本文关于实现子域授权的介绍,也就是在一级域名下创建一个二级域名在父域名下可以查寻到子域名的信息,也即当别的主机指向父域时,父域可以向别的主机提供迭代查询或递归查询。就像根域和om域。
具体实现:
在父域的配置文件中增加如下项:
1.授权的子区域名称。
2.子区域的名称服务器。
3.子区域的名称服务器的IP地址。
主服务器 172.16.200.129 上配置:父域授权
#cd /var/named
#vim wang.com.zone
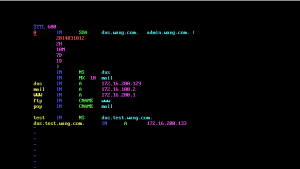
1 $TTL 600
2 @ IN SOA dns.wang.com. admin.wang.com. (
3 2014031012
4 2H
5 10M
6 7D
7 1D
8 )
9 IN NS dns
10 IN MX 10 mail
11 dns IN A 172.16.200.129
12 mail IN A 172.16.100.2
13 WWW IN A 172.16.200.1
14 ftp IN CNAME www
15 pop IN CNAME mail
16
17 test IN NS dns.test.wang.com.
18 dns.test.wang.com. IN A 172.16.200.133
18行的VALUE值要与从服务器中的IP相同,也或者更改从服务器的IP,我的从服务器IP是172.16.200.129
#named-checkconf
#named-checkzone "wang.com" wang.com.zone
#service named reload
#dig -t NS test.wang.com
#systemctl stop firewalld.service
#setenforce 1
关闭防火墙及SELINUX
在这时,肯定是解析失败的。因为没有在从服务器上设置test.wang.com区域
—————————————————————
在子服务器上设置:子域配置
#vim /etc/named.rfc1912.zones
1 // named.rfc1912.zones:
2 //
3 // Provided by Red Hat caching-nameserver package
4 //
5 // ISC BIND named zone configuration for zones recommended by
6 // RFC 1912 section 4.1 : localhost TLDs and address zones
7 // and http://www.ietf.org/internet-drafts/draft-ietf-dnsop-default-local-zones-02.txt
8 // (c)2007 R W Franks
9 //
10 // See /usr/share/doc/bind*/sample/ for example named configuration files.
11 //
12
13 zone "localhost.localdomain" IN {
14 type master;
15 file "named.localhost";
16 allow-update { none; };
17 };
18
19 zone "localhost" IN {
20 type master;
21 file "named.localhost";
22 allow-update { none; };
23 };
24
25 zone "1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.ip6.arpa" IN {
26 type master;
27 file "named.loopback";
28 allow-update { none; };
29 };
30
31 zone "1.0.0.127.in-addr.arpa" IN {
32 type master;
33 file "named.loopback";
34 allow-update { none; };
35 };
36
37 zone "0.in-addr.arpa" IN {
38 type master;
39 file "named.empty";
40 allow-update { none; };
41 };
42
43 zone "test.wang.com" IN {
44 type master;
45 file "test.wang.com.zone";
46 };
47 zone "wang.com" IN {
48 type forward;
49 forwarders { 172.16.200.129; };
50 forward only;
51 };

#vim /var/var/named/test.wang.com.zone
1 $TTL 600
2 @ IN SOA dns.test.wang.com. dnsadmin.tset.wang.com. (
3 2014031001
4 1H
5 5M
6 3D
7 12H
8 )
9 IN NS dns
10 IN MX 10 mail
11 dns IN A 172.16.200.133
12 www IN A 172.16.200.10
13 mail IN A 172.16.200.20

#chown root:named test.wang.com.zone
#chmod 640 test.wang.com.zone
#rndc reload
#systemctl stop firewalld.service
#setenforce 1
[cc]
至此,子域配置完成,父域授权完成
子域测试
[cc lang="php"]
#dig -t NS test.wang.com @172.16.200.133
; <<>> DiG 9.9.4-RedHat-9.9.4-51.el7_4.1 <<>> -t NS test.wang.com @172.16.200.133
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 37063
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 2
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;test.wang.com. IN NS
;; ANSWER SECTION:
test.wang.com. 600 IN NS dns.test.wang.com.
;; ADDITIONAL SECTION:
dns.test.wang.com. 600 IN A 172.16.200.133
;; Query time: 36 msec
;; SERVER: 172.16.200.135#53(172.16.200.135)
;; WHEN: 五 12月 29 12:48:10 CST 2017
;; MSG SIZE rcvd: 76
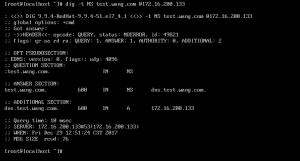
测试成功,可以进行本地正向解析。
父域测试
#dig -t NS test.wang.com @172.16.200.129
; <<>> DiG 9.9.4-RedHat-9.9.4-51.el7_4.1 <<>> -t NS test.wang.com @172.16.200.129
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 39889
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 2
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;test.wang.com. IN NS
;; ANSWER SECTION:
test.wang.com. 600 IN NS dns.test.wang.com.
;; ADDITIONAL SECTION:
dns.test.wang.com. 600 IN A 172.16.200.133
;; Query time: 32 msec
;; SERVER: 172.16.200.129#53(172.16.200.129)
;; WHEN: 五 12月 29 12:52:36 CST 2017
;; MSG SIZE rcvd: 76
父域解析正向成功
