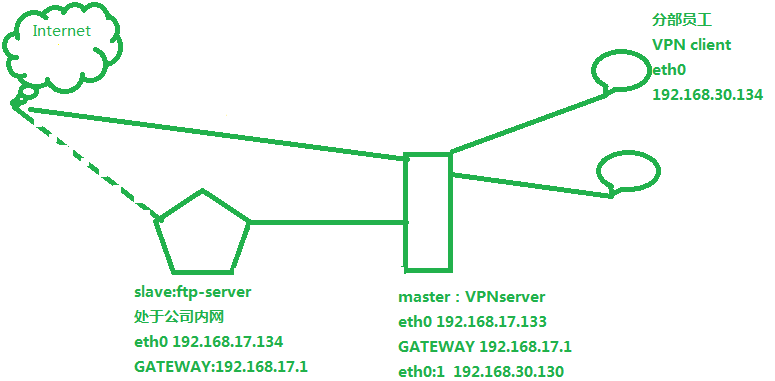
实例1:客户端使用VPN访问服务端局域网内其他机器且可以访问文件服务器如:ftp
拓扑
快速配置
master上网卡配置信息 [root@master ~]# vim /etc/sysconfig/network-scripts/ifcfg-eth0 DEVICE=eth0 TYPE=Ethernet UUID=a186cc9d-8d79-4027-a180-a1b17d884a7b ONBOOT=yes NM_CONTROLLED=no BOOTPROTO=none HWADDR=00:0c:29:4d:47:50 IPADDR=192.168.30.130 NETMASK=255.255.255.0 PREFIX=24 GATEWAY=192.168.30.2 DNS1=119.29.29.29 DEFROUTE=yes IPV4_FAILURE_FATAL=yes IPV6INIT=no NAME="System eth0" USERCTL=no
配置eth0:1 [root@master ~]# vim /etc/sysconfig/network-scripts/ifcfg-eth0:1 DEVICE=eth0:1 TYPE=Ethernet ONBOOT=yes NM_CONTROLLED=no BOOTPROTO=none HWADDR=00:0c:29:4d:47:50 IPADDR=192.168.17.130 NETMASK=255.255.255.0 DEFROUTE=yes IPV4_FAILURE_FATAL=yes IPV6INIT=no NAME="System eth0:1" USERCTL=no
查看配置是否生效 [root@master ~]# ifconfig eth0 Link encap:Ethernet HWaddr 00:0C:29:4D:47:50 inet addr:192.168.30.130 Bcast:192.168.30.255 Mask:255.255.255.0 inet6 addr: fe80::20c:29ff:fe4d:4750/64 Scope:Link UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:1384 errors:0 dropped:0 overruns:0 frame:0 TX packets:1068 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:132561 (129.4 KiB) TX bytes:159706 (155.9 KiB) eth0:1 Link encap:Ethernet HWaddr 00:0C:29:4D:47:50 inet addr:192.168.17.130 Bcast:192.168.17.255 Mask:255.255.255.0 UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 lo Link encap:Local Loopback inet addr:127.0.0.1 Mask:255.0.0.0 inet6 addr: ::1/128 Scope:Host UP LOOPBACK RUNNING MTU:16436 Metric:1 RX packets:70 errors:0 dropped:0 overruns:0 frame:0 TX packets:70 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:0 RX bytes:5864 (5.7 KiB) TX bytes:5864 (5.7 KiB) 开启路由转发 [root@master ~]# vim /etc/sysctl.conf # Kernel sysctl configuration file for Red Hat Linux # # For binary values, 0 is disabled, 1 is enabled. See sysctl(8) and # sysctl.conf(5) for more details. # Controls IP packet forwarding net.ipv4.ip_forward = 1 ....
使之立即生效 [root@master ~]# sysctl -p net.ipv4.ip_forward = 1 net.ipv4.conf.default.rp_filter = 1 net.ipv4.conf.default.accept_source_route = 0 kernel.sysrq = 0 kernel.core_uses_pid = 1 net.ipv4.tcp_syncookies = 1 net.bridge.bridge-nf-call-ip6tables = 0 net.bridge.bridge-nf-call-iptables = 0 net.bridge.bridge-nf-call-arptables = 0 kernel.msgmnb = 65536 kernel.msgmax = 65536 kernel.shmmax = 68719476736 kernel.shmall = 4294967296
开始安装openvpn
[root@master ~]# tar -xf lzo-2.09.tar.gz -C /usr/local/src/ [root@master lzo-2.09]# ./configure --prefix=/usr/ && echo $? && sleep 3 && make -j 4 && echo $? && sleep 3 && make install && echo $? [root@master ~]# tar -xf openvpn-2.2.2.tar.gz -C /usr/local/src/ [root@master openvpn-2.2.2]# ./configure --with-lzo-lib=/usr/ && echo $? && sleep 3 && make -j 4 && echo $? && sleep 3 && make install && echo $?
在master上(即VPN server上)建立CA认证
[root@master 2.0]# ls build-ca build-key-server Makefile revoke-full build-dh build-req openssl-0.9.6.cnf sign-req build-inter build-req-pass openssl-0.9.8.cnf vars build-key clean-all openssl-1.0.0.cnf whichopensslcnf build-key-pass inherit-inter pkitool build-key-pkcs12 list-crl README [root@master 2.0]# vim vars #直接跳到末尾修改为如下内容 export KEY_COUNTRY="CN" export KEY_PROVINCE="beijing" export KEY_CITY="beijing" export KEY_ORG="sishen" export KEY_EMAIL="root@localhost" #使之立即生效 [root@master 2.0]# source !$ source vars NOTE: If you run ./clean-all, I will be doing a rm -rf on /usr/local/src/openvpn-2.2.2/easy-rsa/2.0/keys [root@master 2.0]# ls #注意多出了一个keys目录 build-ca build-key-server list-crl README build-dh build-req Makefile revoke-full build-inter build-req-pass openssl-0.9.6.cnf sign-req build-key clean-all openssl-0.9.8.cnf vars build-key-pass inherit-inter openssl-1.0.0.cnf whichopensslcnf build-key-pkcs12 keys pkitool [root@master 2.0]# ls keys/ index.txt serial 建立CA认证 [root@master 2.0]# ./build-ca Generating a 1024 bit RSA private key .......................++++++ .....++++++ writing new private key to 'ca.key' ----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [CN]: State or Province Name (full name) [beijing]: Locality Name (eg, city) [beijing]: Organization Name (eg, company) [sishen]: Organizational Unit Name (eg, section) [changeme]:SA Common Name (eg, your name or your server's hostname) [changeme]:master Name [changeme]:xueji Email Address [[email protected]]:xueji@163.com [root@master 2.0]# ls keys/ ca.crt ca.key index.txt serial 为VPN server颁发证书 [root@master 2.0]# ./build-key-server master Generating a 1024 bit RSA private key ............++++++ ..............++++++ writing new private key to 'master.key' ----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [CN]: State or Province Name (full name) [beijing]: Locality Name (eg, city) [beijing]: Organization Name (eg, company) [sishen]: Organizational Unit Name (eg, section) [changeme]:SA #注意这里要和CA认证中心一致 Common Name (eg, your name or your server's hostname) [master]:master Name [changeme]: Email Address [[email protected]]: Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []: An optional company name []: Using configuration from /usr/local/src/openvpn-2.2.2/easy-rsa/2.0/openssl-1.0.0.cnf Check that the request matches the signature Signature ok The Subject's Distinguished Name is as follows countryName :PRINTABLE:'CN' stateOrProvinceName :PRINTABLE:'beijing' localityName :PRINTABLE:'beijing' organizationName :PRINTABLE:'sishen' organizationalUnitName:PRINTABLE:'SA' commonName :PRINTABLE:'master' name :PRINTABLE:'changeme' emailAddress :IA5STRING:'[email protected]' Certificate is to be certified until Jun 15 23:14:48 2028 GMT (3650 days) Sign the certificate? [y/n]:y 1 out of 1 certificate requests certified, commit? [y/n]y Write out database with 1 new entries Data Base Updated [root@master 2.0]# ls keys/master.* keys/master.crt keys/master.csr keys/master.key 服务器证书文件 服务器证书请求文件 服务器的私钥 生成user01的证书相关文件 [root@master 2.0]# ./build-key user01 Generating a 1024 bit RSA private key ..................++++++ ..................++++++ writing new private key to 'user01.key' ----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [CN]: State or Province Name (full name) [beijing]: Locality Name (eg, city) [beijing]: Organization Name (eg, company) [sishen]: Organizational Unit Name (eg, section) [changeme]:SA Common Name (eg, your name or your server's hostname) [user01]: Name [changeme]: Email Address [[email protected]]: Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []: An optional company name []: Using configuration from /usr/local/src/openvpn-2.2.2/easy-rsa/2.0/openssl-1.0.0.cnf Check that the request matches the signature Signature ok The Subject's Distinguished Name is as follows countryName :PRINTABLE:'CN' stateOrProvinceName :PRINTABLE:'beijing' localityName :PRINTABLE:'beijing' organizationName :PRINTABLE:'sishen' organizationalUnitName:PRINTABLE:'SA' commonName :PRINTABLE:'user01' name :PRINTABLE:'changeme' emailAddress :IA5STRING:'[email protected]' Certificate is to be certified until Jun 15 23:24:46 2028 GMT (3650 days) Sign the certificate? [y/n]:y 1 out of 1 certificate requests certified, commit? [y/n]y Write out database with 1 new entries Data Base Updated [root@master 2.0]# ls keys/user01.* keys/user01.crt keys/user01.csr keys/user01.key 生成迪菲赫尔曼对称加密认证文件 [root@master 2.0]# ./build-dh Generating DH parameters, 1024 bit long safe prime, generator 2 This is going to take a long time ..................+.............................+...+...........+.......................................................................+..........+.+........+...+........................................................................................................................................+.................++*++*++* [root@master 2.0]# ls keys/dh1024.pem keys/dh1024.pem
配置VPN server
[root@master ~]# cp /usr/local/src/openvpn-2.2.2/sample-config-files/server.conf /etc/server.conf [root@master ~]# vim /etc/server.conf 35 proto tcp 36 ;proto udp 78 ca /usr/local/src/openvpn-2.2.2/easy-rsa/2.0/keys/ca.crt 79 cert /usr/local/src/openvpn-2.2.2/easy-rsa/2.0/keys/master.crt 80 key /usr/local/src/openvpn-2.2.2/easy-rsa/2.0/keys/master.key 88 dh /usr/local/src/openvpn-2.2.2/easy-rsa/2.0/keys/dh1024.pem 139 push "route 192.168.30.0 255.255.255.0" 189 push "redirect-gateway def1" 197 push "dhcp-option DNS 119.29.29.29" 198 push "dhcp-option DNS 223.5.5.5" 206 client-to-client 296 verb 4
启动VPN server
[root@master ~]# which openvpn /usr/local/sbin/openvpn [root@master ~]# /usr/local/sbin/openvpn --config /etc/server.conf ............................... Tue Jun 19 07:42:06 2018 us=357113 MULTI: TCP INIT maxclients=1024 maxevents=1028 Tue Jun 19 07:42:06 2018 us=357130 Initialization Sequence Completed 打开另一个终端 [root@master ~]# netstat -antup | grep 1194 tcp 0 0 0.0.0.0:1194 0.0.0.0:* LISTEN 63187/openvpn [root@master ~]# ifconfig eth0 Link encap:Ethernet HWaddr 00:0C:29:DA:AA:E1 inet addr:192.168.30.130 Bcast:192.168.30.255 Mask:255.255.255.0 inet6 addr: fe80::20c:29ff:feda:aae1/64 Scope:Link UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:7278 errors:0 dropped:0 overruns:0 frame:0 TX packets:5889 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:2236038 (2.1 MiB) TX bytes:914346 (892.9 KiB) eth0:1 Link encap:Ethernet HWaddr 00:0C:29:DA:AA:E1 inet addr:192.168.17.130 Bcast:192.168.17.255 Mask:255.255.255.0 UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 lo Link encap:Local Loopback inet addr:127.0.0.1 Mask:255.0.0.0 inet6 addr: ::1/128 Scope:Host UP LOOPBACK RUNNING MTU:16436 Metric:1 RX packets:4 errors:0 dropped:0 overruns:0 frame:0 TX packets:4 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:0 RX bytes:240 (240.0 b) TX bytes:240 (240.0 b) tun0 Link encap:UNSPEC HWaddr 00-00-00-00-00-00-00-00-00-00-00-00-00-00-00-00 inet addr:10.8.0.1 P-t-P:10.8.0.2 Mask:255.255.255.255 UP POINTOPOINT RUNNING NOARP MULTICAST MTU:1500 Metric:1 RX packets:0 errors:0 dropped:0 overruns:0 frame:0 TX packets:0 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:100 RX bytes:0 (0.0 b) TX bytes:0 (0.0 b)
配置客户端
[root@node-1 ~]# vim /etc/sysconfig/network-scripts/ifcfg-eth0 DEVICE=eth0 TYPE=Ethernet UUID=10241cf1-2617-46ed-9c3a-49a77d3f015d ONBOOT=yes NM_CONTROLLED=no BOOTPROTO=none HWADDR=00:50:56:32:c0:ee IPADDR=192.168.17.131 PREFIX=24 GATEWAY=192.168.17.130 DNS1=119.29.29.29 DOMAIN=223.5.5.5 DEFROUTE=yes IPV4_FAILURE_FATAL=yes IPV6INIT=no NAME="System eth0" NETMASK=255.255.255.0 DNS2=223.5.5.5 USERCTL=no [root@node-1 ~]# ifconfig eth0 Link encap:Ethernet HWaddr 00:50:56:32:C0:EE inet addr:192.168.17.131 Bcast:192.168.17.255 Mask:255.255.255.0 inet6 addr: fe80::250:56ff:fe32:c0ee/64 Scope:Link UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:1258 errors:0 dropped:0 overruns:0 frame:0 TX packets:1032 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:108510 (105.9 KiB) TX bytes:67796 (66.2 KiB) lo Link encap:Local Loopback inet addr:127.0.0.1 Mask:255.0.0.0 inet6 addr: ::1/128 Scope:Host UP LOOPBACK RUNNING MTU:16436 Metric:1 RX packets:12 errors:0 dropped:0 overruns:0 frame:0 TX packets:12 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:0 RX bytes:720 (720.0 b) TX bytes:720 (720.0 b) [root@node-1 ~]# route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 192.168.17.0 0.0.0.0 255.255.255.0 U 0 0 0 eth0 169.254.0.0 0.0.0.0 255.255.0.0 U 1002 0 0 eth0 0.0.0.0 192.168.17.130 0.0.0.0 UG 0 0 0 eth0 测试联通性 [root@node-1 ~]# ping 192.168.17.130 PING 192.168.17.130 (192.168.17.130) 56(84) bytes of data. 64 bytes from 192.168.17.130: icmp_seq=1 ttl=64 time=5.15 ms 64 bytes from 192.168.17.130: icmp_seq=2 ttl=64 time=0.246 ms 64 bytes from 192.168.17.130: icmp_seq=3 ttl=64 time=0.343 ms
在master上测试登录
[root@master ~]# ssh 192.168.17.131 The authenticity of host '192.168.17.131 (192.168.17.131)' can't be established. RSA key fingerprint is a9:5d:8e:75:2a:81:71:32:ef:57:7c:e3:72:ba:0a:7c. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added '192.168.17.131' (RSA) to the list of known hosts. root@192.168.17.131's password: Last login: Tue Jun 19 04:24:14 2018 from 192.168.30.1 [root@node-1 ~]# mkdir /etc/openvpn #建立客户端vpn配置文件存放路径 [root@master ~]# scp lzo-2.09.tar.gz openvpn-2.2.2.tar.gz 192.168.17.131:/root/ root@192.168.17.131's password: lzo-2.09.tar.gz 100% 581KB 580.9KB/s 00:00 openvpn-2.2.2.tar.gz 100% 890KB 889.8KB/s 00:00 [root@master keys]# scp user01.crt user01.key 192.168.17.131:/etc/openvpn root@192.168.17.131's password: user01.crt 100% 3877 3.8KB/s 00:00 user01.key 100% 916 0.9KB/s 00:00
[root@master keys]# scp ca.crt 192.168.17.131:/etc/openvpn/
[email protected]'s password:
ca.crt 100% 1302 1.3KB/s 00:00
在node-1上安装
[root@node-1 ~]# tar -xf lzo-2.09.tar.gz -C /usr/local/src/ [root@node-1 ~]# tar -xf openvpn-2.2.2.tar.gz -C /usr/local/src/ [root@node-1 ~]# cd /usr/local/src/lzo-2.09/ [root@node-1 lzo-2.09]# ./configure --prefix=/usr/ && echo $? && sleep 3 && make -j 4 && echo $? sleep 3 && make install && echo $? [root@node-1 lzo-2.09]# cd /usr/local/src/openvpn-2.2.2/ [root@node-1 openvpn-2.2.2]# ./configure --with-lzo-lib=/usr/ && echo $? && sleep 3 && make -j 4 && echo $? && sleep 3 && make install && echo $? 配置客户端vpn配置文件 [root@node-1 ~]# cp /usr/local/src/openvpn-2.2.2/sample-config-files/client.conf /etc/openvpn/ [root@node-1 ~]# vim /etc/openvpn/client.conf 36 proto tcp 42 remote 192.168.17.130 1194 88 ca /etc/openvpn/ca.crt 89 cert /etc/openvpn/user01.crt 90 key /etc/openvpn/user01.key 120 verb 4
在客户端启动vpn
[root@node-1 ~]# /usr/local/sbin/openvpn --config /etc/openvpn/client.conf --daemon [root@node-1 ~]# ifconfig tun0 tun0 Link encap:UNSPEC HWaddr 00-00-00-00-00-00-00-00-00-00-00-00-00-00-00-00 inet addr:10.8.0.6 P-t-P:10.8.0.5 Mask:255.255.255.255 UP POINTOPOINT RUNNING NOARP MULTICAST MTU:1500 Metric:1 RX packets:0 errors:0 dropped:0 overruns:0 frame:0 TX packets:3 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:100 RX bytes:0 (0.0 b) TX bytes:228 (228.0 b) 测试通信 [root@node-1 ~]# ping -c 2 192.168.30.130 PING 192.168.30.130 (192.168.30.130) 56(84) bytes of data. 64 bytes from 192.168.30.130: icmp_seq=1 ttl=64 time=0.442 ms 64 bytes from 192.168.30.130: icmp_seq=2 ttl=64 time=0.466 ms --- 192.168.30.130 ping statistics --- 2 packets transmitted, 2 received, 0% packet loss, time 1008ms rtt min/avg/max/mdev = 0.442/0.454/0.466/0.012 ms [root@node-1 ~]# ping -c 2 10.8.0.1 PING 10.8.0.1 (10.8.0.1) 56(84) bytes of data. 64 bytes from 10.8.0.1: icmp_seq=1 ttl=64 time=0.577 ms 64 bytes from 10.8.0.1: icmp_seq=2 ttl=64 time=0.637 ms --- 10.8.0.1 ping statistics --- 2 packets transmitted, 2 received, 0% packet loss, time 1009ms rtt min/avg/max/mdev = 0.577/0.607/0.637/0.030 ms
在master上测试连接公司内部电脑
[root@master ~]# ssh 192.168.30.132 The authenticity of host '192.168.30.132 (192.168.30.132)' can't be established. RSA key fingerprint is a9:5d:8e:75:2a:81:71:32:ef:57:7c:e3:72:ba:0a:7c. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added '192.168.30.132' (RSA) to the list of known hosts. root@192.168.30.132's password: Last login: Tue Jun 19 04:24:19 2018 from 192.168.30.1 [root@master ~]# ssh 192.168.30.132 The authenticity of host '192.168.30.132 (192.168.30.132)' can't be established. RSA key fingerprint is a9:5d:8e:75:2a:81:71:32:ef:57:7c:e3:72:ba:0a:7c. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added '192.168.30.132' (RSA) to the list of known hosts. root@192.168.30.132's password: Last login: Tue Jun 19 04:24:19 2018 from 192.168.30.1 [root@node-2 ~]# rpm -ivh /opt/cdrom/Packages/vsftpd-2.2.2-11.el6_4.1.x86_64.rpm [root@node-2 ~]# service vsftpd start Starting vsftpd for vsftpd: [ OK ] 在node-1上测试node-1与node-2的连通性 [root@node-1 ~]# ping -c 2 192.168.30.132 PING 192.168.30.132 (192.168.30.132) 56(84) bytes of data. --- 192.168.30.132 ping statistics --- 2 packets transmitted, 0 received, 100% packet loss, time 11016ms #ping不通 到vpn server上添加一条iptables规则 [root@master ~]# /etc/init.d/iptables start iptables: Applying firewall rules: [ OK ] [root@master ~]# iptables -t nat -A POSTROUTING -s 10.8.0.0/255.255.255.0 -j SNAT --to-source 192.168.30.130 [root@master ~]# /etc/init.d/iptables save iptables: Saving firewall rules to /etc/sysconfig/iptables:[ OK ] [root@master ~]# /etc/init.d/iptables status Table: filter Chain INPUT (policy ACCEPT) num target prot opt source destination Chain FORWARD (policy ACCEPT) num target prot opt source destination Chain OUTPUT (policy ACCEPT) num target prot opt source destination Table: nat Chain PREROUTING (policy ACCEPT) num target prot opt source destination Chain POSTROUTING (policy ACCEPT) num target prot opt source destination 1 SNAT all -- 10.8.0.0/24 0.0.0.0/0 to:192.168.30.130 Chain OUTPUT (policy ACCEPT) num target prot opt source destination 再次测试ping公司内部主机 [root@node-1 ~]# ping -c 2 192.168.30.132 PING 192.168.30.132 (192.168.30.132) 56(84) bytes of data. 64 bytes from 192.168.30.132: icmp_seq=1 ttl=63 time=0.660 ms 64 bytes from 192.168.30.132: icmp_seq=2 ttl=63 time=2.84 ms --- 192.168.30.132 ping statistics --- 2 packets transmitted, 2 received, 0% packet loss, time 1013ms rtt min/avg/max/mdev = 0.660/1.754/2.849/1.095 ms 也可以通过在vpn服务端 [root@node-1 ~]# iptables -t nat -A POSTROUTING -s 10.8.0.0/24 -o eth0 -j MASQUERAD [root@node-1 ~]# rpm -ivh /media/cdrom/Packages/lftp-4.0.9-1.el6.x86_64.rpm [root@node-1 ~]# lftp 192.168.30.132 lftp 192.168.30.132:~> ls drwxr-xr-x 2 0 0 4096 Feb 12 2013 pub lftp 192.168.30.132:/> exit
测试通过VPN访问公网
[root@node-1 ~]# ping -c 2 www.sina.com.cn PING spool.grid.sinaedge.com (101.71.100.123) 56(84) bytes of data. 64 bytes from 101.71.100.123: icmp_seq=1 ttl=127 time=8.24 ms 64 bytes from 101.71.100.123: icmp_seq=2 ttl=127 time=8.18 ms [root@node-1 ~]# ping -c 2 119.29.29.29 PING 119.29.29.29 (119.29.29.29) 56(84) bytes of data. 64 bytes from 119.29.29.29: icmp_seq=1 ttl=127 time=5.99 ms 64 bytes from 119.29.29.29: icmp_seq=2 ttl=127 time=5.86 ms OK~可以上网的~