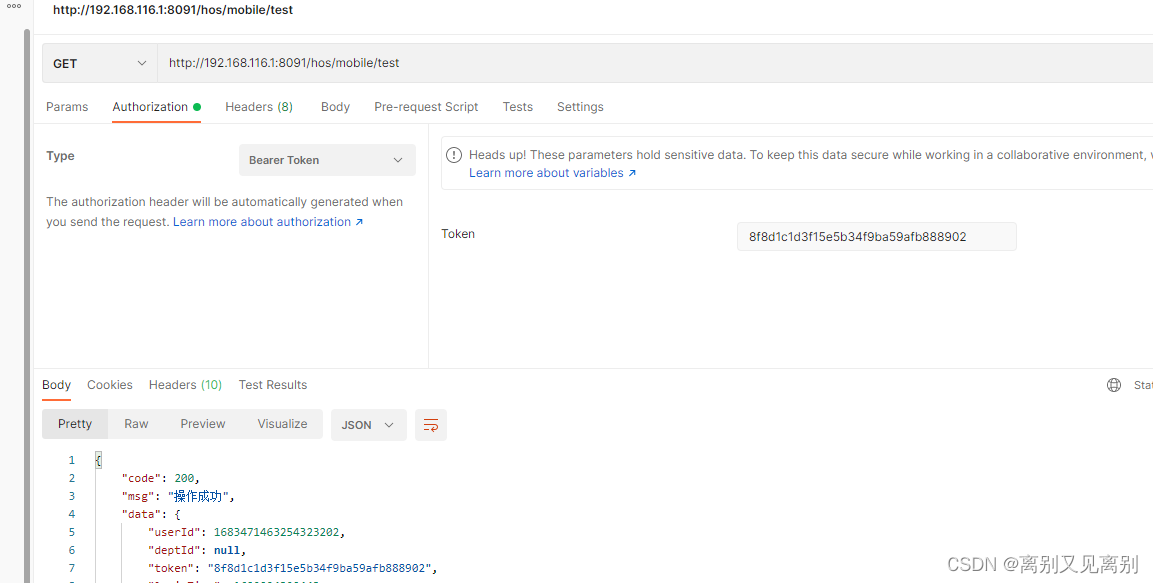
带token后请求成功
带token请求manage
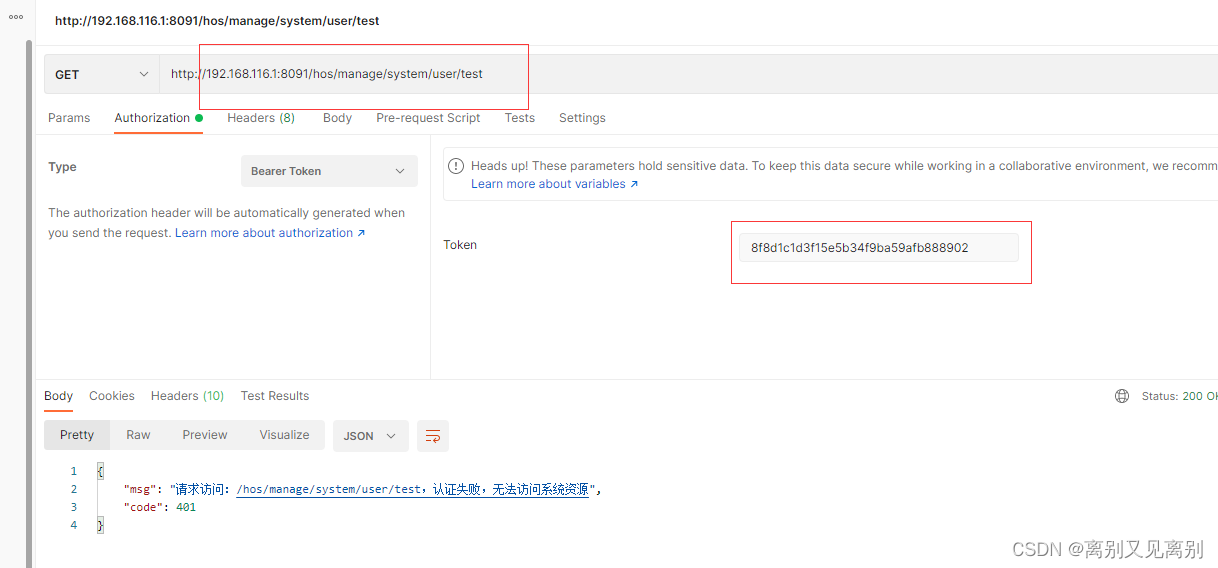
可以看到我用手机端token请求mange是不起作用的,还是会报401
pc端认证
pc端登录获取token
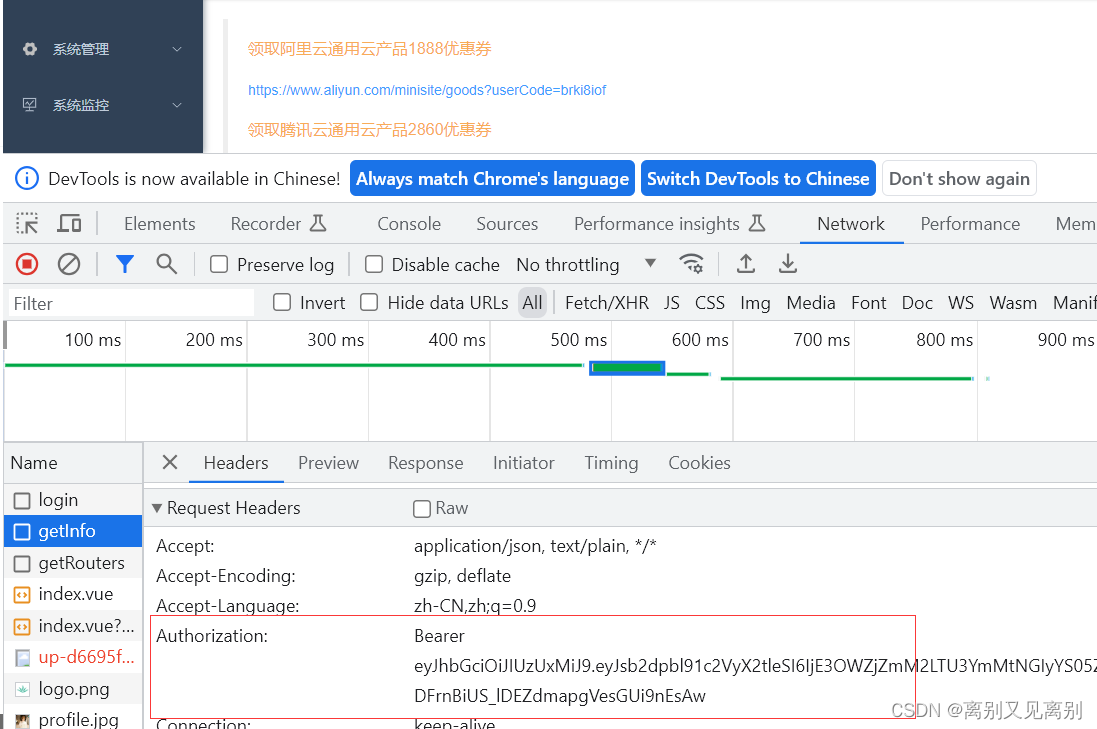
使用token请求 /manage/system/use
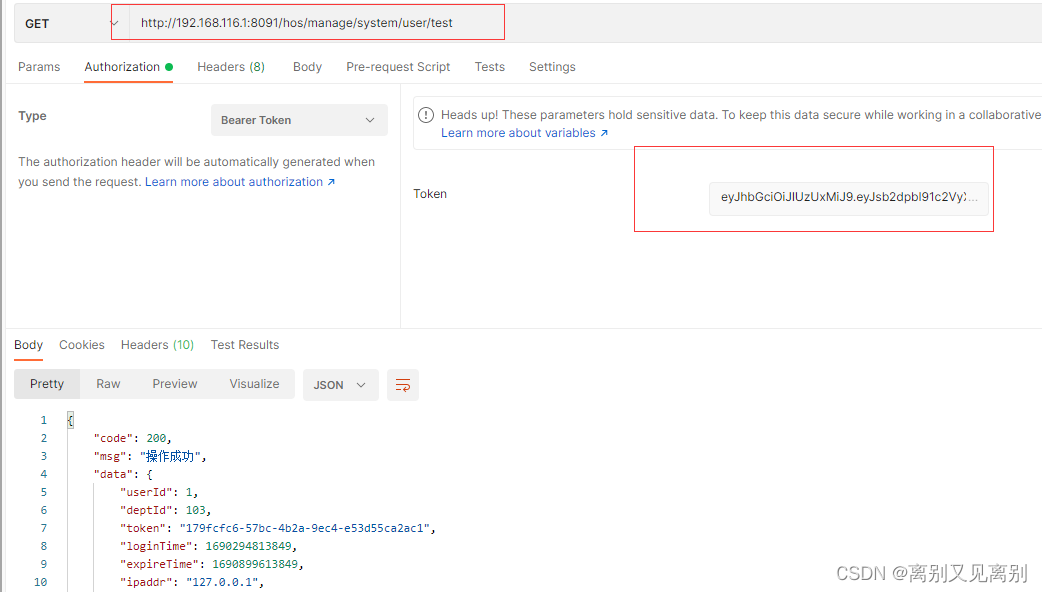
可以看到请求成功
带token请求手机端测试接口 /mobile/test
可以看到请求失败,说明配置生效
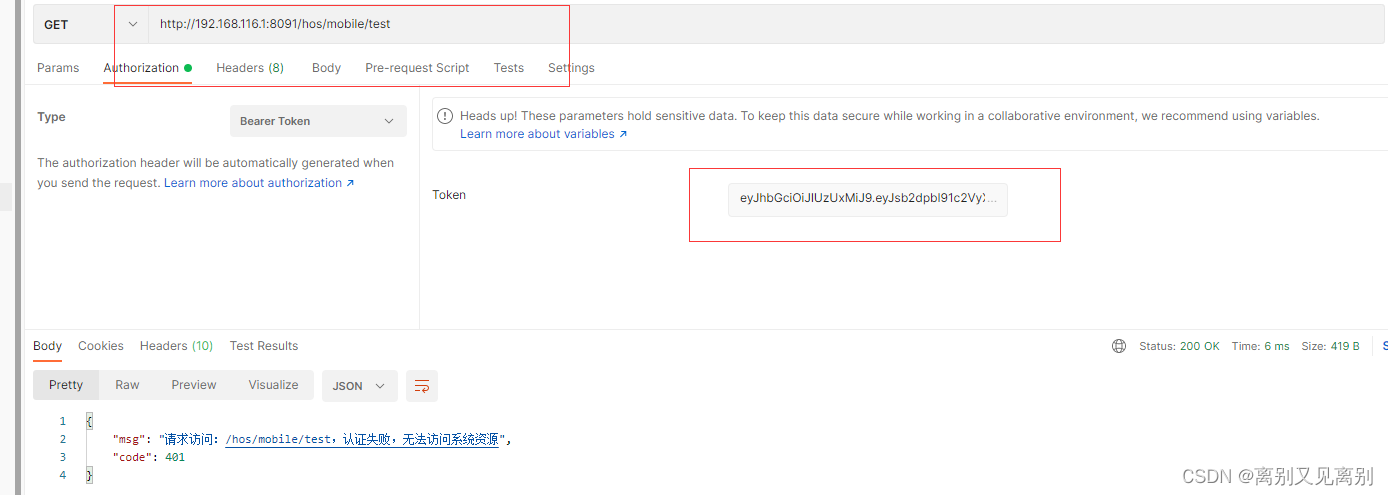
为了更好的说明,附带一张控制台日志的截图
在这里插入图片描述

可以看到每个请求路径都是执行各自的路径配置及各自的token拦截器,由此可以更能说明配置成功,实现了局部AuthenticationManager