学无止境,今天咋们就来整个openvpn,看过我文章的会知道我这个人会的有点杂,没办法,以前搞开发的前几年转运维了,运维的东西很多需要梳理,就记到这边了!不说了。openvpn是个什么东西请百度或谷歌一下。
服务器操作系统:centos7.2 、 openvpn-2.2.2
目录
1) 先将本机的yum换成阿里云的yum源
[root@SCA-LEH600137 ~]# wget -O /etc/yum.repos.d/CentOS-Base.repo http://mirrors.aliyun.com/repo/Centos-7.repo
[root@SCA-LEH600137 ~]# yum clean all
[root@SCA-LEH600137 ~]# yum makecache如果是centos5,则更换如下:
wget -O /etc/yum.repos.d/CentOS-Base.repo http://mirrors.aliyun.com/repo/Centos-5.repo
如果时centos6,则更换如下:
wget -O /etc/yum.repos.d/CentOS-Base.repo http://mirrors.aliyun.com/repo/Centos-6.rep
2)安装依赖的软件包
[root@SCA-LEH600137 ~]# yum install rpm-build gcc lsof -y
[root@SCA-LEH600137 ~]# yum install -y pam-devel*
[root@SCA-LEH600137 ~]# yum install -y lzo lzo-devel openssl openssl-devel pam pam-devel
[root@SCA-LEH600137 ~]# wget http://dl.fedoraproject.org/pub/epel/epel-release-latest-7.noarch.rpm
[root@SCA-LEH600137 ~]# rpm -ivh epel-release-latest-7.noarch.rpm
[root@SCA-LEH600137 ~]# yum install -y pkcs11-helper pkcs11-helper-devel确认已经安装完成:
[root@SCA-LEH600137 ~]# rpm -qa lzo lzo-devel openssl openssl-devel pam pam-devel pkcs11-helper pkcs11-helper-devel
lzo-2.06-8.el7.x86_64
pam-1.1.8-22.el7.x86_64
lzo-devel-2.06-8.el7.x86_64
openssl-devel-1.0.2k-16.el7.x86_64
pam-1.1.8-22.el7.i686
openssl-1.0.2k-16.el7.x86_64
pkcs11-helper-1.11-3.el7.x86_64
pam-devel-1.1.8-22.el7.x86_64
pkcs11-helper-devel-1.11-3.el7.x86_64
[root@SCA-LEH600137 ~]# 3) 安装OpenVPN服务
下载openvpn的源码包
[root@SCA-LEH600137 ~]# wget http://oss.aliyuncs.com/aliyunecs/openvpn-2.2.2.tar.gz
使用rpmbuild将源码包编译成rpm包来进行安装
[root@SCA-LEH600137 ~]# rpmbuild -tb openvpn-2.2.2.tar.gz
执行上面这条命令以后就会正常开始编译了,编译完成以后会在 /root/rpmbuild/RPMS/x86_64 目录下生成 openvpn-2.2.2-1.x86_64.rpm 安装包。

安装
[root@SCA-LEH600137 ~]# ls rpmbuild/RPMS/x86_64/openvpn-2.2.2-1.x86_64.rpm
rpmbuild/RPMS/x86_64/openvpn-2.2.2-1.x86_64.rpm
[root@SCA-LEH600137 ~]# rpm -ivh /root/rpmbuild/RPMS/x86_64/openvpn-2.2.2-1.x86_64.rpm
Preparing... ################################# [100%]
Updating / installing...
1:openvpn-2.2.2-1 ################################# [100%]
Restarting openvpn (via systemctl): [ OK ]4)配置OpenVPN服务(服务端)
初始化PKI
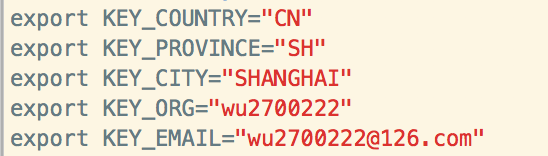
[root@SCA-LEH600137 ~]# cd /usr/share/doc/openvpn-2.2.2/easy-rsa/2.0进入到 /usr/share/doc/openvpn-2.2.2/easy-rsa/2.0 目录下,找到 vars 证书环境文件,修改以下几行 export 定义的参数值
[root@test-vm04 2.0]# vim vars
......
export KEY_COUNTRY="CN" //所在的国家
export KEY_PROVINCE="SH" //所在的省份
export KEY_CITY="SHANGHAI" //所在的城市
export KEY_ORG="wu2700222" //所在的组织
export KEY_EMAIL="[email protected]" //邮件地址
上述参数的值可以自定义设置,对配置无影响。
生成服务端的证书

改为
生成服务端的证书
清除并删除keys目录下的所有key
[root@SCA-LEH600137 ~]# cd /usr/share/doc/openvpn-2.2.2/easy-rsa/2.0
[root@SCA-LEH600137 2.0]# vim vars
[root@SCA-LEH600137 2.0]# ln -s openssl-1.0.0.cnf openssl.cnf
[root@SCA-LEH600137 2.0]# ll openssl*
-rwxr-xr-x 1 root root 7768 Oct 21 2010 openssl-0.9.6.cnf
-rwxr-xr-x 1 root root 8325 Nov 25 2011 openssl-0.9.8.cnf
-rwxr-xr-x 1 root root 8222 Nov 25 2011 openssl-1.0.0.cnf
lrwxrwxrwx 1 root root 17 Dec 26 14:18 openssl.cnf -> openssl-1.0.0.cnf
[root@SCA-LEH600137 2.0]# source ./vars
NOTE: If you run ./clean-all, I will be doing a rm -rf on /usr/share/doc/openvpn-2.2.2/easy-rsa/2.0/keys
[root@SCA-LEH600137 2.0]# ./clean-all
[root@SCA-LEH600137 2.0]# 生成CA证书,刚刚上面已经在vars文件中配置了默认参数值,多次回车完成就可以:
[root@SCA-LEH600137 2.0]# ./build-ca
Generating a 1024 bit RSA private key
...................................++++++
.................++++++
writing new private key to 'ca.key'
-----
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [CN]:
State or Province Name (full name) [SH]:
Locality Name (eg, city) [SHANGHAI]:
Organization Name (eg, company) [wu2700222]:
Organizational Unit Name (eg, section) [changeme]:
Common Name (eg, your name or your server's hostname) [changeme]:
Name [changeme]:
Email Address [[email protected]]:生成服务器证书
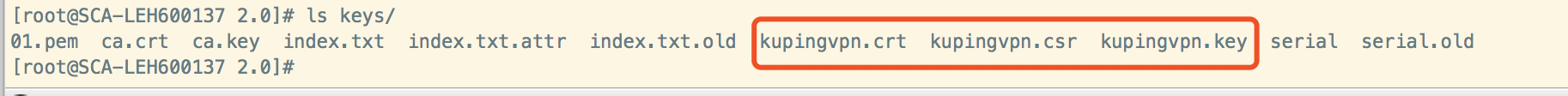
如下kuping是自定义的名字,一直回车,到最后会有两次交互,输入y确认,完成后会在keys目录下保存了kupingvpn.key、kupingvpn.csrl和kupingvpn.crt 三个文件。
[root@SCA-LEH600137 2.0]# ./build-key-server kupingvpn

[root@SCA-LEH600137 2.0]# ls keys/
01.pem ca.crt ca.key index.txt index.txt.attr index.txt.old kupingvpn.crt kupingvpn.csr kupingvpn.key serial serial.old
创建vpn登陆用户的秘钥与证书
如下,创建用户名为kevin的秘钥和证书,一直回车,到最后会有两次确认,只要按y确认即可。完成后,在keys目录下生成1024位RSA服务器密钥kevin.key、kevin.crt和kevin.csr 三个文件。
[root@SCA-LEH600137 2.0]# ./build-key kevin

[root@SCA-LEH600137 2.0]# ls keys/
01.pem ca.crt index.txt index.txt.attr.old kevin.crt kevin.key kupingvpn.csr serial
02.pem ca.key index.txt.attr index.txt.old kevin.csr kupingvpn.crt kupingvpn.key serial.old
-----------------------------------------------------------------------------------------------
如果创建用户证书时报错,可以将keys整个目录删除,然后从source ./vars这一步开始重新操作(慎重,否则之前在keys目录里的用户数据就会都删除)
-----------------------------------------------------------------------------------------------
生成Diffie Hellman参数
[root@SCA-LEH600137 2.0]# ./build-dh
Generating DH parameters, 1024 bit long safe prime, generator 2
This is going to take a long time
.+..............................................................................+.........................................................................................................................................................................+..........................................................................................+........................................................................+..............................................+............................+..............................+.............+..........................................................................................+...................................................+.........+..........+........................+.........................+................................................................................................+.........................................................................+............................................................+.................+.....................+................................................................................+.....................................+........+..............................+..............+......................................................+.........................................................................................................+.....+..................+........................................+...........................................................................................+.....+..................................+.......+....................+......................................................................................................+.........+...+...........+......................................................................................................................................+..........................................+.+.............................................................+...........+.................+...........................+............................................................................................................................+................................................................................................................................+......................................+..................................+.....+............................................+..................................................................................................................................................................................................................................+....................................................................+..+.......+..............................................................................++*++*++*执行了./build-dh后,会在 keys 目录下生成 dh 参数文件 dh1024.pem。该文件客户端验证的时候会用到
[root@SCA-LEH600137 2.0]# ls keys/
01.pem ca.crt dh1024.pem index.txt.attr index.txt.old kevin.csr kupingvpn.crt kupingvpn.key serial.old
02.pem ca.key index.txt index.txt.attr.old kevin.crt kevin.key kupingvpn.csr serial
将/usr/share/doc/openvpn-2.2.2/easy-rsa/2.0/keys 目录下的所有文件复制到 /etc/openvpn下:
复制openvpn服务端配置文件 server.conf 到 /etc/openvpn/ 目录下:
[root@SCA-LEH600137 2.0]# cp -a /usr/share/doc/openvpn-2.2.2/easy-rsa/2.0/keys/* /etc/openvpn/
[root@SCA-LEH600137 2.0]# cp -a /usr/share/doc/openvpn-2.2.2/sample-config-files/server.conf /etc/openvpn/查看server.conf文件的配置
[root@SCA-LEH600137 2.0]# egrep -v "^$|^#|^;" /etc/openvpn/server.conf
port 1194
proto udp
dev tun
ca ca.crt
cert server.crt
key server.key # This file should be kept secret
dh dh1024.pem
server 10.8.0.0 255.255.255.0
ifconfig-pool-persist ipp.txt
keepalive 10 120
comp-lzo
persist-key
persist-tun
status openvpn-status.log
verb 3修改后的配置为
[root@SCA-LEH600137 2.0]# egrep -v "^$|^#|^;" /etc/openvpn/server.conf
local 113.96.61.15 //监听地址(内网或外网地址),最好填写openvpn服务器的公网IP地址(使用"curl ifconfig.me"命令查看)。或者这一行直接注释掉!(我在线上配置的就是注释这行)
port 1194
proto udp
dev tun
ca ca.crt //CA证书路径
cert kupingvpn.crt //此处crt以及下一行的key,请填写生成服务器端证书时用户自定义的名称
key kupingvpn.key
dh dh1024.pem //秘钥交换协议文件
server 10.8.0.0 255.255.255.0 //给vpn客户机分配的地址池。最好别和openvpn部署机的内网ip在一个网段内
ifconfig-pool-persist ipp.txt
push "route 10.0.0.0 255.0.0.0"
client-to-client
keepalive 10 120
comp-lzo
user nobody
group nobody
persist-key
persist-tun
status openvpn-status.log
log openvpn.log
verb 3
5)设置iptables
先设置转发
[root@SCA-LEH600137 2.0]# vim /etc/sysctl.conf
net.ipv4.ip_forward = 1
[root@SCA-LEH600137 2.0]# sysctl -p //使内核参数生效
vm.min_free_kbytes = 409600
vm.vfs_cache_pressure = 200
vm.swappiness = 0
fs.file-max = 1024000
fs.aio-max-nr = 1024000
kernel.sysrq = 1
net.ipv4.ip_forward = 1
添加iptables规则,确保服务器可以转发数据包到外网:
[root@SCA-LEH600137 2.0]# iptables -V
iptables v1.4.21
[root@SCA-LEH600137 2.0]# iptables -t nat -A POSTROUTING -s 10.8.0.0/24 -j MASQUERADE
[root@SCA-LEH600137 2.0]# service iptables save
The service command supports only basic LSB actions (start, stop, restart, try-restart, reload, force-reload, status). For other actions, please try to use systemctl.
[root@SCA-LEH600137 2.0]# iptables -t nat -L
Chain PREROUTING (policy ACCEPT)
target prot opt source destination
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
Chain POSTROUTING (policy ACCEPT)
target prot opt source destination
MASQUERADE all -- 10.8.0.0/24 anywhere
[root@SCA-LEH600137 2.0]# 6)启动OpenVPN
[root@SCA-LEH600137 2.0]# /etc/init.d/openvpn start
或者service openvpn start
加入自启动
chkconfig openvpn on
Starting openvpn (via systemctl): [ OK ]
[root@SCA-LEH600137 2.0]# lsof -i:1194
COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME
openvpn 16532 nobody 5u IPv4 1180988 0t0 UDP *:openvpn
如果1194端口启动不起来,可以通过查看/etc/openvpn/openvpn.log日志进行原因排查
后续给同事开vpn账号,只需要下面几步(比如给wuwei同事开vpn)
[root@SCA-LEH600137 2.0]# pwd
/usr/share/doc/openvpn-2.2.2/easy-rsa/2.0
[root@SCA-LEH600137 2.0]# ./build-key wuwei
[root@SCA-LEH600137 2.0]# /etc/init.d/openvpn restart
Restarting openvpn (via systemctl): [ OK ]
[root@SCA-LEH600137 2.0]# lsof -i:1194
COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME
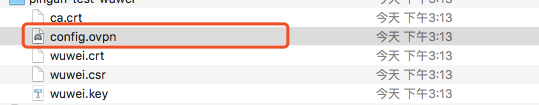
openvpn 18781 nobody 5u IPv4 1186477 0t0 UDP *:openvpn 然后编写wuwei用户的config.ovpn客户端配置文件
[root@SCA-LEH600137 2.0]# vim /tmp/config.ovpn
[root@SCA-LEH600137 2.0]# cat /tmp/config.ovpn
client
dev tun
proto udp
remote 113.96.61.15 1194
resolv-retry infinite
nobind
mute-replay-warnings
ca ca.crt
cert wuwei.crt
key wuwei.key
comp-lzo然后将ca.crt、config.ovpn、wuwei.crt、wuwei.csr、wuwei.key这五个文件放到wuwei用户下
[root@SCA-LEH600137 2.0]# cp keys/wuwei.* keys/ca.crt /tmp/config.ovpn /tmp/wuwei/
[root@SCA-LEH600137 2.0]# ls /tmp/wuwei/
ca.crt config.ovpn wuwei.crt wuwei.csr wuwei.key
[root@SCA-LEH600137 2.0]# cd /tmp/ && tar -zvcf wuwei.tar.gz wuwei
wuwei/
wuwei/wuwei.crt
wuwei/wuwei.csr
wuwei/wuwei.key
wuwei/ca.crt
wuwei/config.ovpn 然后将/tmp/wuwei.tar.gz文件拷贝给用户wuwei,让他在客户机上进行openvpn的连接。
7)openvpn使用说明
7.1)、mac用户
参考https://blog.csdn.net/wu2700222/article/details/85264962

7.2)、windows用户
1. 需要向管理员申请openvpn的配置及秘钥文件(总共包括5个文件:ca.crt证书、config.ovpn客户端配置文件、用户.crt、用户.csr、用户.key)。(其中,config.ovpn客户端文件是直接配置好拷贝给客户机的,这个文件在服务器端是不存在的,需要自己编写)
2. 软件安装包见文末
3. 如果你的电脑没有安装过TAP,安装过程中会有下面的提示,选择安装。
下载地址:
https://openvpn.net/community-downloads/
https://swupdate.openvpn.org/community/releases/openvpn-install-2.4.7-I603.exe
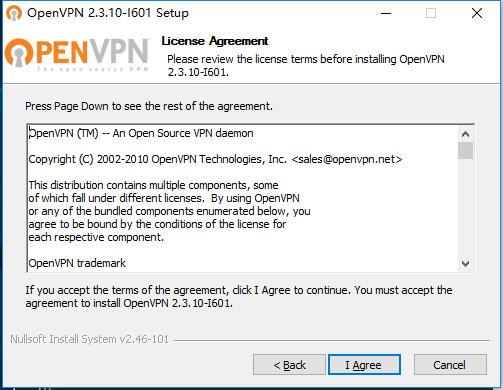
4. 鼠标右键点击软件安装包以管理员方式运行,一直点next 或者agree即可
接着下一步,同意直到安装完成.
5. 安装完成后你的桌面会出现下面的图标,出现这个说明安装成功了。
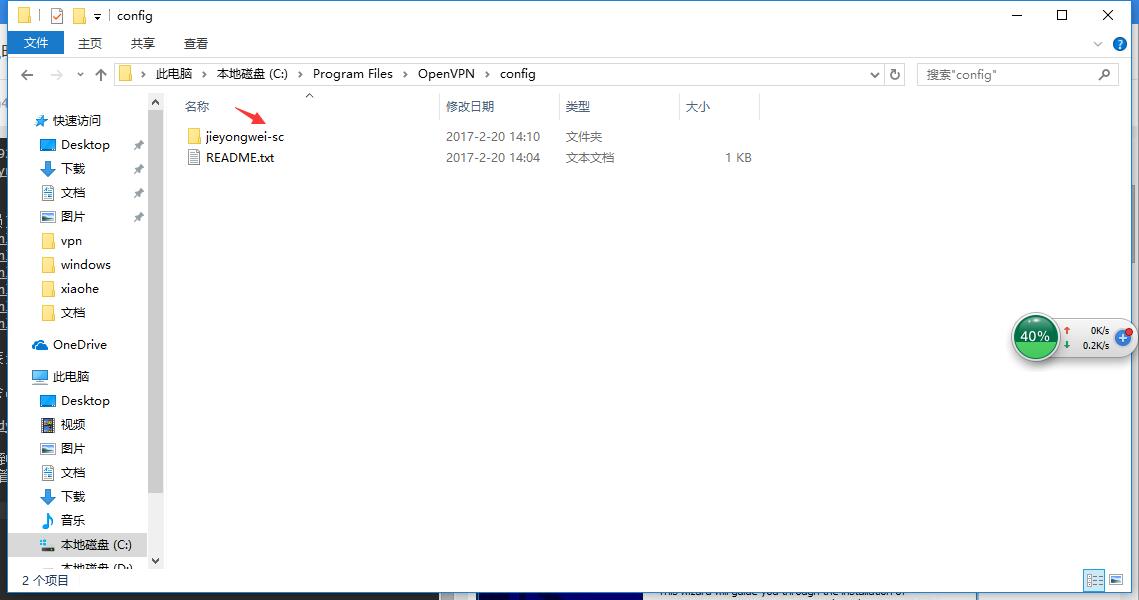
6. 然后打开我的电脑,进到openvpn安装目录即 C:\Program Files\OpenVPN\config 这个文件夹下,然后拿出管理员给你的配置文件,放到这个目录下,如下
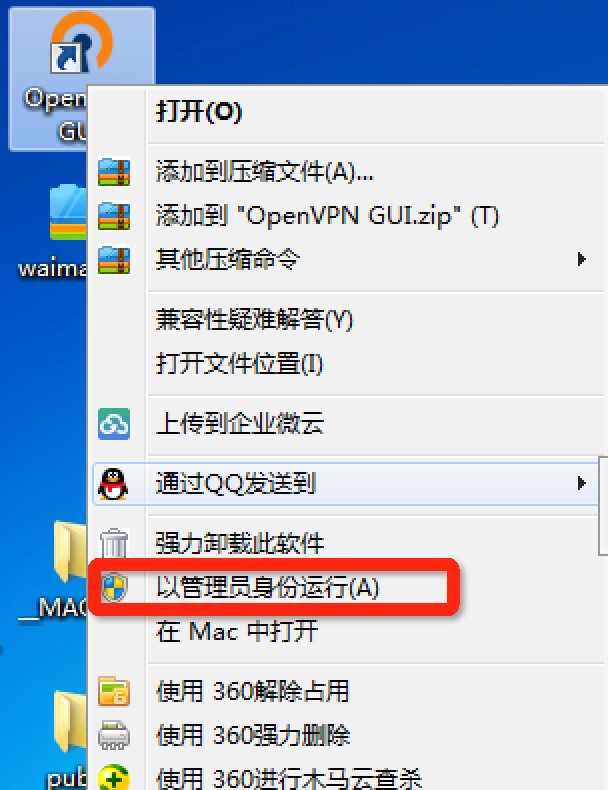
7. 回到桌面,右键openvpn的图标,选择以管理员身份运行
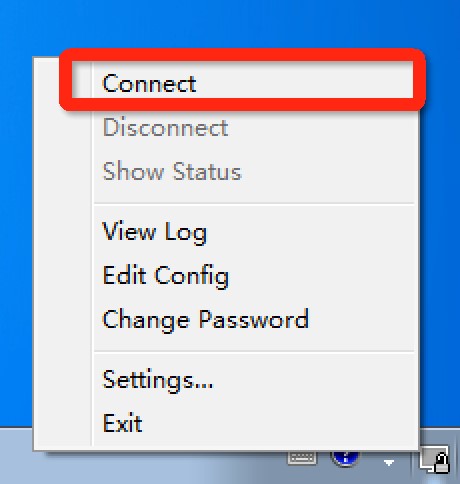
8. 这时候电脑右下角会出现openvpn的程序
9. 鼠标右键,选择connect
10. 程序图标变成绿色,就说明openvpn连接成功了