实验吧web之猫抓老鼠
flag值:KEY: #WWWnsf0cus_NET#
解题步骤:
1.观察题意,说是猫抓老鼠,catch!catch!catch!嘿嘿,不多说了,再说剧透了通过这句话判断是让我们来抓包,于是进入解题页面



2.通过一些列的提交和查询源代码,并没有发现什么问题,于是打开burp进行抓包测试

3.进入解题界面,打开抓包工具,随便输入一点字节或者数字,看burp返回信息
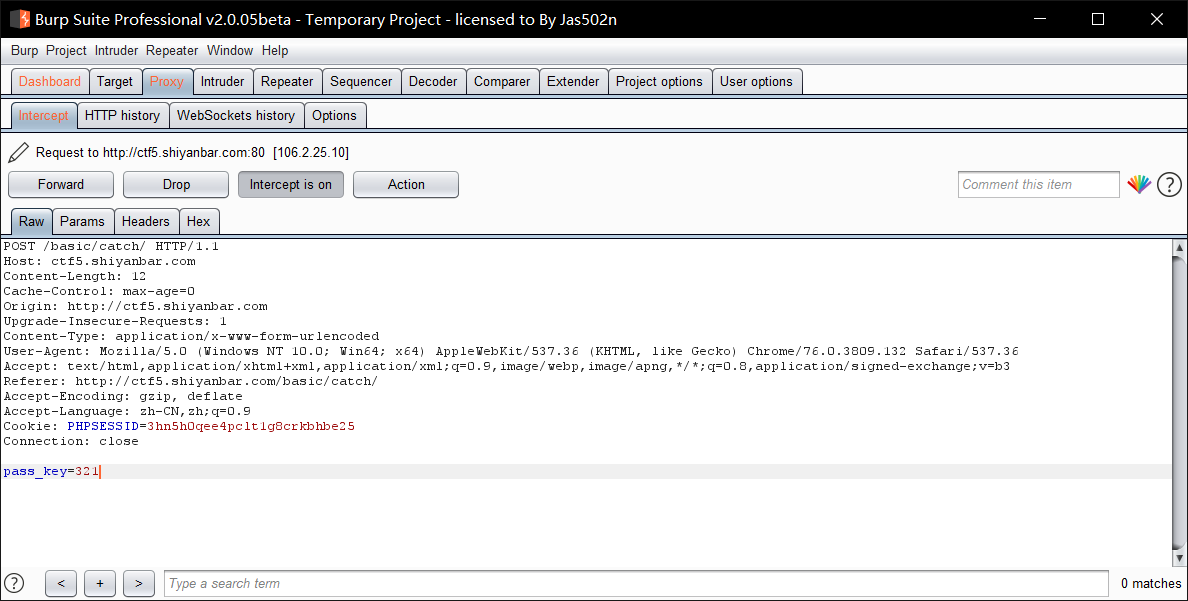

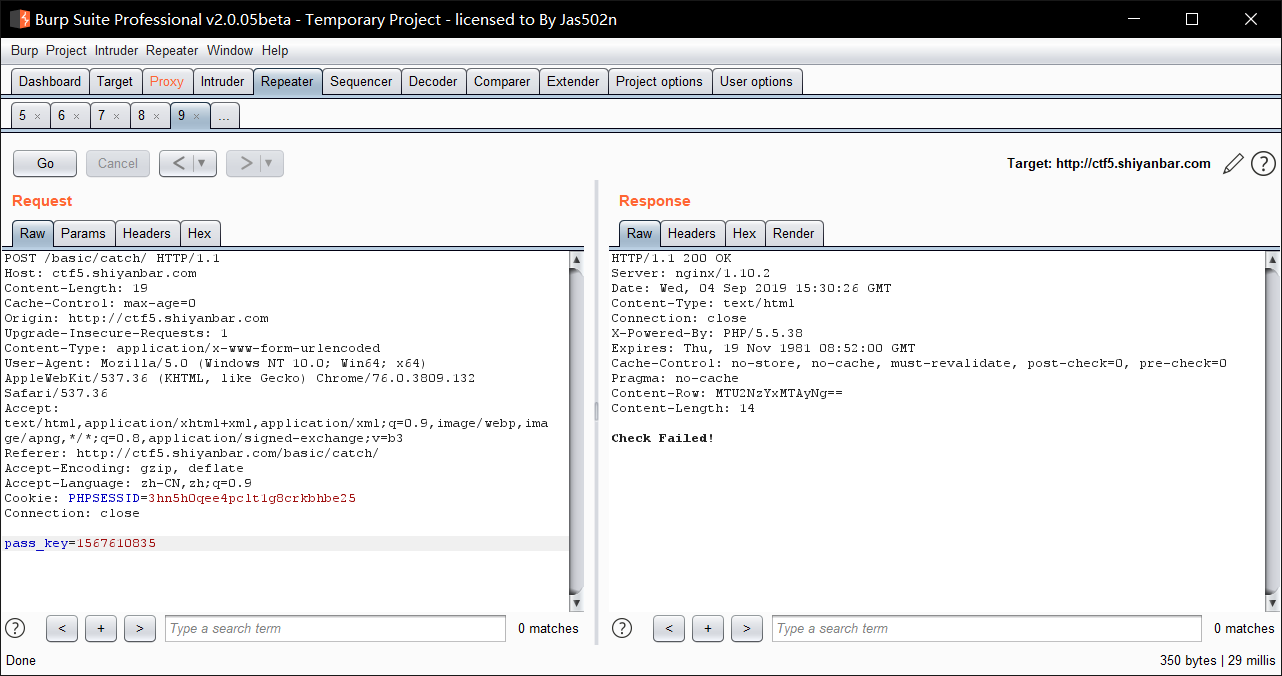
4.根据这个回显判断不出来什么,于是点击Action选择Repeater复制到此功能进行下一步操作
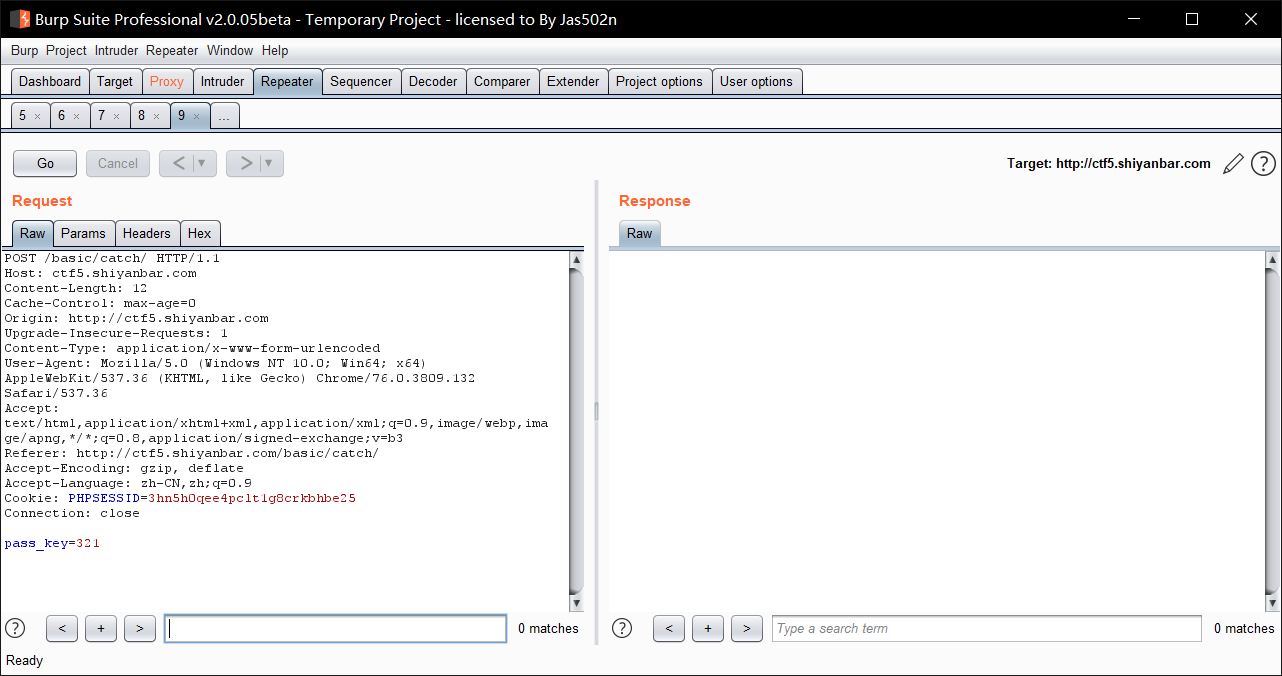

5.点击GO进行下一步,看回显
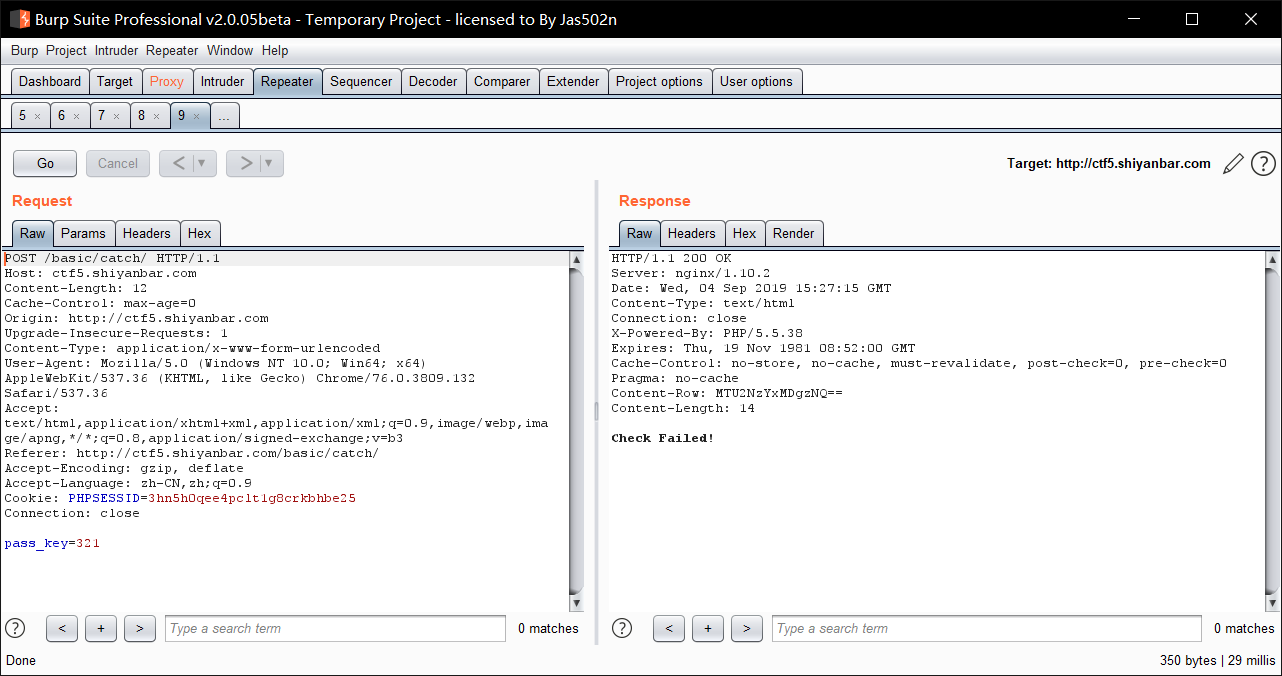

6.回显提示Check Failed!,判断密码错误,这时发现多了一个Content-Row的数值,为base64加密,于是我们进行解密判断


7.填入解密后的数值,发现回显依旧Check Failed!提交错误,进行观察

8.发现Content-Row的base64加密密文发生变化,再次进行解密,发现是时间戳问题


9.由此判断,可以进行时间戳提前的操作,计算出1分钟到2分钟的时间,也就是60s-120s,然后进行base64加密,把加密后的密文放进左侧pass-key中,一直点击GO进行测试
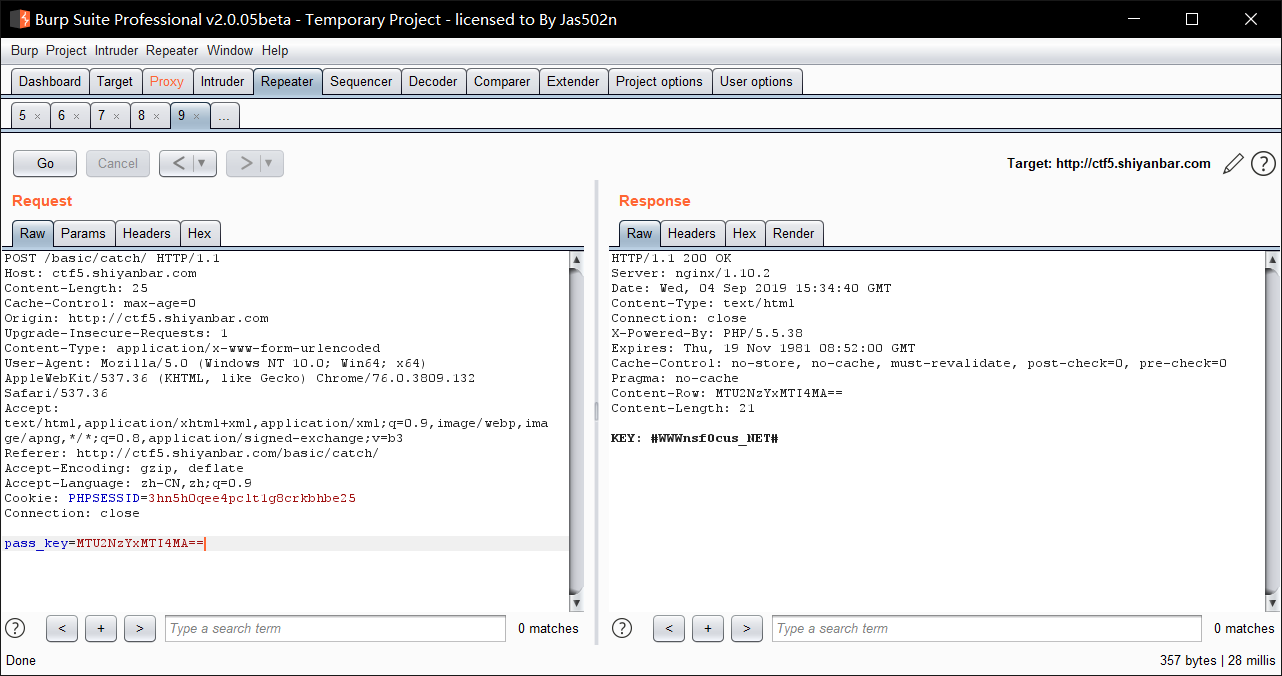

10.右侧答案出现,flag值为KEY: #WWWnsf0cus_NET#,提交成功
11.注意把KEY:去掉