版权声明:本文为博主原创文章,未经博主允许不得转载。 https://blog.csdn.net/tangsilian/article/details/84635971
参考:
参考:
https://github.com/airbus-seclab/android_emuroot/blob/master/docs/Blackhoodie18/emuroot_slides.pdf
aim:了解其授权的实现。
常见的root方案和对应的问题
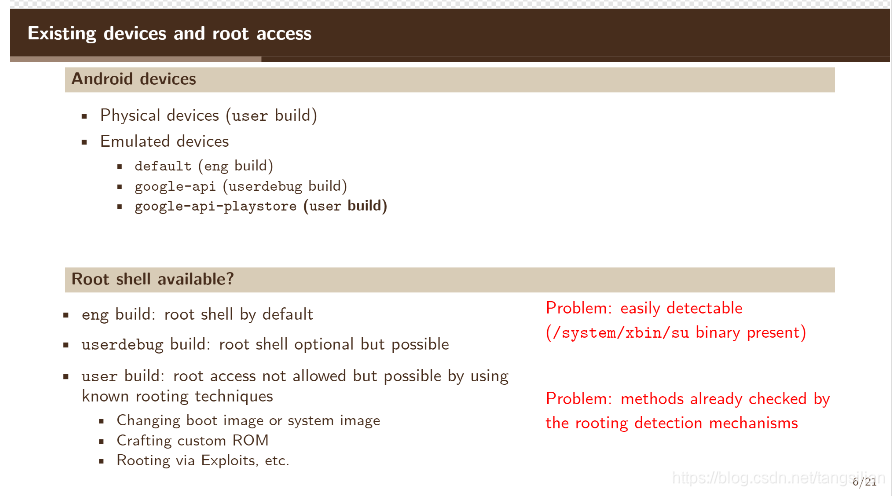
三种root方案:
重刷boot image或者system image
自定义ROM
利用漏洞提权
缺点是存在易被检测的特点,所以如何让APK检测不到自己在root的机器上运行呢?
先了解进程的task_struct

决定进程权限的cred结构体
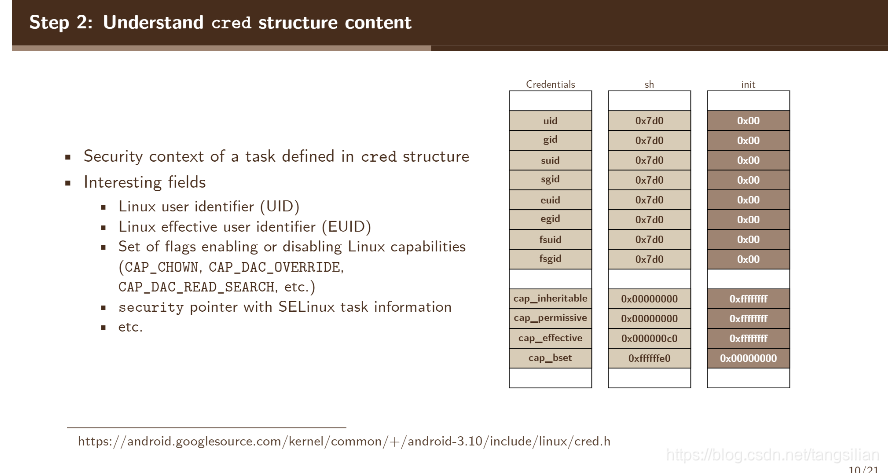
uid_t uid; /* real UID of the task */
gid_t gid; /* real GID of the task */
uid_t suid; /* saved UID of the task */
gid_t sgid; /* saved GID of the task */
uid_t euid; /* effective UID of the task */
gid_t egid; /* effective GID of the task */
uid_t fsuid; /* UID for VFS ops */
gid_t fsgid; /* GID for VFS ops */
unsigned securebits; /* SUID-less security management */
kernel_cap_t cap_inheritable; /* caps our children can inherit */
kernel_cap_t cap_permitted; /* caps we're permitted */
kernel_cap_t cap_effective; /* caps we can actually use */
kernel_cap_t cap_bset; /* capability bounding set */
使用cat /proc/pid/status对比普通shell进程和root进程的cred标志位的值

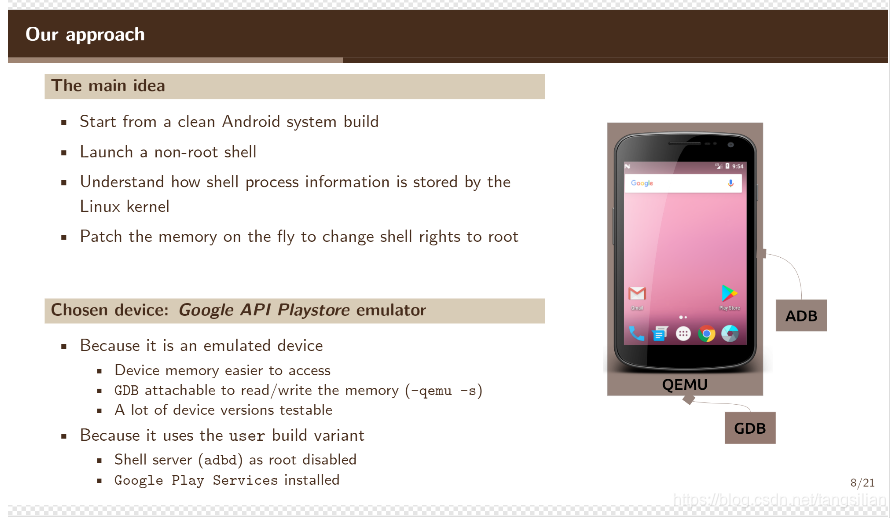
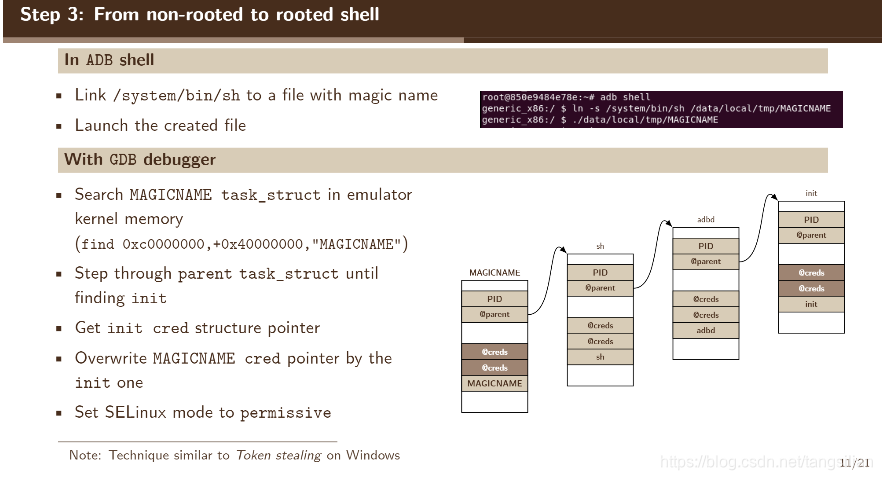
如何从一个non-rooted的shell到root的shell
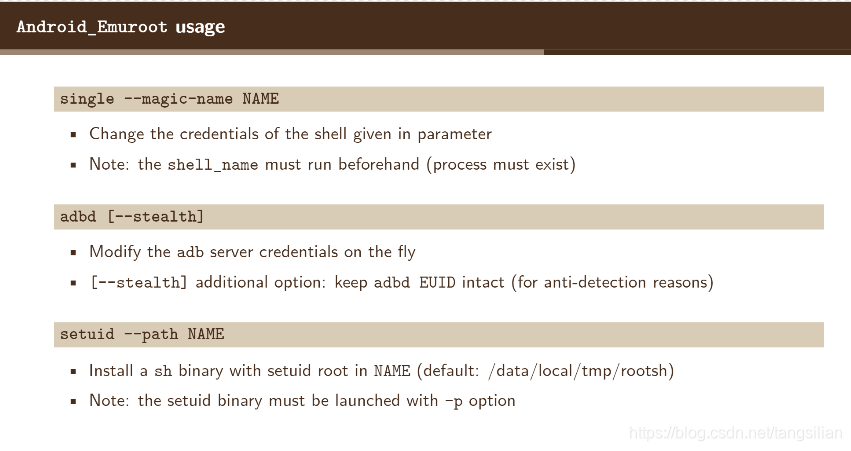
三种授权的方案