版权声明:本文为博主原创文章,未经博主允许不得转载。个人独立博客:https://ichenwin.github.io GitHub、知乎等网站用户名:iChenwin https://blog.csdn.net/u013993802/article/details/84946333
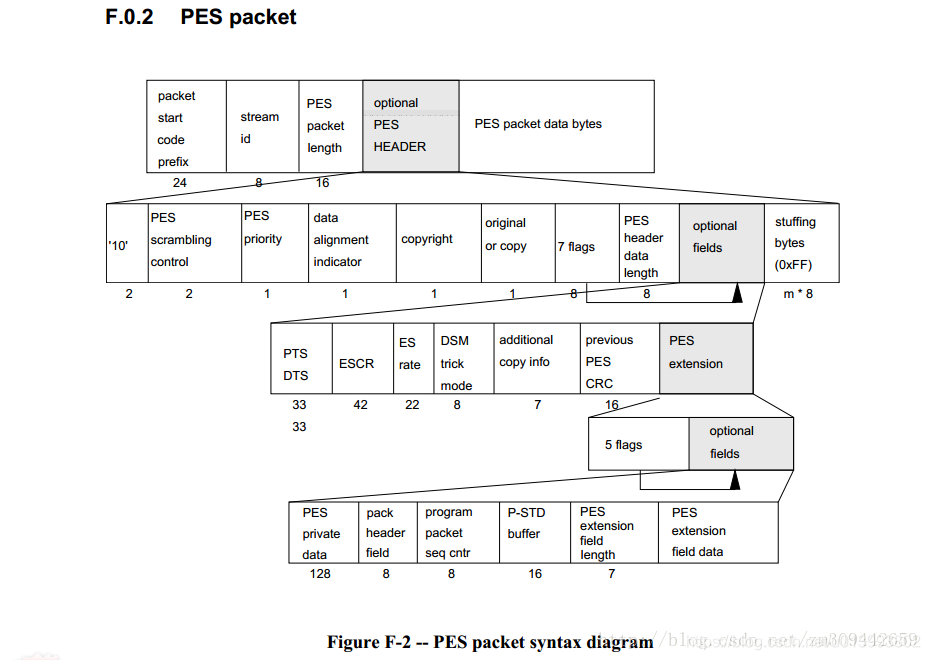
- PES包结构图解:
- PES前面几个字段填写方法:
// 生成 pes 头数据
buffer[0] = 0x00;
buffer[1] = 0x00;
buffer[2] = 0x01;
buffer[3] = (unsigned char)(pes->stream_id);
buffer[4] = (unsigned char)((pes_header_len_syt >> 8) & 0xff);
buffer[5] = (unsigned char)(pes_header_len_syt & 0xff);
buffer[6] = (1<<7)// 2 - check bits '10'
| ((prc->encrypt & 0x03) << 4)// 2 - PES_scrambling_control(0)
| ((pes_priority & 1) << 3)// 1 - PES_priority(0)
| (((~stuff_flag) << 1) & 0x04) // 1 - data_alignment_indicator(0)
| 0 // 1 - copyright(0)
| 0; // 1 - original_or_copy(0)
buffer[7] = (((unsigned char)pes->add_pts) << 7) | ((unsigned char)pes->add_user_data);
// buffer[7] = ((unsigned char)pes->add_pts) << 7;
// 2 - PTS_DTS_flags()
// 1 - ESCR_flag(0)
// 1 - ES_rate_flag(0)
// 1 - DSM_trick_mode_flag(0)
// 1 - additional_copy_info_flag(0)
// 1 - PES_CRC_flag(0)
// 1 - PES_extension_flag()
buffer[8] = (unsigned char)pes_header_ext_len; // 8 - PES_header_data_length
pos = 9;
if (pes->add_pts)
{
pts = prc->ptime_stamp;
buffer[pos++] = (pts >> 28 & 0x0e) | 0x21; // 4 - '0010'
// 3 - PTS [32..30]
// 1 - marker_bit
buffer[pos++] = (pts >> 21); // 8 - PTS [29..22]
buffer[pos++] = (pts >> 13 & 0xfe) | 0x01; // 7 - PTS [21..15]
// 1 - marker_bit
buffer[pos++] = (pts >> 6); // 8 - PTS [14..7]
buffer[pos++] = (pts << 2 & 0xfc) | 0x01; // 7 - PTS [6..0]
// 1 - marker_bit
}
- 接收方PTS时间戳的获取
PTS和DTS字段,本来有效信息是33位,扩展至5个字节,也就是40位。扩展方式:
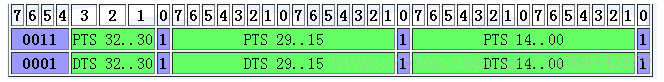
通过上边这个图可以清楚地看到,PTS的33位的各部分,如果从左至右的绿色部分分别为PTS1,PTS2,PTS3的话,那么PTS的计算:
PTS = (PTS1 & 0x0e) << 29 + (PTS2 & 0xfffe) << 14 + (PTS3 & 0xfffe ) >> 1;
DTS(如果有)紧接着后边读取5个字节的数据,也是这样求出来的。