一、服务的控制
1、服务的控制命令
systemctl list-units #列出已经开启的服务当前的状态
list-unit-files #列出所有服务开机启动的状态
set-default multi-user.target #设定系统启动级别为图形模式
systemctl start 服务名 #开启服务
stop 服务名 #暂停服务
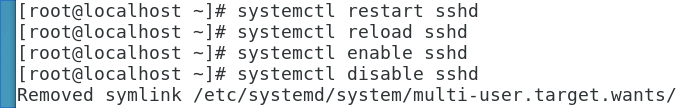
restart 服务名 #关机重新加载服务
reload 服务名 #不关机重新加载服务
enable 服务名 #开机自启服务
disable 服务名 #开机不自启服务
例:




2、sshd 的key认证
ssh-keygen #生成密钥的命令
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa):#指定保存加密字符的文件(使用默认)
Enter passphrase (empty for no passphrase): #设定密码(使用默认)
Enter same passphrase again: #确认密码(使用默认)
Your identification has been saved in /root/.ssh/id_rsa. #私钥(钥匙)
Your public key has been saved in /root/.ssh/id_rsa.pub. #公钥(锁)
The key fingerprint is:
cd:0b:9b:3e:ea:4c:cb:89:4f:9e:e4:8f:be:12:c3:85 [email protected]
The key's randomart image is:
+--[ RSA 2048]----+
| |
| |
| . |
| E . o |
| . . S o |
| + + . |
| o+ o . |
| .X *. |
| .=/+o. |
+-----------------+ #加密服务
ssh-copy-id -i /root/.ssh/id_rsa.pub [email protected] #给自己加锁
The authenticity of host '172.25.254.138 (172.25.254.138)' can't be established.
ECDSA key fingerprint is eb:24:0e:07:96:26:b1:04:c2:37:0c:78:2d:bc:b0:08.
Are you sure you want to continue connecting (yes/no)? yes
/usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed
/usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys
[email protected]'s password:
Number of key(s) added: 1
Now try logging into the machine, with: "ssh '[email protected]'"
and check to make sure that only the key(s) you wanted were added.
authorized_keys id_rsa id_rsa.pub known_hosts
^
#此文件出现标示加密完成
例:

3、sshd的安全设定
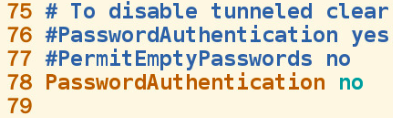
vim /etc/ssh/sshd_config #进入sshd的安全设定文件
78: PasswordAuthentication yes/no #是否允许用户通过登陆系统的密码做sshd的认证
48: PermitRootLogin yes/no #是否允许root用户通过sshd服务的认证
52: AllowUsers username #(服务端存在的用户并且‘有锁’)sshd用户的白名单
DenyUsers username #(服务端存在的用户并且‘有锁’)sshd用户的黑名单例:

4、用户登陆信息的审计
w #查看正在使用当前系统的用户
13:37:03 up 4:27, 3 users, load average: 0.00, 0.01, 0.05
USER TTY LOGIN@ IDLE JCPU PCPU WHAT
root :0 09:09 ?xdm? 26.97s 0.12s gdm-session-worker [pam/gdm-passwo
root pts/0 09:09 4:27m 0.02s 0.02s /bin/bash
root pts/1 13:36 7.00s 0.03s 0.01s w
w -f #查看使用来源
w -i #显示IP
/var/run/utmp
last #查看使用过并退出的用户信息 /var/log/wtmp
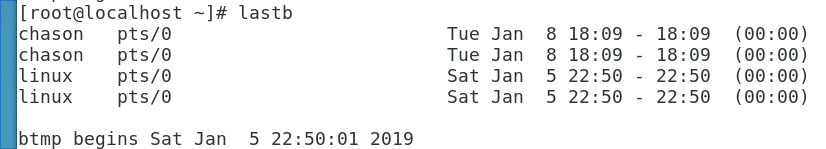
lastb # 试图登陆但没有成功的用户 /var/log/btmp