一、Ingerss搭建
到github上下载Ingress的yaml文件进行修改
https://github.com/kubernetes/ingress-nginx/tree/nginx-0.18.0/deploy
1、先创建一个文件夹存放Ingress相关yaml文件
mkdir Ingress
cd Ingress
2、创建一个命名空间,放置ingress相关配置。
vim namespace.yaml
kubectl create -f namespace.yaml
[root@k8s-master-101 Ingress]# cat namespace.yaml
---
apiVersion: v1
kind: Namespace
metadata:
name: ingress-nginx
3、vim default-backend.yaml
这个文件用来创建default-backend的depolyment和service
如果外界访问的域名不存在的话,则会默认转发到defalut-http-backend这个service,会直接返回404
[root@k8s-master-101 Ingress]# cat default-backend.yaml
---
apiVersion: extensions/v1beta1
kind: Deployment
metadata:
name: default-http-backend
labels:
app: default-http-backend
namespace: ingress-nginx
spec:
replicas: 1
selector:
matchLabels:
app: default-http-backend
template:
metadata:
labels:
app: default-http-backend
spec:
terminationGracePeriodSeconds: 60
containers:
- name: default-http-backend
# Any image is permissible as long as:
# 1. It serves a 404 page at /
# 2. It serves 200 on a /healthz endpoint
image: registry.cn-hangzhou.aliyuncs.com/google_containers/defaultbackend:1.4
livenessProbe:
httpGet:
path: /healthz
port: 8080
scheme: HTTP
initialDelaySeconds: 30
timeoutSeconds: 5
ports:
- containerPort: 8080
resources:
limits:
cpu: 10m
memory: 20Mi
requests:
cpu: 10m
memory: 20Mi
---
apiVersion: v1
kind: Service
metadata:
name: default-http-backend
namespace: ingress-nginx
labels:
app: default-http-backend
spec:
ports:
- port: 80
targetPort: 8080
selector:
app: default-http-backend
kubectl create -f default-backend.yaml
4、configmap 存放tcp udp 虚拟主机的配置
vim tcp-services-configmap.yaml
vim udp-services-configmap.yaml
[root@k8s-master-101 Ingress]# cat tcp-services-configmap.yaml
---
kind: ConfigMap
apiVersion: v1
metadata:
name: tcp-services
namespace: ingress-nginx
[root@k8s-master-101 Ingress]# cat udp-services-configmap.yaml
---
kind: ConfigMap
apiVersion: v1
metadata:
name: udp-services
namespace: ingress-nginx
创建configmap
kubectl create -f tcp-services-configmap.yaml
kubectl create -f udp-services-configmap.yaml
5、vim rbac.yaml 这个yaml文件主要是角色的创建和绑定,负责Ingress的RBAC授权的控制,其创建了Ingress用到的ServiceAccount、ClusterRole、Role、RoleBinding、ClusterRoleBinding
[root@k8s-master-101 Ingress]# cat rbac.yaml
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRole
metadata:
name: nginx-ingress-clusterrole
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- "extensions"
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- "extensions"
resources:
- ingresses/status
verbs:
- update
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: Role
metadata:
name: nginx-ingress-role
namespace: ingress-nginx
rules:
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
resourceNames:
# Defaults to "<election-id>-<ingress-class>"
# Here: "<ingress-controller-leader>-<nginx>"
# This has to be adapted if you change either parameter
# when launching the nginx-ingress-controller.
- "ingress-controller-leader-nginx"
verbs:
- get
- update
- apiGroups:
- ""
resources:
- configmaps
verbs:
- create
- apiGroups:
- ""
resources:
- endpoints
verbs:
- get
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: RoleBinding
metadata:
name: nginx-ingress-role-nisa-binding
namespace: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: nginx-ingress-role
subjects:
- kind: ServiceAccount
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
name: nginx-ingress-clusterrole-nisa-binding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: nginx-ingress-clusterrole
subjects:
- kind: ServiceAccount
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
创建rabc
kubectl create -f rbac.yaml
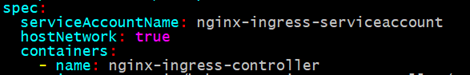
6、mv with-rbac.yaml deployment.yaml 改下名字
vim deployment.yaml
这个文件创建nginx-ingress-controller这个deployment,副本数选择两个,一个node一个。Ingress-controller的作用是将新加入的Ingress进行转化为Nginx的配置。
Ingress Contronler 通过与 Kubernetes API 交互,能够动态的获取cluster中Ingress rules的变化,生成一段 Nginx 配置,再写到 Nginx-ingress-control的 Pod 里,reload pod 使规则生效。从而实现注册的service及其对应域名/IP/Port的动态添加和解析。
[root@k8s-master-101 Ingress]# cat deployment.yaml
---
apiVersion: extensions/v1beta1
kind: Deployment
metadata:
name: nginx-ingress-controller
namespace: ingress-nginx
spec:
replicas: 2
selector:
matchLabels:
app: ingress-nginx
template:
metadata:
labels:
app: ingress-nginx
annotations:
prometheus.io/port: '10254'
prometheus.io/scrape: 'true'
spec:
serviceAccountName: nginx-ingress-serviceaccount
hostNetwork: true
containers:
- name: nginx-ingress-controller
image: registry.cn-hangzhou.aliyuncs.com/google_containers/nginx-ingress-controller:0.18.0
args:
- /nginx-ingress-controller
- --default-backend-service=$(POD_NAMESPACE)/default-http-backend
- --configmap=$(POD_NAMESPACE)/nginx-configuration
- --tcp-services-configmap=$(POD_NAMESPACE)/tcp-services
- --udp-services-configmap=$(POD_NAMESPACE)/udp-services
- --publish-service=$(POD_NAMESPACE)/ingress-nginx
- --annotations-prefix=nginx.ingress.kubernetes.io
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
ports:
- name: http
containerPort: 80
- name: https
containerPort: 443
livenessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 1
注释:
增加hostNetwork:true这一行,这是直接定义Pod网络的方式。定义后,Ingress-controller的IP就与宿主机上一样,并且端口也是宿主机上的端口。这样就可以通过宿主机直接访问到Ingress-controller,然后Ingress-controller则会转发我们的请求到响应后端。
默认下面部分还有args和env中间还有几行安全选项,删除后才能创建pod

kubectl create -f deployment.yaml

7、kubectl get pods -n ingress-nginx -o wide
每台node上一个nginx-ingress-controller
[root@k8s-master-101 Ingress]# kubectl get pods -n ingress-nginx -o wide
NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE
default-http-backend-86569b9d95-8ggjw 1/1 Running 24 14d 172.17.71.8 10.0.0.103 <none>
nginx-ingress-controller-6b46769f55-sf7kg 1/1 Running 20 14d 10.0.0.102 10.0.0.102 <none>
nginx-ingress-controller-6b46769f55-xx4tj 1/1 Running 15 14d 10.0.0.103 10.0.0.103 <none>
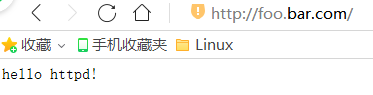
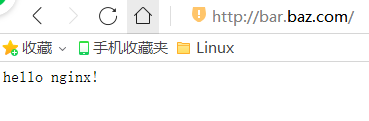
二、http测试
1、创建nginx和httpd的deployment和pod
[root@k8s-master-101 ~]# kubectl run --image=nginx nginx
deployment.apps/nginx created
[root@k8s-master-101 ~]# kubectl run --image=httpd httpd
deployment.apps/httpd created
[root@k8s-master-101 ~]# kubectl get pods
NAME READY STATUS RESTARTS AGE
httpd-7db5849b8-bxpcg 1/1 Running 0 2m51s
nginx-dbddb74b8-wtr7v 1/1 Running 0 3m2s
2、创建service
[root@k8s-master-101 ~]# kubectl expose deployment nginx --port=80 --target-port=80
service/nginx exposed
[root@k8s-master-101 ~]# kubectl expose deployment httpd --port=80 --target-port=80
service/httpd exposed
#查看service地址
[root@k8s-master-101 ~]# kubectl get svc -o wide
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE SELECTOR
httpd ClusterIP 10.10.10.75 <none> 80/TCP 82s run=httpd
kubernetes ClusterIP 10.10.10.1 <none> 443/TCP 20d <none>
nginx ClusterIP 10.10.10.143 <none> 80/TCP 92s run=nginx
3、修改httpd容器首页信息
[root@k8s-master-101 ~]# kubectl exec -it httpd-7db5849b8-bxpcg bash
root@httpd-7db5849b8-bxpcg:/usr/local/apache2# cd htdocs/
root@httpd-7db5849b8-bxpcg:/usr/local/apache2/htdocs# echo "hello httpd!" > index.html
root@httpd-7db5849b8-bxpcg:/usr/local/apache2/htdocs# exit
4、修改nginx容器首页信息
[root@k8s-master-101 ~]# kubectl exec -it nginx-dbddb74b8-wtr7v bash
root@nginx-dbddb74b8-wtr7v:/# cd /usr/share/nginx/html/
root@nginx-dbddb74b8-wtr7v:/usr/share/nginx/html# echo "hello nginx!" > index.html
root@nginx-dbddb74b8-wtr7v:/usr/share/nginx/html# exit
5、在node节点curl测试一下能否访问
[root@k8s-node1-102 ~]# curl 10.10.10.75
hello httpd!
[root@k8s-node1-102 ~]# curl 10.10.10.143
hello nginx!
6、创建Ingress匹配serviceName
vim http.yaml
[root@k8s-master-101 Ingress]# cat http.yaml
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: httpd-test
spec:
rules:
- host: foo.bar.com
http:
paths:
- backend:
serviceName: httpd
servicePort: 80
- host: bar.baz.com
http:
paths:
- backend:
serviceName: nginx
servicePort: 80
[root@k8s-master-101 Ingress]# kubectl create -f http.yaml
[root@k8s-master-101 Ingress]# kubectl get ingress
NAME HOSTS ADDRESS PORTS AGE
httpd-test foo.bar.com,bar.baz.com 80 14d
7、修改host文件,把域名和IP对应,用哪个node都可以,因为前面Ingress-controller在两个节点上都部署了。

8、在浏览器上访问
9、进入容器查看nginx-ingress-controller的具体实现
[root@k8s-master-101 Ingress]# kubectl get pod -n ingress-nginx
NAME READY STATUS RESTARTS AGE
default-http-backend-86569b9d95-8ggjw 1/1 Running 25 15d
nginx-ingress-controller-6b46769f55-sf7kg 1/1 Running 21 14d
nginx-ingress-controller-6b46769f55-xx4tj 1/1 Running 16 15d
[root@k8s-master-101 Ingress]# kubectl exec -it nginx-ingress-controller-6b46769f55-sf7kg bash -n ingress-nginx
root@k8s-node1-102:/etc/nginx# more /etc/nginx/nginx.conf
10、里面主机的配置
#里面有相关配置
## start server bar.baz.com
server {
server_name bar.baz.com ;
listen 80;
listen [::]:80;
set $proxy_upstream_name "-";
location / {
set $namespace "default";
set $ingress_name "httpd-test";
set $service_name "httpd";
set $service_port "80";
set $location_path "/";
rewrite_by_lua_block {
balancer.rewrite()
}
log_by_lua_block {
balancer.log()
monitor.call()
}
port_in_redirect off;
set $proxy_upstream_name "default-nginx-80";
client_max_body_size "1m";
proxy_set_header Host $best_http_host;
# Pass the extracted client certificate to the backend
# Allow websocket connections
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection $connection_upgrade;
proxy_set_header X-Request-ID $req_id;
proxy_set_header X-Real-IP $the_real_ip;
proxy_set_header X-Forwarded-For $the_real_ip;
proxy_set_header X-Forwarded-Host $best_http_host;
proxy_set_header X-Forwarded-Port $pass_port;
proxy_set_header X-Forwarded-Proto $pass_access_scheme;
proxy_set_header X-Original-URI $request_uri;
proxy_set_header X-Scheme $pass_access_scheme;
# Pass the original X-Forwarded-For
proxy_set_header X-Original-Forwarded-For $http_x_forwarded_for;
# mitigate HTTPoxy Vulnerability
# https://www.nginx.com/blog/mitigating-the-httpoxy-vulnerability-with-nginx/
proxy_set_header Proxy "";
# Custom headers to proxied server
proxy_connect_timeout 5s;
proxy_send_timeout 60s;
proxy_read_timeout 60s;
proxy_buffering "off";
proxy_buffer_size "4k";
proxy_buffers 4 "4k";
proxy_request_buffering "on";
proxy_http_version 1.1;
proxy_cookie_domain off;
proxy_cookie_path off;
# In case of errors try the next upstream server before returning an error
proxy_next_upstream error timeout;
proxy_next_upstream_tries 3;
proxy_pass http://upstream_balancer;
proxy_redirect off;
}
}
11、流程大概:首先创建deployment,和它所拥有的pod
然后创建service,和deployment关联
最后创建Ingress,和service关联
三、https测试
1、又得制作证书
mkdir -p /root/https
cd /root/https
cfssl print-defaults csr > ca-csr.json
vim ca-csr.json
[root@k8s-master-101 https]# cat ca-csr.json
{
"CN": "wangxiaoyu",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing"
}
]
}
cfssl print-defaults config >ca-config.json
vim ca-config.json
[root@k8s-master-101 https]# cat ca-config.json
{
"signing": {
"default": {
"expiry": "168h"
},
"profiles": {
"www": {
"expiry": "8760h",
"usages": [
"signing",
"key encipherment",
"server auth"
]
},
"client": {
"expiry": "8760h",
"usages": [
"signing",
"key encipherment",
"client auth"
]
}
}
}
}
cfssl gencert --initca ca-csr.json | cfssljson -bare ca –
cfssl print-defaults csr >server-csr.json
vim server-csr.json
[root@k8s-master-101 https]# cat server-csr.json
{
"CN": "www.wangxiaoyu.com",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing"
}
]
}
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem --config=ca-config.json --profile=www server-csr.json | cfssljson -bare server
kubectl create secret tls wangxiaoyu-https --key server-key.pem --cert server.pem
#查看secret
[root@k8s-master-101 https]# kubectl get secret
NAME TYPE DATA AGE
default-token-lshw2 kubernetes.io/service-account-token 3 20d
wangxiaoyu-https kubernetes.io/tls 2 14d
2、cd …/Ingress/
vim https.yaml
[root@k8s-master-101 Ingress]# cat https.yaml
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: https-test
spec:
tls:
- hosts:
- www.wangxiaoyu.com
secretName: wangxiaoyu-https
rules:
- host: www.wangxiaoyu.com
http:
paths:
- backend:
serviceName: nginx
servicePort: 80
kubectl create -f https.yaml
3、访问https
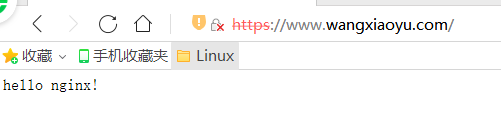
4、大概流程:制作证书,然后生成一个secret秘钥,在Ingress的yaml配置文件中指定secretName。在Ingress资源中引用此Secret即可让Ingress加载并配置为https服务。