版权声明:本文为博主 [小明同学爱思考] 原创文章,转载请注明出处。 https://blog.csdn.net/sinat_22840937/article/details/79959301
RSA

import org.apache.commons.codec.binary.Hex;
import java.security.KeyFactory;
import java.security.KeyPair;
import java.security.KeyPairGenerator;
import java.security.PrivateKey;
import java.security.PublicKey;
import java.security.Signature;
import java.security.interfaces.RSAPrivateKey;
import java.security.interfaces.RSAPublicKey;
import java.security.spec.PKCS8EncodedKeySpec;
import java.security.spec.X509EncodedKeySpec;
/**
* RSA
*
* @author liuming
* @create 2018/4/13
*/
public class RSA {
private static String srcMsg = "imooc security rsa";
public static void main(String[] args) {
jdkRSA(srcMsg);
}
public static void jdkRSA(String srcMsg) {
try {
// 初始化密钥
KeyPairGenerator keyPairGenerator = KeyPairGenerator.getInstance("RSA");
keyPairGenerator.initialize(512);
KeyPair keyPair = keyPairGenerator.generateKeyPair();
RSAPublicKey rsaPublicKey = (RSAPublicKey) keyPair.getPublic();
RSAPrivateKey rsaPrivateKey = (RSAPrivateKey) keyPair.getPrivate();
// 执行签名
PKCS8EncodedKeySpec pkcs8EncodedKeySpec = new PKCS8EncodedKeySpec(rsaPrivateKey.getEncoded());
KeyFactory keyFactory = KeyFactory.getInstance("RSA");
PrivateKey privateKey = keyFactory.generatePrivate(pkcs8EncodedKeySpec);
Signature signature = Signature.getInstance("MD5withRSA");
signature.initSign(privateKey);
signature.update(srcMsg.getBytes());
byte[] bytes = signature.sign();
System.out.println(Hex.encodeHexString(bytes));
// 验证签名
X509EncodedKeySpec x509EncodedKeySpec = new X509EncodedKeySpec(rsaPublicKey.getEncoded());
keyFactory = KeyFactory.getInstance("RSA");
PublicKey publicKey = keyFactory.generatePublic(x509EncodedKeySpec);
signature = Signature.getInstance("MD5withRSA");
signature.initVerify(publicKey);
signature.update(srcMsg.getBytes());
boolean verfied = signature.verify(bytes);
System.out.println(verfied);
} catch (Exception e) {
e.printStackTrace();
}
}
}
DSA

import org.apache.commons.codec.binary.Hex;
import java.security.KeyFactory;
import java.security.KeyPair;
import java.security.KeyPairGenerator;
import java.security.PrivateKey;
import java.security.PublicKey;
import java.security.Signature;
import java.security.interfaces.DSAPrivateKey;
import java.security.interfaces.DSAPublicKey;
import java.security.spec.PKCS8EncodedKeySpec;
import java.security.spec.X509EncodedKeySpec;
/**
* DSS(Digital Signature Standard) 数字签名标准
* DSA(Digital Signature Algorithm) 数字签名算法
*
* @author liuming
* @create 2018/4/13
*/
public class DSA {
private static String srcMsg = "imooc security dsa";
public static void main(String[] args) {
jdkDSA(srcMsg);
}
public static void jdkDSA(String srcMsg) {
try {
// 初始化密钥
KeyPairGenerator keyPairGenerator = KeyPairGenerator.getInstance("DSA");
keyPairGenerator.initialize(512);
KeyPair keyPair = keyPairGenerator.generateKeyPair();
DSAPublicKey dsaPublicKey = (DSAPublicKey) keyPair.getPublic();
DSAPrivateKey dsaPrivateKey = (DSAPrivateKey) keyPair.getPrivate();
// 执行签名
PKCS8EncodedKeySpec pkcs8EncodedKeySpec = new PKCS8EncodedKeySpec(dsaPrivateKey.getEncoded());
KeyFactory keyFactory = KeyFactory.getInstance("DSA");
PrivateKey privateKey = keyFactory.generatePrivate(pkcs8EncodedKeySpec);
Signature signature = Signature.getInstance("SHA1withDSA");
signature.initSign(privateKey);
signature.update(srcMsg.getBytes());
byte[] bytes = signature.sign();
System.out.println(Hex.encodeHexString(bytes));
// 验证签名
X509EncodedKeySpec x509EncodedKeySpec = new X509EncodedKeySpec(dsaPublicKey.getEncoded());
keyFactory = KeyFactory.getInstance("DSA");
PublicKey publicKey = keyFactory.generatePublic(x509EncodedKeySpec);
signature = Signature.getInstance("SHA1withDSA");
signature.initVerify(publicKey);
signature.update(srcMsg.getBytes());
boolean verfied = signature.verify(bytes);
System.out.println(verfied);
} catch (Exception e) {
e.printStackTrace();
}
}
}
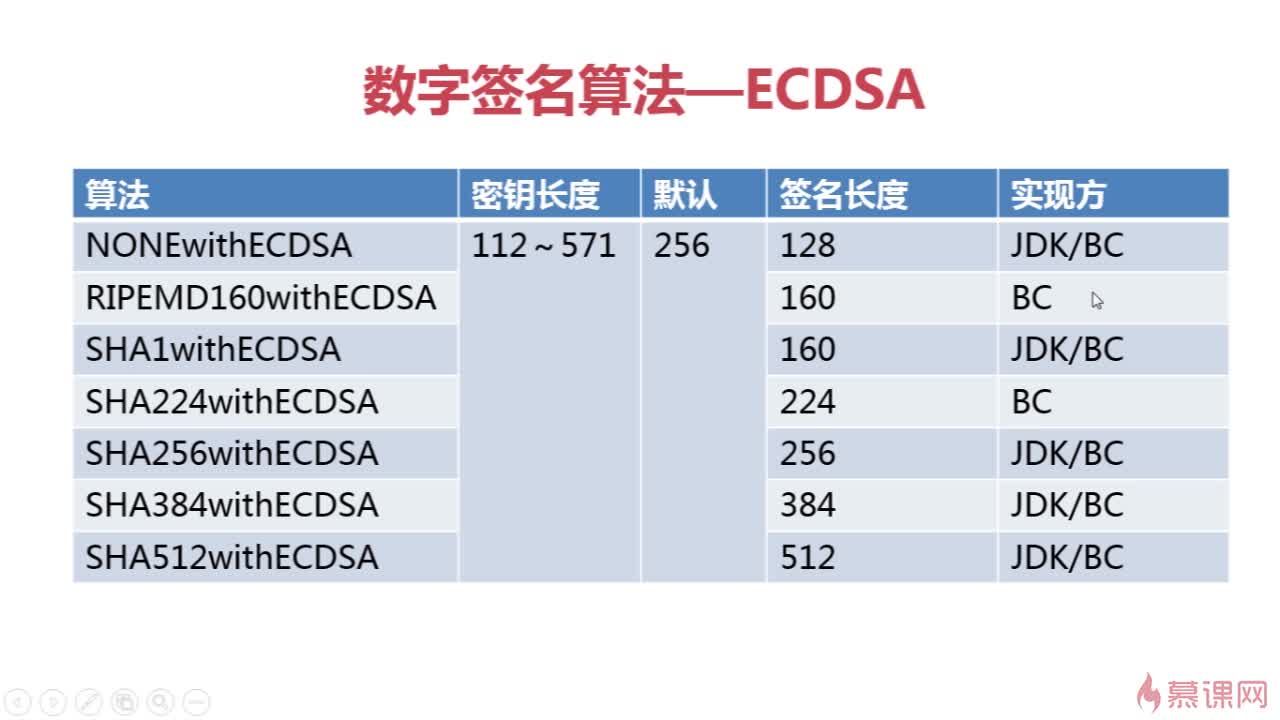
ECDSA
import org.apache.commons.codec.binary.Hex;
import java.security.KeyFactory;
import java.security.KeyPair;
import java.security.KeyPairGenerator;
import java.security.PrivateKey;
import java.security.PublicKey;
import java.security.Signature;
import java.security.interfaces.ECPrivateKey;
import java.security.interfaces.ECPublicKey;
import java.security.spec.PKCS8EncodedKeySpec;
import java.security.spec.X509EncodedKeySpec;
/**
* ECDSA(Elliptic Curve Digital Signature Algorithm) 椭圆曲线数字签名算法
*
* @author liuming
* @create 2018/4/13
*/
public class ECDSA {
private static String srcMsg = "imooc security ecdsa";
public static void main(String[] args) {
jdkECDSA(srcMsg);
}
public static void jdkECDSA(String srcMsg) {
try {
// 初始化密钥
KeyPairGenerator keyPairGenerator = KeyPairGenerator.getInstance("EC");
keyPairGenerator.initialize(256);
KeyPair keyPair = keyPairGenerator.generateKeyPair();
ECPublicKey ecPublicKey = (ECPublicKey) keyPair.getPublic();
ECPrivateKey ecPrivateKey = (ECPrivateKey) keyPair.getPrivate();
// 执行签名
PKCS8EncodedKeySpec pkcs8EncodedKeySpec = new PKCS8EncodedKeySpec(ecPrivateKey.getEncoded());
KeyFactory keyFactory = KeyFactory.getInstance("EC");
PrivateKey privateKey = keyFactory.generatePrivate(pkcs8EncodedKeySpec);
Signature signature = Signature.getInstance("SHA1withECDSA");
signature.initSign(privateKey);
signature.update(srcMsg.getBytes());
byte[] bytes = signature.sign();
System.out.println(Hex.encodeHexString(bytes));
// 验证签名
X509EncodedKeySpec x509EncodedKeySpec = new X509EncodedKeySpec(ecPublicKey.getEncoded());
keyFactory = KeyFactory.getInstance("EC");
PublicKey publicKey = keyFactory.generatePublic(x509EncodedKeySpec);
signature = Signature.getInstance("SHA1withECDSA");
signature.initVerify(publicKey);
signature.update(srcMsg.getBytes());
boolean verfied = signature.verify(bytes);
System.out.println(verfied);
} catch (Exception e) {
e.printStackTrace();
}
}
}