pacp包地址
https://www.malware-traffic-analysis.net/2014/11/23/2014-11-23-traffic-analysis-exercise.pcap.zip
问题与回答
BASIC QUESTIONS
-
What is the IP address of the Windows VM that gets infected?
-
What is the MAC address of the infected VM?
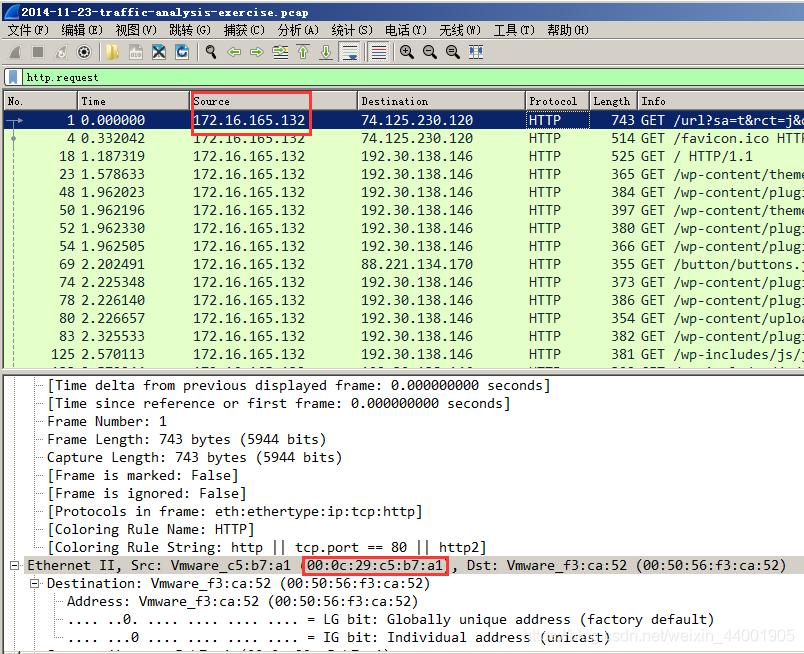
由上图可知被感染的虚拟机ip和mac地址分别为172.16.165.132和00:0c:29:c5:b7:a1
- What is the IP address of the compromised web site?
根据info信息判断,被攻陷的站点ip是192.30.138.146
- What is the domain name of the compromised web site?
该站点域名是hijinksensue.com
-
What is the IP address and domain name that delivered the exploit kit and malware?
-
What is the domain name that delivered the exploit kit and malware?
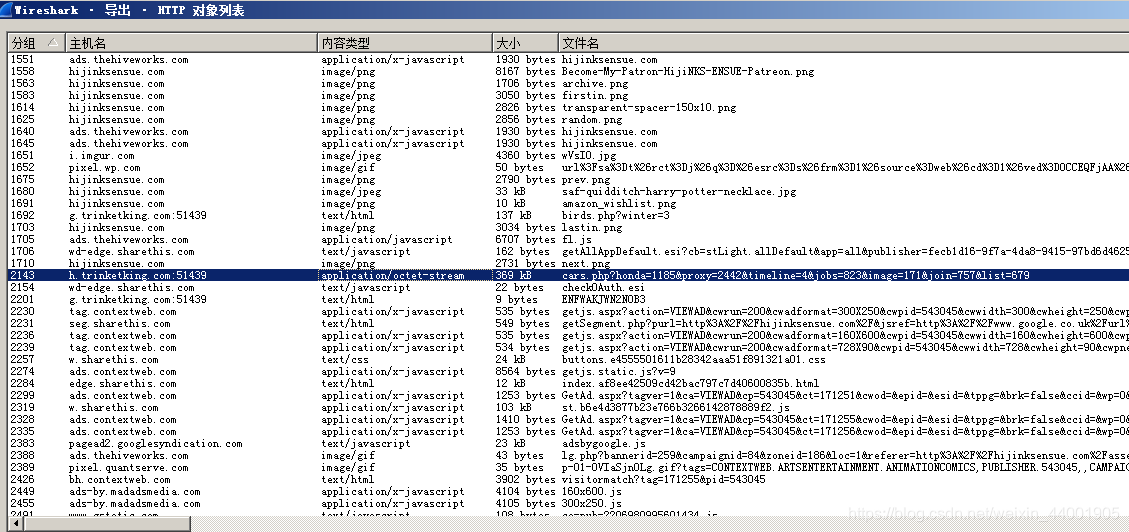
导出http对象,查找可疑内容类型
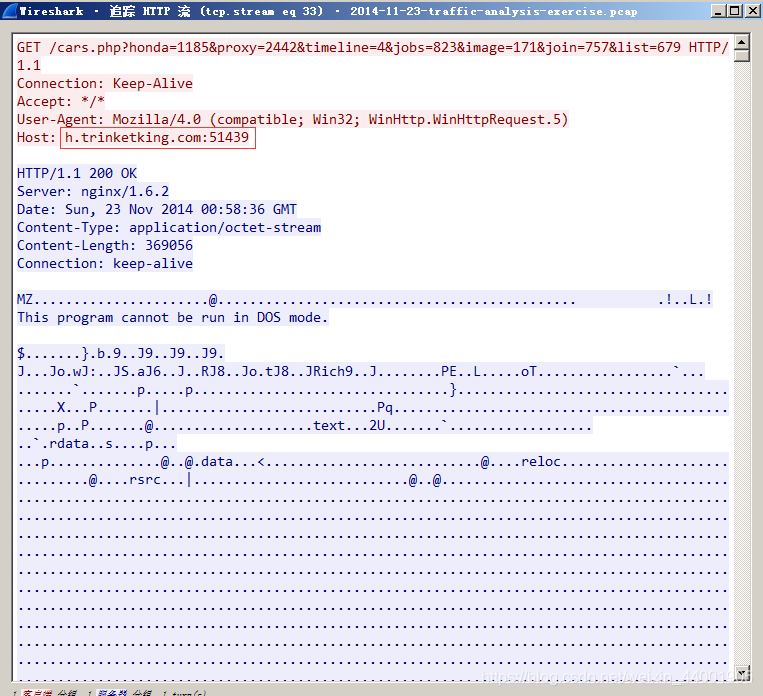
过滤,追踪流发现有个pe文件,dump出来,SHA1:dac3d479ce4af6d2ffd5314191e768543acfe32d
大致分析了一下,是个Qbot银行木马
因此可以判断提供恶意软件的ip和域名分别是37.143.15.180和g.trinketking.com:51439,h.trinketking.com:51439
MORE ADVANCED QUESTIONS
- What is the exploit kit (EK) that delivers the malware?
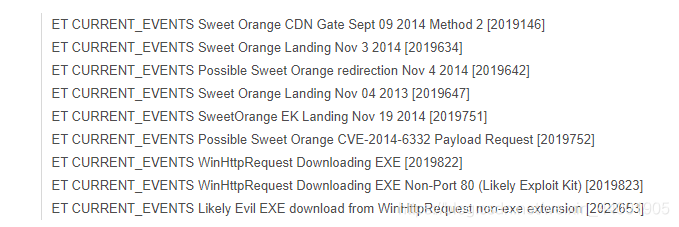
获取hash在vt查找,提供方为Sweet Orange
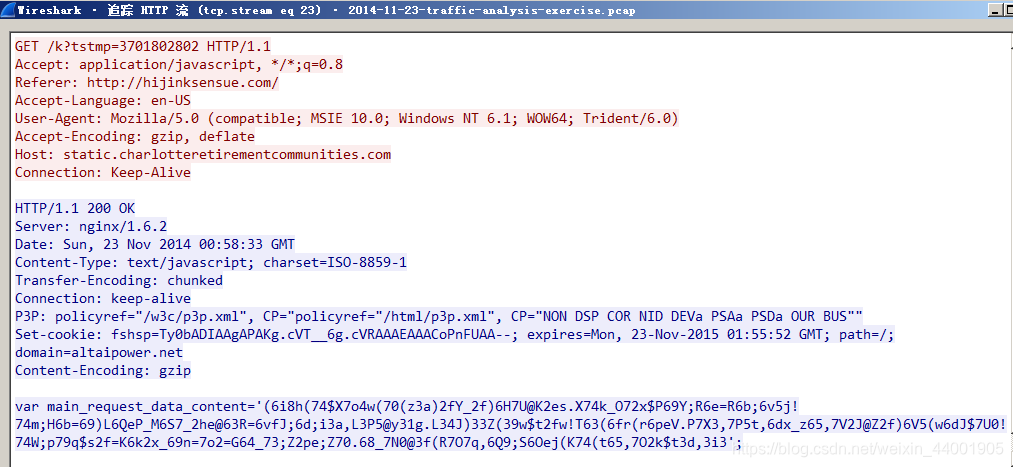
- What is the redirect URL that points to the exploit kit (EK) landing page?
static.charlotteretirementcommunities.com/k?tstmp=3701802802
- What is the IP address of the redirect URL that points to the exploit kit (EK) landing page?
50.87.149.90
这两个问题我一个个翻也就找到什么,看了官网给的答案,是下面的页面,但是也没有发现什么,感觉总是少点东西,也希望有看到的老哥能解答我对这个问题的疑惑
- Extract the malware payload from the pcap. What is the MD5 or SHA256 hash?
在前面的问题中我已经把Qbot后门提取出来了,具体信息如下
File: malware.bin
SHA1: dac3d479ce4af6d2ffd5314191e768543acfe32d
SHA256: cc185105946c202d9fd0ef18423b078cd8e064b1e2a87e93ed1b3d4f2cbdb65d
SHA512: 6057bc6681616a154ee869fb575ed62c5330dc3f513058ab694997d65ce9a2a0a7c2b86158cb8d56e2d002d76b6e51b5d72cf8c4269b9dc509b18a14eee8927d
MD5: 1408275c2e2c8fe5e83227ba371ac6b3