链接:百度云盘 密码:wdl0
最近一直在学习PE 本来还想写一个简单的加密壳 但是感觉自己水平还差点 所以 打算和我一个小伙伴一起合作 等到开学如果能够写出来 会把源码粘出来 分享给大家
我这里和大家声明一下 我这个是文件 是来自吾爱破解的creakme 160 导航链接 帖子里面有更厉害的思路
本帖是编号为28的creakme
现在开始正文
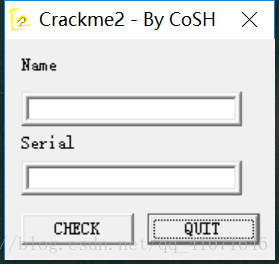
如图 这个页面算是很正常的页面 然后我们随便输入 一下
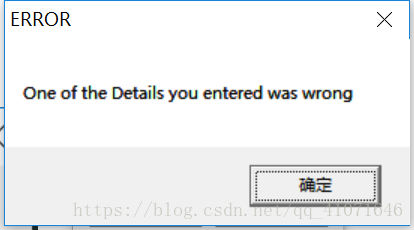
不出意料的出现了错误 然后我们打开od 拖入看看 先分析字符串
发现了我们错误的字符串 跟进去看了看
004014B0 . 64:A1 0000000>mov eax,dword ptr fs:[0]
004014B6 . 6A FF push -0x1
004014B8 . 68 701B4000 push CoSH_2.00401B70
004014BD . 50 push eax
004014BE . 64:8925 00000>mov dword ptr fs:[0],esp
004014C5 . 83EC 08 sub esp,0x8
004014C8 . 53 push ebx ; user32.PostQuitMessage
004014C9 . 55 push ebp
004014CA . 56 push esi
004014CB . 8BF1 mov esi,ecx
004014CD . 57 push edi
004014CE . 8DBE A0000000 lea edi,dword ptr ds:[esi+0xA0]
004014D4 . 8BCF mov ecx,edi
004014D6 . E8 6F030000 call <jmp.&MFC42.#CWnd::GetWindowTextLengthA_3876>
004014DB . 8B1D FC214000 mov ebx,dword ptr ds:[<&USER32.PostQuitMessage>] ; user32.PostQuitMessage
004014E1 . 83F8 05 cmp eax,0x5
004014E4 . 7E 50 jle short CoSH_2.00401536
004014E6 . 8D6E 60 lea ebp,dword ptr ds:[esi+0x60]
004014E9 . 8BCD mov ecx,ebp
004014EB . E8 5A030000 call <jmp.&MFC42.#CWnd::GetWindowTextLengthA_3876>
004014F0 . 83F8 05 cmp eax,0x5 ; 账号长度必须大于5
004014F3 . 7E 41 jle short CoSH_2.00401536
004014F5 . 8D86 E0000000 lea eax,dword ptr ds:[esi+0xE0]
004014FB . 8BCF mov ecx,edi
004014FD . 50 push eax
004014FE . E8 41030000 call <jmp.&MFC42.#CWnd::GetWindowTextA_3874>
00401503 . 8DBE E4000000 lea edi,dword ptr ds:[esi+0xE4]
00401509 . 8BCD mov ecx,ebp
0040150B . 57 push edi
0040150C . E8 33030000 call <jmp.&MFC42.#CWnd::GetWindowTextA_3874> ; 比较密码
00401511 . 8B07 mov eax,dword ptr ds:[edi] ; CoSH_2.00402428
00401513 . 8038 36 cmp byte ptr ds:[eax],0x36
00401516 . 75 1E jnz short CoSH_2.00401536
00401518 . 8078 01 32 cmp byte ptr ds:[eax+0x1],0x32
0040151C . 75 18 jnz short CoSH_2.00401536
0040151E . 8078 02 38 cmp byte ptr ds:[eax+0x2],0x38
00401522 . 75 12 jnz short CoSH_2.00401536
00401524 . 8078 03 37 cmp byte ptr ds:[eax+0x3],0x37
00401528 . 75 0C jnz short CoSH_2.00401536
0040152A . 8078 04 2D cmp byte ptr ds:[eax+0x4],0x2D
0040152E . 75 06 jnz short CoSH_2.00401536
00401530 . 8078 05 41 cmp byte ptr ds:[eax+0x5],0x41
00401534 . 74 17 je short CoSH_2.0040154D
00401536 > 6A 00 push 0x0
00401538 . 68 64304000 push CoSH_2.00403064 ; ASCII "ERROR"
0040153D . 68 38304000 push CoSH_2.00403038 ; ASCII "One of the Details you entered was wrong"
00401542 . 8BCE mov ecx,esi
00401544 . E8 F5020000 call <jmp.&MFC42.#CWnd::MessageBoxA_4224>
00401549 . 6A 00 push 0x0
0040154B . FFD3 call ebx ; user32.PostQuitMessage
0040154D > 8D8E E0000000 lea ecx,dword ptr ds:[esi+0xE0]
00401553 . 8D5424 14 lea edx,dword ptr ss:[esp+0x14]
00401557 . 51 push ecx
00401558 . 68 2C304000 push CoSH_2.0040302C ; ASCII "Well done,"
0040155D . 52 push edx
0040155E . E8 D5020000 call <jmp.&MFC42.#operator+_926>
00401563 . 68 3C314000 push CoSH_2.0040313C
00401568 . 50 push eax
00401569 . 8D4424 18 lea eax,dword ptr ss:[esp+0x18]
0040156D . C74424 28 000>mov dword ptr ss:[esp+0x28],0x0
00401575 . 50 push eax
00401576 . E8 B7020000 call <jmp.&MFC42.#operator+_924>
0040157B . 8B00 mov eax,dword ptr ds:[eax]
0040157D . 6A 00 push 0x0
0040157F . 68 20304000 push CoSH_2.00403020 ; ASCII "YOU DID IT"
00401584 . 50 push eax
00401585 . 8BCE mov ecx,esi
00401587 . C64424 2C 01 mov byte ptr ss:[esp+0x2C],0x1
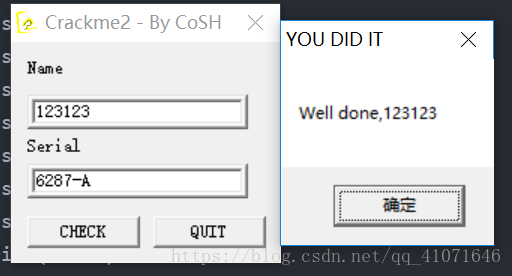
分析到这里其实就很明了了 只要我们将密码搞对就行了 从那一些判断可以判断出来 0x36 0x32 0x38 0x37 0x2d 0x41 依次是这6个 转化成字母就行了 这个好写 由于本人现在在学习python 所以就用python写了
lists=[]
lists.append(chr(0x36))
lists.append(chr(0x32))
lists.append(chr(0x38))
lists.append(chr(0x37))
lists.append(chr(0x2d))
lists.append(chr(0x41))
print(lists)
运行结果为 6287-A 随便输入一个长度大于5的字符串 然后下面输入6287-A 成功!